Privacy News Stories
Below are key excerpts of revealing news articles on privacy and mass surveillance issues from reliable news media sources. If any link fails to function, a paywall blocks full access, or the article is no longer available, try these digital tools.
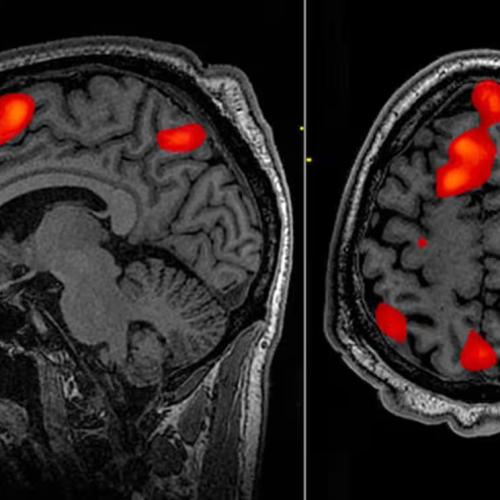
Mental health apps have become increasingly common over the past few years, particularly due to the rise in telehealth during the coronavirus pandemic. However, there's a problem: Data privacy is being compromised in the process. In 2023 the Federal Trade Commission ordered the mental health platform BetterHelp, which is owned by Teladoc (TDOC), to pay a $7.8 million fine to consumers for sharing their mental health data for advertising purposes with Facebook (META) and Snapchat (SNAP) after previously promising to keep the information private. Cerebral, a telehealth startup, admitted last year to exposing sensitive patient information to companies like Google (GOOG, GOOGL), Meta, TikTok, and other third-party advertisers. This info included patient names, birth dates, insurance information, and the patient's responses to mental health self-evaluations through the app. Overall, according to the Mozilla Foundation’s Privacy Not Included online buyer’s guide, only two out of the 27 mental health apps available to users met Mozilla's privacy and security standards in 2023. A December 2022 study of 578 mental health apps published in the Journal of the American Medical Association found that 44% shared data they collected with third parties. A February 2023 report from Duke University found that out of 37 different data brokers that researchers contacted ... firms “were ultimately willing and able to sell the requested mental health data.”
Note: For more along these lines, see concise summaries of deeply revealing news articles on health and the disappearance of privacy from reliable major media sources.
Finances at the vaccine manufacturer Moderna began to fall almost as quickly as they had risen, as most Americans resisted getting yet another COVID booster shot. In a September call aimed at shoring up investors, Moderna’s then-chief commercial officer, Arpa Garay, attributed some of the hesitancy pummeling Moderna's numbers to uninformed vaccine skeptics. What Garay hinted at during the call, but didn’t disclose, was that Moderna already had a sprawling media operation in place aimed at identifying and responding to critics of vaccine policy and the drug industry. Internal company reports and communications ... show that Moderna has worked with former law enforcement and public health officials and a drug industry-funded non-governmental organization called The Public Good Projects (PGP) to confront the “root cause of vaccine hesitancy” by rapidly identifying and “shutting down misinformation.” Part of this effort includes providing talking points to some 45,000 healthcare professionals “on how to respond when vaccine misinformation goes mainstream.” PGP routinely sent Excel lists of accounts to amplify on Twitter and others to de-platform, including populist voices such as ZeroHedge. The messages also suggested emerging narratives to remove from the platform. The growing network these efforts rely on shows the growth of what has been called the censorship industrial complex.
Note: Learn more about Moderna's misinformation department. For more along these lines, see concise summaries of deeply revealing news articles on pharmaceutical industry corruption and media manipulation from reliable sources.
American Amara Majeed was accused of terrorism by the Sri Lankan police in 2019. Robert Williams was arrested outside his house in Detroit and detained in jail for 18 hours for allegedly stealing watches in 2020. Randal Reid spent six days in jail in 2022 for supposedly using stolen credit cards in a state he’d never even visited. In all three cases, the authorities had the wrong people. In all three, it was face recognition technology that told them they were right. Law enforcement officers in many U.S. states are not required to reveal that they used face recognition technology to identify suspects. Surveillance is predicated on the idea that people need to be tracked and their movements limited and controlled in a trade-off between privacy and security. The assumption that less privacy leads to more security is built in. That may be the case for some, but not for the people disproportionately targeted by face recognition technology. As of 2019, face recognition technology misidentified Black and Asian people at up to 100 times the rate of white people. In 2018 ... 28 members of the U.S. Congress ... were falsely matched with mug shots on file using Amazon’s Rekognition tool. Much early research into face recognition software was funded by the CIA for the purposes of border surveillance. More recently, private companies have adopted data harvesting techniques, including face recognition, as part of a long practice of leveraging personal data for profit.
Note: For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
Facial recognition has become a security feature of choice for phones, laptops, passports, and payment apps. Yet it is also, increasingly, a tool of state oppression and corporate surveillance. Immigration and Customs Enforcement and the FBI have deployed the technology as a digital dragnet, searching for suspects among millions of faces in state driver’s license databases, sometimes without first seeking a court order. In early 1963, [Woody Bledsoe] proposed to conduct “a study to determine the feasibility of a simplified facial recognition machine.” A recently declassified history of the CIA’s Office of Research and Development mentions just such a project in 1965; that same year, Woody sent a letter on facial recognition to John W. Kuipers, the division’s chief of analysis. In 1967 ... Woody took on one last assignment that involved recognizing patterns in the human face. The purpose of the experiment was to help law enforcement agencies quickly sift through databases of mug shots and portraits, looking for matches. As before, funding for the project appears to have come from the US government. A 1967 document declassified by the CIA in 2005 mentions an “external contract” for a facial-recognition system that would reduce search time by a hundredfold. Woody’s work set an ethical tone for research on facial recognition that has been enduring and problematic. The potential abuses of facial-recognition technology were apparent almost from its birth.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Apple has said it now requires a judge’s order to hand over information about its customers’ push notification to law enforcement, putting the iPhone maker’s policy in line with rival Google and raising the hurdle officials must clear to get app data about users. It follows the revelation from Oregon Senator Ron Wyden that officials were requesting such data from Apple as well as from Google. Apps of all kinds rely on push notifications to alert smartphone users to incoming messages, breaking news, and other updates. These are the audible “dings” or visual indicators users get when they receive an email or their sports team wins a game. What users often do not realize is that almost all such notifications travel over Google and Apple’s servers. In a letter first disclosed by Reuters last week, Wyden said the practice gave the two companies unique insight into traffic flowing from those apps to users, putting them “in a unique position to facilitate government surveillance of how users are using particular apps.” Apple and Google both acknowledged receiving such requests. Apple added a passage to its guidelines saying such data was available “with a subpoena or greater legal process.” The passage has now been updated to refer to more stringent warrant requirements. Wyden said in a statement that Apple was “doing the right thing by matching Google and requiring a court order to hand over push notification related data.”
Note: Read more about the controversial geofence warrants that use Big Tech data. As an older article about the Apple court order articulates, law enforcement can "intercept your messages, access your health records or financial data, track your location, or even access your phone’s microphone or camera without your knowledge." For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
For the past two weeks, I’ve been using a new camera to secretly snap photos and record videos of strangers in parks, on trains, inside stores and at restaurants. I was testing the recently released $300 Ray-Ban Meta glasses that Mark Zuckerberg’s social networking empire made in collaboration with the iconic eyewear maker. The high-tech glasses include a camera for shooting photos and videos, and an array of speakers and microphones for listening to music and talking on the phone. The glasses, Meta says, can help you “live in the moment” while sharing what you see with the world. Meta, Apple and Magic Leap have all been hyping mixed-reality headsets that use cameras to allow their software to interact with objects in the real world. To inform people that they are being photographed, the Meta Ray-Bans include a tiny LED light embedded in the right frame to indicate when the device is recording. When a photo is snapped, it flashes momentarily. When a video is recording, it is continuously illuminated. As I shot 200 photos and videos with the glasses in public, including on BART trains, on hiking trails and in parks, no one looked at the LED light or confronted me about it. And why would anyone? It would be rude to comment on a stranger’s glasses, let alone stare at them. The ubiquity of smartphones, doorbell cameras and dashcams makes it likely that you are being recorded anywhere you go. But Chris Gilliard, an independent privacy scholar who has studied the effects of surveillance technologies, said cameras hidden inside smart glasses would most likely enable bad actors — like the people shooting sneaky photos of others at the gym — to do more harm.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
Under ... Section 702 [of the Foreign Intelligence Surveillance Act], the US government collects hundreds of millions of phone calls, emails, and text messages each year. An inestimable chunk belongs to American citizens, permanent residents, and others in the United States neither suspected nor accused of any crime. Police and intelligence agencies buy their way around the Fourth Amendment by paying US companies for information that they’d otherwise demand a warrant to disclose. The House Intelligence Committee’s bill—the FISA Reform and Reauthorization Act, or FRRA—does nothing to address this privacy threat. What the FRRA does appear to do, despite its name, is explode the number of companies the US government may compel to cooperate with wiretaps under Section 702. That was the assessment on Friday of Marc Zwillinger, amicus curiae to the Foreign Intelligence Surveillance Court of Review (FISCR). Section 702 currently allows the government to compel a class of companies called “electronic communications providers” to collect communications. If the FRRA becomes law, according to Zwillinger, that category would be greatly expanded to include a slew of new businesses, including “data centers, colocation providers, business landlords, and shared workspaces,” as well as, he says, “hotels where guests connect to the internet.” Communications may be seized under 702 and only years later dug up for an entirely different reason.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
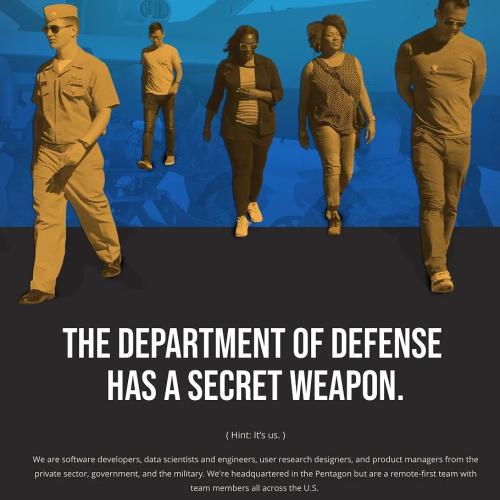
Palantir’s founding team, led by investor Peter Thiel and Alex Karp, wanted to create a company capable of using new data integration and data analytics technology — some of it developed to fight online payments fraud — to solve problems of law enforcement, national security, military tactics, and warfare. Palantir, founded in 2003, developed its tools fighting terrorism after September 11, and has done extensive work for government agencies and corporations though much of its work is secret. Palantir’s MetaConstellation platform allows the user to task ... satellites to answer a specific query. Imagine you want to know what is happening in a certain location and time in the Arctic. Click on a button and MetaConstelation will schedule the right combination of satellites to survey the designated area. The platform is able to integrate data from multiple and disparate sources — think satellites, drones, and open-source intelligence — while allowing a new level of decentralised decision-making. Just as a deep learning algorithm knows how to recognise a picture of a dog after some hours of supervised learning, the Palantir algorithms can become extraordinarily apt at identifying an enemy command and control centre. Alex Karp, Palantir’s CEO, has argued that “the power of advanced algorithmic warfare systems is now so great that it equates to having tactical nuclear weapons against an adversary with only conventional ones.”
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The Palestinian population is intimately familiar with how new technological innovations are first weaponized against them–ranging from electric fences and unmanned drones to trap people in Gaza—to the facial recognition software monitoring Palestinians in the West Bank. Groups like Amnesty International have called Israel an Automated Apartheid and repeatedly highlight stories, testimonies, and reports about cyber-intelligence firms, including the infamous NSO Group (the Israeli surveillance company behind the Pegasus software) conducting field tests and experiments on Palestinians. Reports have highlighted: “Testing and deployment of AI surveillance and predictive policing systems in Palestinian territories. In the occupied West Bank, Israel increasingly utilizes facial recognition technology to monitor and regulate the movement of Palestinians. Israeli military leaders described AI as a significant force multiplier, allowing the IDF to use autonomous robotic drone swarms to gather surveillance data, identify targets, and streamline wartime logistics.” The Palestinian towns and villages near Israeli settlements have been described as laboratories for security solutions companies to experiment their technologies on Palestinians before marketing them to places like Colombia. The Israeli government hopes to crystalize its “automated apartheid” through the tokenization and privatization of various industries and establishing a technocratic government in Gaza.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
The nation’s largest pharmacy chains have handed over Americans’ prescription records to police and government investigators without a warrant, a congressional investigation found, raising concerns about threats to medical privacy. Though some of the chains require their lawyers to review law enforcement requests, three of the largest — CVS Health, Kroger and Rite Aid, with a combined 60,000 locations nationwide — said they allow pharmacy staff members to hand over customers’ medical records in the store. Pharmacies’ records hold some of the most intimate details of their customers’ personal lives, including years-old medical conditions and the prescriptions they take for mental health and birth control. Because the chains often share records across all locations, a pharmacy in one state can access a person’s medical history from states with more-restrictive laws. The Health Insurance Portability and Accountability Act, or HIPAA, regulates how health information is used and exchanged among “covered entities” such as hospitals and doctor’s offices. But the law gives pharmacies leeway as to what legal standard they require before disclosing medical records to law enforcement. In briefings, officials with eight American pharmacy giants — Walgreens Boots Alliance, CVS, Walmart, Rite Aid, Kroger, Cigna, Optum Rx and Amazon Pharmacy — told congressional investigators that they required only a subpoena, not a warrant, to share the records.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The annual “Trouble in Toyland” report, produced by the U.S. Public Interest Research Group (PIRG) and released before the holiday season, historically has focused on safety hazards found in traditional children’s toys. According to the 38th annual “Trouble in Toyland” report, released in mid-November, “Toys that spy on children are a growing threat.” The threats “stem from toys with microphones, cameras and trackers, as well as recalled toys, water beads, counterfeits and Meta Quest VR headsets.” “The riskiest features of smart toys are those that can collect information, especially without our knowledge or used in a way that parents didn’t agree to,” said Teresa Murray, Consumer Watchdog at the U.S. PIRG Education Fund and author of the report. “It’s chilling to learn what some of these toys can do,” Murray said. Smart toys include “stuffed animals that listen and talk, devices that learn their habits, games with online accounts, and smart speakers, watches, play kitchens and remote cars that connect to apps or other technology,” according to PIRG. Smart toys can pose the risk of data breaches, hacking, potential violations of children’s privacy laws such as the Children’s Online Privacy Protection Act of 1998 (COPPA), and exposure to “inappropriate or harmful material without proper filtering and parental controls.” According to PIRG, “We don’t know with certainty when our child plays with a connected toy that the company isn’t recording us or collecting our data.”
Note: A 2015 New York Times article called smart objects a "trainwreck in privacy and security." For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
In the 1970s, congressional investigators revealed that the FBI, NSA, and CIA had spent decades illegally surveilling and harassing the civil rights and anti-war movements. These abuses shocked the American public and led Congress to implement a series of intelligence reforms, including the Foreign Intelligence Surveillance Act (FISA), which set strict limitations on when and how intelligence agencies could perform domestic spying. In the decades since the 9/11 attacks, changing laws and aggressive executive branch lawyering have significantly relaxed the rules that govern surveillance of Americans. We are once again seeing abuses of these powers, including instances of intelligence agents seeking access to the communications of politicians, protesters, and journalists. Today, a bipartisan group of lawmakers ... introduced the Government Surveillance Reform Act of 2023 (GSRA) to reverse this erosion of privacy rights. The GSRA begins by tackling Section 702, a controversial surveillance law that expires at the end of this year. Section 702 allows the government to collect the communications of non-Americans located abroad without a warrant. But Americans’ private phone calls, emails, and text messages are inevitably captured, too — and intelligence officials frequently perform warrantless searches for them. Intelligence officials conducted more than 200,000 of these “backdoor searches” for Americans’ communications last year alone.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
The Department of Homeland Security (DHS) is likely the single largest collector and consumer in the U.S. government of detailed, often intimate, information about Americans and foreigners alike. The department stores and analyzes this information using vast data systems to determine who can enter the country and who is subjected to intrusive inspections, including by parsing through travel records, social media data, non-immigrant visa applications, and other information to detect patterns of behavior that the department has determined are worthy of scrutiny. As we explain in a new Brennan Center report, these systems ... are too often deployed in discriminatory ways that violate Americans’ constitutional rights and civil liberties. It is past time for DHS to stop improvising how it designs and implements its automated systems, with inadequate mechanisms for evaluation and oversight, weak standards, and disproportionate impacts on marginalized communities and individuals. DHS must disclose additional information about its systems, including the policies that govern their operations and reports explaining how they are used. An independent body should undertake a rigorous investigation of DHS’s automated systems, evaluating whether they are useful and accurate, assessing how they function, and determining whether they contain sufficient safeguards to protect privacy, civil rights, and civil liberties.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
OpenAI was created as a non-profit-making charitable trust, the purpose of which was to develop artificial general intelligence, or AGI, which, roughly speaking, is a machine that can accomplish, or surpass, any intellectual task humans can perform. It would do so, however, in an ethical fashion to benefit “humanity as a whole”. Two years ago, a group of OpenAI researchers left to start a new organisation, Anthropic, fearful of the pace of AI development at their old company. One later told a reporter that “there was a 20% chance that a rogue AI would destroy humanity within the next decade”. One may wonder about the psychology of continuing to create machines that one believes may extinguish human life. The problem we face is not that machines may one day exercise power over humans. That is speculation unwarranted by current developments. It is rather that we already live in societies in which power is exercised by a few to the detriment of the majority, and that technology provides a means of consolidating that power. For those who hold social, political and economic power, it makes sense to project problems as technological rather than social and as lying in the future rather than in the present. There are few tools useful to humans that cannot also cause harm. But they rarely cause harm by themselves; they do so, rather, through the ways in which they are exploited by humans, especially those with power.
Note: Read how AI is already being used for war, mass surveillance, and questionable facial recognition technology.
A surveillance program now known as Data Analytical Services (DAS) has for more than a decade allowed federal, state, and local law enforcement agencies to mine the details of Americans’ calls, analyzing the phone records of countless people who are not suspected of any crime, including victims. Using a technique known as chain analysis, the program targets not only those in direct phone contact with a criminal suspect but anyone with whom those individuals have been in contact as well. The DAS program, formerly known as Hemisphere, is run in coordination with the telecom giant AT&T, which captures and conducts analysis of US call records for law enforcement agencies, from local police and sheriffs’ departments to US customs offices and postal inspectors across the country, according to a White House memo reviewed by WIRED. Records show that the White House has provided more than $6 million to the program, which allows the targeting of the records of any calls that use AT&T’s infrastructure—a maze of routers and switches that crisscross the United States. Documents released under public records laws show the DAS program has been used to produce location information on criminal suspects and their known associates, a practice deemed unconstitutional without a warrant in 2018. Orders targeting a nexus of individuals are sometimes called “community of interest” subpoenas, a phrase that among privacy advocates is synonymous with dragnet surveillance.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
The Moderna misinformation reports, reported here for the first time, reveal what the pharmaceutical company is willing to do to shape public discourse around its marquee product. The mRNA COVID-19 vaccine catapulted the company to a $100 billion valuation. Behind the scenes, the marketing arm of the company has been working with former law enforcement officials and public health officials to monitor and influence vaccine policy. Key to this is a drug industry-funded NGO called Public Good Projects. PGP works closely with social media platforms, government agencies and news websites to confront the “root cause of vaccine hesitancy” by rapidly identifying and “shutting down misinformation.” A network of 45,000 healthcare professionals are given talking points “and advice on how to respond when vaccine misinformation goes mainstream”, according to an email from Moderna. An official training programme, developed by Moderna and PGP, alongside the American Board of Internal Medicine, [helps] healthcare workers identify medical misinformation. The online course, called the “Infodemic Training Program”, represents an official partnership between biopharma and the NGO world. Meanwhile, Moderna also retains Talkwalker which uses its “Blue Silk” artificial intelligence to monitor vaccine-related conversations across 150 million websites in nearly 200 countries. Claims are automatically deemed “misinformation” if they encourage vaccine hesitancy. As the pandemic abates, Moderna is, if anything, ratcheting up its surveillance operation.
Note: Strategies to silence and censor those who challenge mainstream narratives enable COVID vaccine pharmaceutical giants to downplay the significant, emerging health risks associated with the COVID shots. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
New Yorkers may have noticed an unwelcome guest hovering round their parties. In the lead-up to Labour Day weekend the New York Police Department (NYPD) said that it would use drones to look into complaints about festivities, including back-yard gatherings. Snooping police drones are an increasingly common sight in America. According to a recent survey by researchers at the Northwestern Pritzker School of Law, about a quarter of police forces now use them. Among the NYPD’s suppliers is Skydio, a Silicon Valley firm that uses artificial intelligence (AI) to make drones easy to fly. The NYPD is also buying from BRINC, another startup, which makes flying machines equipped with night-vision cameras that can smash through windows. Facial-recognition software is now used more widely across America, too, with around a tenth of police forces having access to the technology. A report released in September by America’s Government Accountability Office found that six federal law-enforcement agencies, including the FBI and the Secret Service, were together executing an average of 69 facial-recognition searches every day. Among the top vendors listed was Clearview AI. Surveillance capabilities may soon be further fortified by generative AI, of the type that powers ChatGPT, thanks to its ability to work with “unstructured” data such as images and video footage. The technology will let users “search the Earth for objects”, much as Google lets users search the internet.
Note: For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
During a Senate briefing last week, a federal counterterrorism official cited the October 7 Hamas attack while urging Congress to reauthorize a sprawling and controversial surveillance program repeatedly used to spy on U.S. citizens on U.S. soil. “As evidenced by the events of the past month, the terrorist threat landscape is highly dynamic and our country must preserve [counterterrorism] fundamentals to ensure constant vigilance,” said Director of the National Counterterrorism Center Christine Abizaid. She pointed to Section 702 of the Foreign Intelligence Surveillance Act, which enables the U.S. government to gather vast amounts of intelligence — including about U.S. citizens ... without first seeking a warrant. Section 702 “provides key indications and warning on terrorist plans and ... gives us strategic insight into foreign terrorists and their networks overseas,” Abizaid said. “I respectfully urge Congress to reauthorize this vital authority.” The controversial program is set to expire at the end of the year, and lawmakers sympathetic to the intelligence community are scrambling to protect it. Sean Vitka ... at the civil liberties group Demand Progress [said] that now is the time to enact lasting and dramatic oversight of the 702 authority. “The government has completely failed to demonstrate that any of the privacy protections reformers have called for would impair national security ... so now we’re seeing people grasping at straws trying to turn everything into an excuse for reauthorization,” Vitka said.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Silicon Valley techies are pretty sanguine about commercial surveillance. But they are much less cool about government spying. Government employees and contractors are pretty cool with state surveillance. But they are far less cool with commercial surveillance. What are they both missing? That American surveillance is a public-private partnership: a symbiosis between a concentrated tech sector that has the means, motive, and opportunity to spy on every person in the world and a state that loves surveillance as much as it hates checks and balances. The tech sector has powerful allies in government: cops and spies. No government agency could ever hope to match the efficiency and scale of commercial surveillance. Meanwhile, the private sector relies on cops and spies to go to bat for them, lobbying against new privacy laws and for lax enforcement of existing ones. Think of Amazon’s Ring cameras, which have blanketed entire neighborhoods in CCTV surveillance, which Ring shares with law enforcement agencies, sometimes without the consent or knowledge of the cameras’ owners. Ring marketing recruits cops as street teams, showering them with freebies to distribute to local homeowners. Google ... has managed to play both sides of the culture war with its location surveillance, thanks to the “reverse warrants” that cops have used to identify all the participants at both Black Lives Matter protests and the January 6 coup. Distinguishing between state and private surveillance is a fool’s errand.
Note: For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
As war in Ukraine continues, controversial defense contractors and adjacent companies like Palantir, Anduril, and Clearview AI are taking advantage to develop and level-up controversial AI-driven weapons systems and surveillance technologies. These organizations’ common link? The support of the controversial, yet ever-more powerful Silicon Valley billionaire Peter Thiel. Thiel-backed groups’ involvement in war serves to develop not only problematic and unpredictable weapons technologies and systems, but also apparently to advance and further interconnect a larger surveillance apparatus formed by Thiel and his elite allies’ collective efforts across the public and private sectors, which arguably amount to the entrenchment of a growing technocratic panopticon aimed at capturing public and private life. What’s more, Thiel’s funding efforts signal interest in developing expansive surveillance technologies, especially in the name of combatting “pre-crime” through “predictive policing” style surveillance. As an example, Thiel’s provided significant funds to Israeli intelligence-linked startup Carbyne911 (as did Jeffrey Epstein), which develops call-handling and call-identification capacities for emergency services, and has ... a predictive-policing component. Thiel also assisted in the development and subsequent privatized spinoffs of the US Government’s Defense Advanced Research Projects Agency’s (DARPA) Total Information Awareness project.
Note: Peter Thiel was also recently reported to be an FBI informant. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
Important Note: Explore our full index to revealing excerpts of key major media news stories on several dozen engaging topics. And don't miss amazing excerpts from 20 of the most revealing news articles ever published.