Government Corruption News Stories
Below are key excerpts of revealing news articles on government corruption from reliable news media sources. If any link fails to function, a paywall blocks full access, or the article is no longer available, try these digital tools.
A federal appeals court in the US has killed a ban on plastic containers contaminated with highly toxic PFAS “forever chemicals” found to leach at alarming levels into food, cosmetics, household cleaners, pesticides and other products across the economy. Houston-based Inhance manufactures an estimated 200m containers annually with a process that creates, among other chemicals, PFOA, a toxic PFAS compound. The Environmental Protection Agency (EPA) in December prohibited Inhance from using the manufacturing process. But the conservative fifth circuit court of appeals court overturned the ban. The judges did not deny the containers’ health risks, but said the EPA could not regulate the buckets under the statute it used. The rule requires companies to alert the EPA if a new industrial process creates hazardous chemicals. Inhance has produced the containers for decades and argued that its process is not new, so it is not subject to the regulations. The EPA argued that it only became aware that Inhance’s process created PFOA in 2020, so it could be regulated as a new use, but the court disagreed. PFAS are a class of about 15,000 compounds [that] have been linked to cancer, high cholesterol, liver disease, kidney disease, fetal complications and other serious health problems. A peer-reviewed study in 2011 found Inhance’s containers leached the toxic compounds into their contents.
Note: For more along these lines, see concise summaries of deeply revealing news articles on health and corporate corruption from reliable major media sources.
A devastating new Defense Department inspector general report finds that ... the Army, the primary Defense Department proponent for battlefield influence and deception, has failed to staff its own psyops units. Recent revelations about the Pentagon’s psyops call into question just how effective these programs really are. In 2022, an extensive report by the Washington Post revealed widespread concern inside DOD that psychological operations were being waged both recklessly and ineffectively by the armed services. The report was spurred by research from the Stanford Internet Observatory which detailed over 150 instances of Facebook and Twitter removing accounts linked to U.S. military influence campaigns. The 2019 National Defense Authorization Act gave the Defense Department a green light to engage in offensive psyops campaigns, including clandestine operations that align with the same definition as covert, meaning that the armed forces can carry out influence operations that deny an American connection. After the congressional authorization, an unnamed defense official said, “Combatant commanders got really excited” and were “eager to utilize these new authorities. The defense contractors were equally eager to land lucrative classified contracts to enable clandestine influence operations.” Researchers at Stanford ultimately found that despite the dozens of Defense Department obscured accounts spreading misinformation, the effect on foreign populations was far less than information conveyed overtly from self-identified U.S. sources.
Note: Read about the Pentagon's secret army of 60,000 undercover operatives that manipulate public perception. Learn more about the history of military-intelligence influence on the media in our comprehensive Military-Intelligence Corruption Information Center.
Hardware that breaks into your phone; software that monitors you on the internet; systems that can recognize your face and track your car: The New York State Police are drowning in surveillance tech. Last year alone, the Troopers signed at least $15 million in contracts for powerful new surveillance tools. Surveillance technology has far outpaced traditional privacy laws. In New York, lawmakers launched a years-in-the-making legislative campaign last year to rein in police intrusion. None of their bills have made it out of committee. A report from the U.S. Office of the Director of National Intelligence, put it succinctly: “The government would never have been permitted to compel billions of people to carry location tracking devices on their persons at all times, to log and track most of their social interactions, or to keep flawless records of all their reading habits.” That report called specific attention to the “data broker loophole”: law enforcement’s practice of obtaining data for which they’d otherwise have to obtain a warrant by buying it from brokers. The New York State Police have taken greater and greater advantage of the loophole in recent years. They’ve also spent millions on mobile device forensic tools, or MDFTs, powerful hacking hardware and software that allow users to download full, searchable copies of a cellphone’s data, including social media messages, emails, web and search histories, and minute-by-minute location information.
Note: For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
Private donors including big-box stores, fossil fuel companies, and tech giants are secretly giving hundreds of millions of dollars annually to law enforcement agencies and related foundations, allowing police to buy specialized weapons and technology with little public oversight. Experts say this huge deluge of police “dark money” funding, detailed in a new University of Chicago working paper ... leaves law enforcement beholden to the companies and powerful donors bankrolling them, rather than the communities that officers are sworn to serve. The study, which analyzed a database of nonprofit tax returns, found that from 2014 to 2019, more than 600 private donors and organizations collectively funneled $461 million to police and to other nonprofits supporting police. The Baltimore Police Department for years used private money to fund a secret aerial surveillance program that could track the locations of people throughout the city in real time. The program ... was eventually ruled unconstitutional in court. In Los Angeles, the city’s police department used money from Target ... routed through a local police foundation — to purchase software from Palantir, venture capitalist Peter Thiel’s data analytics company, that provides police massive amounts of sensitive data and purports to identify crime “hot spots.” For the most part, the millions in dark-money funding that police agencies receive each year is perfectly legal. There are largely no laws or policies governing foundation donations to the police.
Note: For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
According to Wikipedia, the United States has been involved in 107 wars since its founding and 41 of these were fought against the Indigenous peoples of North America. Most of these wars are ignored by schools, textbooks and the media, but the pressure to become involved in additional conflict is ever-present. At times the number of private contractors has been larger than that of enlisted troops. In April 2008, there were 163,900 contractors and 160,000 enlisted troops in Iraq. But when most media reported the number of Americans in the war zone, they reported the number of enlisted troops and not the contractors. This results in a predictable under-estimate of American involvement and additional earnings for contractor providers. Every year, the defense industry donates millions of dollars to the campaigns of members of Congress, creating pressure on the legislative branch to fund specific weapons systems, maintain an extremely high Pentagon budget, and add ever more military spending. In 2022 the weapons/defense industry donated $10.2 million to the 84 members of the House and Senate Armed Services Committees. And the wars continue. In his book “The United States of War,” David Vine reports that, “In the nearly two decades since U.S. forces invaded Afghanistan and Iraq, the U.S. military has fought in at least 22 countries.” If we are to escape a future of forever wars, all justifications for war should be questioned and debated before the killing starts.
Note: Learn more about war failures and lies in our comprehensive Military-Intelligence Corruption Information Center. For more, see concise summaries of deeply revealing news articles on war from reliable major media sources.
The Haitian Bald Headed Party (PHTK) has tyrannically ruled Haiti since 2011. The U.S. State Department, who unilaterally picked Ariel Henry to be Haiti’s prime minister in July of 2021, has now decided Henry no longer fits their interests and has forced him to step down. Henry was prevented from returning to Haiti on March 5 by paramilitary gangs who attempted to take the Toussaint Louverture International Airport, opening fire and hitting a plane bound for Cuba. The imperial forces responsible for over half a million illegal U.S. guns in Haiti that fuel this unparalleled violence are now preparing their next move to keep Haiti subdued. For the past 18 months, the Biden administration has sought to facilitate what will be the fourth U.S.-led foreign invasion and occupation of Haiti in the last 100 years by deputizing Kenya, Benin, the Bahamas, and other western neocolonies to carry out the occupation. The CIA remains active as well seeking a neocolony the U.S. can deputize to carry out this invasion. The only Haitian representatives that can be considered for the U.S.-led transitional government have to agree to the occupation. U.S. policy empowers and works with corrupt political leadership in Haiti because they can be relied upon to do the U.S.’s bidding. Meanwhile, those leaders who refuse to sell out to imperial interests are repressed and murdered. The ruling PHTK [has] bragged about being “legal bandits” above the law and employing ... government death squads armed with hundreds of thousands of U.S. weapons.
Note: The US government wants Ariel Henry out to purportedly prevent a full scale civil war. Is the US now trying to address Haitian stability and violence that US policies have helped create? Read about US involvement in the assassination of Haitian President Jovenel Moïse. Learn more about the role the arms industry plays in global conflicts in our comprehensive Military-Intelligence Corruption Information Center.
Federal investigators have ordered Google to provide information on all viewers of select YouTube videos. In a just-unsealed case from Kentucky ... undercover cops sought to identify the individual behind the online moniker “elonmuskwhm,” who they suspect of buying bitcoin for cash. In conversations with the user in early January, undercover agents sent links of YouTube tutorials for mapping via drones and augmented reality software, then asked Google for information on who had viewed the videos, which collectively have been watched over 30,000 times. The court orders show the government telling Google to provide the names, addresses, telephone numbers and user activity for all Google account users who accessed the YouTube videos between January 1 and January 8, 2023. The government also wanted the IP addresses of non-Google account owners who viewed the videos. The cops argued, “There is reason to believe that these records would be relevant and material to an ongoing criminal investigation, including by providing identification information about the perpetrators.” The court granted the order and Google was told to keep the request secret. Privacy experts said the orders were unconstitutional because they threatened to undo protections in the 1st and 4th Amendments covering free speech and freedom from unreasonable searches. Albert Fox-Cahn, executive director at the Surveillance Technology Oversight Project [says that] “no one should fear a knock at the door from police simply because of what the YouTube algorithm serves up. I’m horrified that the courts are allowing this.”
Note: The article refers to federal investigators and to undercover cops, but it doesn't specify who was actually doing the investigating. What agency or agencies were involved in these secret operations? For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
The National Park Service is continuing to convert dozens of its sites across the country to cashless payments only, drawing complaints and, now, a lawsuit. Starting in June last year, visitors to Rocky Mountain National Park in Colorado were told that they could not use cash to enter the park or use its campgrounds. The negative reactions were swift, with visitors raising privacy concerns and expressing confusion about why the American dollar would not be welcome in the U.S. parks system. Now these complaints are the subject of a lawsuit filed on March 6 in U.S. District Court in the District of Columbia, asserting that the service’s policies violate federal law defining cash as “legal tender” and the visitors’ “lawful right to pay in cash” at national sites, including those without bank accounts or cards or those who simply prefer to pay cash. In addition to the park service, its director, Charles F. Sams, III, and the Department of the Interior were named as defendants. One of the three plaintiffs, Toby Stover, a New York woman, drove to Hyde Park, N.Y., in January. She ... was not allowed to enter after trying to pay $10 in cash, the filing said. The plaintiffs’ lawyer, Ray L. Flores, II, said in an emailed reply to questions that the legal action is being financially backed by the Children’s Health Defense. Mr. Flores said in the email that cashless policies were “a key component — if not the linchpin — of the surveillance state.”
Note: This article is also available here. A 2018 Guardian piece titled "The cashless society is a con and big finance is behind it" describes some of the basic problems with the push to go cashless.
The FBI spends "every day, all day long" interrogating people over their Facebook posts. At least, that's what agents told Stillwater, Oklahoma, resident Rolla Abdeljawad when they showed up at her house to ask her about her social media activity. Three FBI agents came to Abdeljawad's house and said that they had been given "screenshots" of her posts by Facebook. Her lawyer Hassan Shibly posted a video of the incident. "Facebook gave us a couple of screenshots of your account," one agent in a gray shirt said in the video. "So we no longer live in a free country and we can't say what we want?" replied Abdeljawad. "No, we totally do. That's why we're not here to arrest you or anything," a second agent in a red shirt added. "We do this every day, all day long. It's just an effort to keep everybody safe and make sure nobody has any ill will." Shibly says that he doesn't know which Facebook post caught the agents' attention, and that it was the first time he had heard of Facebook's parent company, Meta, preemptively reporting posts to law enforcement. [Abdeljawad] made multiple angry posts per day about the war in Gaza, referring to Israel as "Israhell." But none of the posts on her feed call for violence. Ironically, Abdeljawad had also posted a warning about exactly the kind of government monitoring she was later subjected to. "Don't fall for their games. Our community is being watched & they are just waiting for any reason to round us up," Abdeljawad wrote.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the erosion of civil liberties from reliable major media sources.
For 55 years, every presidential administration has granted early protection to major candidates who requested it. The Biden administration is the sole outlier. The Kennedy campaign made its fifth formal request for Secret Service protection in March, citing a 67-page report of repeated death threats, nutjob letters, two heavily armed intruders to a campaign event, an invader in Kennedy’s Cape Cod house, and another man who invaded Kennedy’s home twice in one day when Kennedy and his wife, Cheryl Hines, were at home. President Biden’s decision to deny Secret Service protection to Kennedy seems to be based on political considerations and weaponizes the Secret Service by making it necessary for Kennedy to raise and spend millions of dollars each month for security. Kennedy appears to fit neatly into the law governing Secret Service protection for presidential candidates. Security costs the campaign 30 cents out of each dollar raised. Secret Service records recently revealed the agency’s conclusions that Kennedy is at “elevated risk for adverse attention,” and after reviewing credible armed threats against Kennedy, the agency assembled a group of eight teams ready to step in quickly after they get the go-ahead. But they never got it. RFK Jr. has provoked and challenged some of the most powerful forces in our country, especially concerning the military-industrial complex, the CIA, and endless foreign wars that so enrich defense contractors. The perils to Kennedy arise not only because of his name but also because of the mainstream media’s relentless demonization of him.
Note: Nikki Haley asked for Secret Service protection earlier this month, and the Secret Service agreed even though she is no longer in the race. Read more about the JFK assassination. For more along these lines, see concise summaries of deeply revealing news articles on government corruption from reliable major media sources.
A new nonfiction streaming series, “Four Died Trying” ... investigates not only the JFK liquidation, but also the people and players allegedly behind the assassinations of Malcolm X on Feb. 21, 1965; Rev. Martin Luther King Jr., on April 4, 1968; and Sen. Robert Francis Kennedy on June 6, 1968. Each of these killings is a false mystery. We know what happened to these guys. Each of these leaders in the 1960s were killed by the powers-that-be because of what they were doing at the time. Who planned it? It’s a combination of people within the Pentagon, the CIA, Johnson, elements of the mob. There’s continually more evidence to show that all of these groups were involved. They were each of them, in their own ways, working for a better world. President Kennedy ... was trying to end the Cold War. Malcolm was going to bring charges against the U.S. in the U.N., in the World Court. Martin Luther King came out against the Vietnam War and was planning the occupation of Washington, D.C. [with the Poor People’s Campaign]. Bobby was becoming the candidate of the poor and disenfranchised and was talking about investigating his brother’s death and pulling out of Vietnam. We haven’t had any president since then who hasn’t been a creature of this military-industrial-intelligence-complex. This is the profound warning Eisenhower gives us. He worries that a technocracy, a scientific elite, could control American democracy. It’s a profound warning from a general and a president to the American public that we unfortunately did not heed as we should have.
Note: Listen to an excellent podcast with the filmmakers about what these tragic assassinations had in common. For more along these lines, read our in-depth essay on the MLK assassination, along with concise summaries of revealing news articles on assassinations.
The U.S. Navy is reportedly preparing to test a hypersonic weapon as part of a joint developmental program with the U.S. Army, which aims to unleash the military’s Long-Range Hypersonic Weapon (LRHW) capabilities. The forthcoming test will involve the C-HGB, which relies on the Navy’s booster rocket motor to propel the weapon to hypersonic speeds. Once the rocket is ejected, the C-HGB can glide at speeds of Mach 5 or greater.Production of the C-HGB for the Army and the Navy has been underway for several years in cooperation with Dynetics ... who was contracted to develop the prototypes. Dynetics’ development of the C-HGB prototypes marks the first time that a domestic private sector entity has been tasked with building hypersonic weapons. Known as Dark Eagle, the Army says its LRHW will be capable of reaching targets within a range of 1,725 miles and reportedly traveling at speeds exceeding 3,800 miles per hour. Presently, the U.S. is racing against similar hypersonic developments being undertaken by Russia and China, who have been actively testing similar weapons capabilities for years. Earlier this month, it was revealed that the U.S. Air Force conducted a test with a prototype hypersonic missile in the Marshall Islands. Formally known as the AGM-183, the missile is an air-launched rapid response weapon (ARRW), a type of hypersonic air-to-ground missile that was the result of a $480 million contract granted to Lockheed Martin in 2018.
Note: Learn more about emerging warfare technology in our comprehensive Military-Intelligence Corruption Information Center. For more, see concise summaries of deeply revealing news articles on military corruption from reliable major media sources.
A man filed a federal lawsuit Monday alleging he was paralyzed and needed his legs amputated after police officers in St. Petersburg, Florida, put him in restraints, placed him in the back of a police van without a seatbelt and then drove in a reckless manner. Heriberto Alejandro Sanchez-Mayen filed the lawsuit in US District Court for the Middle District of Florida against the city of St. Petersburg and officers Sarah Gaddis and Michael Thacker. After being handcuffed, Sanchez-Mayen was placed in the back of [a police] van where there were no seatbelts. Thacker allegedly drove “in a reckless manner and at an unsafe rate of speed,” before he suddenly came to a hard stop at an alleged red light, the suit states. The hard stop caused Sanchez-Mayen to be thrown forward, and his head struck a metal partition. After driving to the Pinellas County jail, Thacker opened the rear doors of the van and found Sanchez-Mayen “lying face down, motionless, unconscious, and unresponsive,” the suit states. The officer unsuccessfully attempted to wake him up and then dragged his limp body out of the van, causing Sanchez-Mayen to hit his head on the bumper, the door and the concrete floor. Sanchez-Mayen suffered spinal cord injuries that left him a quadriplegic, or paralyzed in all of his limbs, and resulted in the amputation of both of his legs. The lawsuit states Sanchez-Mayen should not have been arrested in the first place, noting the criminal trespassing charge was later dismissed.
Note: New Haven, Connecticut has agreed to a $45 million settlement with Randy Cox, another man who was paralyzed while being transported handcuffed and without a seat belt in the back of a police van. For more along these lines, see concise summaries of important news articles on police corruption from reliable major media sources.
Haiti was born in 1804 out of a 13-year revolution in which the enslaved people of the then French colony of Saint-Domingue dismantled their chains, defeated, in succession, the armies of France, Britain and Spain, and established a new nation. Elites in Europe and America, meanwhile, fearful that the Haitian example might embolden others struggling for freedom, sought to isolate the new nation, refusing for decades even to recognise it. In 1825, France demanded, as the price of recognition, reparations of 150m francs. France was compelling enslaved people and their descendants to pay their former masters ... forcing [Haiti] to take out loans from French banks at exorbitant rates. By 1914, 80% of the government budget went to repaying the debt. Western nations have not only impoverished Haiti, they have also constantly intervened. Jean-Bertrand Aristide [was] a leftwing priest with mass support among Haiti’s working class and poor. Twice, in 1990 and 2001, waves of public support propelled Aristide to the presidency. And twice, in 1991 and 2004, he was ousted in bloody coups. After the first coup, Aristide returned to power with US support. Nevertheless, many of the coup leaders were on the CIA payroll and the agency did not hide its hostility. A decade later, opposition to Aristide’s economic and social policies led America to force him out of office. Today, the Haitian state barely exists.
Note: In 2021, Colombian mercenaries who had received training in the US assassinated Haitian President Jovenel Moïse. For more along these lines, see concise summaries of important news articles on intelligence agency corruption from reliable major media sources.
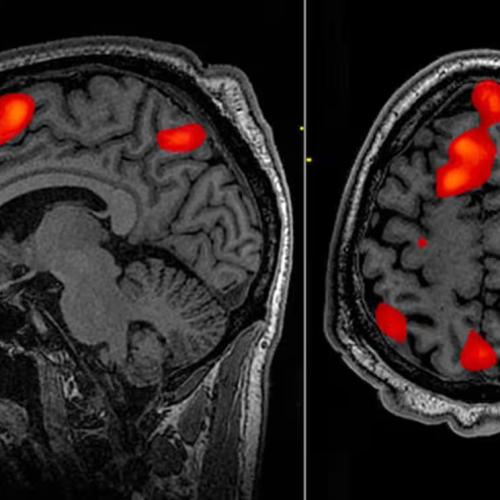
Billionaire Elon Musk’s brain-computer interface (BCI) company Neuralink made headlines earlier this year for inserting its first brain implant into a human being. Such implants ... are described as “fully implantable, cosmetically invisible, and designed to let you control a computer or mobile device anywhere you go." They can help people regain abilities lost due to aging, ailments, accidents or injuries, thus improving quality of life. Yet, great ethical concerns arise with such advancements, and the tech is already being used for questionable purposes. Some Chinese employers have started using “emotional surveillance technology” to monitor workers’ brainwaves. Governments and militaries are already ... describing the human body and brain as war’s next domain. On this new “battlefield,” an era of neuroweapons ... has begun. The Pentagon’s research arm DARPA directly or indirectly funds about half of invasive neural interface technology companies in the US. DARPA has initiated at least 40 neurotechnology-related programs over the past 24 years. As a 2024 RAND report speculates, if BCI technologies are hacked or compromised, “a malicious adversary could potentially inject fear, confusion, or anger into [a BCI] commander’s brain and cause them to make decisions that result in serious harm.” Academic Nicholas Evans speculates, further, that neuroimplants could “control an individual’s mental functions,” perhaps to manipulate memories, emotions, or even to torture the wearer. In a [military research paper] on neurowarfare: "Microbiologists have recently discovered mind-controlling parasites that can manipulate the behavior of their hosts according to their needs by switching genes on or off. Since human behavior is at least partially influenced by their genetics, nonlethal behavior modifying genetic bioweapons that spread through a highly contagious virus could thus be, in principle, possible.
Note: The CIA once used brain surgery to make six remote controlled dogs. For more, see important information on microchip implants and CIA mind control programs from reliable major media sources.
Police in the U.S. recently combined two existing dystopian technologies in a brand new way to violate civil liberties. A police force in California recently employed the new practice of taking a DNA sample from a crime scene, running this through a service provided by US company Parabon NanoLabs that guesses what the perpetrators face looked like, and plugging this rendered image into face recognition software to build a suspect list. Parabon NanoLabs ... alleges it can create an image of the suspect’s face from their DNA. Parabon NanoLabs claim to have built this system by training machine learning models on the DNA data of thousands of volunteers with 3D scans of their faces. The process is yet to be independently audited, and scientists have affirmed that predicting face shapes—particularly from DNA samples—is not possible. But this has not stopped law enforcement officers from seeking to use it, or from running these fabricated images through face recognition software. Simply put: police are using DNA to create a hypothetical and not at all accurate face, then using that face as a clue on which to base investigations into crimes. This ... threatens the rights, freedom, or even the life of whoever is unlucky enough to look a little bit like that artificial face. These technologies, and their reckless use by police forces, are an inherent threat to our individual privacy, free expression, information security, and social justice.
Note: Law enforcement officers in many U.S. states are not required to reveal that they used face recognition technology to identify suspects. For more along these lines, see concise summaries of important news articles on police corruption and the erosion of civil liberties from reliable major media sources.
Last month, I revealed internal Twitter and Department of Homeland Security emails showing that the agency had successfully pressured the social media platform to censor the New York Times during the 2020 presidential election. It was impossible to get the Times to comment on my reporting that revealed that a government agency, enacted to protect national security, had muzzled one of its own. The paper remained silent. That was the case until last week when the Times finally mentioned the issue. In a lengthy article that falsely paints efforts to promote free speech as orchestrated entirely by Trump supporters, the Times buried an acknowledgment of our reporting some 52 paragraphs down. The backhanded way in which the Times finally noted that the government had suppressed the speech — in an article that essentially argues that free speech is a dangerous right-wing plot — reflects the institution's changing nature. Many in the public may view the paper as a beacon of the free press. After all, the most important Supreme Court case enshrining media rights was New York Times v. U.S., the 1971 case that made it clear that journalists have the right to publish even classified documents. There are sprawling constitutional issues at heart here that should go beyond left and right. This government or the next administration may use the DHS apparatus to control what is said about almost any political issue. DHS bureaucrats ... have planned to suppress “misinformation” about the Ukraine war, the origins of COVID-19, and topics as broad as “racial justice.” That power can easily be exploited. Last month, I testified before Congress on the importance of free speech. I also filed an amicus brief to the Supreme Court ... urging the justices to consider the lengthy evidence that the government has already overstepped its authority with respect to online censorship.
Note: This Substack was written by independent journalist Lee Fang. Read more about Department of Homeland Security's censorship efforts, including offensive operations to manipulate public opinion, discredit individuals, and infiltrate online groups. For more along these lines, see concise summaries of important news articles on censorship and media manipulation from reliable sources.
The US government (USG) funded and supported a program of dangerous laboratory research that may have resulted in the creation and accidental laboratory release of SARS-CoV-2, the virus that caused the Covid-19 pandemic. Following the outbreak, the USG lied in order to cover up its possible role. The evidence of a possible laboratory creation revolves around a multi-year US-led research program that involved US and Chinese scientists. The research was designed by US scientists, funded mainly by the National Institutes of Health (NIH) and the Department of Defense, and administered by a US organization, the EcoHealth Alliance (EHA), with much of the work taking place at the Wuhan Institute of Virology (WIV). The NIH became the home for biodefense research starting in 2001. Biodefense funding from the Defense Department budget went to Dr. Anthony Fauci’s division, the National Institute for Allergies and Infectious Diseases (NIAID). NIAID and DARPA (in the Defense Department) supported extensive research on potential pathogens for biowarfare and biodefense, and for the design of vaccines to protect against biowarfare. NIAID became a large-scale financial supporter of Gain of Function (GoF) research, meaning laboratory experiments designed to genetically alter pathogens to make them even more pathogenic. There is a high likelihood that the US Government continues to this day to fund dangerous GoF work.
Note: Watch our latest Mindful News Brief series on the strong evidence that bioweapons research created COVID-19. For more along these lines, see concise summaries of deeply revealing news articles on COVID from reliable major media sources.
The United Nations has delivered more than $2.9 billion in cash to Afghanistan since the Taliban seized control, resulting in the flow of U.S. funds to the extremist group, according to a recent government report. The U.N. deposits the cash into a private Afghan bank and disburses funds to the agency’s aid organizations and nonprofit humanitarian groups. But the money does not stop there. Some winds up at the central bank of Afghanistan, which is under the control of the Taliban. The group took over the country after the withdrawal of U.S. forces in August 2021. The report, from the Special Inspector General for Afghanistan Reconstruction, provides the first detailed account of how U.S. cash falls under the control of the Taliban and adds to a growing body of evidence that contributions to the U.N. are not always reaching Afghans in need. After getting the money from the Federal Reserve Bank of New York, the U.N. flies shrink-wrapped $100 bills to the Kabul International Airport. The money arrives on a regular basis, as much as $40 million at a time. “Aid diversion does happen, and when it does, humanitarian work has to halt and solutions need to be found,” said one U.N. official who was not authorized to make public comment. “There are cases where the Taliban seek to take control of distribution according to their priorities, or other cases where aid work is stopped altogether.” The only way to stop [the diversion of foreign aid] would be to halt the flow of money.
Note: Read more about how the Taliban are now arms dealers after the US military left billions of dollars worth of weapons in Afghanistan. Learn more about war failures and lies in our comprehensive Military-Intelligence Corruption Information Center.
The Biological Weapons Convention (BWC) prohibits the production, use, development, stockpiling, or transfer of biological toxins or disease-causing organisms against humans, animals, or plants. More than 180 countries are party to the pact, which came into force in 1975 as the first multilateral treaty to ban an entire class of weapon. And in the years since, the taboo against state use of biological weapons has largely held. Yet a volatile geopolitical environment, combined with the rapid advance and increased access in the ability to edit and engineer pathogens, is straining and testing the nearly 50-year-old BWC as never before. From the BWC’s beginnings, critics have said it lacked vital elements, like a verification mechanism to make sure everyone is following it. Global tensions, scientific advances, and the ever-expanding repertoire of what is possible with both biology and chemistry are making those flaws and cracks ever more visible. Some high-profile mishaps linked to the US chemical and biological weapons programs ... along with public anger over the use of herbicides like Agent Orange during the Vietnam War, prompted Congress to pressure the Nixon administration to review the biological and chemical weapons programs. Contagions are hard to control and contain, and the same pathogens that can infect your target can also sicken you and your population. This is also why they tend to be used as a stealth agent of war. “The holy grail that we’ve struggled with with the Biological Weapons Convention is how do you verify that the countries that have signed up to the treaty are not making biological weapons?” said Kenneth Ward, US special representative to the Biological Weapons Convention.
Note: Watch our latest Mindful News Brief series on the strong evidence that bioweapons research created COVID-19. Learn more about emerging warfare technology in our comprehensive Military-Intelligence Corruption Information Center. For more, see concise summaries of deeply revealing news articles on science corruption from reliable major media sources.
Important Note: Explore our full index to revealing excerpts of key major media news stories on several dozen engaging topics. And don't miss amazing excerpts from 20 of the most revealing news articles ever published.