Civil Liberties Media Articles
Below are key excerpts of revealing news articles on the erosion of our civil liberties from reliable news media sources. If any link fails to function, a paywall blocks full access, or the article is no longer available, try these digital tools.
On May 30, Illinois became the 37th state to pass the Equal Right Amendment (ERA), which says, Equality of rights under the law shall not be denied or abridged by the United States or by any State on account of sex. Next, advocates aim to secure the final state needed to ratify the amendment. They will probably target Virginia, North Carolina or Georgia. The law is overdue. Many Americans assume that the United States already has gender-equality rules. The Civil Rights Act, Title IX and the Equal Pay Act all offer protections against discrimination. But these are pieces of legislation. New laws and Supreme Court rulings can diminish their power. An amendment, by contrast, would force a constitutional reckoning for sex-based discrimination. Activists lobbied, marched, went on strike and persuaded Congress to pass the amendment in 1972. Within just two years, 34 states ratified it. Then the momentum faltered. The amendment failed to secure ratification from the four additional states needed before 1982, the expiration date set by Congress. Passing the ERA will not be easy. Fierce opposition has long accompanied feminist surges, and this is already happening today. In Illinois, Republicans largely spoke out against the amendment. The dominant party could block the ERAs path at the federal level, and other states could rescind their decades-old ratification. Securing the final state to pass the ERA will probably prove as challenging as it was to secure the final state to pass the 19th Amendment a century ago.
Note: For more along these lines, see concise summaries of deeply revealing civil liberties news articles from reliable major media sources.
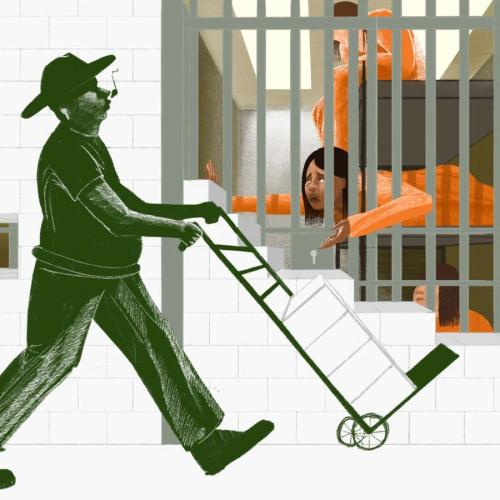
Sen. Jeff Merkley (D-Ore.) went to a shuttered Walmart in Brownsville, Texas, that has been converted into a detention center for immigrant children who have been separated from their parents. He asked for a tour. Instead, the government contractor that runs the converted store called the cops. An officer filled out a police report, and the senator was asked to leave. The half-hour incident at a strip mall near the southern border with Mexico underscores the lack of transparency from President Trumps administration about its intensifying efforts to break up undocumented families caught crossing the border, the centerpiece of a zero tolerance policy announced by Attorney General Jeff Sessions last month. The administration calls this zero tolerance.' ... It is really a zero humanity policy," Merkley said. The senator said he tried to go through proper channels to arrange a site visit but was rebuffed. Merkley said hes also sought to figure out just how many kids are being held at the old Walmart ... but he still cannot get a straight answer. [This] policy may split up an untold number of families. Minors are not allowed in criminal jails, where adults are held when theyre charged with crimes related to crossing the border. Children are sent to separate facilities. This happens even if their folks present themselves at official ports of entry and declare that they are seeking asylum.
Note: The response from the White House to this incident was to blame Merkley for immigrant crimes. For more along these lines, see concise summaries of deeply revealing government corruption news articles from reliable major media sources.
Protesters mainly women are defying police and energy companies in non-violent environmental activism. Way out in the Appalachian hills ... an orderly clutch of tents were surrounded by a plastic yellow ribbon that read, police line do not cross. Past that, a woman sat on top of a 50ft pole. Opposite the knot of tents where the womans supporters kept 24-hour vigil lay an encampment of police, pipeline workers, and private security. On Wednesday 23 May, the protester, nicknamed Nutty, finally came down after a record-breaking 57 days spent in the trees ... to stop a fracked natural-gas pipeline from being built through the state. Her final three days in the trees were spent without food. There are others, too, who remain in the forest and are still blocking construction by putting their lives on the line. These activists hold the typical concerns of having a gas pipeline run through the yard: if it leaks it poisons the water, the font of the incredible biodiversity in the area; theres a two-and-a-half-mile blast radius if it explodes; the pipeline is taking their land through eminent domain against their will for resource extraction. But they also say this is about more than just a pipeline, built by Mountain Valley Pipeline LLC. It is, they say, also about the erosion of democracy and the natural world. Virginias governor, Ralph Northam, took $50,000 from MVPs largest shareholder, EQT Corp, and another $199,251 from Dominion Energy, [a] major shareholder of the Atlantic Coast Pipeline being built nearby.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corruption in government and in the corporate world.
Cedric OBannon tried to ignore the sharp pain in his side and continue filming. The independent journalist, who was documenting a white supremacist rally in Sacramento, said he wanted to capture the neo-Nazi violence against counter-protesters with his GoPro camera. But the pain soon became overwhelming. He lifted up his blood-soaked shirt and realized that one of the men carrying a pole with a blade on the end of it had stabbed him in the stomach, puncturing him nearly two inches deep. He limped his way to an ambulance. Police did not treat OBannon like a victim. Officers instead monitored his Facebook page and sought to bring six charges against him, including conspiracy, rioting, assault and unlawful assembly. His presence at the protest along with his use of the black power fist and social media posts expressing his ideals were proof that he had violated the rights of neo-Nazis at the 26 June 2016 protests, police wrote in a report. None of the white supremacists have been charged for stabbing OBannon. OBannons case is the latest example of police in the US targeting leftwing activists, anti-Trump protesters and black Americans for surveillance and prosecution over their demonstrations and online posts. At the same time, critics say, they are failing to hold neo-Nazis responsible for physical violence. Michael German, a former FBI agent, said the Sacramento case was part of a pattern of police in the US siding with far-right groups and targeting their critics.
Note: A New York Times article describes how journalists, legal observers and volunteer medics were charged with riot-related crimes for attending a protest. United Nations officials recently said that the US government's treatment of activists was increasingly "incompatible with US obligations under international human rights law". For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the erosion of civil liberties.
Saudi Arabias Crown Prince Mohammed bin Salman has cast himself as a reformer, advocating equality for women and granting them the right to drive. But in the past few days, Saudi activists who called for exactly those things were arrested, accused by the authorities of undermining national security and branded traitors in pro-government newspapers. The unusually vicious state-led crackdown has targeted Saudi Arabias most prominent womens rights advocates, including activists who led the first protests against the driving ban decades ago and were jailed for their defiance. The arrests have been puzzling for their timing occurring just weeks before the driving ban is set to be lifted. But Saudis have also been stunned by the gravity of the charges and the deeply personal attacks on the activists, whose pictures were circulated in government-friendly media outlets in what human rights groups called a smear campaign intended to silence calls for womens rights. But the detentions of the womens rights advocates continue a pattern: Over the past year, as the crown prince has consolidated power, authorities have locked up dozens of dissidents and perceived enemies, including rights activists, clerics, businessmen and princes.
Note: Why is the US such close allies with such a repressive Muslim regime with almost total disregard for human rights? For more along these lines, see concise summaries of deeply revealing news articles on government corruption and threats to civil liberties.
In 2017, officials at the Stewart immigration detention center in Georgia placed Shoaib Ahmed, a 24-year-old immigrant from Bangladesh, in solitary confinement for encouraging fellow workers to stop working. His punishment was solitary confinement for 10 days. Stewart is operated by the largest prison corporation in the US, CoreCivic (formerly Corrections Corporation of America), under a contract with Immigration and Customs Enforcement (Ice). A growing number of detained immigrants ... are subjected to forced labor. In April, we filed a lawsuit ... against CoreCivic, alleging that the prison corporation violates human trafficking laws and employs a deprivation scheme to force immigrants detained at Stewart to work for sub-minimum wages, and then threatens to punish them for refusing to work through solitary confinement or loss of access to necessities. A lawsuit against Geo Group, another prison corporation, is moving forward for using similar practices. CoreCivics abuse and exploitation ... constitute a contemporary form of slavery as we detailed in a submission to the UN special rapporteur on the human rights of migrants. None of this bothered a group of 18 Republican lawmakers ... who sent a letter to Jeff Sessions, Ice, and the Department of Labor asking them to help ... Geo Group defend itself against the lawsuits. These legislators support for the prison corporations perhaps should not come as a surprise. Private prison companies contributed $1.6m during the 2016 federal election cycle.
Note: The federal class action lawsuit described in the article above was filed against CoreCivic by Project South jointly with the Southern Poverty Law Center, attorney Andrew Free, and the law firm Burns Charest LLP. For more along these lines, see concise summaries of deeply revealing news articles on prison industry corruption and the erosion of civil liberties.
Palestinian officials say at least 58 people have been killed in the latest round of protests. A mass attempt by Palestinians to cross the border fence separating Israel from Gaza turned violent, as Israeli soldiers responded with rifle fire. Monday became the bloodiest day since the campaign of demonstrations began seven weeks ago to protest Israels economic blockade of Gaza. Tens of thousands of Palestinians took part in the Gaza protests. Protests also took place on the West Bank. By late in the evening, 58 Palestinians, including several teenagers, had been killed and more than 1,350 wounded by gun fire, the Health Ministry said. Israeli soldiers and snipers used barrages of tear gas as well as live gunfire to keep protesters from entering Israeli territory. The protest nearest to Gaza City ... turned into a pitched battle. Emergency workers with stretchers carried off a stream of injured protesters, many with leg wounds but some having been shot in the abdomen. Even as Palestinians anger erupted, American and Israeli officials celebrated President Trumps move of the embassy to Jerusalem. Previous administrations in Washington, like the governments of most American allies, had been unwilling to make the transfer, insisting that the status of Jerusalem needed to be resolved in a peace agreement with the Palestinians.
Note: For more along these lines, see concise summaries of deeply revealing military corruption news articles from reliable major media sources.
The National Memorial for Peace and Justice, which opens on Thursday, is a place unlike any other in the United States. Together with a new Legacy Museum which also opens this week, it addresses head on a subject that has been marked by a booming silence until now the enforcement of white supremacy in America through racial terrorism in the form of lynching, as well as its other guises: slavery, segregation and modern mass incarceration. The memorial records and honors the more than 4,000 people of color ... who lost their lives to terror lynching. [It] sits audaciously atop a hill overlooking the heart of Montgomery. From its grounds you look down on the state capitol, the legislative beating heart of Alabama that acted as the first capital of the Confederacy and presides over a state constitution that to this day outlaws white and black kids going to school together: in 2004 and 2012 Alabamans held referendums on whether to remove the racist ban; both times the overwhelmingly white majority voted to keep it. [Equal Justice Initiative] has identified more than 4,384 lynchings by white people of people of colour [from] 1877 to 1950. They spanned 800 counties. Huge crowds often turned out: 10,000 to watch Henry Smith, 17, tortured and burned on a 10ft-high stage in Paris, Texas in 1893; 20,000 at the burning alive of Willy Brown in Omaha, Nebraska in 1919. Such was the communal complicity that sometimes entire white communities would attend to a man, woman and child.
Note: For more along these lines, see concise summaries of deeply revealing civil liberties news articles from reliable major media sources.
Fifty years ago ... Dr. Martin Luther King Jr. was gunned down in Memphis. The Washington Post is running a series of commentaries. The New York Times ran an emotional editorial. Neither paper will mention that they each denounced Dr. King in his later years. Nor will any outlet today likely mention that King had fallen sharply out of favor with much of the national media ... on April 4, 1967. The offense was a speech in New York. King spoke of the hundreds of thousands trembling under our violence abroad, and added that a country as financially and politically committed to war as ours could never fight a War on Poverty in earnest. One hundred and sixty-eight newspapers denounced him in the days that followed. These editorials had a peculiarly vicious flavor. In late 1967, King pooh-poohed the violence and extremism criticisms of the civil rights movement, explicitly saying the excesses of urban rioters were infinitely less dangerous and immoral than the cold, corporatized murder of the American mainstream. If destruction of property is deplorable, he asked, what is the use of napalm on people? Yet the mainstream King is the one most Americans have been conditioned to believe in. King ... died wanting us to radically change our way of life. But history has sanitized him, turning him into a mainstream leader who accomplished what he could within an acceptable role. That sanitizing continues on each of these anniversaries, and is a sad commentary on our inability to listen to even the best of us.
Note: A recent Corbett Report on the assassination of MKL has some powerful evidence of conspiracy at the highest levels. For more along these lines, see concise summaries of deeply revealing news articles on media corruption and the erosion of civil liberties.
The Supreme Court on Monday shielded a police officer from being sued for shooting an Arizona woman in her front yard, once again making it harder to bring legal action against officers who use excessive force, even against an innocent person. With two dissents, the high court tossed out a lawsuit by a Tucson woman who was shot four times outside her home because she was seen carrying a large knife. Justices Sonia Sotomayor and Ruth Bader Ginsburg said in dissent the victim did not threaten the police or a friend who was standing nearby. This "decision is not just wrong on the law; it also sends an alarming signal to law enforcement officers and the public," Sotomayor wrote. Since the Civil War, federal law has allowed people to sue government officials, including the police, for violating their constitutional rights. But in recent years, the Supreme Court has erected a shield of immunity for police and said officers may not be sued unless victims can point to a nearly identical shooting that had been deemed unconstitutionally excessive in a previous decision. The justices did not rule on whether officer Andrew Kisela acted reasonably when he used potentially deadly force against Amy Hughes. The court instead ruled [that Kisela] could not be sued because the victim could not cite a similar case. Sotomayor said the majority had revised the facts to favor the officer. "Hughes was nowhere near the officers, had committed no illegal act, was suspected of no crime, and did not raise the knife," she wrote.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corruption in policing and in the court system.
In the five decades since Martin Luther King Jr. was shot dead by an assassin at age 39, his children have worked tirelessly to preserve his legacy. They are unanimous on one key point: James Earl Ray did not kill Martin Luther King. For the King family and others in the civil rights movement, the FBIs obsession with King in the years leading up to his slaying in Memphis on April 4, 1968 - pervasive surveillance, a malicious disinformation campaign and open denunciations by FBI director J. Edgar Hoover - laid the groundwork for their belief that he was the target of a plot. Until her own death in 2006, Coretta Scott King, who endured the FBIs campaign to discredit her husband, was open in her belief that a conspiracy led to the assassination. Her family filed a civil suit in 1999 ... and a Memphis jury ruled that the local, state and federal governments were liable for Kings death. There is abundant evidence, Coretta King said after the verdict, of a major, high-level conspiracy in the assassination of my husband. The jury found the mafia and various government agencies were deeply involved in the assassination. Mr. Ray was set up to take the blame. But nothing changed afterward. William Pepper, a New York lawyer and civil rights activist who knew and worked with King ... became convinced of Rays innocence and continued to investigate the case even after Ray died. Pepper wrote three books outlining the conspiracy, most recently The Plot to Kill King in 2016, which were largely ignored by the media.
Note: Watch an excellent, six-minute clip from Canada's PBS giving powerful evidence based on the excellent work of William Pepper that King was assassinated by factions in government that wanted his movement stopped. For more along these lines, see concise summaries of deeply revealing civil liberties news articles from reliable major media sources.
The U.S. military took more than four years to process a Freedom of Information Act request for a copy of the Guantnamo guidelines for censoring prison library material - and censored the guidelines when it processed the request. The paperwork the military released appeared to leave out three pages of the prisons procedure for handling the Quran. The Miami Herald sought the Nov. 27, 2013, document in a Dec. 10, 2013, FOIA request. The U.S. Southern Command apparently released the document, with redactions, on March 21 but didnt put it in the mail for five more days. It arrived at the Herald newsroom, which is next door to Southcom, on Tuesday. The Guantnamo prison is a Law of War detention site run by the Pentagon; left unclear was the U.S. militarys law enforcement or prosecution function related to the Detainee Library, which circulates books among 26 of the prisons 41 detainees. Of those 26, only two have been convicted of war crimes. Former CIA captives at the clandestine Camp 7 prison, including those accused of plotting the 9/11 attacks, dont have privileges at the main library but can draw from a different, secret collection. In May 2016, a U.S. Army officer in charge of detainee diversionary programs told reporters that negative screening criteria included military topics, extreme graphic violence, nudity, sexuality and extremism. Many of the prisons current detainees were held by the CIA for weeks or years before their transfer to U.S. military custody.
Note: A letter titled, "Will I Die At Guantanamo Bay? After 15 Years, I Deserve Justice" was recently published by Newsweek. For more along these lines, see concise summaries of deeply revealing news articles on corruption in government and in the intelligence community.
In November, the Saudi government locked up hundreds of influential businessmen - many of them members of the royal family - in the Riyadh Ritz-Carlton in what it called an anti-corruption campaign. Most have since been released but they are hardly free. During months of captivity, many were subject to coercion and physical abuse. In the early days of the crackdown, at least 17 detainees were hospitalized for physical abuse and one later died in custody with a neck that appeared twisted, a badly swollen body and other signs of abuse, according to a person who saw the body. To leave the Ritz, many of the detainees not only surrendered huge sums of money, but also signed over to the government control of precious real estate and shares of their companies - all outside any clear legal process. As the architect of the crackdown, Crown Prince Mohammed bin Salman prepares to travel to the United States this month to court American investment. Saudi officials are spotlighting his reforms. But extensive interviews with Saudi officials, members of the royal family, and relatives, advisers and associates of the detainees revealed a murkier, coercive operation, marked by cases of physical abuse, which transferred billions of dollars in private wealth to the crown princes control. The government ... has refused to specify the charges against individuals and, even after they were released, to clarify who was found guilty or innocent, making it impossible to know how much the process was driven by personal score settling.
Note: Yet the U.S. continues to court Saudi Arabia as one of its closest allies. For more along these lines, see concise summaries of deeply revealing government corruption news articles from reliable major media sources.
Plainclothes police officers stormed the village of Madhura in Bihar State. They chased men into fields and detained the bride and groom, already covered in turmeric powder to prepare for the ceremony, for further questioning. Speaking to reporters at the police station later, Ms. Kumari, with downcast eyes, made her position clear: I will not marry, sir, she said. I want to study. Indias child marriage rate is one of the highest in the world. But as awareness has spread about the detriments associated with underage marriages ... the prevalence has dropped. Child marriage [in India] is finely threaded with other practices, including the exchange of a dowry from the brides family to the groom, and sometimes with sex trafficking, making it difficult to tackle any one issue without addressing others. Social workers said there are no easy solutions. Bihar, a poor, agrarian state in northern India, has one of the highest rates of underage marriages in the country. In 2005, 69 percent of surveyed women said they married when they were underage. Ten years later, the number fell to 42.5 percent. Last year, the Bihari government ... dispatched social workers to villages and cities across the state, and announced that priests who officiate weddings would be required to sign declarations affirming that both parties are of legal age to marry. The legal age for marriage for Indian women is 18 years old. For men, it is 21. With the 2006 Prohibition of Child Marriage Prevention Act, Indian lawmakers criminalized child marriage.
Note: While India has outlawed child marriage as a country, twenty-seven US States set no minimum age for marriage.
Fifty years after the federal Fair Housing Act banned racial discrimination in lending, African Americans and Latinos continue to be routinely denied conventional mortgage loans at rates far higher than their white counterparts. This modern-day redlining persisted in 61 metro areas even when controlling for applicants' income, loan amount and neighborhood, according to millions of ... records analyzed by Reveal from The Center for Investigative Reporting. Lenders and their trade organizations do not dispute the fact that they turn away people of color at rates far greater than whites, [and] singled out the three-digit credit score ... as especially important in lending decisions. Reveal's analysis included all records publicly available under the Home Mortgage Disclosure Act. Credit score was not included because that information is not publicly available. That's because lenders have deflected attempts to force them to report that data to the government. America's largest bank, JPMorgan Chase & Co., has argued that the data should remain closed off even to academics. At the same time, studies have found proprietary credit score algorithms to have a discriminatory impact on borrowers of color. The "decades-old credit scoring model" currently used "does not take into account consumer data on ... bill payments," Republican Sen. Tim Scott of South Carolina wrote in August. "This exclusion disproportionately hurts African-Americans, Latinos, and young people who are otherwise creditworthy."
Note: For more along these lines, see concise summaries of deeply revealing news articles on financial industry corruption and civil liberties.
Last week, the existence of a draft Department of Homeland Security (DHS) report came to light, which calls for long-term surveillance of Sunni Muslim immigrants. Internal documents obtained from the FBI and DHS last year also showed how the agencies are surveilling the Movement for Black Lives, bringing into mind tactics of Cointelpro, an FBI program which secretly and illegally conducted surveillance on the civil rights movement in order to disrupt Americans ability to organize politically. But these are not the only types of surveillance this administration is engaged in. On 18 October, DHS implemented a new rule to track the internet activity of all visa applicants, visa holders and legal permanent residents. The rule would also apply to naturalized US citizens. The new rule would track and store social media account information and other highly sensitive data as part of individuals immigration files. The policy would allow DHS to collect and track immigrants social media accounts handles as well as aliases, and search results from both public search engines as well as commercial databases. The rule ... seems like it was designed with the specific purpose of hampering our freedom of speech, in line with the Trump administrations other chilling tactics of attacks on the press and crackdowns on protesters who do not fall in line with the policies of this administration. This covert surveillance, now culminating in overt spying on immigrants, is designed as a tactic to control and fracture dissent.
Note: Read more about the FBI's infamous Cointelpro program. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
Eight humanitarian volunteers who help migrants survive desert treks have been charged with federal crimes, prompting fears of an escalating crackdown by the Trump administration. The volunteers, all members of the Arizona-based group No More Deaths, appeared in court on Tuesday charged with a variety of offences including driving in a wilderness area, entering a wildlife refuge without a permit and abandoning property the latter an apparent reference to leaving water, food and blankets on migrant trails. The charges came a week after No More Deaths, a coalition of religious and community activists, published a report accusing border patrol agents of condemning migrants to death by sabotaging water containers and other supplies. It also accused agents of harassing volunteers in the field. Hours after the reports publication one activist, Scott Warren, 35, was arrested and charged with harboring two undocumented immigrants, a felony. No More Deaths stopped short of calling it retaliation for the report but said the timing was suspicious. Warren was among the eight who appeared in court this week. No More Deaths said the charges fit a pattern of interference in efforts to save the lives of migrants who trek for days or weeks across harsh deserts which bake by day and freeze by night. The charges relate to activities in Cabeza Prieta national wildlife refuge. Some 32 sets of human remains were found there last year.
Note: A New York Times article is titled "4 Convicted of Entering Refuge in Quest to Aid Migrants." And this informative article shows the US government's obsession with stopping activists.
An Amish family in Pennsylvania must connect to its local municipal sewer system, even though it would require the use of an electric pump, which goes against the family's religious beliefs. A Jan. 5 opinion by a divided Pennsylvania Commonwealth Court finally ended the five-year legal battle. The court agreed with a lower court ruling that ordered the Yoder family to connect to the municipal sewer system. The Yoder family argued that use of electricity violates its religious convictions. The family has used an outhouse - an "old-fashioned privy" - that did not require running water or electricity. But Sugar Grove Township requires residents with properties that abut the sewer system to connect to it at the owners' cost. The ruling addressed whether the Yoders could connect to the system without use of an electric pump. The court ruled that that using an electric pump was the "least intrusive means" of connecting to the sewer system. In a dissenting opinion, Judge Patricia McCullough expressed concern with the ruling, saying there were other ways of disposing of sewage in a sanitary way that would not infringe upon the Yoder family's religious rights. That's a concern shared by Sara Rose, a senior staff attorney with the American Civil Liberties Union. "They didn't consider the other ways that the government could have achieved its ends," she said. She also said the decision unduly put the burden on the Yoders.
Note: For more along these lines, see concise summaries of deeply revealing civil liberties news articles from reliable major media sources.
I was captured when I was in my 20s and brought to Guantanamo Bay in 2004, after more than two years in secret prisons. I have been imprisoned here without charges since then. I am now 43. Thirteen years ago, your country brought me here because of accusations about who I was. Confessions were beaten out of me in those secret prisons. I tried, but I am no longer trying to fight against those accusations from the past. What I am asking today is, how long is my punishment going to continue? Your president says there will be no more transfers from here. Am I going to die here? If I have committed crimes against the law, charge me. In 15 years, I have never been charged, and the worst things the government has said about me were extracted by force. The judge in my habeas case decided years ago that I had been subjected to physical and psychological abuse during my interrogations, and statements the government has wanted to use against me are not reliable. Even if I were cleared, it would not matter. There are men here who have been cleared for years who are sitting in prison next to me. Detainees here, all Muslim, have never had rights equal to other human beings. Even when we first won the right to challenge our detention, in the end, it became meaningless. It is hard for me to ... believe that laws will not be bent again to allow the government to win. But this week, I am joining a group of detainees here, all of us who have been held without charges for years, to try again to ask the courts for protection.
Note: The above was written by Sharqawi Al Hajj, a Yemeni citizen detained at Guantanamo Bay. For more along these lines, see the "10 Craziest Things in the Senate Report on Torture". For more, see concise summaries of deeply revealing news articles on corruption in government and in the intelligence community.
The Justice Department was caught in another high-profile travesty last month. On Dec. 20, federal judge Gloria Navarro declared a mistrial in the case against Nevada rancher Cliven Bundy and others after prosecutors were caught withholding massive amounts of evidence undermining federal charges. Bundy, a 71-year old Nevadan rancher, and his sons and supporters were involved in an armed standoff with the Bureau of Land Management (BLM) ... stemming from decades of unpaid cattle grazing fees and restrictions. The Bundys have long claimed the feds were on a vendetta against them, and 3,300 pages of documents the Justice Department wrongfully concealed from their lawyers provides smoking guns that buttress their case. A whistleblowing memo by BLM chief investigator Larry Wooten charges that BLM chose "the most intrusive, oppressive, large scale and militaristic trespass cattle (seizure) possible" against Bundy. The feds charged the Bundys with conspiracy in large part because the ranchers summoned militia to defend them after they claimed that FBI snipers had surrounded their ranch. Justice Department lawyers scoffed at this claim in prior trials ... but newly-released documents confirm that snipers were in place prior to the Bundys call for help. The feds also belatedly turned over multiple threat assessments which revealed that the Bundys were not violent or dangerous, including an FBI analysis that concluded that BLM was "trying to provoke a conflict" with the Bundys.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corruption in government and in the judicial system.
Important Note: Explore our full index to key excerpts of revealing major media news articles on several dozen engaging topics. And don't miss amazing excerpts from 20 of the most revealing news articles ever published.