Privacy News Stories
Below are key excerpts of revealing news articles on privacy and mass surveillance issues from reliable news media sources. If any link fails to function, a paywall blocks full access, or the article is no longer available, try these digital tools.
The Federal Reserves little-known role housing the assets of other central banks comes with a unique benefit to the United States: It serves as a source of foreign intelligence for Washington. Senior officials from the U.S. Treasury and other government departments have turned to these otherwise confidential accounts several times a year to analyze the asset holdings of the central banks of Russia, China, Iraq, Turkey, Yemen, Libya and others, according to more than a dozen current and former senior Fed and Treasury officials. The U.S. central bank keeps a tight lid on information contained in these accounts. But according to the officials interviewed by Reuters, U.S. authorities regularly use a need to know confidentiality exception in the Feds service contracts with foreign central banks. Some 250 foreign central banks and governments keep $3.3 trillion of their assets at the Federal Reserve Bank of New York, about half of the worlds official dollar reserves, using a service advertised in a 2015 slide presentation as safe and confidential. Other major central banks and some commercial banks offer similar services. But only the Fed offers direct access to U.S. debt markets and to the worlds reserve currency, the dollar. In all, the people interviewed by Reuters identified seven instances in the last 15 years in which the accounts gave U.S. authorities insights into the actions of foreign counterparts or market movements, at times leading to a specific U.S. response.
Note: It's quite telling that no other major media picked up this important piece. For more along these lines, see concise summaries of deeply revealing news articles on financial industry corruption and the disappearance of privacy.
Under a secret Bush administration program initiated weeks after the Sept. 11 attacks, counterterrorism officials have gained access to financial records from a vast international database and examined banking transactions involving thousands of Americans and others in the United States. The program, run out of the Central Intelligence Agency and overseen by the Treasury Department ... is a significant departure from typical practice in how the government acquires Americans' financial records. Treasury officials did not seek individual court-approved warrants or subpoenas to examine specific transactions, instead relying on broad administrative subpoenas for millions of records. That access to large amounts of confidential data was highly unusual, several officials said, and stirred concerns inside the administration about legal and privacy issues. "The capability here is awesome or, depending on where you're sitting, troubling," said one former senior counterterrorism official who considers the program valuable. While tight controls are in place, the official added, "the potential for abuse is enormous." The program is separate from the National Security Agency's efforts to eavesdrop without warrants and collect domestic phone records, operations that have provoked fierce public debate and spurred lawsuits against the government and telecommunications companies.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
Regulators have approved the first drug with a sensor that alerts doctors when the medication has been taken. The digital pill combines two existing products: the former blockbuster psychiatric medication Abilify - long used to treat schizophrenia and bipolar disorder - with a sensor tracking system first approved in 2012. Experts say the technology could be a useful tool, but it will also change how doctors relate to their patients as theyre able to see whether they are following instructions. The pill has not yet been shown to actually improve patients medication compliance, a feature insurers are likely to insist on before paying for the pill. Additionally, patients must be willing to allow their doctors and caregivers to access the digital information. The technology carries risks for patient privacy, too, if there are breaches of medical data or unauthorized use as a surveillance tool, said James Giordano, a professor of neurology at Georgetown University Medical Center. Could this type of device be used for real-time surveillance? The answer is of course it could, said Giordano. The new pill, Abilify MyCite, is embedded with a digital sensor that is activated by stomach fluids, sending a signal to a patch worn by the patient and notifying a digital smartphone app that the medication has been taken.
Note: In 2010, it was quietly reported that Novartis AG would be seeking regulatory approval for such "chip-in-a-pill technology". For more along these lines, see concise summaries of deeply revealing news articles on microchip implants and the disappearance of privacy.
The Trump administration has declared all-out war on leakers. But the administration is battling the wrong enemy with the wrong weapons. Digital secrets stolen from the National Security Agency represent the real ... security problem. More than half a billion pages have been swiped. The stolen data includes some of the NSAs most prized cyber weapons. Most were created by the agencys own hacker team, the Tailored Access Operations (TAO) unit. Government hackers search for ways to crack into widely used computer operating systems, such as Microsoft Windows. When they discover a way in ... rather than notify the companies that their products are dangerously flawed, the NSA often secretly stores these vulnerabilities and later converts them into powerful cyber weapons, known as exploits. Like burglars tools, the exploits can secretly open a crack in a system, such as Windows, and insert an implant containing NSA malware - enabling the agency to take control of any computer using that Windows program. Unknown to the public, the NSA has for years been negligent in protecting its top-secret material, including these cyber weapons. Meanwhile, the Trump administration continues searching for someone who passed a few tidbits about White House bickering to a reporter, rather than focus on the NSA losing potentially deadly cyber weapons.
Note: In 2014, it was reported that the NSA was developing tools to make it relatively easy to hack millions of computers at once. Two years later, a large collection of NSA hacking tools was leaked. Now, these tools are being used by criminals against people all over the world. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
In 1982, long before most Americans ever had to think about warrantless eavesdropping, the journalist James Bamford published The Puzzle Palace: A Report on N.S.A., Americas Most Secret Agency, the first book to be written about the National Security Agency. In the book, Bamford describes the agency as free of legal restrictions while wielding technological capabilities for eavesdropping beyond imagination. He concludes with an ominous warning: Like an ever-widening sinkhole, N.S.A.s surveillance technology will continue to expand, quietly pulling in more and more communications and gradually eliminating more and more privacy. Three decades later, this pronouncement feels uncomfortably prescient: we were warned. Incredibly enough, the Department of Justice, under Jimmy Carter, complied with Bamfords Freedom of Information Act requests, supplying him with secret documents related to the Church Committee, the Senate group that, in 1975, investigated American intelligence agencies for potential transgression of their mandates. That the government would hand over sensitive information to Bamford predictably infuriated the N.S.A.; Reagan Administration lawyers tried to bully Bamford into ceding his goods, threatening him with the Espionage Act, while the N.S.A. attempted to sequester the documents hed uncovered. But because he was a lawyer, Bamford knew that he had done nothing wrong.
Note: As a producer for ABC News, Bamford was also the one who obtained startling declassified documents showing that the top Pentagon generals signed off on plans in the early 1960s to blow up a US ship in the Havana harbor or incite violent terrorism in US cities and blame it on Cuba. Strangely, ABC's article "U.S. Military Wanted to Provoke War With Cuba" was the only media report on this incredibly revealing document release. For more along these lines, see concise summaries of revealing news articles on intelligence agency corruption and the disappearance of privacy.
The FBI counterterrorism divisions identification of a movement it calls black identity extremists is the latest addition to the list of protesters and dissidents the agency puts under the domestic terrorism umbrella. But many national security experts say the designation [is] simply a label that allows the FBI to conduct additional surveillance on basically anyone whos black and politically active, said Michael German, who left the FBI in 2004. While the practice of labeling certain protest groups as domestic terrorists is not unique to President Trumps administration, Hina Shamsi ... at the American Civil Liberties Union, said theres concern that abusive and unjustified investigations by the FBI are rising. The problem, Shamsi said, is partly in the overly broad definition of domestic terrorism in the Patriot Act as a violation of the criminal laws ... intended to influence the policy of a government by intimidation or coercion. Eighty-four members of Congress cited that intention to intimidate or coerce in a letter to the Justice Department last week that asked whether the department had labeled Dakota Access Pipeline protesters domestic terrorists. The Justice Department did not respond to questions about the letter. The FBI report that focused on black identity extremists ... had interest groups questioning whether the designation has been used to single out members of Black Lives Matter.
Note: The Department of Homeland Security has reportedly been monitoring the Black Lives Matter movement since 2014, in some cases producing "minute-by-minute reports on protesters movements". For more along these lines, read about Cointelpro, the program used by corrupt intelligence agencies to spy on and attack the U.S. civil rights movement beginning in the 1960's. See also concise summaries of deeply revealing news articles about the erosion of civil liberties.
Trump administration lawyers are demanding the private account information of potentially thousands of Facebook users in three separate search warrants served on the social media giant. The warrants specifically target the accounts of three Facebook users who are described ... as "anti-administration activists who have spoken out at organized events, and who are generally very critical of this administration's policies." One of those users, Emmelia Talarico, operated the disruptj20 page where Inauguration Day protests were organized and discussed; the page was visited by an estimated 6,000 users whose identities the government would have access to if Facebook hands over the information. Talarico says if her account information was given to the government, officials would have access to her "personal passwords, security questions and answers, and credit card information," plus "the private lists of invitees and attendees to multiple political events." The American Civil Liberties Union, representing the three Facebook users, filed a motion to quash the warrants Thursday. "What is particularly chilling about these warrants is that anti-administration political activists are going to [be] scrutinized by the very administration they are protesting," said ACLU attorney Scott Michelman. Facebook was initially served the warrants in February 2017 along with a gag order which barred the social media company from alerting the three users that the government was seeking their private information.
Note: United Nations officials recently said that the US government's treatment of activists was increasingly "incompatible with US obligations under international human rights law". For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy.
When Bill Binney, former NSA analyst and head of the anti-terror ThinThread metadata program sits in front of you and says he is not afraid of the government, you have to admire him. A wheel-chair-bound U.S. serviceman who rose in the ranks of intelligence to work in top-secret NSA programs, Binney created ThinThread prior to September 11, 2001, and says it mathematically broke down all phone communications anywhere in the world without any infringement on Constitutional rights. The program was self-running. More important, it worked. In "A Good American," the new documentary from executive producer Oliver Stone ... audiences are taken on a tense and frightening ride through Binney and his colleagues' experience developing and deploying ThinThread in tests, only to see its funding pulled just weeks before 9/11 in favor of an expensive and ineffective ... program called Trailblazer. Binney contends that ThinThread would have identified the terrorists who planned and executed the 9/11 terror attacks, thereby preventing them from occurring. When ThinThread's plug was pulled, Binney and his team challenged their NSA bosses, and in the process found themselves at odds with the U.S. government and in a complex web of lies and corruption. Thus, when Binney said he remains unafraid of possible repercussions or retaliation tied to the film's thesis, it's not hard to believe. "What else can they do to me?" he asks. "They've already tried everything to stop me."
Note: Watch a free trailer or rent the whole documentary on this webpage. Read a revealing, detailed New York Times article on Oliver Stone and his profound work to expose corruption and manipulation through film. For more along these lines, see concise summaries of deeply revealing intelligence agency corruption news articles from reliable major media sources. Then explore the excellent, reliable resources provided in our 9/11 Information Center.
Years before anyone had ever heard of [Edward] Snowden, [Bill] Binney, a gifted cryptologist and mathematician, was pushing back against the NSAs spying overreach. In October 2001 ... he resigned rather than participate in a clandestine, massively overpriced and questionably legal electronic spying system code-named Trailblazer. Eventually, the government came after him. [Binney] was thrilled by [Oliver] Stones powerful biopic of Snowden, who astounded the world with his massive exposure of the NSAs global spying programs. "I think it will help people understand what is really going on behind the scenes. They are invading the privacy of everyone," he says. "They can turn on your cellphone and listen to you. They can turn on your camera and watch you." In 2013 ... James Clapper, the director of national intelligence, [lied] under oath during a congressional hearing about the NSAs spying programs. Snowden was watching. He had also seen what had happened to Binney and fellow NSA executives Thomas Drake, Ed Loomis and Kirk Wiebe, whose homes were raided by FBI agents after The New York Times exposed the NSAs secret spying programs in 2005. Drake, prosecuted under the 1917 Espionage Act, was eventually acquitted ... but his career was ruined. [Snowden's] critics insist he should have pursued his complaints internally, despite the persuasive examples of Binney and his comrades that such resistance is futile, even risky.
Note: Watch a free trailer or rent the whole documentary on this webpage. Read a revealing, detailed New York Times article on Oliver Stone and his profound work to expose corruption and manipulation through film. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
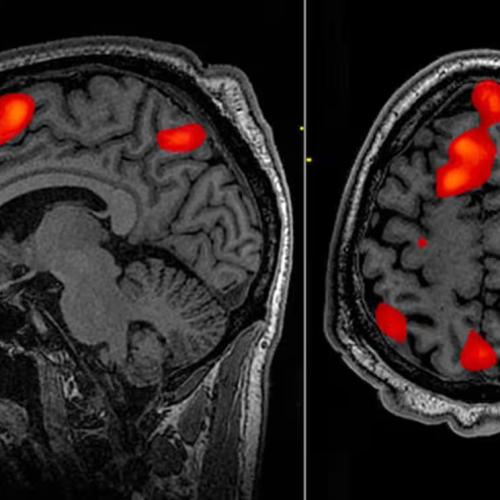
Two Stanford University researchers have reported startling accuracy in predicting sexual orientation using computer technology. Dr. Michal Kosinski and Yilun Wang, whose research will be published by the Journal of Personality and Social Psychology, say that AI can distinguish between the face of a heterosexual man and a homosexual man in 81 percent of cases. For women, the predictive accuracy is 71 percent. The average human is less adept at identifying between straight and gay people purely based on an image: We are only able to guess correctly in 61 percent of cases for men and 54 percent for women. When scientists presented the algorithm with five facial images of a single person, the accuracy increased to 91 percent for men and 83 percent for women. Kosinski and Wang used deep neural networks to sample 35,326 facial images of men and women taken from a dating website. The findings advance discussion about the biological factors that may determine ones sexual orientation. However, Kosinski tells The Economist, the research is not intended to be used to profile or out homosexual men and women. Rather, it is designed to demonstrate - or even warn - that technological advances can be used for such means and could pose a threat to our privacy, given that digital information is so easily accessible. The researchers argue the digitalization of our lives and rapid progress in AI continues to erode the privacy of sexual orientation and other intimate traits.
Note: Emerging artificial intelligence technologies are currently being developed for use in warfare. According to a United Nations report, misuse of these technologies may threaten human rights. For more along these lines, see concise summaries of deeply revealing privacy news articles from reliable major media sources.
The US government is seeking to unmask every person who visited an anti-Trump website in what privacy advocates say is an unconstitutional fishing expedition for political dissidents. The warrant appears to be an escalation of the Department of Justices (DoJ) campaign against anti-Trump activities, including the harsh prosecution of inauguration day protesters. On 17 July, the DoJ served a website-hosting company, DreamHost, with a search warrant for every piece of information it possessed that was related to a website that was used to coordinate protests during Donald Trumps inauguration. The warrant ... seeks to get the IP addresses of 1.3 million people who visited [the site], as well as the date and time of their visit and information about what browser or operating system they used. The warrant was made public Monday, when DreamHost announced its plans to challenge the government in court. The government has aggressively prosecuted activists arrested during the 20 January protests in Washington DC. In April, the US attorneys office in Washington DC filed a single indictment charging more than 217 people with identical crimes, including felony rioting. The Electronic Frontier Foundation, which has been advising DreamHost, characterized the warrant as unconstitutional. I cant conceive of a legitimate justification other than casting your net as broadly as possible, senior staff attorney Mark Rumold [said]. What they would be getting is a list of everyone who has ever been interested in attending these protests.
Note: In May, United Nations officials said that the US treatment of activists was increasingly "incompatible with US obligations under international human rights law". For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the erosion of privacy.
Google processes more than three billion search queries a day. It has altered our notions of privacy, tracking what we buy, what we search for online - and even our physical location at every moment of the day. It is a monopoly. So it matters how this company works - who it hires, who it fires and why. Last week, Google fired a software engineer for writing a memo that questioned the companys gender diversity policies and made statements about womens biological suitability for technical jobs. Portions of the memo violate our code of conduct and cross the line by advancing harmful gender stereotypes, Googles chief executive, Sundar Pichai, wrote. Its impossible to believe that Google or other large tech companies a few years ago would have reacted like this to such a memo. In 2011 when CNN filed a Freedom of Information Act request for the workplace diversity data on big tech companies, Google [asked] for its data to be excluded. Google began to disclose statistics [in 2014] showing that only 17 percent of its technical work force was female. Today Google is under growing scrutiny, and the cognitive dissonance between the outward-facing Dont be evil stance and the internal misogynistic brogrammer rhetoric was too extreme. Google had to fire the offending engineer, James Damore, but anyone who spends time on the message boards frequented by Valley engineers will know that the bro culture that gave us Gamergate - an online movement that targeted women in the video game industry - [remains] prevalent.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the erosion of privacy.
Forget swiping a credit card or badge to buy food at work. One Wisconsin-based tech firm is offering to install rice-size microchips in its employees' hands. Three Square Market will be the first firm in the U.S. to use the device, which was approved by the FDA in 2004, CEO Todd Westby told CNBC on Monday. "We think it's the right thing to do for advancing innovation just like the driverless car basically did in recent months," he said. The company, which provides technology for break-room markets or mini-market kiosks, is anticipating over 50 employees to be voluntarily chipped. Westby said he and his family will be chipped, too. The chip, which costs $300 per implant, is inserted with a needle between the thumb and forefinger. Once an employee has the chip installed, he or she can purchase food in the break room, open doors and log into computers. And for those who may be concerned about Big Brother watching, Westby said there is no way for employees to be tracked. "Unlike your cell phone that is trackable and traceable pretty much no matter where you are, this device is only readable if you're within six inches of a proximity reader," he said. Three Square Market's partner, BioHax International in Sweden, has already started using the microchips in about 150 of its employees.
Note: A Swedish company's chief executive was recently "chipped" live on stage to promote this dubious technology. And do you really think they are not trackable? Read about the agenda to chip all people in this powerful essay and these news articles.
Officials seized Trump protesters cell phones, cracked their passwords, and are now attempting to use the contents to convict them of conspiracy to riot at the presidential inauguration. Prosecutors have indicted over 200 people on felony riot charges for protests in Washington, D.C. on January 20. Some defendants face up to 75 years in prison. Evidence against the defendants has been scant from the moment of their arrest. As demonstrators, journalists, and observers marched through the city, D.C. police officers channelled hundreds of people into a narrow, blockaded corner, where they carried out mass arrests. Some of those people ... are now suing for wrongful arrest. Police also seized more than 100 cell phones. All of the ... phones were locked. But a July 21 court document shows that investigators were successful in opening the locked phones. Prosecutors moved to use a wealth of information from the phones as evidence, including the phones call detail records, SMS or MMS messages, contact logs/email logs, chats or other messaging applications, website search history and website history, and images or videos. One of the more than 200 defendants has pleaded guilty to riot charges after being named extensively in a superseding indictment. But the case against most defendants is less clear; in the superseding indictment, prosecutors accuse hundreds defendants of conspiracy to riot, based on overt acts as banal as chanting anti-capitalist slogans or wearing dark clothing.
Note: In May, United Nations officials said that the US treatment of activists was increasingly "incompatible with US obligations under international human rights law". For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the erosion of civil liberties.
Forty-five states and the District of Columbia are mounting a bipartisan rebellion against President Donald Trumps commission on vote fraud by either declining to release any of the requested data or by providing only limited information to the panel. The Presidential Advisory Commission on Voter Integrity's request for extensive personal information about voters has ignited a firestorm in many states, including from both Republican and Democrat officials who oversee elections. The panel is seeking "dates of birth, political party (if recorded in your state), last four digits of social security number if available, voter history (elections voted in) from 2006 onward, active/inactive status, cancelled status, information regarding any felony convictions, information regarding voter registration in another state, information regarding military status, and overseas citizen information." Nineteen states - both red and blue - and D.C. are flat-out refusing to comply with the request, citing privacy concerns and some claiming the 15-member vote fraud panel is politically-motivated. Many officials have expressed disbelief and outrage at the commission's call to hand over a staggering amount of voter data, some of which they say is confidential or sensitive. It is unclear how the commission plans to move forward after the backlash. The panel is slated to meet later this month.
Note: After several lawsuits, the voting panel is now telling states to hold off on sending data. For more along these lines, see concise summaries of deeply revealing elections corruption news articles from reliable major media sources. And don't miss the critically important information provided in our Elections Information Center.
Investigators have revealed that targets of high-tech spying in Mexico included an international group of experts backed by the Organization of American States who had criticized the governments investigation into the disappearance of 43 students. Previous investigations by the internet watchdog group Citizen Lab found that the spyware had been directed at journalists, activists and opposition politicians in Mexico. But targeting foreign experts operating under the aegis of an international body marks an escalation of the scandal. The experts had diplomatic status, making the spying attempt even graver. The spyware, known as Pegasus, is made by the Israel-based NSO Group, which says it sells only to government agencies for use against criminals and terrorists. It turns a cellphone into an eavesdropper, giving snoopers the ability to remotely activate its microphone and camera and access its data. The spyware is uploaded when users click on a link in email messages. Citizen Lab said the spyware attempts against the international experts occurred in March 2016 as the group was preparing its final, critical report on the government investigation into the disappearances. The 43 students were detained by local police in the city of Iguala on 26 September 2014, and were turned over to a crime gang. Only one students remains have been identified. The experts criticized the governments conclusions, saying ... that government investigators had not looked into other evidence.
Note: Read the report by Citizen Lab at the University of Toronto for the details of these suspicious spyware attacks. For more along these lines, see concise summaries of deeply revealing news articles on corruption in government and the erosion of civil liberties.
Mexican journalists, lawyers and activists were targeted by spyware produced by Israels NSO Group that is sold exclusively to governments. [A] report by Citizen Lab at the University of Toronto said the targets included people, such as prominent journalists Carmen Aristegui and Carlos Loret de Mola, who were investigating alleged government corruption and purported human rights abuses by security forces. The people targeted received messages with links that, if clicked on, opened up their devices to being exploited and spied upon. NSOs Pegasus spyware allows hackers access to phone calls, messages, cameras and personal data. Other targets included members of the Centro Miguel Agustin Pro Juarez, a prominent human rights group that has investigated cases such as the disappearance of 43 students whom police allegedly detained and turned over to drug gang killers; the anti-graft group Mexicans Against Corruption and Impunity; and the Mexican Institute for Competitiveness, a civil society group working on economic policy and combatting corruption. Aristegui, who exposed a case of possible conflict of interest involving a luxury home acquired from a government contractor ... was aggressively targeted. She received more than two-dozen messages with NSO links claiming to be from the U.S. Embassy in Mexico, Amber Alerts, colleagues, people in her personal life, her bank, phone company and notifications of kidnappings, the report said.
Note: If the above link is not working, this Associated Press article is also available here. For more along these lines, see concise summaries of deeply revealing news articles on corruption in government and the erosion of civil liberties.
Leaked documents and public records reveal a troubling fusion of private security, public law enforcement, and corporate money in the fight over the Dakota Access Pipeline. By the time law enforcement officers began evicting residents of the ... resistance camp near the Standing Rock Sioux reservation on February 22, the brutal North Dakota winter had already driven away most of the pipeline opponents. It would have been a natural time for the private security company in charge of monitoring the pipeline to head home. But internal communications between TigerSwan and its client, pipeline parent company Energy Transfer Partners, show that the security firm instead reached for ways to stay in business. Indeed, TigerSwan appeared to be looking for new causes, too. The ... firms sweeping surveillance of anti-Dakota Access protesters had already spanned five months and expanded into Iowa, South Dakota, and Illinois. TigerSwan became particularly interested in Chicago. [Leaked] documents dated between February 19 and February 21 describe TigerSwans efforts to monitor an anti-Trump protest organized by the local chapter of the Answer Coalition, an anti-war, anti-racism group. Answer Coalitions ... John Beacham, who organized the protest TigerSwan described, said that [the NoDAPL movement] was not the events primary focus. Theyre trying to make connections where they arent. Its almost like theyre trying to cast conspiracy theories across the entire progressive movement, he told The Intercept.
Note: The above article is part of an in-depth series, and includes many original source documents. Standing Rock activists were also targeted for investigation by the FBIs joint terrorism taskforce. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
Sensitive personal details relating to almost 200 million US citizens have been accidentally exposed by a marketing firm contracted by the Republican National Committee. The 1.1 terabytes of data includes birthdates, home addresses, telephone numbers and political views of nearly 62% of the entire US population. The data was available on a publicly accessible Amazon cloud server. Anyone could access the data. The information seems to have been collected from a wide range of sources - from posts on controversial banned threads on the social network Reddit, to committees that raised funds for the Republican Party. The information was stored in spreadsheets uploaded to a server owned by Deep Root Analytics. It had last been updated in January. Although it is known that political parties routinely gather data on voters, this is the largest breach of electoral data in the US to date and privacy experts are concerned about the sheer scale of the data gathered. "This is not just sensitive, it's intimate information, predictions about people's behaviour, opinions and beliefs that people have never decided to disclose to anyone," [said] Privacy International's policy officer Frederike Kaltheuner. However, the issue of data collection and using computer models to predict voter behaviour is not just limited to marketing firms - Privacy International says that the entire online advertising ecosystem operates in the same way.
Note: Elites like hedge fund billionaire Robert Mercer have been backing a major effort to produce powerful new forms of mind control by combining mass media with Big Data. As the data collected for this purpose becomes increasingly accessible, privacy disappears.
As grocery shoppers work to digest Amazons massive acquisition of Whole Foods for $13.7 billion, the digital storefront recently scored a victory that aims to reinforce the companys growing investments in brick-and-mortar retail. Amazon was awarded a patent May 30 that could help it choke off a common issue faced by many physical stores: Customers use of smartphones to compare prices even as they walk around a shop. But Amazon now has the technology to prevent that type of behavior when customers enter any of its physical stores and log onto the WiFi networks there. Titled Physical Store Online Shopping Control, Amazons patent describes a system that can identify a customers Internet traffic and sense when the smartphone user is trying to access a competitors website. When that happens, Amazon may take one of several actions. It may block access to the competitors site, preventing customers from viewing comparable products from rivals. It might redirect the customer to Amazons own site or to other, Amazon-approved sites. It might notify an Amazon salesperson to approach the customer. Or it might send the customers smartphone a text message, coupon or other information designed to lure the person back into Amazons orbit.
Note: For more along these lines, see concise summaries of deeply revealing corporate corruption news articles from reliable major media sources.
Important Note: Explore our full index to revealing excerpts of key major media news stories on several dozen engaging topics. And don't miss amazing excerpts from 20 of the most revealing news articles ever published.