Privacy Media Articles
Below are key excerpts of revealing news articles on privacy and mass surveillance issues from reliable news media sources. If any link fails to function, a paywall blocks full access, or the article is no longer available, try these digital tools.
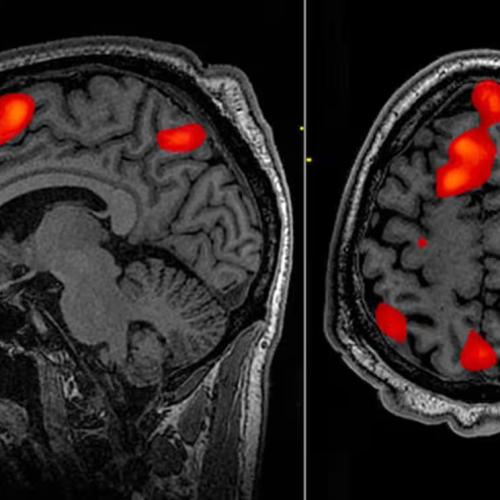
An AI-based decoder that can translate brain activity into a continuous stream of text has been developed, in a breakthrough that allows a person’s thoughts to be read non-invasively for the first time. The decoder could reconstruct speech with uncanny accuracy while people listened to a story – or even silently imagined one – using only fMRI scan data. Previous language decoding systems have required surgical implants. Large language models – the kind of AI underpinning OpenAI’s ChatGPT ... are able to represent, in numbers, the semantic meaning of speech, allowing the scientists to look at which patterns of neuronal activity corresponded to strings of words with a particular meaning rather than attempting to read out activity word by word. The decoder was personalised and when the model was tested on another person the readout was unintelligible. It was also possible for participants on whom the decoder had been trained to thwart the system, for example by thinking of animals or quietly imagining another story. Jerry Tang, a doctoral student at the University of Texas at Austin and a co-author, said: “We take very seriously the concerns that it could be used for bad purposes and have worked to avoid that. We want to make sure people only use these types of technologies when they want to and that it helps them.” Prof Tim Behrens, a computational neuroscientist ... said it opened up a host of experimental possibilities, including reading thoughts from someone dreaming.
Note: This technology has advanced considerably since Jose Delgado first stopped a charging bull using radio waves in 1965. For more along these lines, see concise summaries of deeply revealing news articles on mind control and the disappearance of privacy from reliable major media sources.
U.S. citizens are being subjected to a relentless onslaught from intrusive technologies that have become embedded in the everyday fabric of our lives, creating unprecedented levels of social and political upheaval. These widely used technologies ... include social media and what Harvard professor Shoshanna Zuboff calls "surveillance capitalism"—the buying and selling of our personal info and even our DNA in the corporate marketplace. But powerful new ones are poised to create another wave of radical change. Under the mantle of the "Fourth Industrial Revolution," these include artificial intelligence or AI, the metaverse, the Internet of Things, the Internet of Bodies (in which our physical and health data is added into the mix to be processed by AI), and my personal favorite, police robots. This is a two-pronged effort involving both powerful corporations and government initiatives. These tech-based systems are operating "below the radar" and rarely discussed in the mainstream media. The world's biggest tech companies are now richer and more powerful than most countries. According to an article in PC Week in 2021 discussing Apple's dominance: "By taking the current valuation of Apple, Microsoft, Amazon, and others, then comparing them to the GDP of countries on a map, we can see just how crazy things have become… Valued at $2.2 trillion, the Cupertino company is richer than 96% of the world. In fact, only seven countries currently outrank the maker of the iPhone financially."
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The Georgia Army National Guard plans to combine two deeply controversial practices — military recruiting at schools and location-based phone surveillance — to persuade teens to enlist, according to contract documents reviewed by The Intercept. The federal contract materials outline plans by the Georgia Army National Guard to geofence 67 different public high schools throughout the state, targeting phones found within a one-mile boundary of their campuses with recruiting advertisements “with the intent of generating qualified leads of potential applicants for enlistment while also raising awareness of the Georgia Army National Guard.” Geofencing refers generally to the practice of drawing a virtual border around a real-world area. The ad campaign will make use of a variety of surveillance advertising techniques, including capturing the unique device IDs of student phones, tracking pixels, and IP address tracking. It will also plaster recruiting solicitations across Instagram, Snapchat, streaming television, and music apps. The campaign plans not only call for broadcasting recruitment ads to kids at school, but also for pro-Guard ads to follow these students around as they continue using the internet and other apps, a practice known as retargeting. While the state’s plan specifies targeting only high school juniors and seniors ages 17 and above, demographic ad targeting is known to be error prone, and experts told The Intercept it’s possible the recruiting messages could reach the phones of younger children.
Note: For more along these lines, see concise summaries of deeply revealing news articles on military corruption and the disappearance of privacy from reliable major media sources.
A MintPress News investigation has found dozens of ex-U.S. State Department officials working in key positions at TikTok. Many more individuals with backgrounds in the FBI, CIA and other departments of the national security state also hold influential posts at the social media giant, affecting the content that over one billion users see. The influx of State Department officials into TikTok’s upper ranks is a consequence of “Project Texas,” an initiative the company began in 2020 in the hopes of avoiding being banned altogether in the United States. During his time in office, Secretary of State Mike Pompeo led the charge to shut the platform down, frequently labeling it a “spying app” and a “propaganda tool for the Chinese Communist Party.” It was widely reported that the U.S. government had forced the sale of TikTok to Walmart and then Microsoft. But in late 2020, as Project Texas began, those deals mysteriously fell through, and the rhetoric about the dangers of TikTok from officials evaporated. Project Texas is a $1.5 billion security operation to move the company’s data to Austin. In doing so, it announced that it was partnering with tech giant Oracle, a corporation that, as MintPress has reported on, is the CIA in all but name. Evidently, Project Texas also secretly included hiring all manner of U.S. national security state personnel to oversee the company’s operations – and not just from the State Department. Virtually every branch of the national security state is present at TikTok.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corruption in intelligence agencies and in the corporate world from reliable major media sources.
The U.S. Army Cyber Command told defense contractors it planned to surveil global social media use to defend the "NATO brand," according to a 2022 webinar recording reviewed by The Intercept. "NATO is one of our key brands that we are pushing, as far as our national security alliance," [Lt. Col. David Beskow] explained. The mass social media surveillance appears to be just one component of a broader initiative to use private-sector data mining to advance the Army's information warfare efforts. Beskow expressed an interest in purchasing access to nonpublic commercial web data, corporate ownership records, supply chain data, and more. While the U.S. national security establishment frequently warns against other countries' "weaponization" of social media and the broader internet, recent reporting has shown the Pentagon engages in some of the very same conduct. Researchers from Graphika and the Stanford Internet Observatory uncovered a network of pro-U.S. Twitter and Facebook accounts covertly operated by U.S. Central Command, an embarrassing revelation that led to a “sweeping audit of how it conducts clandestine information warfare." Despite years of alarm in Washington over the threat posed by deepfake video fabrications to democratic societies, The Intercept reported last month that U.S. Special Operations Command is seeking vendors to help them make their own deepfakes to deceive foreign internet users.
Note: For more along these lines, see concise summaries of deeply revealing news articles on military corruption and media manipulation from reliable sources.
A controversial facial recognition database, used by police departments across the nation, was built in part with 30 billion photos the company scraped from Facebook and other social media users without their permission. The company, Clearview AI, boasts of its potential for identifying rioters at the January 6 attack on the Capitol, saving children being abused or exploited, and helping exonerate people wrongfully accused of crimes. But critics point to privacy violations and wrongful arrests fueled by faulty identifications made by facial recognition, including cases in Detroit and New Orleans, as cause for concern over the technology. Once a photo has been scraped by Clearview AI, biometric face prints are made and cross-referenced in the database, tying the individuals to their social media profiles and other identifying information forever — and people in the photos have little recourse to try to remove themselves. CNN reported Clearview AI last year claimed the company's clients include "more than 3,100 US agencies, including the FBI and Department of Homeland Security." BBC reported Miami Police acknowledged they use the technology for all kinds of crimes, from shoplifting to murder. The risk of being included in what is functionally a "perpetual police line-up" applies to everyone, including people who think they have nothing to hide, [said] Matthew Guariglia, a senior policy analyst for the international non-profit digital rights group Electronic Frontier Fund.
Note: Read about the rising concerns of the use of Clearview AI technology in Ukraine, with claims to help reunite families, identify Russian operatives, and fight misinformation. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The secret contract was finalized on Nov. 8, 2021, a deal between a company that has acted as a front for the United States government and the American affiliate of a notorious Israeli hacking firm. Under the arrangement, the Israeli firm, NSO Group, gave the U.S. government access to one of its most powerful weapons — a geolocation tool that can covertly track mobile phones around the world without the phone user’s knowledge or consent. Only five days earlier, the Biden administration had announced it was taking action against NSO, whose hacking tools for years had been abused by governments around the world to spy on political dissidents, human rights activists and journalists. The White House placed NSO on a Commerce Department blacklist, declaring the company a national security threat. The secret contract ... violates the Biden administration’s public policy, and still appears to be active. The contract, reviewed by The Times, stated that the “United States government” would be the ultimate user of the tool, although it is unclear which government agency authorized the deal and might be using the spyware. Elements of America’s expansive national security apparatus in recent years have bought the weapons, deployed them against drug traffickers, and have quietly pushed to consolidate control of them into the hands of the United States and its closest allies. The F.B.I. purchased access in 2019 to NSO’s most powerful hacking tool, known as Pegasus, which invades mobile phones and mines their contents.
Note: Read how journalists and activists have been targeted with NSO Group spyware. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Private thoughts may not be private for much longer, heralding a nightmarish world where political views, thoughts, stray obsessions and feelings could be interrogated and punished all thanks to advances in neurotechnology. In a new book, The Battle for Your Brain, Duke University bioscience professor Nita Farahany argues that such intrusions into the human mind by technology are so close that a public discussion is long overdue and lawmakers should immediately establish brain protections as it would for any other area of personal liberty. Farahany, who served on Barack Obama’s commission for the study of bioethical issues, believes that advances in neurotechnology mean that intrusions through the door of brain privacy, whether by way of military programs or by way of well-funded research labs at big tech companies, are at hand via brain-to-computer innovations like wearable tech. “All of the major tech companies have massive investments in multifunctional devices that have brain sensors in them,” Farahany said. “Neural sensors will become part of our everyday technology and a part of how we interact with that technology.” François du Cluzel, a project manager at Nato Act Innovation Hub, issued a report in November 2020 entitled Cognitive Warfare that, it said, “is not limited to the military or institutional world. Since the early 1990s, this capability has tended to be applied to the political, economic, cultural and societal fields.”
Note: Read more about these troubling developments. For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
Recent reports about the Secret Service and Immigration and Customs Enforcement playing fast and loose with rules regarding cellphone tracking and the FBI purchasing phone location data from commercial sources constitute an important wake-up call. They remind us that those handy mobile devices many people tote around are the most cost-effective surveillance system ever invented. "The United States Secret Service and U.S. Immigration and Customs Enforcement, Homeland Security Investigations (ICE HSI) did not always adhere to Federal statute and cellsite simulator (CSS) policies when using CSS during criminal investigations," the Department of Homeland Security's Office of the Inspector General reported last month. "Separately, ICE HSI did not adhere to Department privacy policies and the applicable Federal privacy statute when using CSS." The OIG report referred to the use of what is commonly called "stingray" technology—devices that simulate cellphone towers and trick phones within range into connecting and revealing their location. "They also gather information about the phones of countless bystanders who happen to be nearby," the ACLU warns. Even the most precise phone company location data remains available with court approval. The courts are currently mulling multiple cases involving "geofence warrants" whereby law enforcement seeks data not on individuals, but on whoever was carrying a device in a designated area at a specified time.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
The precise locations of the U.S. government’s high-tech surveillance towers along the U.S-Mexico border are being made public for the first time as part of a mapping project by the Electronic Frontier Foundation. While the Department of Homeland Security’s investment of more than a billion dollars into a so-called virtual wall between the U.S. and Mexico is a matter of public record, the government does not disclose where these towers are located, despite privacy concerns of residents of both countries — and the fact that individual towers are plainly visible to observers. The surveillance tower map is the result of a year’s work steered by EFF Director of Investigations Dave Maass. As border surveillance towers have multiplied across the southern border, so too have they become increasingly sophisticated, packing a panoply of powerful cameras, microphones, lasers, radar antennae, and other sensors. Companies like Anduril and Google have reaped major government paydays by promising to automate the border-watching process with migrant-detecting artificial intelligence. Opponents of these modern towers, bristling with always-watching sensors, argue the increasing computerization of border security will lead inevitably to the dehumanization of an already thoroughly dehumanizing undertaking. Nobody can say for certain how many people have died attempting to cross the U.S.-Mexico border in the recent age of militarization and surveillance. Researchers estimate that the minimum is at least 10,000 dead.
Note: As the article states, the Department of Homeland Security was "the largest reorganization of the federal government since the creation of the CIA and the Defense Department," and has resulted in U.S. taxpayers funding corrupt agendas that have led to massive human rights abuses. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
In March 2003, the newly christened Department of Homeland Security, or DHS, opened its doors. The department took everything from immigration enforcement and counterterrorism to airport security and disaster response under one gargantuan bureaucracy. Despite these wide-ranging missions, the department's unifying logic in the post 9/11 era has been to wage the so-called war on terror at home. The result has been systemic abuse of minority communities, a dangerous militarization of American life, and a massive waste of money that sapped resources from addressing the real threats to our homeland. DHS agencies have militarized U.S. streets, sending officers in tactical gear to respond to civilian protests and conducting surveillance of U.S. citizens engaged in constitutionally protected activities. There are stories of DHS drones surveilling Indigenous water and land protectors and DHS forces spying on Black Lives Matter protesters. DHS even monitored journalists who reported on the department's tactics. None of these abuses have come cheap. Since its founding in 2003, the U.S. has spent $1.4 trillion on the agency. That's more than seven times what the government spent over the same period on the Centers for Disease Control and Prevention (CDC), including the CDC's COVID-19 pandemic response—and more than five times more than on the Environmental Protection Agency. The [DHS] was supposed to be about making the U.S. safer. But it has failed.
Note: A thorough investigation reveals details on the DHS "Disinformation Governance Board," an unsuccessful effort in 2022 to police online speech it considers inaccurate and dangerous. Now, the DHS board and its key subcommittees are undergoing sweeping changes as public concern grows over social media censorship and government overreach.
The United States Federal Bureau of Investigation has acknowledged for the first time that it purchased US location data rather than obtaining a warrant. The disclosure came today during a US Senate hearing. Senator Ron Wyden ... put the question of the bureau’s use of commercial data to its director, Christopher Wray: “Does the FBI purchase US phone-geolocation information?” Wray said his agency was not currently doing so. “To my knowledge, we do not currently purchase commercial database information that includes location data derived from internet advertising,” Wray said. “I understand that we previously—as in the past—purchased some such information for a specific national security pilot project. But that’s not been active for some time.” In its landmark Carpenter v. United States decision, the Supreme Court held that government agencies accessing historical location data without a warrant were violating the Fourth Amendment’s guarantee against unreasonable searches. The decision left open a glaring loophole that allows the government to simply purchase whatever it cannot otherwise legally obtain. US Customs and Border Protection (CBP) and the Defense Intelligence Agency are among the list of federal agencies known to have taken advantage of this loophole. The Department of Homeland Security ... purchased the geolocations of millions of Americans from private marketing firms. The data were derived from ... benign sources, such as mobile games and weather apps.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
The FBI and the Defense Department were actively involved in research and development of facial recognition software that they hoped could be used to identify people from video footage captured by street cameras and flying drones, according to thousands of pages of internal documents that provide new details about the government's ambitions to build out a powerful tool for advanced surveillance. The documents, revealed in response to an ongoing Freedom of Information Act lawsuit the American Civil Liberties Union filed against the FBI, show how closely FBI and Defense officials worked with academic researchers to refine artificial-intelligence techniques that could help in the identification or tracking of Americans without their awareness or consent. Many of the records relate to the Janus program, a project funded by the Intelligence Advanced Research Projects Agency, or IARPA. The improved facial recognition system was ultimately folded into a search tool, called Horus, and made available to the Pentagon's Combating Terrorism Technical Support Office, which helps provide military technologies to civilian police forces. No federal laws regulate how facial recognition systems can be used. The tool's use in domestic mass surveillance would be a "nightmare scenario," said Nathan Wessler, a deputy director at the ACLU. "It could give the government the ability to pervasively track as many people as they want for as long as they want. There's no good outcome for that in a democratic society."
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Caleb Kenyon, a defense attorney in Florida, saw a geofence warrant was when a new client received an alarming email from Google in January 2020. Police were requesting personal data from the client, Zachary McCoy, and Kenyon had just seven days to stop Google from turning it over, the email said. The geofence warrant included a map and GPS coordinates, and instructed Google to provide identifying information for every user whose device was found within the radius of that location at a certain date and time. “It was so bizarre that I just didn’t even have a concept for what I was dealing with,” he said. Kenyon is not alone. As tech firms build ever more sophisticated means of surveilling people and their devices – technology that law enforcement is eager to take advantage of – the legal community is scrambling to keep up. The National Association of Criminal Defense Lawyers (NACDL) ... recently created the Fourth Amendment Center, named for the constitutional right against unreasonable searches. The center is one of the few resources available for helping attorneys better understand how new technology is being used against their clients. It can be years before the defense community catches wind of the newest surveillance tools. Unlike other search warrants, geofence warrants don’t require probable cause or a specific suspect in mind; they gather information on anyone within the vicinity of an alleged crime. Advocates argue this violates the fourth amendment.
Note: For more along these lines, see concise summaries of deeply revealing news articles on court system corruption and the disappearance of privacy from reliable major media sources.
The recent launch of a new mobile phone service introduced significant new privacy protections into the mobile phone system. This exciting new approach highlights the failure of the existing mobile phone infrastructure to protect privacy, and points the way forward for a wide variety of technologies. Today’s cellphones are generally a privacy disaster. Partly that’s the result of the two companies that control the operating system software on the vast majority of the world’s pocket computers. In order for your carrier to route calls and data to your phone, the network needs to constantly know which cell tower your phone is near. And when you make a call or use data, the provider can see where that traffic is going. Cell carriers track and store this accidental byproduct of the technology in order to record people’s location history and network activity for marketing purposes and, in certain circumstances, for sharing with law enforcement. The new phone service, called Pretty Good Phone Privacy (PGPP), uses encryption techniques to deliberately blind itself so that it can’t know that the user of a mobile device is you, or what data you are sending from that phone. You connect to the PGPP service for payment, and that’s all. With PGPP’s approach, the carrier simply does not have the data to turn over to anyone. It cannot be sold, leaked, or hacked, let alone offered to overreaching law enforcement agencies. Verizon, T-Mobile, AT&T, and their smaller competitors could be offering such a privacy-protecting service, but don’t want to.
Note: Explore a treasure trove of concise summaries of incredibly inspiring news articles which will inspire you to make a difference.
The fingerprints of unvaccinated New York City teachers were reportedly sent to the FBI with "problem code" flags, prompting outrage from former educators who lost their jobs over the mandate. Earlier this month, John Bursch, who is representing teachers who are suing the city over the mandate, said teachers who refused the shot now have a "flag in their file," which will impact their ability to get another job. "When the city puts these problem codes on employees who have been terminated because of their unconstitutional policies, not only do they have this flag in their files, but their fingerprints are sent with that flag to the FBI and the New York Criminal Justice Services, so it impacts their ongoing ability to get employment at other places," Bursch said Feb. 8. Investigative journalist Betsy Combier wrote an affidavit uncovering how the Education Department was allegedly able to "flag" certain teachers without sufficient evidence of wrongdoing. "I found out that the DOE has right now an agency called the Office of Personnel Investigation, and what they do is they have employees of the DOE who, forgive me, call themselves investigators, but they're not," Combier said. "So they work for OPI, and when they get an accusation from anybody, it doesn't matter who, well, the principals send it to them, but the original complaint against somebody could be made by anybody that this employee, that employee did something wrong."
Note: For more along these lines, see concise summaries of deeply revealing news articles on coronavirus vaccines from reliable major media sources.
A study published Monday ... outlines how expansive the market for people’s health data has become. After contacting data brokers to ask what kinds of mental health information she could buy, researcher Joanne Kim reported that she ultimately found 11 companies willing to sell bundles of data that included information on what antidepressants people were taking, whether they struggled with insomnia or attention issues, and details on other medical ailments, including Alzheimer’s disease or bladder-control difficulties. Some of the data was offered in an aggregate form that would have allowed a buyer to know, for instance, a rough estimate of how many people in an individual Zip code might be depressed. But other brokers offered personally identifiable data featuring names, addresses and incomes, with one data-broker sales representative pointing to lists named “Anxiety Sufferers” and “Consumers With Clinical Depression in the United States.” Some even offered a sample spreadsheet. The Health Insurance Portability and Accountability Act, known as HIPAA, restricts how hospitals, doctors’ offices and other “covered health entities” share Americans’ health data. But the law doesn’t protect the same information when it’s sent anywhere else, allowing app makers and other companies to legally share or sell the data. Some of the data brokers offered ... opt-out forms. But ... many people probably didn’t realize the brokers had collected their information in the first place. Privacy advocates have for years warned about the unregulated data trade, saying the information could be exploited by advertisers or misused for predatory means. The health-data issue has in some ways gotten worse, in large part because of the increasing sophistication with which companies can collect and share people’s personal information — including not just in defined lists, but through regularly updated search tools and machine-learning analyses.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
New details about the FBI’s failures to comply with restrictions on the use of foreign intelligence for domestic crimes have emerged. Section 702 of the Foreign Intelligence Surveillance Act (FISA) ... grants the government the ability to intercept the electronic communications of overseas targets who are unprotected by the Fourth Amendment. That authority is set to expire at the end of the year. But errors in the FBI’s secondary use of the data—the investigation of crimes on US soil—are likely to inflame an already fierce debate over whether law enforcement agents can be trusted with such an invasive tool. Central to this tension has been a routine audit by the Department of Justice’s (DOJ) national security division and the office of the director of national intelligence (ODNI) ... which unearthed new examples of the FBI failing to comply with rules limiting access to intelligence ostensibly gathered to protect US national security. Such “errors,” they said, have occurred on a “large number” of occasions. A report on the audit, only recently declassified, found that in the first half of 2020, FBI personnel unlawfully searched raw FISA data on numerous occasions. In one incident, agents reportedly sought evidence of foreign influence linked to a US lawmaker. In another, an inappropriate search pertained to a local political party. In what privacy and civil liberties lawyers have termed a “backdoor search,” the FBI regularly searches through unminimized data during investigations, and routinely prior to launching them.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
The reptilian annual World Economic Forum at Davos, where the masters of the universe meet to congratulate themselves on their benevolent dictatorship, is home to many sinister ideas. This year, one of the creepiest discussions of all was delivered under the guise of progress and productivity. Nita Farahany, a Duke University professor and futurist, gave a presentation at Davos about neurotechnology that is creating “brain transparency.” The new technologies, which Farahany says are being deployed in workplaces around the world ... include a variety of wearable sensors that read the brain’s electrical impulses and can show how fatigued you are, whether you’re focused on the task at hand or if your attention is wandering. According to Farahany, thousands of companies have hooked workers ranging from train drivers to miners up to these devices already, in the name of workplace safety. But what we are really discussing is workplace surveillance. Farahany paints a picture of a near future in which every office worker could be fitted with a small wearable that would constantly record brain activity, creating an omnipotent record of your thoughts, attention and energy that the boss could study at leisure. Farahany acknowledges that there could be drawbacks here: “Done poorly, it could become the most oppressive technology we’ve ever introduced on a wide scale.” All of this raises the question: what exactly is your employer buying when they give you a paycheck? For bosses, the answer is simple: “Everything.”
Note: Tune into a fascinating, 17 min. conversation about this issue that raises important questions about the overreliance on technology as a tool of control, under the guise of workplace safety. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption from reliable major media sources.
The US government’s new mobile app for migrants to apply for asylum at the US-Mexico border is blocking many Black people from being able to file their claims because of facial recognition bias in the tech, immigration advocates say. The app, CBP One, is failing to register many people with darker skin tones, effectively barring them from their right to request entry into the US. People who have made their way to the south-west border from Haiti and African countries, in particular, are falling victim to apparent algorithm bias in the technology that the app relies on. The government announced in early January that the new CBP One mobile app would be the only way migrants arriving at the border can apply for asylum and exemption from Title 42 restrictions. Racial bias in face recognition technology has long been a problem. Increasingly used by law enforcement and government agencies to fill databases with biometric information including fingerprints and iris scans, a 2020 report by Harvard University called it the “least accurate” identifier, especially among darker-skinned women with whom the error rate is higher than 30%. Emmanuella Camille, a staff attorney with the Haitian Bridge Alliance ... said the CBP One app has helped “lighter-skin toned people from other nations” obtain their asylum appointments “but not Haitians” and other Black applicants. Besides the face recognition technology not registering them ... many asylum seekers have outdated cellphones – if they have cellphones at all – that don’t support the CBP One app.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the erosion of civil liberties from reliable major media sources.
Important Note: Explore our full index to key excerpts of revealing major media news articles on several dozen engaging topics. And don't miss amazing excerpts from 20 of the most revealing news articles ever published.