Government Corruption Media Articles
Below are key excerpts of revealing news articles on government corruption from reliable news media sources. If any link fails to function, a paywall blocks full access, or the article is no longer available, try these digital tools.
For almost 4,000 years, some governments have insisted that if wars must be fought, there should be rules. During its assault, on Black Saturday, Hamas broke numerous laws of war, starting with its rocket fire into Israel, which made no attempt to discriminate between military and civilian targets, breaking article 13 of protocol II of the Geneva conventions. Its fighters murdered, tortured and raped, breaking common article 3 of the Geneva conventions and articles 27 and 32 of the fourth convention. They also engaged in pillage and terrorism (33, fourth convention) and the taking of hostages (34, fourth, and article 8 of the Rome statute). In responding to this attack, Israel has also broken several laws of war. These crimes begin with the use of collective penalties against the people of Gaza (article 33 of the fourth convention and article 4 of protocol II). One aspect of this punishment appears to be the pattern of Israel’s bombing and shelling of Gaza. The war crime in this case is the damage to property: article 50 of the first Geneva convention, article 51 of the second Geneva convention and article 147 of the fourth Geneva convention. Many of the buildings hit, including numerous schools and health facilities, do not appear to qualify as military targets, despite Israeli claims that Hamas uses people as human shields. Such indiscriminate attacks contravene article 13, protocol II and article 53, fourth convention. The bombing of mosques breaks article 16 of protocol II.
Note: For more along these lines, see concise summaries of deeply revealing news articles on war from reliable major media sources.
The conflict between Israel and Hamas is just the latest impetus behind a boom in international arms sales that is bolstering profits and weapons-making capacity among American suppliers. The surge in sales is providing the Biden administration with new opportunities to tie the militaries of other countries more closely to the United States, the world’s biggest arms exporter, while also raising concerns that a more heavily armed world will be prone to careen into further wars. Even before Israel responded to the deadly Hamas attack, the combination of Russia’s invasion of Ukraine and the perception of a rising threat from China was spurring a global rush to purchase fighter planes, missiles, tanks, artillery, munitions and other lethal equipment. Worldwide military spending last year — on weapons, personnel and other costs — hit $2.2 trillion, the highest level in inflation-adjusted dollars since at least the end of the Cold War, according to the Stockholm International Peace Research Institute, which prepares an annual tally. Excluding sales within the United States, China and Russia, worldwide spending on military procurement is expected to hit $241 billion next year, a 23 percent increase since last year. That is by far the largest two-year increase in the database maintained by Janes, a company that has been tracking military spending for nearly two decades. As of last year, the United States controlled an estimated 45 percent of the world’s weapons exports, nearly five times more than any other nation.
Note: For more along these lines, see concise summaries of deeply revealing news articles on military corruption from reliable major media sources.
Silicon Valley techies are pretty sanguine about commercial surveillance. But they are much less cool about government spying. Government employees and contractors are pretty cool with state surveillance. But they are far less cool with commercial surveillance. What are they both missing? That American surveillance is a public-private partnership: a symbiosis between a concentrated tech sector that has the means, motive, and opportunity to spy on every person in the world and a state that loves surveillance as much as it hates checks and balances. The tech sector has powerful allies in government: cops and spies. No government agency could ever hope to match the efficiency and scale of commercial surveillance. Meanwhile, the private sector relies on cops and spies to go to bat for them, lobbying against new privacy laws and for lax enforcement of existing ones. Think of Amazon’s Ring cameras, which have blanketed entire neighborhoods in CCTV surveillance, which Ring shares with law enforcement agencies, sometimes without the consent or knowledge of the cameras’ owners. Ring marketing recruits cops as street teams, showering them with freebies to distribute to local homeowners. Google ... has managed to play both sides of the culture war with its location surveillance, thanks to the “reverse warrants” that cops have used to identify all the participants at both Black Lives Matter protests and the January 6 coup. Distinguishing between state and private surveillance is a fool’s errand.
Note: For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
As war in Ukraine continues, controversial defense contractors and adjacent companies like Palantir, Anduril, and Clearview AI are taking advantage to develop and level-up controversial AI-driven weapons systems and surveillance technologies. These organizations’ common link? The support of the controversial, yet ever-more powerful Silicon Valley billionaire Peter Thiel. Thiel-backed groups’ involvement in war serves to develop not only problematic and unpredictable weapons technologies and systems, but also apparently to advance and further interconnect a larger surveillance apparatus formed by Thiel and his elite allies’ collective efforts across the public and private sectors, which arguably amount to the entrenchment of a growing technocratic panopticon aimed at capturing public and private life. What’s more, Thiel’s funding efforts signal interest in developing expansive surveillance technologies, especially in the name of combatting “pre-crime” through “predictive policing” style surveillance. As an example, Thiel’s provided significant funds to Israeli intelligence-linked startup Carbyne911 (as did Jeffrey Epstein), which develops call-handling and call-identification capacities for emergency services, and has ... a predictive-policing component. Thiel also assisted in the development and subsequent privatized spinoffs of the US Government’s Defense Advanced Research Projects Agency’s (DARPA) Total Information Awareness project.
Note: Peter Thiel was also recently reported to be an FBI informant. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
As Israel escalates its attacks on Gaza, the State Department is discouraging diplomats working on Middle East issues from making public statements suggesting the U.S. wants to see less violence. In messages circulated on Friday, State Department staff wrote that high-level officials do not want press materials to include three specific phrases: “de-escalation/ceasefire,” “end to violence/bloodshed” and “restoring calm.” The revelation provides a stunning signal about the Biden administration’s reluctance to push for Israeli restraint as the close U.S. partner expands the offensive it launched after Hamas ... attacked Israeli communities. U.S. officials have said they expect Israel to abide by the laws of war in its operation against Hamas. But they have avoided discussion of a ceasefire, even as aid groups and some analysts have suggested that may be essential to allow civilians to flee Gaza and allow vital supplies to enter the area after Israel cut off electricity and water. U.S. President Joe Biden has repeatedly pledged to support Israel as it seeks to avenge the unprecedented Hamas assault. Yet as Israel’s biggest source of diplomatic and military support, the U.S. has significant leverage in the matter of how the country chooses to seek retribution and whether Israeli Prime Minister Benjamin Netanyahu tries to limit the civilian toll of his response. Biden allies may nudge the president and his team to issue stronger calls for Netanyahu to prioritize humanitarian concerns.
Note: Why wasn’t this headline in other major media? Both Washington Post and NBC News included this in only one paragraph in longer articles as if it were unimportant. For more along these lines, see concise summaries of deeply revealing news articles on war from reliable major media sources.
The CIA has for the first time acknowledged that the 1953 coup it backed in Iran that overthrew its prime minister and cemented the rule of Shah Mohammad Reza Pahlavi was undemocratic. The CIA in 2013 admitted its role in the coup that brought down Iran’s then prime minister, Mohammad Mosaddeq, but until now has not publicly acknowledged that the move was undemocratic. Much of the agency’s official history of the coup remains classified, complicating the public’s understanding of an event that still resonates, as tensions remain high between Tehran and Washington. Iran’s mission to the United Nations described the 1953 coup as marking “the inception of relentless American meddling in Iran’s internal affairs” and dismissed the US acknowledgments. “The US admission never translated into compensatory action or a genuine commitment to refrain from future interference, nor did it change its subversive policy towards the Islamic Republic of Iran,” the mission said in a statement. Seven decades later, the 1953 coup remains as hotly debated as ever in Iran, where many see a straight line leading from the coup to the 1979 Islamic Revolution that ultimately toppled the shah. The coup also prompted the CIA into a series of further actions in other countries, including Guatemala, where US clandestine operations in 1954 installed a military dictator and sparked a 40-year civil war that likely killed approximately 245,000 people.
Note: This admission came in the CIA's official podcast. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption from reliable major media sources.
Since 1973, at least 194 people have been freed from death row after evidence of innocence revealed that they had been wrongfully convicted. That’s almost one person exonerated for every ten who’ve been executed. Wrongful convictions rob innocent people of decades of their lives, waste tax dollars, and re-traumatize the victim’s family, while the people responsible remain unaccountable. Contrary to popular belief, the appeals process is not designed to catch cases of innocence. It is simply to determine whether the original trial was conducted properly. Most exonerations came only because of the extraordinary efforts of people working outside the system – pro bono lawyers, family members, even students. Wrongfully convicted people have spent up to 33 years on death row ... before the truth came to light. Any effort to streamline the death penalty process or cut appeals will only increase the risk that an innocent person is executed. Frank Lee Smith was sentenced to death in Florida on the testimony of a single witness. Four years later, the same witness saw a photo of a different man and realized she had made a mistake. DNA tests later confirmed that Smith was innocent, but it was too late. He had died in prison. Cameron Todd Willingham was executed in Texas in 2004 for setting fire to his home, killing his three children. Experts now say that the arson theories used in the investigation are scientifically invalid. Willingham may very well have been executed for an accidental fire.
Note: Read more about the innocent people sentenced to death in the US. For more along these lines, see concise summaries of deeply revealing news articles on judicial system corruption from reliable major media sources.
Kangaroo court. That’s how plaintiffs lawyers in a federal lawsuit ... describe the obscure U.S. government tribunal charged with adjudicating claims for compensation by thousands of people who say they suffered serious injuries from COVID-19 vaccines. The lawsuit ... alleges that the Countermeasures Injury Compensation Program (CICP) violates the 5th and 7th amendments of the U.S. Constitution by failing to provide “basic due process protections, transparency, and judicial oversight.” The plaintiffs — eight people who say they experienced debilitating side-effects from the COVID-19 vaccine, as well as React 19, a nonprofit organization for people who claim vaccine-related injuries, want to stop the government from forcing their claims into the CICP until due process safeguards are added. Those include the right to review evidence, obtain discovery, present expert witnesses and appeal adverse decisions. Vaccine makers Pfizer, Moderna and Johnson & Johnson, which have been indemnified by the government and are not named in the suit, also did not immediately respond to requests for comment. The plaintiffs blame the COVID vaccine for causing a wide range of ailments including Bell’s palsy, blood clots in the brain, vertigo, vascular inflammation, chronic fatigue syndrome, small fiber neuropathy, heart palpitations and more. Four plaintiffs have filed claims for compensation with the CICP but have been told there is “no timeline” for adjudicating their cases.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and COVID vaccines from reliable major media sources.
In December 2010 under the Obama administration, Congress enacted the Healthy, Hunger-Free Kids Act. This legislation provided for more fruits and vegetables in school meal programs, a focus on whole grains and a lot fewer starchy vegetables and trans-fat laden foods. In response, some food companies rejiggered ingredients just enough to add “whole grain” to their packaging. Things went downhill from there. Congress caved to lobbying in 2014, allowing schools to serve high-salt french fries and pizza sold by these companies. Again, big food lobbied hard and legislators pulled back on restrictions for sodium levels, flavored milks and amounts of refined grains. We in the United States seem to believe that ... education is unconnected to food and how we eat. Instead, our kids are at the mercy of the companies and brands inundating them: Tyson, General Mills, Kraft, Heinz and many others. Before the pandemic began, the overwhelming majority of US schools offered branded foods during or around mealtimes, and that this is worth $20bn in ... profits for the food industry. Pantries and food banks get in bed with corporate food companies because they don’t want to lose access to large quantities of foods and beverages that fill people up. That these products are unhealthy is a secondary or tertiary concern. Food banks and pantries are not always meeting the nutritional profiles of the people they serve, particularly people who are struggling with diabetes, obesity and decades of poor eating.
Note: For more along these lines, see concise summaries of deeply revealing news articles on food system corruption from reliable major media sources.
For Palestinians in Gaza, Israel’s eyes are never very far away. Surveillance drones buzz constantly from the skies. The highly-secured border is awash with security cameras and soldiers on guard. But Israel’s eyes appeared to have been closed in the lead-up to an unprecedented onslaught by the militant Hamas group, which broke down Israeli border barriers and sent hundreds of militants into Israel to carry out a brazen attack that has killed hundreds. Israel withdrew troops and settlers from the Gaza Strip in 2005. But even after Hamas overran Gaza in 2007, Israel appeared to maintain its edge, using technological and human intelligence. It claimed to know the precise locations of Hamas leadership and appeared to prove it through the assassinations of militant leaders in surgical strikes, sometimes while they slept in their bedrooms. Israel has known where to strike underground tunnels used by Hamas to ferry around fighters and arms. Despite those abilities, Hamas was able to keep its plan under wraps. The ferocious attack, which likely took months of planning and meticulous training and involved coordination among multiple militant groups, appeared to have gone under Israel’s intelligence radar. An Egyptian intelligence official said Egypt, which often serves as a mediator between Israel and Hamas, had spoken repeatedly with the Israelis about “something big,” without elaborating. He said Israeli officials were focused on the West Bank and played down the threat from Gaza.
Note: According to Efrat Fenigson, a former Israeli soldier who served on the Gaza border, "A cat moving alongside the fence is triggering all forces." How could Israeli intelligence not have known that this attack was coming? For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and war from reliable major media sources.
Public schools ... are the focus of a new report on surveillance and kids by the American Civil Liberties Union (ACLU). "Over the last two decades, a segment of the educational technology (EdTech) sector that markets student surveillance products to schools — the EdTech Surveillance industry — has grown into a $3.1 billion a year economic juggernaut," begins Digital Dystopia The Danger in Buying What the EdTech Surveillance Industry is Selling. "The EdTech Surveillance industry accomplished that feat by playing on school districts' fears of school shootings, student self-harm and suicides, and bullying — marketing them as common, ever-present threats." As the authors detail, among the technologies are surveillance cameras. These are often linked to software for facial recognition, access control, behavior analysis, and weapon detection. That is, cameras scan student faces and then algorithms identify them, allow or deny them entry based on that ID, decide if their activities are threatening, and determine if objects they carry may be dangerous or forbidden. "False hits, such as mistaking a broomstick, three-ring binder, or a Google Chromebook laptop for a gun or other type of weapon, could result in an armed police response to a school," cautions the report. Students are aware that they're being observed. Of students aged 14–18 surveyed by the ACLU ... thirty-two percent say, "I always feel like I'm being watched."
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Some of the experts responsible for helping to craft the U.S. dietary guidelines also take money from big food and drug companies. A report ... by the nonprofit U.S. Right to Know makes those concerns plain. Nine of the 20 experts on the 2025 Dietary Guidelines Advisory Committee have had conflicts of interest in the food, beverage, pharmaceutical or weight loss industries in the last five years, the report found. Gary Ruskin, the executive director of the nonprofit, said the finding “erodes confidence in the dietary guidelines,” which provide recommendations on how people can eat a healthier diet. The guidelines are widely used by policymakers to set priorities in federal food programs, health care and education. Questions about industry influence could damage the public’s trust that the recommendations are based in science. When committee members receive funding from certain industry groups or organizations, it raises the concern that they may be biased, Dr. [Marion] Nestle said. “Part of the problem is the influence is unconscious,” she said. “People don’t recognize it,” she added, and will often deny it. Even if such relationships do not influence the experts, Mr. Ruskin said, they can create the appearance that they do — which can seed doubt about how independent the committee’s recommendations actually are. Industry influence can [also] creep in later in the process ... when the U.S.D.A. and the H.H.S. produce the final guidelines based on the committee’s advice.
Note: U.S. Right to Know is an excellent resource for investigating how the food industry shapes science, policy and public opinion. For more along these lines, see concise summaries of deeply revealing news articles on food system corruption from reliable major media sources.
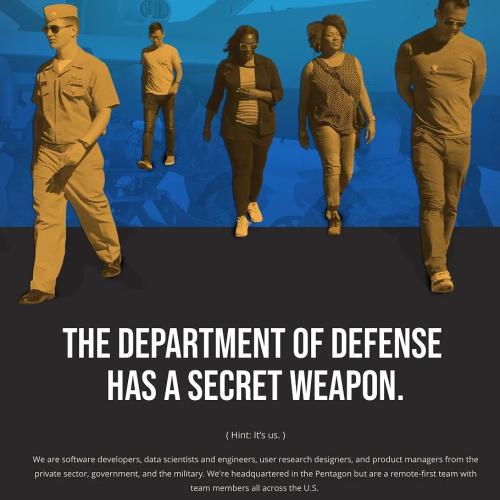
More than 80 percent of four-star officers retiring from the U.S. armed forces go on to work in the defense industry, a new study has found, underscoring the close relationship between top U.S. brass and government-contracted companies. Twenty-six of 32 four-star admirals and generals who retired from June 2018 to July 2023 were later employed in roles including executive, adviser, board member or lobbyist for companies with significant defense business, according to the analysis from the Quincy Institute for Responsible Statecraft, a think tank that advocates restraining the military’s role in U.S. foreign policy. “The revolving door between the U.S. government and the arms industry, which involves hundreds of senior Pentagon officials and military officers every year, generates the appearance — and in some cases the reality — of conflicts of interest in the making of defense policy and in the shaping of the size and composition of the Pentagon budget,” authors William Hartung and Dillon Fisher wrote. The findings shed new light on a phenomenon examined in a 2021 report from the Government Accountability Office, which found that 14 major defense contractors ... employed 1,700 former senior officials or acquisition officials in 2019. The GAO concluded that while defense contractors benefit from the practice, it could “affect public confidence in the government” by creating a perception that military officials may favor a company they see as a future employer.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corruption in the military and in the corporate world from reliable major media sources.
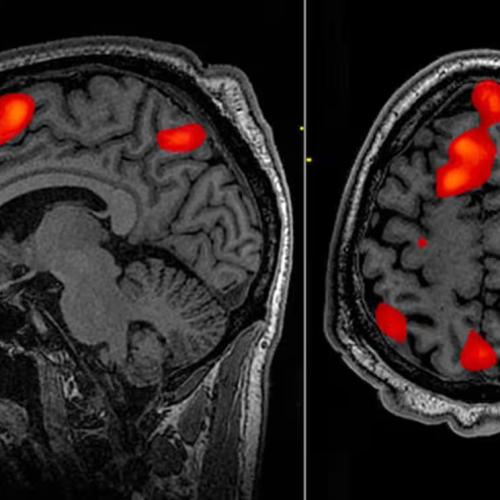
On April 27, 2021, then-director of the CDC, Rochelle Walensky stated, “we have not seen any reports” of post-vaccination myocarditis, but this was a false statement. When Walensky claimed to have “not seen any reports,” there were dozens of reports in the US Vaccine Adverse Event Reporting System (VAERS). “The CDC,” notes [journalist Zachary] Stieber, “was warned by Israel on Feb. 28, 2021, about a ‘large number’ of myocarditis cases after Pfizer COVID-19 vaccination. Internally, the warning was designated as ‘high’ importance and set off a review of US data.” The Israeli Ministry of Health requested a joint meeting with the Food and Drug Administration (FDA) and the CDC to respond to this trend. “The Israeli National Focal Point is noticing a large number of reports of myocarditis, particularly in young people, following the administration of the Pfizer vaccines,” the email stated. Even when more information about myocarditis became public, [Walensky's] agency continued to downplay the risks. Stieber also found that the CDC’s V-Safe self-reporting system did not include a category for myocarditis reports. To this day, the CDC has not released complete, updated data on myocarditis. The agency’s cover-up of adverse cardiac events has had profound consequences and represents a major breach of trust and abuse of authority. Due to the higher risks of myocarditis after Moderna, Sweden, Norway, Finland, Germany, and France suspended the use of the Moderna vaccine for people under 30 two years ago.
Note: When current and former FDA advisers and academics asked the FDA to improve COVID vaccine labeling given the significant risk of severe vaccine injuries, the agency denied almost every single request. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and coronavirus vaccines from reliable major media sources.
From Virginia to Florida, law enforcement all over the US are increasingly using tools called reverse search warrants – including geofence location warrants and keyword search warrants – to come up with a list of suspects who may have committed particular crimes. While the former is used by law enforcement to get tech companies to identify all the devices that were near a certain place at a certain time, the latter is used to get information on everyone who’s searched for a particular keyword or phrase. It’s a practice public defenders, privacy advocates and many lawmakers have criticised, arguing it violates fourth amendment protections against unreasonable searches. Unlike reverse search warrants, other warrants and subpoenas target a specific person that law enforcement has established there is probable cause to believe has committed a specific crime. But geofence warrants are sweeping in nature and are often used to compile a suspect list to further investigate. Google broke out how many geofence warrants it received for the first time in 2021. The company revealed it received nearly 21,000 geofence warrants between 2018 and 2020. The tech giant did not specify how many of those requests it complied with but did share that in the second half of 2020, it responded to 82% of all government requests for data in the US with some level of information. Apple has taken steps to publish its own numbers. In the first half of 2022 the company fielded a total of 13 geofence warrants and complied with none.
Note: The legal world is struggling to keep up with the rise of tech firms building ever more sophisticated means of surveilling people and their devices. For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
In March of 2021 a nonprofit group called the Center for Countering Digital Hate (CCDH) released a report about online misinformation. Founded [by] Imran Ahmed, the CCDH ... provides the White House with a powerful weapon to use against critics including RFK Jr. and [Elon] Musk, while also pressuring platforms like Facebook and Twitter to enforce the administration’s policies. One rumor that came up ... is that [Ahmed] works for British intelligence. “There’s nothing surprising about this,” said Mike Benz, a former State Department official who now runs the Foundation for Freedom Online, a free-speech watchdog. “This is not the first rodeo of British and U.S. intelligence services creating a cutout for the purpose of influencing the online news economy, to rig public debate in favor of political speech that supports agency agendas.” CCDH’s ... chairman is Simon Clark, a former senior fellow at the Center for American Progress (CAP), a D.C. think tank aligned with the corporate arm of the Democratic Party. One might conclude that CCDH functions as an arm of the corporate wing of the Democratic Party, to be deployed against the perceived enemies of corporate Democrats, whether they come from the left or the right. Clark was also a senior fellow at the Atlantic Council’s Digital Forensics Lab. “The Atlantic Council, in the past several years, has had seven CIA directors on its board of directors or board of advisers,” said Benz. “And it’s one of the premier architects of online censorship.”
Note: Read an excellent piece on what gave rise to the modern censorship regime. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and media manipulation from reliable sources.
Google maintains one of the world’s most comprehensive repositories of location information. Drawing from phones’ GPS coordinates, plus connections to Wi-Fi networks and cellular towers, it can often estimate a person’s whereabouts to within several feet. It gathers this information in part to sell advertising, but police routinely dip into the data to further their investigations. The use of search data is less common, but that, too, has made its way into police stations throughout the country. Traditionally, American law enforcement obtains a warrant to search the home or belongings of a specific person, in keeping with a constitutional ban on unreasonable searches and seizures. Warrants for Google’s location and search data are, in some ways, the inverse of that process, says Michael Price, the litigation director for the National Association of Criminal Defense Lawyers’ Fourth Amendment Center. Rather than naming a suspect, law enforcement identifies basic parameters—a set of geographic coordinates or search terms—and asks Google to provide hits, essentially generating a list of leads. By their very nature, these Google warrants often return information on people who haven’t been suspected of a crime. In 2018 a man in Arizona was wrongly arrested for murder based on Google location data. Google says it received a record 60,472 search warrants in the US last year, more than double the number from 2019. The company provides at least some information in about 80% of cases.
Note: For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
Fort Ord was one of 800 U.S. military bases, large and small, that were shuttered between 1988 and 2005. The cities of Seaside and Marina, Calif., where Fort Ord had been critical to the local economy, were left with a ghost town of clapboard barracks and decrepit, World War II-era concrete structures that neither of the cities could afford to tear down. Also left behind were poisonous stockpiles of unexploded ordnance, lead fragments, industrial solvents and explosives residue, a toxic legacy that in some areas of the base remains largely where the Army left it. Across the country, communities were promised that closed bases would be restored, cleaned up and turned over for civilian use. But the cleanup has proceeded at a snail’s pace at many of the facilities, where future remediation work could extend until 2084 and local governments are struggling with the cost of making the land suitable for development. At more than 1,000 sites within the closed bases, the land is so badly contaminated that no one will ever be allowed to live on it. Sites that were supposed to be clean were later found full of asbestos, radioactivity and other health threats. Military base cleanups are often full of surprises, but Hunters Point is in a league of its own. Two former supervisors at an environmental firm, Tetra Tech EC, which the Navy hired to help clean up the base, were convicted in 2018 of fraudulently submitting clean dirt to a laboratory in place of the contaminated dirt at the shipyard.
Note: For more along these lines, see concise summaries of deeply revealing news articles on military corruption from reliable major media sources.
When I joined the CIA in January 1990, I did it to serve my country. My whole world, like the worlds of all Americans, changed dramatically and permanently on September 11, 2001. Within months of the attacks, I found myself heading to Pakistan as the chief of CIA counterterrorism operations in Pakistan. Almost immediately, my team began capturing al-Qaeda fighters at safehouses all around Pakistan. Just a month after the September 11 attacks, the CIA leadership gathered its army of lawyers and black ops people and came up with a plan to legalize torture. This was despite the fact that torture has long been patently illegal in the United States. But it didn’t matter. In the end, I was the only person associated with the CIA’s torture program who was prosecuted and imprisoned. I never tortured anybody. But I was charged with five felonies, including three counts of espionage, for telling ABC News and the New York Times that the CIA was torturing its prisoners, that torture was official U.S. government policy, and that the policy had been approved by the president himself. I served 23 months in a federal prison. Former CIA Director George Tenet, former CIA Deputy Director John McLaughlin, former CIA Deputy Director for Operations Jose Rodriguez, former CIA Executive Director John Brennan, and CIA [contractors] James Mitchell and Bruce Jessen ... weakened our democracy by pretending that the Constitution and the rule of law didn’t exist.
Note: This article was written by CIA whistleblower John Kiriakou. For more along these lines, see the "10 Craziest Things in the Senate Report on Torture". For more, see concise summaries of deeply revealing news articles on intelligence agency corruption from reliable major media sources.
What would a progressive Pentagon look like? I’m not talking about a “woke” Pentagon that touts and celebrates its “diversity,” including its belated acceptance of LGBTQ+ members. Painting “Black Lives Matter” and rainbow flags on B-52 bombers doesn’t make the bombs dropped any less destructive. All too many Americans didn't know how badly they'd been lied to about the Vietnam War until the Pentagon Papers emerged near the end of that disastrous conflict. All too many Americans didn't know how badly they'd been lied to about the Afghan War until the Afghan War Papers emerged near the end of that disastrous conflict. All too many Americans didn't know how badly they'd been lied to about the Iraq War until the myth of Saddam Hussein's weapons of mass destruction (which had been part of the bogus rationale for invading that country) crumbled. A progressive Pentagon would ... celebrate the insights of Generals Smedley Butler and Dwight D. Eisenhower that war is fundamentally a racket (Butler) and that the military-industrial-congressional complex poses the severest of threats to freedom and democracy in America (President Eisenhower). A progressive Pentagon would ... recognize that one cannot serve both a republic and an empire, that a choice must be made, and that a Pentagon of the present kind in a genuine republic would voluntarily downsize itself, while largely dismantling its imperial infrastructure of perhaps 800 overseas bases.
Note: Read decorated general Smedley Butler's 1935 book War is a Racket. For more along these lines, see concise summaries of deeply revealing news articles on military corruption from reliable major media sources.
Important Note: Explore our full index to key excerpts of revealing major media news articles on several dozen engaging topics. And don't miss amazing excerpts from 20 of the most revealing news articles ever published.