Government Corruption Media Articles
Below are key excerpts of revealing news articles on government corruption from reliable news media sources. If any link fails to function, a paywall blocks full access, or the article is no longer available, try these digital tools.
In November 2020 ... a ballot initiative known as Measure J passed with 57 percent support, amending the LA County charter so that jailing people before trial would be treated as a last resort. In June, LA County signed over the handling of changes to pretrial detention under Measure J to the consulting firm Accenture, a behemoth in the world of biometric databases and predictive policing. Accenture has pushed counterterror and policing strategies around the globe: The company built the world’s biggest biometric identification system in India, which has used similar technologies to surveil protesters and conduct crowd control as part of efforts by Prime Minister Narendra Modi’s Bharatiya Janata Party to investigate the citizenship of Muslim residents. Accenture ballooned into a giant in federal consulting over the course of the “war on terror,” winning hundreds of millions of dollars in lucrative contracts from federal agencies like the Department of Homeland Security for projects from a “virtual border” to recruiting and hiring Customs and Border Protection and Border Patrol agents. In 2006, Accenture won a $10 million contract for a DHS biometric ID program, the world’s second biggest, to collect and share biometric data on foreign nationals entering or leaving the U.S. Several LA-based advocates told The Intercept that the contract is yet another development that calls into question the county’s commitment to real criminal justice reform.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
Last year, the Republican chairman of the US House Permanent Select Committee on Intelligence (HPSCI) presented an image of Americans protesting the war in Gaza while implying possible ties between the protesters and Hamas, an allegation that was used to illustrate why surveillance reforms may prove detrimental to national security. In December, as many as 200 Republican staffers gathered behind closed doors to hear a presentation ... aimed at shoring up support for a US surveillance program known as Section 702. Section 702 authorizes the government to surveil foreigners located physically overseas ... but not Americans or individuals on US soil. While eavesdropping on foreigners is permitted, doing so for the explicit purpose of gaining access to an American’s communications—a practice commonly referred to as “reverse targeting”—is strictly forbidden. “Yes, it’s true, you cannot ‘target’ protesters under 702,” one aide, a legislative director for a Republican lawmaker, says. “But that doesn’t mean the FBI doesn't still have the power to access those emails or listen to their calls if it wants.” Between 2020 and early 2021, the FBI conducted “tens of thousands” of queries related to “civil unrest” in the United States. “Political protest is literally how America was founded. It’s in our DNA,” says Jason Pye, senior policy analyst at the nonprofit FreedomWorks. “Whether you agree with these protesters or not is irrelevant.”
Note: The FBI has a long history of spying on political activists. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
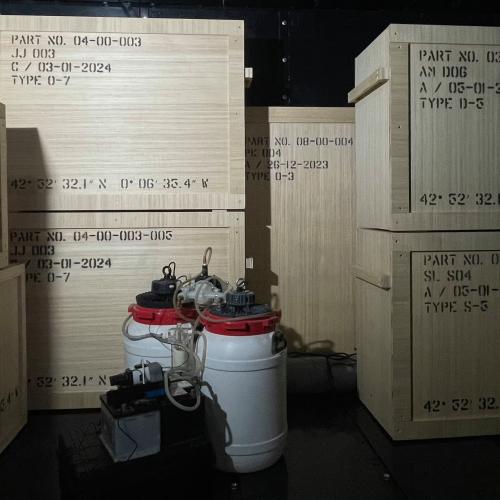
The United States Defense Department announced Friday that it found no evidence that the government is covering up contact with extraterrestrials. The report was issued by the Pentagon’s All-domain Anomaly Resolution Office (AARO), the unit created and tasked in recent years with studying UAP sightings. The report in its own way raises as many new questions as it answers. AARO investigators, for instance, dug through the claims of witnesses and whistleblowers and successfully traced back the underlying research projects, Special Access Programs (SAPs), and classified compartments. As the report says, “AARO investigated numerous named, and described, but unnamed programs alleged to involve UAP exploitation conveyed to AARO through official interviews,” and ultimately, “conclude[d] many of these programs represent authentic, current and former sensitive, national security programs, but none of these programs have been involved with capturing, recovering, or reverse-engineering off-world technology or material.” What exactly are the secret compartmentalized programs that the whistleblowers and government witnesses misidentified as being related to UAP technology? What, exactly, are the Pentagon, intelligence community, or defense contractors working on that ... looks and sounds like reverse-engineering out-of-this-world technology or even studying so-called “non-human biologics”?
Note: For more along these lines, see concise summaries of deeply revealing news articles on UFOs from reliable major media sources. Then explore the excellent, reliable resources provided in our new UFO Information Center.
The Pentagon has known of fundamental flaws with U.S. military operations in the Horn of Africa for nearly 20 years but has nonetheless forged ahead, failing to address glaring problems, according to a 2007 study. The 50-page analysis, conducted by the Institute for Defense Analyses, a private think tank that works solely for the U.S. government, is based on anonymized interviews with key U.S. government officials from across various departments and agencies. It found America’s nascent war in the Horn of Africa was plagued by a failure to define the parameters of the conflict or its aims; an overemphasis on military measures without a clear definition of the optimal military strategy; and barriers to coordination between the military and other government agencies. In 2007, the year the ... U.S. Africa Command, or AFRICOM, began operations, the U.S. conducted its first declared airstrike in Somalia. Since then, it has carried out more than 280 air attacks and commando raids, aimed primarily at the terrorist group al-Shabab, while the CIA and elite troops created local proxy forces to conduct low-profile operations on behalf of the United States. At the same time, the U.S. has provided Somalia with billions of dollars in counterterrorism assistance. The IDA study lamented the “presence of al-Qaeda” in the Horn of Africa and the “failed state of Somalia.” Both remain realities despite two decades of forever war.
Note: Learn more about war failures and lies in our comprehensive Military-Intelligence Corruption Information Center. For more, see concise summaries of deeply revealing news articles on military corruption from reliable major media sources.
The US is reported to have made more than 100 weapons sales to Israel, including thousands of bombs, since the start of the war in Gaza, but the deliveries escaped congressional oversight because each transaction was under the dollar amount requiring approval. The Biden administration ... has kept up a quiet but substantial flow of munitions to help replace the tens of thousands of bombs Israel has dropped on the tiny coastal strip, making it one of the most intense bombing campaigns in military history. Administration officials informed Congress of the 100 foreign military sales to Israel in a classified briefing. The sales ... are reported to have included precision-guided munitions, small diameter bombs, bunker busters, small arms and other lethal aid. The under-the-radar deliveries made by the Biden administration to Israel were additional to the three major military sales that were made public since the start of the war: $320m in precision bomb kits in November and 14,000 tank shells costing $106m and $147.5m of fuses and other components needed to make 155mm artillery shells in December. “Whether it is arms sales to Saudi Arabia and the UAE under the Trump administration, or sales to Israel under the Biden administration, Congress – and the American public – deserve full transparency about who is buying US weapons and how many weapons we are selling them,” said Democratic congressman Joaquin Castro.
Note: Learn more about arms industry corruption in our comprehensive Military-Intelligence Corruption Information Center. For more along these lines, see concise summaries of deeply revealing news articles on war from reliable major media sources.
Joe Biden's administration has admitted transporting migrants on secret flights into the U.S. and lawyers for its immigration agencies claim revealing the locations could create national security 'vulnerabilities'. Customs and Border Protection has refused to disclose crucial information about a program last year arranging flights for thousands of undocumented immigrants from foreign airports directly to U.S. cities. While record numbers of migrants were flowing over the southern border last year, the Biden White House was also directly transporting them into the country. Use of a cell phone app has allowed for the near undetected arrival by air of 320,000 [migrants] with no legal rights to enter the United States. Included in details of a Freedom of Information Act (FOIA) lawsuit first reported by Todd Bensman, the Center for Immigration Studies found Biden's CBP approved the latest secretive flights that transported hundreds of thousands of illegal immigrants from foreign countries into at least 43 different American airports from January through December 2023. The program was part of Biden's expansion of the CBP One app, which kicked off at the start of last year. [Migrants] who cannot legally enter the U.S. use CBP One to apply for travel authorization. Migrants are able to remain in the U.S. for two years without obtaining legal status and meanwhile are eligible for work authorization.
Note: Read the full in-depth report by the Center for Immigration studies here. For more along these lines, see concise summaries of deeply revealing news articles on government corruption from reliable major media sources.
The New York Times on February 25 published an explosive story of what purports to be the history of the CIA in Ukraine from the Maidan coup of 2014 to the present. The story, “The Spy War: How the CIA Secretly Helps Ukraine Fight Putin” ... relied on more than 200 interviews in Ukraine, the US, and “several European countries.” There is a CIA listening post in the forest along the Russian border, one of 12 “secret” bases the US maintains there. Beginning in 2016, the CIA trained an “elite Ukrainian commando force known as Unit 2245, which captured Russian drones and communications gear so that CIA technicians could reverse-engineer them.” One of the reasons that I believe the Times article was “authorized” by the intelligence community is because of what isn’t in it. There’s no mention, for example, that the United Nations has deemed Ukraine to be one of the most corrupt countries in the world, where money just seems to disappear into foreign accounts and the pockets of Ukrainian government officials. There’s no mention that Ukraine has become a “supermarket” for black market weapons and that western weapons meant for the war effort have popped up all over the world. And there is no mention at all that it was the CIA and the State Department that were responsible for the 2014 overthrow of the Ukrainian government in the first place, an action that resulted in Russia’s decision to invade eight years later.
Note: John Kiriakou is a whistleblower, former CIA counter-terrorism officer, and former senior investigator on the Senate Foreign Relations Committee. In our War Failures and Lies section in our comprehensive Military-Intelligence Corruption Information Center, we discuss how the CIA has supported Neo-Nazis in Ukraine since at least 2014, the year of the far-right coup that incorporated the Nazi group Azov Battalion into the country’s National Guard. Since then, declassified government documents show that Ukraine was systematically developed as a proxy for US war against Russia. In 2016, Congress removed a ban on funding Ukrainian neo-fascist groups, effectively paving the way for American arms and weapons to fall in the hands of Ukraine’s Nazi organizations.
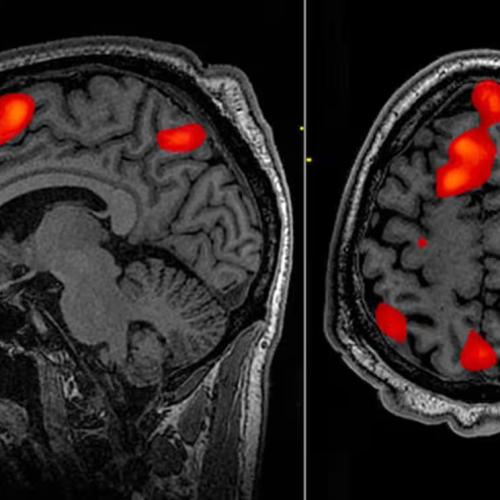
COVID-19 may have been created in a Chinese lab, a British professor told the UN Wednesday. Richard H. Ebright, a molecular biologist at Rutgers University, was quoted saying in a new Wall Street Journal article that the virus that killed millions around the world may actually have been manmade in China’s Wuhan Institute of Virology. He cited evidence found in a 2018 document from the lab that talked of making such a virus. “[The document] elevates the evidence provided by the genome sequence from the level of noteworthy to the level of a smoking gun,” Ebright said. The papers from the lab cited by Ebright contained drafts and notes regarding a grant proposal called Project DEFUSE, which sought to test engineering bat coronaviruses in a way that would make them more easily transmissible to humans. The proposal was ultimately rejected and denied funding by the US Defense Advanced Research Projects Agency, but Wade suggested that their work could have been carried out by researchers in Wuhan who had secured Chinese government funding. “Viruses made according to the DEFUSE protocol could have been available by the time Covid-19 broke out,” wrote [Nicholas] Wade, a former science editor of the New York Times. Along with the research notes, Wade claimed the specific genetic structure of the coronavirus that allowed it to infect humans served as another strong indication of “the virus’s laboratory birth.”
Note: Explore a list of news article summaries on the significant likelihood that COVID was engineered in the context of bioweapons research with US funding and Chinese military involvement at the Wuhan Institute of Virology.
In 2018 ... the government was buying up reams of consumer data — information scraped from cellphones, social media profiles, internet ad exchanges and other open sources — and deploying it for often-clandestine purposes like law enforcement and national security in the U.S. and abroad. The places you go, the websites you visit, the opinions you post — all collected and legally sold to federal agencies. The data is used in a wide variety of law enforcement, public safety, military and intelligence missions, depending on which agency is doing the acquiring. We’ve seen it used for everything from rounding up undocumented immigrants or detecting border tunnels. We’ve also seen data used for man hunting or identifying specific people in the vicinity of crimes or known criminal activity. And generally speaking, it’s often used to identify patterns. It’s often used to look for outliers or things that don’t belong. So say you have a military facility, you could look for devices that appear suspicious that are lingering near that facility. Did you know that your car tires actually broadcast a wireless signal to the central computer of your car, telling it what the tire pressure is? It’s there for perfectly legitimate safety reasons. Governments have ... figured out that the car tire is a proxy for the car. And if you just put little sensors somewhere or you run the right code on devices that you scatter around the world, then you can kind of track people with car tires.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Government officials covered up the origins of COVID-19 and “forced” the vaccination of millions of people worldwide to “protect the integrity of the bioweapons industry,” according to a senior research scientist [at] Yale University. Harvey Risch, M.D., Ph.D. ... provided compelling testimony on what he believes accounts for the “crushingly obsessive push to COVID-vaccinate every living person on the planet.” Risch was among the medical experts ... who participated in Monday’s Senate roundtable discussion on “Federal Health Agencies and the COVID Cartel: What Are They Hiding?” Risch highlighted circumstantial evidence that COVID-19 “leaked from the Wuhan Institute of Virology” (WIV) in China in fall 2019. There is evidence the virus contains a unique genetic sequence “that also exists in Moderna patents from 2017,” while intelligence has “overwhelmingly” indicated the WIV as the source of the virus. According to Risch, “This work and the WIV leak was what I consider to be the fruit of our bioweapons industry that has been performing secretive and nefarious biological weapons development for the last 70 years.” Risch said that much of this research was banned in 1975, with the enactment of the United Nations Biological Weapons Convention, which prohibited the development of offensive bioweapons. However, a carve-out in the treaty allows “small quantities of offensive bioweapons ... to be developed in order to do research on vaccine countermeasures.”
Note: For more along these lines, see concise summaries of deeply revealing news articles on COVID and government corruption from reliable major media sources.
Wikileaks founder Julian Assange, as of this writing, faces a final attempt to appeal his extradition from the U.K. to the U.S. If he fails, he faces Espionage Act charges that could lead to living out the remainder of his life in federal prison. If Assange is extradited and successfully prosecuted for espionage, it would create a dangerous precedent for the government to suppress future reporting. The New York Times has a long and storied record of publishing classified materials going back to the 1971 Pentagon Papers, which showed the true history of the Vietnam War. More recently, the Washington Post and other outlets reported on the Discord intelligence leaks, revealing that Pentagon officials had suspected that the Ukrainian counter-offensive against Russia would fail ... among many other revelations. In 2013, DOJ officials noted that the legal theory used to prosecute Assange would apply almost equally to most major newspapers with a history of reporting on government secrets, such as the many news outlets that covered Edward Snowden’s disclosures about warrantless NSA mass surveillance of Americans. It’s not hard to see how the U.S. views Assange as an enemy of the state. He has exposed secrets and hypocrisy of American policymakers on the highest level. Diplomatic cables show the extent to which the State Department often acts as an extension of narrow multinational corporate interests. Wikileaks has published many documents that go well beyond the diplomatic cables and Democratic emails. The Afghanistan war documents disclosed by Wikileaks show extensive civilian deaths and Taliban militancy, far beyond what the Pentagon had previously acknowledged.
Note: The US prosecution of Assange undermines press freedom. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and media manipulation from reliable sources.
Unidentified anomalous phenomena (UAP) have not only fueled public curiosity but have underscored the urgency for enhanced transparency from our government and its agencies. There is [a] need for Congress to initiate thorough public hearings on UAP, following explosive testimony last summer from intelligence officer-turned-whistleblower David Grusch regarding above top-secret crash retrieval and reverse engineering programs of technologies of unknown origin and nonhuman intelligence. Drawing inspiration from the historic U.S. Senate Select Committee to Study Governmental Operations with Respect to Intelligence Activities, commonly known as the Church Committee, Congress could adopt a similar, no-nonsense approach, which would unearth government secrets about UAP, establish unprecedented transparency and instill unwavering accountability in the process. The Church Committee, led by then-Senator Frank Church (D-ID) in 1975, was pivotal in investigating and exposing US intelligence agency abuses. Taking a cue from this historic success, a Church-style Select Committee on UAP is not just advisable but imperative. Such a committee would compel government agencies and officials to testify openly about their knowledge of UAP encounters. The committee would unearth the extent to which the intelligence community engaged in a disinformation campaign against the American people to keep its UAP secrets buried.
Note: For more along these lines, see concise summaries of deeply revealing news articles on UFOs from reliable major media sources. Then explore the excellent, reliable resources provided in our new UFO Information Center.
As Army pain doctor Maj. Michael Stockin prepares to be arraigned Friday on charges that he sexually abused dozens of patients at Madigan Army Medical Center, near Tacoma, Washington, two of those former patients described to CBS News what they say was conduct that betrayed their trust. "Myself and Dr. Stockin were left alone in the room. He first checked my shoulders and then he asked me to stand up and to pull down my pants and lift up my gown," said one of the soldiers, who had consulted the Army physician for shoulder pain. "Dr. Stockin, he was face level with my groin, and he started touching my genitals." Both men, now retired after more than 20 years in the Army including three combat tours each, spoke exclusively to CBS News, describing alleged misconduct hidden under the guise of medical care. They described visits to a doctor who was supposed to treat their pain, but they say instead inflicted even worse. The Army has charged Stockin with 48 counts of abusive sexual contact and five counts of indecent viewing under the military code of justice. The Army has confirmed that all of the 42 alleged victims who were treated at the clinic at Joint Base Lewis-McChord are men. The case is being prosecuted by the Army's Office of Special Trial Counsel (OSTC). Ryan Guilds, a civilian attorney representing seven of Stockin's accusers ... says he believes there could be hundreds of victims, making the scope of this case "historic."
Note: For more along these lines, see concise summaries of deeply revealing news articles on sexual abuse by healthcare providers from reliable major media sources.
Dr. Phil called the migrant crisis at the southern border “out of control” during on appearance on Joe Rogan’s podcast — blasting the Biden administration for “paying money to take these children and sell them into sex slavery.” Phil McGraw, the former TV host, shared video footage of a conversation that he had with Brandon Judd, president of the National Border Patrol Council, during Tuesday’s episode of “The Joe Rogan Experience.” Judd told McGraw that US border authorities no longer had rapid DNA testing kits due to the massive influx of migrants that have poured into the country from Mexico. McGraw speculated that the lack of DNA testing could lead to minors being linked up with traffickers. “They come in with these addresses written on their bodies, written on their arm and we call up there and say, ‘Do you know so and so?’ ‘Yes, we’re waiting for them.’ ‘Okay, they’ll be on a plane or a bus’.” McGraw lashed out at President Biden and his administration for what he perceives as lax enforcement of immigration laws. “This is a weird thing they are doing. They’re just letting people come in, and the Red Cross and different groups are giving people maps, showing them how to do it, and encouraging it,” McGraw said. McGraw praised Texas for deploying agents to the border with Mexico. He said state law enforcement is a greater deterrent of illegal immigration than Customs and Border Protection.
Note: Watch a concerning interview with an investigative journalist exposing who's behind the large government-funded facilities housing thousands of undocumented children. A Department of Homeland Security whistleblower Aaron Stevenson is trying to stop the facilitation of child trafficking at the US border. Watch a 23-min video of his experience with this deeply concerning issue, including his investigation into a common pattern of criminals (many of them sex traffickers) across the world who become sponsors for unaccompanied children. Worst off, when he tried to track down who was monitoring and vetting the sponsors, he couldn't find any information about it. According to a report by The Center for Public Integrity, thousands have disappeared from sponsors' homes after the federal government placed them there. Why is this not being talked about on a mainstream level?
The disastrous situation at the US-Mexico border is, and has been, intentionally produced. Illegal crossings have risen to unprecedented levels. There is a bipartisan consensus about what must be done. Tellingly, the same “solution” is also being quietly rolled out at all American ports of entry that are not currently being “overrun”, such as airports. That solution, of course, is biometric surveillance, enabled by AI, facial recognition/biometrics and autonomous devices. This “solution” is not just being implemented throughout the United States as an alleged means of thwarting migrants, it is also being rapidly implemented throughout the world in apparent lockstep. Global policy agendas, ratified by nearly every country in the world ... seek both to restrict the extent of people’s freedom of movement and to surveil people’s movements ... through the global implementation of digital identity. The defense tech firm Anduril ... is one of the main beneficiaries of government contracts to build autonomous surveillance towers along the US-Mexico border, which are now also being rolled out along the US-Canada border. Anduril will create “a digital wall that is not a barrier so much as a web of all-seeing eyes, with intelligence to know what it sees.” While Anduril is one of the main companies building the “virtual wall,” they are not alone. General Dynamics, a defense firm deeply connected to organized crime, espionage scandals and corruption, has developed several hundred remote video surveillance systems (RVSS) towers for CBP while Google, another Big Tech firm with CIA connections, has been tapped by CBP to have its AI used in conjunction with Anduril’s towers, which also utilize Anduril’s own AI operating system known as Lattice.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
There are three basic problems with the CIA: its objectives, methods, and unaccountability. In effect, the CIA is a secret army of the U.S., capable of creating mayhem across the world with no accountability whatsoever. When President Dwight Eisenhower decided that Africa’s rising political star, democratically elected Patrice Lumumba of Zaire (now the Democratic Republic of Congo), was the “enemy,” the CIA conspired in his 1961 assassination, thus undermining the democratic hopes for Africa. The CIA has been held to serious public account just once, in 1975. In that year, Idaho Senator Frank Church led a Senate investigation that exposed the CIA’s shocking rampage of assassinations, coups, destabilization, surveillance, and Mengele-style torture and medical “experiments.” Since 1975, the CIA has run secretive operations backing Islamic jihadists in Afghanistan that utterly wrecked Afghanistan while giving rise to al-Qaeda. The CIA has likely run secretive operations in the Balkans against Serbia, in the Caucuses against Russia, and in Central Asia targeting China, all deploying CIA-backed jihadists. In the 2010s, the CIA ran deadly operations to topple Syria’s Bashir al-Assad, again with Islamic jihadists. For at least 20 years, the CIA has been deeply involved in fomenting the growing catastrophe in Ukraine, including the violent overthrow of Ukraine’s President Viktor Yanukovych in February 2014 that triggered the devastating war now engulfing Ukraine.
Note: Learn more about the rise of the CIA in our comprehensive Military-Intelligence Corruption Information Center. For more, see concise summaries of deeply revealing news articles on intelligence agency corruption from reliable major media sources.
An artist in the south of France says he's planning to destroy up to $45 million worth of art, including pieces by Rembrandt, Picasso, and Andy Warhol, if WikiLeaks founder Julian Assange dies in prison. Andrei Molodkin [said] that he put a collection of masterpieces that had been donated to him into a 29-ton safe hooked up to two barrels — one containing an acid powder and the other containing an accelerator — which, when pumped into the safe, will create a reaction strong enough to destroy all its contents. The project is called "Dead Man's Switch," and it is backed by Assange's wife, Stella. Assange is currently in jail in the U.K. awaiting his final appeal over extradition to the United States to face charges under the Espionage Act, which will take place later this month. WikiLeaks published thousands of leaked documents relating to the wars in Iraq and Afghanistan, and Assange is alleged to have conspired to obtain and disclose U.S. national defense information. Molodkin says that the safe will be hooked up to a 24-hour timer which must be reset every day or else it will trigger the release of the two barrel's corrosive substances inside. He says, each day, the timer will only be reset when someone "close to Assange" confirms he is alive. Assange's wife, Stella, says the project asks the question of "which is the greater taboo: destroying art or destroying human life? If democracy wins, the art will be preserved - as will Julian's life."
Note: The US prosecution of Assange undermines press freedom. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and media manipulation from reliable sources.
Despite its long history as part of conflicts, sexual violence is often not reported because of the trauma and shame it brings to survivors, their families and their wider communities. There has also been reticence among various authorities to speak out. Only in modern times, in the 1990s when wars broke out in Rwanda and Yugoslavia, did the United Nations begin to recognize sexual violence as ... a category of war crime. The specific term "conflict-related sexual violence," or CRSV, was first introduced in 2000 when the United Nations Security Council issued a resolution that launched the Women, Peace and Security Agenda. The U.N. defined the term as "rape, sexual slavery, forced prostitution, forced pregnancy, forced abortion, enforced sterilization, forced marriage and any other form of sexual violence of comparable gravity perpetrated against women, men, girls or boys that is directly or indirectly linked to a conflict." [CRSV] is widespread and is used as a tactic of war to assert dominance and power. "It can be just as traumatizing to see your daughter, your sister or your parents being raped in front of you," says [Dr. Ranit] Mishori. "Or you're forced to strip naked in front of soldiers or in the city square. People often carry this trauma without knowing it's an international crime and minimize what happened to them." For conflict resolution and peace building to be successful, survivors need to be included in the process. For some countries this method has already started to work. [In Colombia], they have built women into the peace process. It's not perfect — no peace is perfect — but it is progressive and it is intentional, and that is important. Intentional peace building must be inclusive of survivors of this form of violence.
Note: The public receives censored and sanitized versions of war from the government and the media. Yet in reality, unethical violations of domestic and international human rights law are common and often kept hidden during wartime. For more, see concise summaries of deeply revealing news articles on sexual abuse scandals from reliable major media sources.
A US court this week banned three weedkillers widely used in American agriculture, finding that the Environmental Protection Agency (EPA) broke the law in allowing them to be on the market. The ruling is specific to three dicamba-based weedkillers manufactured by Bayer, BASF and Syngenta, which have been blamed for millions of acres of crop damage and harm to endangered species and natural areas across the midwest and south. Discovery documents turned up in the litigation showed the companies knew that their dicamba weedkillers would probably lead to off-target crop damage. This is the second time a federal court has banned these weedkillers since they were introduced for the 2017 growing season. In 2020, the ninth circuit court of appeals issued its own ban, but months later the Trump administration reapproved the weedkilling products. But a federal judge in Arizona ruled on Monday that the EPA made a crucial error in reapproving dicamba, finding the agency did not post it for public notice and comment as required by law. US district judge David Bury wrote ... that it was a “very serious” violation and that if EPA had done a full analysis, it probably would not have made the same decision. Bury wrote that the EPA did not allow many people who are deeply affected by the weedkiller – including specialty farmers, conservation groups and more – to comment. “The evidence has shown that dicamba cannot be used without causing massive and unprecedented harm to farms as well as endangering plants and pollinators,” said George Kimbrell [with] the Center for Food Safety, which litigated the case.
Note: For more along these lines, see concise summaries of deeply revealing news articles on health and government corruption from reliable major media sources.
Look at the case of Lucas Bellamy. He had been arrested in Minnesota. Immediately before the arrest, he ate a bag of drugs in an effort to fool police into thinking that he didn’t have any. But he immediately began feeling sick. Jail officers took him to a local hospital, where he was treated. The doctors there told the jailers to return him to the hospital if he became ill again. He began vomiting as soon as he got back to his cell. By evening he was refusing food and crawling around his cell as a guard and nurse stood and watched him. By noon the next day, he was dead on the floor. The case of Brandon Clay Dodson is even worse. Dodson was arrested on a burglary charge and was being held in the local jail in Clayton, Alabama. He told a guard that several other prisoners had been beating him, and he asked to be moved into segregated housing for his own protection. He later told the guards in solitary that he wasn’t feeling well, but they ignored him. And a day after that, the 43-year-old was found dead in his bed. In a 104-page ruling, a federal judge in Louisiana ruled against the administrators of the Louisiana State Penitentiary at Angola, [highlighting] just a few of the untold number of medical horrors that prisoners suffer all the time there, including “a man denied medical attention four times during a stroke, leaving him blind and paralyzed; a man denied access to a specialist for four years while his throat cancer advanced; even a blind man denied a cane for 16 years.”
Note: John Kiriakou is a former CIA counter-terrorism officer and former senior investigator on the Senate Foreign Relations Committee. In 2015, investigations in Arizona, Florida, Maine, Minnesota, and New York uncovered escalating inmate deaths related to the use of for-profit medical services in prisons. A New York Times article about this was published but it quickly disappeared. For more along these lines, see concise summaries of deeply revealing news articles on prison system corruption from reliable major media sources.
Important Note: Explore our full index to key excerpts of revealing major media news articles on several dozen engaging topics. And don't miss amazing excerpts from 20 of the most revealing news articles ever published.