Privacy News Articles
Below are key excerpts of revealing news articles on privacy and mass surveillance issues from reliable news media sources. If any link fails to function, a paywall blocks full access, or the article is no longer available, try these digital tools.
Facial recognition has become a security feature of choice for phones, laptops, passports, and payment apps. Yet it is also, increasingly, a tool of state oppression and corporate surveillance. Immigration and Customs Enforcement and the FBI have deployed the technology as a digital dragnet, searching for suspects among millions of faces in state driver’s license databases, sometimes without first seeking a court order. In early 1963, [Woody Bledsoe] proposed to conduct “a study to determine the feasibility of a simplified facial recognition machine.” A recently declassified history of the CIA’s Office of Research and Development mentions just such a project in 1965; that same year, Woody sent a letter on facial recognition to John W. Kuipers, the division’s chief of analysis. In 1967 ... Woody took on one last assignment that involved recognizing patterns in the human face. The purpose of the experiment was to help law enforcement agencies quickly sift through databases of mug shots and portraits, looking for matches. As before, funding for the project appears to have come from the US government. A 1967 document declassified by the CIA in 2005 mentions an “external contract” for a facial-recognition system that would reduce search time by a hundredfold. Woody’s work set an ethical tone for research on facial recognition that has been enduring and problematic. The potential abuses of facial-recognition technology were apparent almost from its birth.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
The New York Times's explanation of its decision to report, after what it said was a one-year delay, that the National Security Agency is eavesdropping domestically without court-approved warrants was woefully inadequate. And I have had unusual difficulty getting a better explanation for readers, despite the paper's repeated pledges of greater transparency. For the first time since I became public editor, the executive editor and the publisher have declined to respond to my requests for information about news-related decision-making. My queries concerned the timing of the exclusive Dec. 16 article about President Bush's secret decision in the months after 9/11 to authorize the warrantless eavesdropping on Americans in the United States. I e-mailed a list of 28 questions to Bill Keller, the executive editor [of the New York Times], on Dec. 19, three days after the article appeared. He promptly declined to respond to them. I then sent the same questions to Arthur Sulzberger Jr., the publisher, who also declined to respond. They held out no hope for a fuller explanation in the future. The top Times people involved in the final decisions [are] refusing to talk and urging everyone else to remain silent.
A young African American man, Randal Quran Reid, was pulled over by the state police in Georgia. He was arrested under warrants issued by Louisiana police for two cases of theft in New Orleans. The arrest warrants had been based solely on a facial recognition match, though that was never mentioned in any police document; the warrants claimed "a credible source" had identified Reid as the culprit. The facial recognition match was incorrect and Reid was released. Reid ... is not the only victim of a false facial recognition match. So far all those arrested in the US after a false match have been black. From surveillance to disinformation, we live in a world shaped by AI. The reason that Reid was wrongly incarcerated had less to do with artificial intelligence than with ... the humans that created the software and trained it. Too often when we talk of the "problem" of AI, we remove the human from the picture. We worry AI will "eliminate jobs" and make millions redundant, rather than recognise that the real decisions are made by governments and corporations and the humans that run them. We have come to view the machine as the agent and humans as victims of machine agency. Rather than seeing regulation as a means by which we can collectively shape our relationship to AI, it becomes something that is imposed from the top as a means of protecting humans from machines. It is not AI but our blindness to the way human societies are already deploying machine intelligence for political ends that should most worry us.
Note: For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
Imagine a global spying network that can eavesdrop on every single phone call, fax or e-mail, anywhere on the planet. It sounds like science fiction, but it's true. Two of the chief protagonists - Britain and America - officially deny its existence. But the BBC has confirmation from the Australian Government that such a network really does exist. The base is linked directly to the headquarters of the US National Security Agency (NSA) at Fort Mead in Maryland, and it is also linked to a series of other listening posts scattered across the world, like Britain's own GCHQ. The power of the network, codenamed Echelon, is astounding. Every international telephone call, fax, e-mail, or radio transmission can be listened to by powerful computers capable of voice recognition. They home in on a long list of key words, or patterns of messages. The network is so secret that the British and American Governments refuse to admit that Echelon even exists. But another ally, Australia, has decided not to be so coy. The man who oversees Australia's security services, Inspector General of Intelligence and Security Bill Blick, has confirmed to the BBC that their Defence Signals Directorate (DSD) does form part of the network. Asked if they are then passed on to countries like Britain and America, he said: "They might be in certain circumstances." They are looking for evidence of international crime, like terrorism. But the system is so widespread all sorts of private communications, often of a sensitive commercial nature, are hoovered up and analysed.
Note that this is a 1999 article, long before the revelations of Edward Snowden. The capability to monitor all communications has existed for a long time. For a powerful, well documented 20-page paper in the Federal Communications Law Journal providing strong evidence that this program is unconstitutional, click here.
American Amara Majeed was accused of terrorism by the Sri Lankan police in 2019. Robert Williams was arrested outside his house in Detroit and detained in jail for 18 hours for allegedly stealing watches in 2020. Randal Reid spent six days in jail in 2022 for supposedly using stolen credit cards in a state he’d never even visited. In all three cases, the authorities had the wrong people. In all three, it was face recognition technology that told them they were right. Law enforcement officers in many U.S. states are not required to reveal that they used face recognition technology to identify suspects. Surveillance is predicated on the idea that people need to be tracked and their movements limited and controlled in a trade-off between privacy and security. The assumption that less privacy leads to more security is built in. That may be the case for some, but not for the people disproportionately targeted by face recognition technology. As of 2019, face recognition technology misidentified Black and Asian people at up to 100 times the rate of white people. In 2018 ... 28 members of the U.S. Congress ... were falsely matched with mug shots on file using Amazon’s Rekognition tool. Much early research into face recognition software was funded by the CIA for the purposes of border surveillance. More recently, private companies have adopted data harvesting techniques, including face recognition, as part of a long practice of leveraging personal data for profit.
Note: For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
OpenAI was created as a non-profit-making charitable trust, the purpose of which was to develop artificial general intelligence, or AGI, which, roughly speaking, is a machine that can accomplish, or surpass, any intellectual task humans can perform. It would do so, however, in an ethical fashion to benefit “humanity as a whole”. Two years ago, a group of OpenAI researchers left to start a new organisation, Anthropic, fearful of the pace of AI development at their old company. One later told a reporter that “there was a 20% chance that a rogue AI would destroy humanity within the next decade”. One may wonder about the psychology of continuing to create machines that one believes may extinguish human life. The problem we face is not that machines may one day exercise power over humans. That is speculation unwarranted by current developments. It is rather that we already live in societies in which power is exercised by a few to the detriment of the majority, and that technology provides a means of consolidating that power. For those who hold social, political and economic power, it makes sense to project problems as technological rather than social and as lying in the future rather than in the present. There are few tools useful to humans that cannot also cause harm. But they rarely cause harm by themselves; they do so, rather, through the ways in which they are exploited by humans, especially those with power.
Note: Read how AI is already being used for war, mass surveillance, and questionable facial recognition technology.
Silicon Valley techies are pretty sanguine about commercial surveillance. But they are much less cool about government spying. Government employees and contractors are pretty cool with state surveillance. But they are far less cool with commercial surveillance. What are they both missing? That American surveillance is a public-private partnership: a symbiosis between a concentrated tech sector that has the means, motive, and opportunity to spy on every person in the world and a state that loves surveillance as much as it hates checks and balances. The tech sector has powerful allies in government: cops and spies. No government agency could ever hope to match the efficiency and scale of commercial surveillance. Meanwhile, the private sector relies on cops and spies to go to bat for them, lobbying against new privacy laws and for lax enforcement of existing ones. Think of Amazon’s Ring cameras, which have blanketed entire neighborhoods in CCTV surveillance, which Ring shares with law enforcement agencies, sometimes without the consent or knowledge of the cameras’ owners. Ring marketing recruits cops as street teams, showering them with freebies to distribute to local homeowners. Google ... has managed to play both sides of the culture war with its location surveillance, thanks to the “reverse warrants” that cops have used to identify all the participants at both Black Lives Matter protests and the January 6 coup. Distinguishing between state and private surveillance is a fool’s errand.
Note: For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
From Virginia to Florida, law enforcement all over the US are increasingly using tools called reverse search warrants – including geofence location warrants and keyword search warrants – to come up with a list of suspects who may have committed particular crimes. While the former is used by law enforcement to get tech companies to identify all the devices that were near a certain place at a certain time, the latter is used to get information on everyone who’s searched for a particular keyword or phrase. It’s a practice public defenders, privacy advocates and many lawmakers have criticised, arguing it violates fourth amendment protections against unreasonable searches. Unlike reverse search warrants, other warrants and subpoenas target a specific person that law enforcement has established there is probable cause to believe has committed a specific crime. But geofence warrants are sweeping in nature and are often used to compile a suspect list to further investigate. Google broke out how many geofence warrants it received for the first time in 2021. The company revealed it received nearly 21,000 geofence warrants between 2018 and 2020. The tech giant did not specify how many of those requests it complied with but did share that in the second half of 2020, it responded to 82% of all government requests for data in the US with some level of information. Apple has taken steps to publish its own numbers. In the first half of 2022 the company fielded a total of 13 geofence warrants and complied with none.
Note: The legal world is struggling to keep up with the rise of tech firms building ever more sophisticated means of surveilling people and their devices. For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
Recent reports about the Secret Service and Immigration and Customs Enforcement playing fast and loose with rules regarding cellphone tracking and the FBI purchasing phone location data from commercial sources constitute an important wake-up call. They remind us that those handy mobile devices many people tote around are the most cost-effective surveillance system ever invented. "The United States Secret Service and U.S. Immigration and Customs Enforcement, Homeland Security Investigations (ICE HSI) did not always adhere to Federal statute and cellsite simulator (CSS) policies when using CSS during criminal investigations," the Department of Homeland Security's Office of the Inspector General reported last month. "Separately, ICE HSI did not adhere to Department privacy policies and the applicable Federal privacy statute when using CSS." The OIG report referred to the use of what is commonly called "stingray" technology—devices that simulate cellphone towers and trick phones within range into connecting and revealing their location. "They also gather information about the phones of countless bystanders who happen to be nearby," the ACLU warns. Even the most precise phone company location data remains available with court approval. The courts are currently mulling multiple cases involving "geofence warrants" whereby law enforcement seeks data not on individuals, but on whoever was carrying a device in a designated area at a specified time.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Facebook wants to get up close and personal with its users after a patent was revealed detailing a desire to secretly watch users through their webcam or smartphone camera, spying on your mood in order to sell you tailored content or advertisements. The purpose behind the invasive idea is to analyse people through the camera in real time while they browse online and if it recognises you looking happy, bored or sad, it would deliver an advert fitting your emotion. If you were forlorn, for example, it would be able to serve an ad to perk you up, or know what products you had previously looked at online and put them under your nose at just the right time. The social network has filed several patents over the years on emotion-based technology but this, based on 'passive imaging data' is perhaps the most unnerving, considering it would take control of cameras that weren't even switched on by the user. As described by CB Insights: "This patent proposes capturing images of the user through smartphone or laptop cameras, even when the user is not actively using the camera. By visually tracking a user's facial expression, Facebook aims to monitor the user's emotional reactions to different types of content." Other patents listed by Facebook include a text messaging platform to detect a user's mood by measuring how hard and fast they were typing, then augment the message format, such as adding emojis or changing the font size, to match their emotion.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
A safe that tallies the cash that is placed in it. A sniper rifle equipped with advanced computer technology for improved accuracy. A car that lets you stream music from the Internet. All of these innovations sound great, until you learn the risks that this type of connectivity carries. Recently, two security researchers, sitting on a couch and armed only with laptops, remotely took over a Chrysler Jeep Cherokee speeding along the highway ... while a Wired reporter was driving. A hacked car is a high-profile example of what can go wrong with the coming Internet of Things objects equipped with software and connected to digital networks. The selling point ... is added convenience and better safety. In reality, it is a ... train wreck in privacy and security. That smart safe? Hackers can empty it with a single USB stick while erasing all [evidence] of their crime. That high-tech rifle? Researchers managed to remotely manipulate its target selection without the shooters knowing. The Internet of Things is also a privacy nightmare. Databases that already have too much information about us will now be bursting with data on the places weve driven, the food weve purchased and more. Last week, at Def Con, the annual information security conference, researchers set up an Internet of Things Village to show how they could hack everyday objects like baby monitors, thermostats and security cameras. Connecting everyday objects introduces new risks if done at mass scale. Once a hacker is in - she's in everywhere.
Note: Read how a hacked vehicle may have resulted in journalist Michael Hastings' death in 2013. The networked computerization of everyday objects means that these objects can spy on you, accelerating the disappearance of privacy in the name of convenience. What will happen when the "internet of things" expands to include microchip implants in people?
In March I received a call from the White House counsels office regarding a speech I had prepared for my boss at the State Department. The speech was about the impact ... of National Security Agency surveillance practices. The draft stated that if U.S. citizens disagree with congressional and executive branch determinations about the proper scope of signals intelligence activities, they have the opportunity to change the policy through our democratic process. But the White House counsels office told me that no, that wasnt true. I was instructed to amend the line. Some intelligence practices remain so secret, even from members of Congress, that there is no opportunity for our democracy to change them. Public debate about the bulk collection of U.S. citizens data by the NSA has focused largely on Section 215 of the Patriot Act. Based in part on classified facts that I am prohibited by law from publishing, I believe that Americans should be even more concerned about the collection and storage of their communications under Executive Order 12333 than under Section 215. Unlike Section 215, the executive order authorizes collection of the content of communications, not just metadata, even for U.S. persons. It does not require that the affected U.S. persons be suspected of wrongdoing and places no limits on the volume of communications by U.S. persons that may be collected and retained. None of the reforms that Obama announced earlier this year will affect such collection.
Note: The above was written by John Napier Tye, former section chief for Internet freedom in the State Departments Bureau of Democracy, Human Rights and Labor. A 2014 Washington Post investigation sheds more light on the NSA's legally dubious domestic mass surveillance program. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
Whistle-blower AT&T technician Mark Klein says his effort to reveal alleged government surveillance of domestic Internet traffic was blocked not only by U.S. intelligence officials but also by the top editors of the Los Angeles Times. Klein describes how he stumbled across "secret NSA rooms" being installed at an AT&T switching center in San Francisco and later heard of similar rooms in at least six other cities. Eventually, Klein says he decided to take his documents to the Los Angeles Times, to blow the whistle on what he calls "an illegal and Orwellian project." But after working for two months with LA Times reporter Joe Menn, Klein says he was told the story had been killed at the request of then-Director of National Intelligence John Negroponte and then-director of the NSA Gen. Michael Hayden. Klein says he then took his AT&T documents to The New York Times, which published its exclusive account last April [later removed from NY Times website]. In the court case against AT&T, Negroponte formally invoked the "state secrets privilege," claiming the lawsuit and the information from Klein and others could "cause exceptionally grave damage to the national security of the United States." The Los Angeles Times' decision was made by the paper's editor at the time, Dean Baquet, now the Washington bureau chief of The New York Times. As the new Washington bureau chief of The New York Times, Baquet now oversees the reporters who have broken most of the major stories involving the government surveillance program, often over objections from the government.
Note: This webpage was removed from the ABC website, but is still available through archive.org on thise webpage. So after the NY Times has the guts to report this important story, the man who was responsible for the censorship at the LA Times is transferred to the very position in the NY Times where he can now block future stories there. For why this case of blatant media censorship isn't making headlines, click here.
In 2010, the Washington Post reported that "every day, collection systems at the [NSA] intercept and store 1.7 billion emails, phone calls and other type of communications." In 2011, NSA expanded a program to provide real-time location information of every American with a cell phone, acquiring more than a billion cell phone records each day from AT&T. Later, newspapers around the world began publishing confidential documents leaked by [Edward] Snowden. Americans learned that the NSA can tap almost any cell phone in the world, exploit computer games like Angry Birds to poach personal data, access anyone's email and web browsing history [and] remotely penetrate almost all computers. The NSA used Facebook and Google apps to send malware to targeted individuals. NSA filched almost 200,000,000 records a month from private computer cloud accounts. Obama perpetuated perverse Bush-era legal doctrines to totally shield federal surveillance from judicial scrutiny. Obama's Justice Department secretly decreed that all phone records of all Americans were "relevant" to terrorism investigations and that the NSA could therefore justifiably seize everyone's personal data. Snowden revealed how the NSA had covertly carried out "the most significant change in the history of American espionage from the targeted surveillance of individuals to the mass surveillance of entire populations."
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
The future of wearable technology, beyond now-standard accessories like smartwatches and fitness tracking rings, is ePANTS, according to the intelligence community. The federal government has shelled out at least $22 million in an effort to develop “smart” clothing that spies on the wearer and its surroundings. Similar to previous moonshot projects funded by military and intelligence agencies, the inspiration may have come from science fiction and superpowers, but the basic applications are on brand for the government: surveillance and data collection. Billed as the “largest single investment to develop Active Smart Textiles,” the SMART ePANTS — Smart Electrically Powered and Networked Textile Systems — program aims to develop clothing capable of recording audio, video, and geolocation data, the Office of the Director of National Intelligence announced in an August 22 press release. Garments slated for production include shirts, pants, socks, and underwear, all of which are intended to be washable. There is already evidence that private industry outside of the national security community are interested in smart clothing. Meta, Facebook’s parent company, is looking to hire a researcher “with broad knowledge in smart textiles and garment construction, integration of electronics into soft and flexible systems, and who can work with a team of researchers working in haptics, sensing, tracking, and materials science.”
Note: Smart objects have been called a "train wreck in privacy and security." For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Imagine a world where wireless devices are as small as a grain of salt. These miniaturized devices have sensors, cameras and communication mechanisms to transmit the data they collect back to a base in order to process. Today, you no longer have to imagine it: microelectromechanical systems (MEMS), often called motes, are real and they very well could be coming to a neighborhood near you. With such a small size, these devices can stay suspended in an environment just like a particle of dust. They can: Collect data including acceleration, stress, pressure, humidity, sound and more from sensors; Process the data with what amounts to an onboard computer system; Store the data in memory; Wirelessly communicate the data to the cloud, a base or other MEMs. Since smart dust devices are miniature sensors they can record anything that they are programmed to record. Since they are so small, they are difficult to detect. Your imagination can run wild regarding the negative privacy implications when smart dust falls into the wrong hands. Once billions of smart dust devices are deployed over an area it would be difficult to retrieve or capture them if necessary. The volume of smart dust that could be engaged by a rogue individual, company or government to do harm would make it challenging for the authorities to control. Many of the applications for smart dust are still in the concept stage. We might not know when it will progress to the point of wide-scale adoption, but ... its a question of when rather than if.
Note: This takes privacy issues to an entirely new level. This AP article states the supermicro chips are "just 0.002 inches by 0.002 inches and look like bits of powder. They're thin enough to be embedded in a piece of paper." They are also small enough to slip into a vaccine unnoticed. And check out another Forbes article titled "Stratospheric Balloons Will Rain Tiny Electronic Spies From The Sky." For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
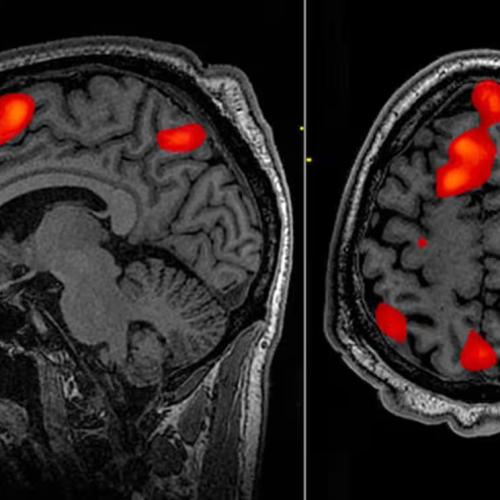
Billionaire Elon Musk’s brain-computer interface (BCI) company Neuralink made headlines earlier this year for inserting its first brain implant into a human being. Such implants ... are described as “fully implantable, cosmetically invisible, and designed to let you control a computer or mobile device anywhere you go." They can help people regain abilities lost due to aging, ailments, accidents or injuries, thus improving quality of life. Yet, great ethical concerns arise with such advancements, and the tech is already being used for questionable purposes. Some Chinese employers have started using “emotional surveillance technology” to monitor workers’ brainwaves. Governments and militaries are already ... describing the human body and brain as war’s next domain. On this new “battlefield,” an era of neuroweapons ... has begun. The Pentagon’s research arm DARPA directly or indirectly funds about half of invasive neural interface technology companies in the US. DARPA has initiated at least 40 neurotechnology-related programs over the past 24 years. As a 2024 RAND report speculates, if BCI technologies are hacked or compromised, “a malicious adversary could potentially inject fear, confusion, or anger into [a BCI] commander’s brain and cause them to make decisions that result in serious harm.” Academic Nicholas Evans speculates, further, that neuroimplants could “control an individual’s mental functions,” perhaps to manipulate memories, emotions, or even to torture the wearer. In a [military research paper] on neurowarfare: "Microbiologists have recently discovered mind-controlling parasites that can manipulate the behavior of their hosts according to their needs by switching genes on or off. Since human behavior is at least partially influenced by their genetics, nonlethal behavior modifying genetic bioweapons that spread through a highly contagious virus could thus be, in principle, possible.
Note: The CIA once used brain surgery to make six remote controlled dogs. For more, see important information on microchip implants and CIA mind control programs from reliable major media sources.
Finances at the vaccine manufacturer Moderna began to fall almost as quickly as they had risen, as most Americans resisted getting yet another COVID booster shot. In a September call aimed at shoring up investors, Moderna’s then-chief commercial officer, Arpa Garay, attributed some of the hesitancy pummeling Moderna's numbers to uninformed vaccine skeptics. What Garay hinted at during the call, but didn’t disclose, was that Moderna already had a sprawling media operation in place aimed at identifying and responding to critics of vaccine policy and the drug industry. Internal company reports and communications ... show that Moderna has worked with former law enforcement and public health officials and a drug industry-funded non-governmental organization called The Public Good Projects (PGP) to confront the “root cause of vaccine hesitancy” by rapidly identifying and “shutting down misinformation.” Part of this effort includes providing talking points to some 45,000 healthcare professionals “on how to respond when vaccine misinformation goes mainstream.” PGP routinely sent Excel lists of accounts to amplify on Twitter and others to de-platform, including populist voices such as ZeroHedge. The messages also suggested emerging narratives to remove from the platform. The growing network these efforts rely on shows the growth of what has been called the censorship industrial complex.
Note: Learn more about Moderna's misinformation department. For more along these lines, see concise summaries of deeply revealing news articles on pharmaceutical industry corruption and media manipulation from reliable sources.
The Moderna misinformation reports, reported here for the first time, reveal what the pharmaceutical company is willing to do to shape public discourse around its marquee product. The mRNA COVID-19 vaccine catapulted the company to a $100 billion valuation. Behind the scenes, the marketing arm of the company has been working with former law enforcement officials and public health officials to monitor and influence vaccine policy. Key to this is a drug industry-funded NGO called Public Good Projects. PGP works closely with social media platforms, government agencies and news websites to confront the “root cause of vaccine hesitancy” by rapidly identifying and “shutting down misinformation.” A network of 45,000 healthcare professionals are given talking points “and advice on how to respond when vaccine misinformation goes mainstream”, according to an email from Moderna. An official training programme, developed by Moderna and PGP, alongside the American Board of Internal Medicine, [helps] healthcare workers identify medical misinformation. The online course, called the “Infodemic Training Program”, represents an official partnership between biopharma and the NGO world. Meanwhile, Moderna also retains Talkwalker which uses its “Blue Silk” artificial intelligence to monitor vaccine-related conversations across 150 million websites in nearly 200 countries. Claims are automatically deemed “misinformation” if they encourage vaccine hesitancy. As the pandemic abates, Moderna is, if anything, ratcheting up its surveillance operation.
Note: Strategies to silence and censor those who challenge mainstream narratives enable COVID vaccine pharmaceutical giants to downplay the significant, emerging health risks associated with the COVID shots. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
A controversial facial recognition database, used by police departments across the nation, was built in part with 30 billion photos the company scraped from Facebook and other social media users without their permission. The company, Clearview AI, boasts of its potential for identifying rioters at the January 6 attack on the Capitol, saving children being abused or exploited, and helping exonerate people wrongfully accused of crimes. But critics point to privacy violations and wrongful arrests fueled by faulty identifications made by facial recognition, including cases in Detroit and New Orleans, as cause for concern over the technology. Once a photo has been scraped by Clearview AI, biometric face prints are made and cross-referenced in the database, tying the individuals to their social media profiles and other identifying information forever — and people in the photos have little recourse to try to remove themselves. CNN reported Clearview AI last year claimed the company's clients include "more than 3,100 US agencies, including the FBI and Department of Homeland Security." BBC reported Miami Police acknowledged they use the technology for all kinds of crimes, from shoplifting to murder. The risk of being included in what is functionally a "perpetual police line-up" applies to everyone, including people who think they have nothing to hide, [said] Matthew Guariglia, a senior policy analyst for the international non-profit digital rights group Electronic Frontier Fund.
Note: Read about the rising concerns of the use of Clearview AI technology in Ukraine, with claims to help reunite families, identify Russian operatives, and fight misinformation. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
Bill Gates ... just called for a complete and utter shutdown and quarantining of the entire American nation. Despite urging from public health experts, Gates wrote in a Washington Post opinion piece, some states and counties havent shut down completely. This is a recipe for disaster. Because people can travel freely across state lines, so can the virus. The countrys leaders need to be clear: Shutdown anywhere means shutdown everywhere. Until the case numbers start to go down ... no one can continue business as usual or relax the shutdown. He then added that the impacts of the new coronavirus could linger another 18 months or so, until a vaccine was developed. For the peons of America, work isnt an option. Its food. Its survival. The fate of a hard-earned dream shouldnt rest with a globalist billionaire whos warning of dire coronavirus consequences to come all the while making hands-over-fist coronavirus money. Its a conflict of interest. WHO didnt announce the coronavirus as a pandemic until the very day after Gates ... made a very large donation to a cause that benefits WHO. In a 2017 piece titled, Meet the worlds most powerful doctor: Bill Gates, Politico wrote: Some billionaires are satisfied with buying themselves an island. Bill Gates got a United Nations health agency. Over the past decade, the worlds richest man has become the World Health Organizations second-biggest donor, second only to the United States. This largesse gives him outsized influence over its agenda. The result, say his critics, is that Gates priorities have become the WHOs.
Very Important Note: To understand how the coronavirus is being used to exert more control over humanity, don't miss this incredibly important video focused on how Bill Gates is using fear around the coronavirus to push through his agenda to vaccinate everyone on the planet and then require a "digital certificate" to ensure they've been vaccinated. For other reliable, verifiable informing demonstrating how Gates' vaccine agenda has already harmed hundreds of thousands of children read this excellent article by Robert F. Kennedy, Jr.
Private thoughts may not be private for much longer, heralding a nightmarish world where political views, thoughts, stray obsessions and feelings could be interrogated and punished all thanks to advances in neurotechnology. In a new book, The Battle for Your Brain, Duke University bioscience professor Nita Farahany argues that such intrusions into the human mind by technology are so close that a public discussion is long overdue and lawmakers should immediately establish brain protections as it would for any other area of personal liberty. Farahany, who served on Barack Obama’s commission for the study of bioethical issues, believes that advances in neurotechnology mean that intrusions through the door of brain privacy, whether by way of military programs or by way of well-funded research labs at big tech companies, are at hand via brain-to-computer innovations like wearable tech. “All of the major tech companies have massive investments in multifunctional devices that have brain sensors in them,” Farahany said. “Neural sensors will become part of our everyday technology and a part of how we interact with that technology.” François du Cluzel, a project manager at Nato Act Innovation Hub, issued a report in November 2020 entitled Cognitive Warfare that, it said, “is not limited to the military or institutional world. Since the early 1990s, this capability has tended to be applied to the political, economic, cultural and societal fields.”
Note: Read more about these troubling developments. For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
The precise locations of the U.S. government’s high-tech surveillance towers along the U.S-Mexico border are being made public for the first time as part of a mapping project by the Electronic Frontier Foundation. While the Department of Homeland Security’s investment of more than a billion dollars into a so-called virtual wall between the U.S. and Mexico is a matter of public record, the government does not disclose where these towers are located, despite privacy concerns of residents of both countries — and the fact that individual towers are plainly visible to observers. The surveillance tower map is the result of a year’s work steered by EFF Director of Investigations Dave Maass. As border surveillance towers have multiplied across the southern border, so too have they become increasingly sophisticated, packing a panoply of powerful cameras, microphones, lasers, radar antennae, and other sensors. Companies like Anduril and Google have reaped major government paydays by promising to automate the border-watching process with migrant-detecting artificial intelligence. Opponents of these modern towers, bristling with always-watching sensors, argue the increasing computerization of border security will lead inevitably to the dehumanization of an already thoroughly dehumanizing undertaking. Nobody can say for certain how many people have died attempting to cross the U.S.-Mexico border in the recent age of militarization and surveillance. Researchers estimate that the minimum is at least 10,000 dead.
Note: As the article states, the Department of Homeland Security was "the largest reorganization of the federal government since the creation of the CIA and the Defense Department," and has resulted in U.S. taxpayers funding corrupt agendas that have led to massive human rights abuses. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
The Biden administration took a public stand last year against the abuse of spyware to target human rights activists, dissidents and journalists: It blacklisted the most notorious maker of the hacking tools, the Israeli firm NSO Group. But the global industry for commercial spyware — which allows governments to invade mobile phones and vacuum up data — continues to boom. Even the U.S. government is using it. The Drug Enforcement Administration is secretly deploying spyware from a different Israeli firm, according to five people familiar with the agency’s operations, in the first confirmed use of commercial spyware by the federal government. The most sophisticated spyware tools — like NSO’s Pegasus — have “zero-click” technology, meaning they can stealthily and remotely extract everything from a target’s mobile phone, without the user having to click on a malicious link to give Pegasus remote access. They can also turn the mobile phone into a tracking and secret recording device, allowing the phone to spy on its owner. But hacking tools without zero-click capability, which are considerably cheaper, also have a significant market. Commercial spyware has been used by intelligence services and police forces to hack phones used by drug networks and terrorist groups. But it has also been abused by numerous authoritarian regimes and democracies to spy on political opponents and journalists. This has led governments to a sometimes tortured rationale for their use.
Note: Read about how NSO Group spyware was used against journalists and activists by the Mexican government. For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
The House committee investigating the events of January 6, 2021, is nearly finished. Nearly 900 ... criminal prosecutions of alleged rioters remain underway, and one case has shed troubling new light on how the FBI investigated these defendants. The suspect's name is David Rhine. His lawyer is the first to present a potentially successful challenge to the geofencing warrant the FBI used to place some defendants inside the Capitol building during the attack. A previous Wired report last year found 45 federal criminal cases citing the warrant, which required Google to provide the FBI with data on devices using its location services inside a set geographic area. Rhine's case has revealed just how expansive the FBI's request to Google really was. Google initially listed 5,723 devices in response to the warrant, then whittled the tally to exclude likely Capitol staff and police as well as anyone who wasn't "entirely within the geofence, to about a 70 percent probability." The final list of identifying details handed over to the FBI had 1,535 names. It included people whose phones had been turned off or put in airplane mode, and "people who attempted to delete their location data following the attacks were singled out by the FBI for greater scrutiny." It's ... easy to envision geofencing warrants undergoing the usual surveillance mission creep. Left unchecked, law enforcement could decide geofence data would come in handy while looking for a journalist's whistleblowing source, or perhaps at political protests.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Australia's two most populous states are trialling facial recognition software that lets police check people are home during COVID-19 quarantine, expanding trials that have sparked controversy to the vast majority of the country's population. Little-known tech firm Genvis Pty Ltd said on a website for its software that New South Wales (NSW) and Victoria, home to Sydney, Melbourne and more than half of Australia's 25 million population, were trialling its facial recognition products. The Perth, Western Australia-based startup developed the software in 2020 with WA state police to help enforce pandemic movement restrictions. South Australia state began trialling a similar, non-Genvis technology last month, sparking warnings from privacy advocates around the world about potential surveillance overreach. The involvement of New South Wales and Victoria, which have not disclosed that they are trialling facial recognition technology, may amplify those concerns. Under the system being trialled, people respond to random check-in requests by taking a 'selfie' at their designated home quarantine address. If the software, which also collects location data, does not verify the image against a "facial signature", police may follow up with a visit to the location to confirm the person's whereabouts. While the recognition technology has been used in countries like China, no other democracy has been reported as considering its use in connection with coronavirus containment procedures.
Note: On Sept. 21st, thousands of citizens took to the streets to protest policies like this in Melbourne alone, as shown in this revealing video. The police are responding almost like they are at war, as show in this video. Yet the major media outside of Australia are largely ignoring all of this, while the Australian press is highly biased against the protesters. Are we moving towards a police state? For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus and the disappearance of privacy from reliable major media sources.
When the man from Hangzhou returned home from a business trip, the local police got in touch. They had tracked his car by his license plate in nearby Wenzhou, which has had a spate of coronavirus cases. Stay indoors for two weeks, they requested. After around 12 days, he was bored and went out early. This time, not only did the police contact him, so did his boss. He had been spotted ... by a camera with facial recognition technology, and the authorities had alerted his company as a warning. I was a bit shocked by the ability and efficiency of the mass surveillance network. They can basically trace our movements ... at any time and any place, said the man, who asked not to be identified for fear of repercussions. Chinese have long been aware that they are tracked by the world's most sophisticated system of electronic surveillance. The coronavirus emergency has brought some of that technology out of the shadows, providing the authorities with a justification for sweeping methods of high tech social control. Artificial intelligence and security camera companies boast that their systems can scan the streets for people with even low-grade fevers, recognize their faces even if they are wearing masks and report them to the authorities. If a coronavirus patient boards a train, the railway's "real name" system can provide a list of people sitting nearby. Mobile phone apps can tell users if they have been on a flight or a train with a known coronavirus carrier, and maps can show them ... where infected patients live.
Note: The New York Times strangely removed this article. Yet it is also available here. Is there something they don't want us to know? Read an excellent article showing how this virus scare is being used to test China's intense surveillance technologies in very disturbing ways. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
As white supremacists have carried out a growing number of deadly attacks in recent years, the FBI has come under mounting criticism for its failure to address the threat posed by far-right extremist ideologies, whose adherents account for most of the politically motivated violence in the U.S. At the same time, the bureau has also been heavily criticized for devoting large resources to surveilling political dissent by groups and individuals, often of color, who pose no threat but are critical of the government because they oppose official immigration policies or demand police accountability. The FBIs preoccupation with policing nonviolent critical ideologies while neglecting to investigate ideologies tied to real, and increasing, violence was perhaps best captured in an infamous 2017 threat assessment report warning law enforcement agencies of the supposed rise of a black identity extremist movement targeting police. The black identity extremism category was a product of the FBIs imagination. Last year ... bureau officials told legislators that they were doing away with a set of earlier domestic terrorism categories in favor of four larger ones. The FBIs fictional black identity extremists would now be lumped together with white supremacists under a new racially motivated violent extremism category. That false equivalence made it virtually impossible for the public to know whether the FBI was devoting resources to investigating real threats of racist violence or social and racial justice groups critical of government.
Note: Read a revealing essay on COINTELPRO, the FBI program that targeted civil rights and anti-war activists from 1965-1975. For more along these lines, see concise summaries of deeply revealing news articles on civil liberties from reliable major media sources.
The Newborn Genetic Screening test is required in all 50 states. Nearly every baby born in the United States gets a heel prick shortly after birth. Their newborn blood fills six spots on a special filter paper card. It is used to test baby for dozens of congenital disorders. Some states destroy the blood spots after a year, 12 states store them for at least 21 years. California, however, is one of a handful of states that stores the remaining blood spots for research indefinitely in a state-run biobank. The child's leftover blood spots become property of the state and may be sold to outside researchers without the parent's knowledge or consent. "I just didn't realize there was a repository of every baby born in the state. It's like fingerprints," new mom Soniya Sapre responded. In California ... you do have the right to ask the biobank to destroy the leftovers after the fact, though the agency's website states it "may not be able to comply with your request." You also have the right to find out if your child's blood spots have been used for research, but you would have to know they were being used in the first place and we've discovered that most parents don't. But researchers with the California Genetic Disease Screening Program aren't the only ones with access to samples stored in the biobank. Blood spots are given to outside researchers for $20 to $40 per spot. According to biobank records, the program sold about 16,000 blood spots over the past five years, totaling a little more than $700,000.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy.
Over the last two years, researchers in China and the United States have begun demonstrating that they can send hidden commands that are undetectable to the human ear to Apples Siri, Amazons Alexa and Googles Assistant. Researchers have been able to secretly activate the artificial intelligence systems on smartphones and smart speakers, making them dial phone numbers or open websites. In the wrong hands, the technology could be used to unlock doors, wire money or buy stuff online - simply with music playing over the radio. A group of students from University of California, Berkeley, and Georgetown University showed in 2016 that they could hide commands in white noise played over loudspeakers and through YouTube videos to get smart devices to turn on airplane mode or open a website. This month, some of those Berkeley researchers published a research paper that went further, saying they could embed commands directly into recordings of music or spoken text. So while a human listener hears someone talking or an orchestra playing, Amazons Echo speaker might hear an instruction to add something to your shopping list. There is no American law against broadcasting subliminal messages to humans, let alone machines. The Federal Communications Commission discourages the practice as counter to the public interest, and the Television Code of the National Association of Broadcasters bans transmitting messages below the threshold of normal awareness.
Note: Read how a hacked vehicle may have resulted in journalist Michael Hastings' death in 2013. A 2015 New York Times article titled "Why Smart Objects May Be a Dumb Idea" describes other major risks in creating an "Internet of Things". Vulnerabilities like those described in the article above make it possible for anyone to spy on you with these objects, accelerating the disappearance of privacy.
The National Security Agency maintains a page on its website that outlines its mission statement. Since at least May 2016, the surveillance agency had featured honesty as the first of four core values listed on NSA.gov, alongside respect for the law, integrity, and transparency. On January 12, however, the NSA removed the mission statement page which can still be viewed through the Internet Archive and replaced it with a new version. Now, the parts about honesty and the pledge to be truthful have been deleted. The agencys new top value is commitment to service, which it says means excellence in the pursuit of our critical mission. Those are not the only striking alterations. All references to trust, honor, and openness have disappeared. The agency previously stated on its website that it embraced transparency and claimed that all of its activities were aimed at ensuring the safety, security, and liberty of our fellow citizens. That has also been discarded. The new list of values includes the additions respect for people and accountability. But the section on respecting people is a reference to diversity within the NSA workforce, not a general commitment to members of the public. Accountability is defined as taking responsibility for our decisions. The one core value that remains essentially unchanged is respect for the law, which the agency says means it is grounded in our adherence to the U.S. Constitution and compliance with the U.S. laws, regulations and policies that govern our activities.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
I Googled mainstream media is And there it was. Googles autocomplete suggestions: mainstream media is dead, dying, fake news, fake, finished. Googles first suggested link ... leads to a website called CNSnews.com and an article: The Mainstream media are dead. How had it, an obscure site Id never heard of, dominated Googles search algorithm on the topic? In the About us tab, I learn CNSnews is owned by the Media Research Center. It receives a large bulk of its funding more than $10m in the past decade from a single source, the hedge fund billionaire Robert Mercer. Robert Mercer is the money behind an awful lot of things. He was Trumps single biggest donor. Since 2010, Mercer has donated $45m to different political campaigns all Republican and another $50m to non-profits all rightwing, ultra-conservative. This is a billionaire who is ... trying to reshape the world according to his personal beliefs. He is reported to have a $10m stake in the [Cambridge Analytica], which was spun out of a bigger British company called SCL Group. It specialises in election management strategies and messaging and information operations, refined over 25 years. In military circles this is known as psyops psychological operations. Cambridge Analytica makes the astonishing boast that it has psychological profiles based on 5,000 separate pieces of data on 220 million American voters. With this, a computer ... can predict and potentially control human behaviour. Its incredibly dangerous.
Note: The above article provides a detailed look at how mass media is being combined with Big Data to produce powerful new forms of mind control.
"There's really only two types of companies or two types of people which are those who have been hacked and realize it and those who have been hacked and haven't." That's what mobile security expert John Hering tells 60 Minutes correspondent Sharyn Alfonsi about the danger of cellphone hacking. To prove his point, Hering assembled a group of ace hackers. Jon Oberheide showed 60 Minutes an app he created that looks legitimate but allows him to take control of a phone and suck out ... information [such as] contacts, recent purchases and text messages. Another hacker, Adam Laurie, uses radio frequency identification to hack phones. "He didn't need my phone number," Alfonsi explains. "All he had to do was physically touch my phone." He demonstrated by brushing by her in the lobby of her hotel. When he did ... her phone [automatically] dialed Laurie, allowing him to listen in on anything discussed in the room with Alfonsi's phone. A so-called "CryptoPhone" ... alerts the user when someone is trying to attack or hack into his or her phone. "Certain government facilities will try to get into your phone if you get too close to them," Alfonsi explains. To demonstrate, Les Goldsmith, CEO of ESD America, a company that specializes in countersurveillance technologies, took Alfonsi for a ride ... near a secure government facility. As they were driving past, a red line appeared on the CryptoPhone, indicating that ... if she were using a regular phone, the government agency could hear her call and read her text messages.
Note: For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the disappearance of privacy.
The sneak-and-peek provision of the Patriot Act that was alleged to be used only in national security and terrorism investigations has overwhelmingly been used in narcotics cases. Now the New York Times reports that National Security Agency data will be shared with other intelligence agencies like the FBI without first applying any screens for privacy. The ACLU of Massachusetts blog Privacy SOS explains [that] domestic law enforcement officials now have access to huge troves of American communications, obtained without warrants, that they can use to put people in cages. This basically formalizes what was already happening. Weve known for a couple of years now that the Drug Enforcement Administration and the IRS were getting information from the NSA. Because that information was obtained without a warrant, the agencies were instructed to engage in parallel construction when explaining to courts and defense attorneys how the information had been obtained. It certainly isnt the only time that that national security apparatus has let law enforcement agencies benefit from policies that are supposed to be reserved for terrorism investigations in order to get around the Fourth Amendment, then instructed those law enforcement agencies to misdirect, fudge and outright lie about how they obtained incriminating information. This isnt just a few rogue agents. The lying has been a matter of policy.
Note: For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the disappearance of privacy.
Scores of low-flying planes circling American cities are part of a civilian air force operated by the FBI and obscured behind fictitious companies. The aircraft are equipped with high-tech cameras, and ... technology capable of tracking thousands of cellphones. The surveillance equipment is used for ongoing investigations, the FBI says, generally without a judge's approval. The Drug Enforcement Administration has its own planes, also registered to fake companies, according to a 2011 Justice Department ... report. At the time, the DEA had 92 aircraft in its fleet. And since 2007, the U.S. Marshals Service has operated an aerial surveillance program with its own fleet equipped with technology that can capture data from thousands of cellphones. "These are not your grandparents' surveillance aircraft," said Jay Stanley, a senior policy analyst with the American Civil Liberties Union. Evolving technology can record higher-quality video from long distances, even at night, and can capture certain identifying information from cellphones using a device known as a "cell-site simulator" [to] trick pinpointed cellphones into revealing identification numbers of subscribers, including those not suspected of a crime. The Obama administration [has] been directing local authorities through secret agreements not to reveal their own use of the devices. During the past few weeks, the AP tracked planes from the FBI's fleet on more than 100 flights over at least 11 states plus the District of Columbia.
Note: For more along these lines, see concise summaries of deeply revealing news articles about the corrupt intelligence agencies that facilitate the erosion of privacy rights in the U.S. and elsewhere.
At least 50 U.S. law enforcement agencies have secretly equipped their officers with radar devices that allow them to effectively peer through the walls of houses to see whether anyone is inside. Those agencies, including the FBI and the U.S. Marshals Service, began deploying the radar systems more than two years ago with little notice to the courts and no public disclosure of when or how they would be used. The technology raises legal and privacy issues because the U.S. Supreme Court has said officers generally cannot use high-tech sensors to tell them about the inside of a person's house without first obtaining a search warrant. The radars work like finely tuned motion detectors, using radio waves to zero in on movements as slight as human breathing from a distance of more than 50 feet. They can detect whether anyone is inside of a house, where they are and whether they are moving. The device the Marshals Service and others are using [was] first designed for use in Iraq and Afghanistan. They represent the latest example of battlefield technology finding its way home to civilian policing and bringing complex legal questions with it. Those concerns are especially thorny when it comes to technology that lets the police determine what's happening inside someone's home.
Note: This technology is not new. Working as interpreter in Washington, DC, WantToKnow.info founder Fred Burks witnessed this technology being used by the police there in the late 1980s. Explore an informative ACLU report detailing the many surveillance technologies used by police which are often used illegally. For more along these lines, see this deeply revealing summarized NPR report about The Pentagon's massive Program 1033 to widely distribute military hardware to domestic police forces.
The U.S. government threatened to fine Yahoo $250,000 a day in 2008 if it failed to comply with a broad demand to hand over user communications a request the company believed was unconstitutional according to court documents unsealed [on September 11] that illuminate how federal officials forced American tech companies to participate in the National Security Agencys controversial PRISM program. The documents ... outline a secret and ultimately unsuccessful legal battle by Yahoo to resist the governments demands. The companys loss required Yahoo to become one of the first to begin providing information to PRISM, a program that gave the NSA extensive access to records of online communications by users of Yahoo and other U.S.-based technology firms. The ruling by the Foreign Intelligence Surveillance Court of Review became a key moment in the development of PRISM, helping government officials to convince other Silicon Valley companies that unprecedented data demands had been tested in the courts and found constitutionally sound. Eventually, most major U.S. tech companies, including Google, Facebook, Apple and AOL, complied. Microsoft had joined earlier, before the ruling, NSA documents have shown. PRISM was first revealed by former NSA contractor Edward Snowden last year. Documents made it clear that the program allowed the NSA to order U.S.-based tech companies to turn over e-mails and other communications to or from foreign targets without search warrants for each of those targets. Other NSA programs gave even more wide-ranging access to personal information of people worldwide, by collecting data directly from fiber-optic connections.
Note: For more on this, see concise summaries of deeply revealing government surveillance news articles from reliable major media sources.
The US governments web of surveillance is vast and interconnected. You can be pulled into the National Security Agencys database quietly and quickly. Through ICREACH, a Google-style search engine created for the intelligence community, the NSA provides data on private communications to 23 government agencies. More than 1,000 analysts had access to that information. It was confirmed earlier this month that the FBI shares its master watchlist, the Terrorist Screening Database, with at least 22 foreign governments, countless federal agencies, state and local law enforcement, plus private contractors. The watchlist [is] based on [low] standards and secret evidence, which ensnares innocent people. Indeed, the standards are so low that the US governments guidelines specifically allow for a single, uncorroborated source of information including a Facebook or Twitter post to serve as the basis for placing you on its master watchlist. Of the 680,000 individuals on that FBI master list, roughly 40% have no recognized terrorist group affiliation, according to the Intercept. These individuals dont even have a connection as the government loosely defines it to a designated terrorist group, but they are still branded as suspected terrorists. The US [government uses] a loose standard so-called reasonable suspicion in determining who, exactly, can be watchlisted. ["Reasonable suspicion"] requires neither concrete evidence nor irrefutable evidence. Instead, an official is permitted to consider reasonable inferences and to draw from the facts in light of his/her experience.
Note: For more on this, see concise summaries of deeply revealing terrorism news articles from reliable major media sources.
The former National Security Agency contractor Edward J. Snowden said in a wide-ranging interview ... that the oversight of surveillance programs was so weak that members of the United States military working at the spy agency sometimes shared sexually explicit photos they intercepted. He also said the British government often pioneered the most invasive surveillance programs because its intelligence services operate with fewer restrictions intended to protect individual privacy than its counterparts in the United States and other allies. In the course of their daily work they stumble across something that is completely unrelated to their work, for example an intimate nude photo of someone in a sexually compromising situation but theyre extremely attractive, he said. So what do they do? They turn around in their chair and they show a co-worker. And their co-worker says: Oh, hey, thats great. Send that to Bill down the way. Mr. Snowden said that type of sharing ... was seen as the fringe benefits of surveillance positions. He said that this was never reported and that the system for auditing surveillance programs was incredibly weak. Mr. Snowden had particularly stark criticism for the British governments surveillance programs, because in Britain the respect for individual privacy, he said, is not strongly encoded in law or policy. Because it has fewer restrictions, British intelligence platforms are used as a testing ground for programs of all five intelligence partners, a group referred to as Five Eyes, which includes Britain, Canada, Australia, New Zealand and the United States.
Note: For more on this, see concise summaries of deeply revealing privacy news articles from reliable major media sources.
British spies have developed "dirty tricks" ... that include releasing computer viruses, spying on journalists and diplomats, jamming phones and computers, and using sex to lure targets into "honey traps." Documents taken from the National Security Agency by Edward Snowden ... describe techniques developed by a secret British spy unit called the Joint Threat Research and Intelligence Group (JTRIG). According to the documents ... the agency's goal was to "destroy, deny, degrade [and] disrupt" enemies by "discrediting" them, planting misinformation and shutting down their communications. The propaganda campaigns use deception, mass messaging and "pushing stories" via Twitter, Flickr, Facebook and YouTube. JTRIG also uses "false flag" operations, in which British agents carry out online actions that are designed to look like they were performed by one of Britain's adversaries. Other documents ... show that JTRIG ... used a DDOS attack to shut down Internet chat rooms used by members of the hacktivist group known as Anonymous. A computer virus called Ambassadors Reception was "used in a variety of different areas" and was "very effective." When sent to adversaries ... the virus will "encrypt itself, delete all emails ... and block the computer user from logging on. Spies have long used sexual "honey traps" to snare, blackmail and influence targets. Most often, a male target is led to believe he has an opportunity for a romantic relationship or a sexual liaison with a woman, only to find that the woman is actually an intelligence operative.
Note: You can read the documents released by Snowden at this link and this one. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption from reliable major media sources.
The British government can tap into the cables carrying the worlds web traffic at will and spy on what people are doing on some of the worlds most popular social media sites ... without the knowledge or consent of the companies. Documents taken from the National Security Agency by Edward Snowden and obtained by NBC News detail how British cyber spies demonstrated a pilot program to their U.S. partners in 2012 in which they were able to monitor YouTube in real time and collect addresses from the billions of videos watched daily, as well as some user information, for analysis. At the time the documents were printed, they were also able to spy on Facebook and Twitter. Called Psychology A New Kind of SIGDEV" (Signals Development), the presentation includes a section that spells out Broad real-time monitoring of online activity of YouTube videos, URLs liked on Facebook, and Blogspot/Blogger visits. The monitoring program is called Squeaky Dolphin. Experts told NBC News the documents show the British had to have been either physically able to tap the cables carrying the worlds web traffic or able to use a third party to gain physical access to the massive stream of data. Representatives of Facebook and Google, which owns YouTube, said they ... were unaware the collection had occurred. The NSA does analysis of social media similar to that in the GCHQ demonstration. In 2010 ... GCHQ exploited unencrypted data from Twitter to identify specific users around the world and target them with propaganda.
Note: Read an article diving deeper and showing how online reputations are ruthlessly destroyed by powerful groups. For more along these lines, see concise summaries of deeply revealing news articles about questionable intelligence agency practices and the erosion of privacy.
The National Security Agency is winning its long-running secret war on encryption, using supercomputers, technical trickery, court orders and behind-the-scenes persuasion to undermine the major tools protecting the privacy of everyday communications in the Internet age, according to newly disclosed documents. The agency has circumvented or cracked much of the encryption, or digital scrambling, that guards global commerce and banking systems, protects sensitive data like trade secrets and medical records, and automatically secures the e-mails, Web searches, Internet chats and phone calls of Americans and others around the world, the documents show. Many users assume or have been assured by Internet companies that their data is safe from prying eyes, including those of the government, and the N.S.A. wants to keep it that way. The agency treats its recent successes in deciphering protected information as among its most closely guarded secrets, restricted to those cleared for a highly classified program code-named Bullrun, according to the documents, provided by Edward J. Snowden, the former N.S.A. contractor. Beginning in 2000, as encryption tools were gradually blanketing the Web, the N.S.A. invested billions of dollars in a clandestine campaign to preserve its ability to eavesdrop. Having lost a public battle in the 1990s to insert its own back door in all encryption, it set out to accomplish the same goal by stealth. The agency ... deployed custom-built, superfast computers to break codes, and began collaborating with technology companies in the United States and abroad to build entry points into their products [called "backdoors"].
Note: For an excellent article in the UK's respected Guardian on this, click here. For a guide from the Guardian on "How to remain secure against NSA surveillance", click here.
[The] fact that a car is not a simple machine of glass and steel but a hackable network of computers, is what [Charlie Miller and Chris Valasek] have spent the last year trying to demonstrate. Miller, a 40-year-old security engineer at Twitter, and Valasek, the 31-year-old director of security intelligence at the Seattle consultancy IOActive, received an $80,000-plus grant last fall from [the] Defense Advanced Research Projects Agency to root out security vulnerabilities in automobiles. The need for scrutiny is growing as cars are increasingly automated and connected to the Internet. Practically every American carmaker now offers a cellular service or Wi-Fi network like General Motors OnStar, Toyotas Safety Connect and Fords SYNC. Without better security its all potentially vulnerable, and automakers are remaining mum or downplaying the issue. As I drove their vehicles for more than an hour, Miller and Valasek showed that theyve reverse-engineered enough of the software of the [Ford] Escape and the Toyota Prius (both the 2010 model) to demonstrate a range of nasty surprises: everything from annoyances like uncontrollably blasting the horn to serious hazards like slamming on the Prius brakes at high speeds. They sent commands from their laptops that killed power steering, spoofed the GPS and made pathological liars out of speedometers and odometers. Finally they directed me out to a country road, where Valasek showed that he could violently jerk the Prius steering at any speed, threatening to send us into a cornfield or a head-on collision.
Note: Don't miss the unbelievable video at the above link which shows how a good hacker can take control of your car's steering, brakes, and much more. For more on the OnStar system in most GM cars now and how it allows spying on you, read the CNN article titled "OnStar's 'brazen' data tracking comes under fire" at this link. For more on government and corporate digital security invasions, see the deeply revealing reports from reliable major media sources available here.
New documents prove what was once dismissed as paranoid fantasy: totally integrated corporate-state repression of dissent. It was more sophisticated than we had imagined: new documents show that the violent crackdown on Occupy last fall so mystifying at the time was not just coordinated at the level of the FBI, the Department of Homeland Security, and local police. The crackdown, which involved, as you may recall, violent arrests, group disruption, canister missiles to the skulls of protesters, people held in handcuffs so tight they were injured, people held in bondage till they were forced to wet or soil themselves was coordinated with the big banks themselves. The Partnership for Civil Justice Fund, in a groundbreaking scoop that should once more shame major US media outlets (why are nonprofits now some of the only entities in America left breaking major civil liberties news?), filed this request. The document reproduced here in an easily searchable format shows a terrifying network of coordinated DHS, FBI, police, regional fusion center, and private-sector activity so completely merged into one another that the monstrous whole is, in fact, one entity: in some cases, bearing a single name, the Domestic Security Alliance Council. And it reveals this merged entity to have one centrally planned, locally executed mission. The documents, in short, show the cops and DHS working for and with banks to target, arrest, and politically disable peaceful American citizens.
Note: For analysis of these amazing documents revealing the use of joint government and corporate counterterrorism structures against peaceful protestors of financial corruption, click here and here. For a Democracy Now! video segment on this, click here.
Undercover police officers routinely adopted a tactic of "promiscuity" with the blessing of senior commanders, according to a former agent who worked in a secretive unit of the Metropolitan police for four years. The former undercover policeman claims that sexual relationships with activists were sanctioned for both men and women officers infiltrating anarchist, leftwing and environmental groups. Sex was a tool to help officers blend in, the officer claimed, and was widely used as a technique to glean intelligence. He said undercover officers, particularly those infiltrating environmental and leftwing groups, viewed having sex with a large number of partners "as part of the job". His comments contradict claims last week from the Association of Chief Police Officers that operatives were absolutely forbidden to sleep with activists. The claims follow the unmasking of undercover PC Mark Kennedy, who had sexual relationships with several women during the seven years he spent infiltrating a ring of environmental activists. Another two covert officers have been named in the past fortnight who also had sex with the protesters they were sent to spy on, fuelling allegations that senior officers had authorised sleeping around as a legitimate means of gathering intelligence.
Note: For a comprehensive overview of the still-ongoing revelations about police provocateur Mark Kennedy and his cohorts in the UK police infiltration of environmental and related activist groups, click here.
Law enforcement is tracking Americans' cell phones in real timewithout the benefit of a warrant. Amid all the furor over the Bush administration's warrantless wiretapping program a few years ago, a mini-revolt was brewing over another type of federal snooping that was getting no public attention at all. Federal prosecutors were seeking what seemed to be unusually sensitive records: internal data from telecommunications companies that showed the locations of their customers' cell phonessometimes in real time, sometimes after the fact. Prosecutors "were using the cell phone as a surreptitious tracking device," said Stephen W. Smith, a federal magistrate in Houston. "And I started asking the U.S. Attorney's Office, 'What is the legal authority for this? What is the legal standard for getting this information?'" Those questions are now at the core of a constitutional clash between President Obama's Justice Department and civil libertarians alarmed by what they see as the government's relentless intrusion into the private lives of citizens. There are numerous other fronts in the privacy warsabout the content of e-mails, for instance, and access to bank records and credit-card transactions. The Feds now can quietly get all that information. But cell-phone tracking is among the more unsettling forms of government surveillance, conjuring up Orwellian images of Big Brother secretly following your movements through the small device in your pocket.
Note: For many key reports from major media sources on the disturbing trend toward increasing government and corporate surveillance, click here.
The Transportation Security Administration ... has on its web site a mythbuster that tries to reassure the public. Myth: The No-Fly list includes an 8-year-old boy. Buster: No 8-year-old is on a T.S.A. watch list. Meet Mikey Hicks, said Najlah Feanny Hicks, introducing her 8-year-old son, a New Jersey Cub Scout and frequent traveler who has seldom boarded a plane without a hassle because he shares the name of a suspicious person. Its not a myth. Hickss mother initially sensed trouble when he was a baby and she could not get a seat for him on their flight to Florida at an airport kiosk; airline officials explained that his name was on the list, she recalled. The first time he was patted down, at Newark Liberty International Airport, Mikey was 2. He cried. After years of long delays and waits for supervisors at every airport ticket counter, this years vacation to the Bahamas badly shook up the family. Mikey was frisked on the way there, then more aggressively on the way home. Up your arms, down your arms, up your crotch someone is patting your 8-year-old down like hes a criminal, Mrs. Hicks recounted. It is true that Mikey is not on the federal governments no-fly list, which includes about 2,500 people, less than 10 percent of them from the United States. But his name appears to be among some 13,500 on the larger selectee list, which sets off a high level of security screening.
Note: For many reports from major media sources on the extreme loss of liberties brought about by the highly touted "war on terrorism," click here.
Every phone call, text message, email and website visit made by private citizens is to be stored for a year and will be available for monitoring by government bodies. All telecoms companies and internet service providers will be required by law to keep a record of every customer’s personal communications, showing who they have contacted, when and where, as well as the websites they have visited. Despite widespread opposition to the increasing amount of surveillance in Britain, 653 public bodies will be given access to the information, including police, local councils, the Financial Services Authority, the ambulance service, fire authorities and even prison governors. They will not require the permission of a judge or a magistrate to obtain the information, but simply the authorisation of a senior police officer or the equivalent of a deputy head of department at a local authority. The Government announced yesterday it was pressing ahead with privately held “Big Brother” databases that opposition leaders said amounted to “state-spying” and a form of “covert surveillance” on the public. It is doing so despite its own consultation showing that it has little public support. The new rules ... will not only force communications companies to keep their records for longer, but to expand the type of data they keep to include details of every website their customers visit.
Note: For many more reports from major media sources on the disturbing trend toward increasing government and corporate surveillance and loss of privacy, click here.
OLBERMANN: It has taken less than 24 hours after the Bush presidency ended for a former analyst at the National Security Agency to come forward to reveal new allegations about how this nation was spied on by its own government. Russell Tice [reveals] that under the collar of fighting terrorism, the Bush administration was also targeting specific groups of Americans for surveillance. TICE: The National Security Agency had access to all Americans communications, faxes, phone calls, and their computer communications. They monitored all communications. What was done was a sort of an ability to look at the meta data, the signaling data for communications, and ferret that information to determine what communications would ultimately be collected. Basically, filtering out sort of like sweeping everything with that meta data, and then cutting down ultimately what you are going to look at and what is going to be collected, and in the long run have an analyst look at, you know, needles in a haystack for what might be of interest. OLBERMANN: I mention that you say specific groups were targeted. What group or groups can you tell us about? TICE: [Some of the groups they] collected on were U.S. news organizations and reporters and journalists. The collection ... was 24/7, and you know, 365 days a year, and it made no sense.
Note: To watch this revealing clip on video, click here. For many reports on government surveillance and invasions of privacy, click here.
Outside the convention hall, New York City police plan to control protesters using a device that directs sound for up to 1,500 feet in a spotlight-like beam. Meanwhile, a display of former Republican presidents inside the hall will feature campaign speeches that are funneled to listeners through highly focused audio beams. Both technologies feature unprecedented manipulation of sound, but for very different purposes. And while both technologies have unique, "gee-whiz" factors, some remain uneasy with the idea of using sound to control crowds. When in weapon mode, LRAD blasts a tightly controlled stream of caustic sound that can be turned up to high enough levels to trigger nausea or possibly fainting. LRAD ... has been used by the U.S. military in Iraq and at sea as a non-lethal force. In these settings, operators can use the device not only to convey orders, but also as a weapon. In tests, police have shown how they can convey orders in a normal voice to someone as far as four blocks away. The sound beam is even equipped with a viewfinder so the operator can precisely target the audio by finding a person in cross hairs. Rather than using pure volume to throw sound far, the LRAD reaches distant ears by focusing the audio beam. Wherever the beam makes contact with air, the air molecules interact in a way that isolates the original audible sound. So if you're standing in front of the ultrasonic sound wave, you can hear the sound. If you're a few inches away, you hear nothing. Already, some Coca-Cola machines in Japan are equipped with the technology so passers-by hear the enticing sound of soda being poured into a glass of ice.
Note: For more reliable information on these "non-lethal weapons," click here.
Whats more devilishly un-American than launching one of the most massive government surveillance programs of private citizens in U.S. history, all under the guise of protecting people from the coronavirus? Thats the COVID-19 Testing, Reaching, And Contacting Everyone (TRACE) Act in all its $100 billion grant giveaway glory. According to H.R. 6666s text: The taxpayer funds will be used to trace and monitor the contacts of infected individuals, and to support the quarantine of such contacts, through mobile health units and, as necessary ... at [citizens] residences. That means government comes to your home, taps on your door and demands you take a COVID-19 test. And if you test positive, that means the government makes sure you stay at home. The top dogs at the Health and Human Services and the Centers for Disease Control and Prevention are in control of disbursing the $100 billion to local governments to carry out the COVID-19 testing more specifically, to hire, train, compensate and pay the expenses of individuals to staff mobile health units and to knock on citizens doors and to enforce compliance with quarantining. This is nothing but a massive government surveillance program cloaked in a cure-the-coronavirus label. A petition at Change.org to stop the nonsense has generated about 28,000 signatures. HR 6666 violates inalienable rights to ones person, home and property, to ones life, freedoms, privacy and security, the petition states.
Note: Why the huge price tag of $100 billion, which is more than the entire 2019 budget for the US Dept. of Health and Human Services? Explore this bill which greatly threatens privacy and civil rights on the website of the US Congress at this link. This excellent and well researched video leaves little doubt that some people will be taken from their homes and children taken from their mothers. For those concerned about being traced and quarantined, this article has good information on who is behind it all. Sign a petition opposing this bill on this webpage.
Did you know that the United States, Canada, Britain, Australia, and New Zealand participate together in an electronic eavesdropping cooperative called "The Five Eyes Alliance"? Or that Britain "has secretly gained access to the network of cables which carry the world's phone calls and internet traffic and has started to process vast streams of sensitive personal information which it is sharing with its American partner, the National Security Agency"? One key innovation has been GCHQ's ability to tap into and store huge volumes of data drawn from fibre-optic cables for up to 30 days so that it can be sifted and analysed. GCHQ and the NSA are consequently able to access and process vast quantities of communications between entirely innocent people, as well as targeted suspects. This includes recordings of phone calls, the content of email messages, entries on Facebook and the history of any internet user's access to websites - all of which is deemed legal, even though the warrant system was supposed to limit interception to a specified range of targets. Say you're the NSA. By law, there are certain sorts of spying you're not lawfully allowed to do on Americans. (And agency rules constraining you too.) But wait. Allied countries have different laws and surveillance rules. Put bluntly, intelligence agencies have an incentive to make themselves complicit in foreign governments spying on their own citizens.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
As China encourages people to return to work despite the coronavirus outbreak, it has begun a bold mass experiment in using data to regulate citizens lives by requiring them to use software on their smartphones that dictates whether they should be quarantined or allowed into subways, malls and other public spaces. The system does more than decide in real time whether someone poses a contagion risk. It also appears to share information with the police, setting a template for new forms of automated social control that could persist long after the epidemic subsides. The Alipay Health Code, as Chinas official news media has called the system, was first introduced in the eastern city of Hangzhou ... with the help of Ant Financial, a sister company of the e-commerce giant Alibaba. People in China sign up through Ants popular wallet app, Alipay, and are assigned a color code green, yellow or red that indicates their health status. The system is already in use in 200 cities and is being rolled out nationwide, Ant says. As soon as a user grants the software access to personal data, a piece of the program labeled reportInfoAndLocationToPolice sends the persons location, city name and an identifying code number to a server. The software does not make clear to users its connection to the police. In the United States, it would be akin to the Centers for Disease Control and Prevention using apps from Amazon and Facebook to track the coronavirus, then quietly sharing user information with the local sheriffs office.
Note: Learn in this revealing article how China is blacklisting certain citizens using this system and "banning them from any number of activities, including accessing financial markets or travelling by air or train, as the use of the governments social credit system accelerates." Learn more about the serious risk of the Coronavirus increasing the surveillance state in this excellent article. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
A surveillance program now known as Data Analytical Services (DAS) has for more than a decade allowed federal, state, and local law enforcement agencies to mine the details of Americans’ calls, analyzing the phone records of countless people who are not suspected of any crime, including victims. Using a technique known as chain analysis, the program targets not only those in direct phone contact with a criminal suspect but anyone with whom those individuals have been in contact as well. The DAS program, formerly known as Hemisphere, is run in coordination with the telecom giant AT&T, which captures and conducts analysis of US call records for law enforcement agencies, from local police and sheriffs’ departments to US customs offices and postal inspectors across the country, according to a White House memo reviewed by WIRED. Records show that the White House has provided more than $6 million to the program, which allows the targeting of the records of any calls that use AT&T’s infrastructure—a maze of routers and switches that crisscross the United States. Documents released under public records laws show the DAS program has been used to produce location information on criminal suspects and their known associates, a practice deemed unconstitutional without a warrant in 2018. Orders targeting a nexus of individuals are sometimes called “community of interest” subpoenas, a phrase that among privacy advocates is synonymous with dragnet surveillance.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Should the government have to get a warrant before using a drone to spy on your home and backyard? We think so, and in an amicus brief filed last Friday in Long Lake Township v. Maxon, we urged the Michigan Supreme Court to find that warrantless drone surveillance of a home violates the Fourth Amendment. In this case, Long Lake Township hired private operators to repeatedly fly drones over Todd and Heather Maxon’s home to take aerial photos and videos of their property in a zoning investigation. The Township did this without a warrant and then sought to use this documentation in a court case against them. In our brief, we argue that the township’s conduct was governed by and violated the Fourth Amendment and the equivalent section of the Michigan Constitution. Drone prevalence has soared in recent years, fueled by both private and governmental use. We have documented more than 1,471 law enforcement agencies across the United States that operate drones. In some cities, police have begun implementing “drone as first responder” programs, in which drones are constantly flying over communities in response to routine calls for service. Authorities have routinely used aerial surveillance technologies against individuals participating in racial justice movements. Under this backdrop, states like Florida, Maine, Minnesota, Nevada, North Dakota, and Virginia have enacted statutes requiring warrants for police use of drones.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Car makers Nissan and Kia can collect data on their drivers’ “sexual activity” and “sex lives” — and may sell the info to third-party advertisers, according to a shocking study by an internet privacy watchdog. The creepy collection of personal information by the two auto companies earned them failing grades from The Mozilla Foundation, maker of the Firefox web browser, which ran privacy checks on 25 car brands. The foundation said most car companies can comb through a variety of sources to glean personal information about drivers after they pair their smartphones with a vehicle’s connected services. “This invasive harvesting of information is collected via a web of sensors, microphones, cameras and the phones, apps, and connected services you use in your vehicle,” according to Mozilla Foundation. The car firms can then take that data and sell it to or share it with vendors, insurance companies and others. Of the 25 car brands that were reviewed, Nissan’s privacy policy “is probably the most ... messed up privacy policy we have ever read,” according to Mozilla Foundation. “They come right out and say they can collect and share your sexual activity, health diagnosis data, and genetic information and other sensitive personal information for targeted marketing purposes,” the foundation wrote. Mozilla Foundation also flagged other car companies such as Chrysler, Chevrolet, Toyota, Audi, Jeep, and Honda for “brazenly collecting deeply personal information from the moment they get into a car.”
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The United States government has been secretly amassing a "large amount" of "sensitive and intimate information" on its own citizens, a group of senior advisers informed Avril Haines, the director of national intelligence. The government effort to accumulate data revealing the minute details of Americans' lives [is] described soberly and at length by the director's own panel of experts in a newly declassified report. The report states that the government believes it can "persistently" track the phones of "millions of Americans" without a warrant, so long as it pays for the information. It is often trivial "to deanonymize and identify individuals" from data that was packaged ... for commercial use. Such data may be useful, it says, to "identify every person who attended a protest or rally based on their smartphone location or ad-tracking records." Such civil liberties concerns are prime examples of how "large quantities of nominally 'public' information can result in sensitive aggregations." What's more, information collected for one purpose "may be reused for other purposes," which may "raise risks beyond those originally calculated," an effect called "mission creep." "In the wrong hands," [Office of the Director of National Intelligence] advisers warn, the same mountain of data the government is quietly accumulating could be turned against Americans to "facilitate blackmail, stalking, harassment, and public shaming." These are all offenses that have been committed by intelligence agencies and White House administrations in the past.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
U.S. citizens are being subjected to a relentless onslaught from intrusive technologies that have become embedded in the everyday fabric of our lives, creating unprecedented levels of social and political upheaval. These widely used technologies ... include social media and what Harvard professor Shoshanna Zuboff calls "surveillance capitalism"—the buying and selling of our personal info and even our DNA in the corporate marketplace. But powerful new ones are poised to create another wave of radical change. Under the mantle of the "Fourth Industrial Revolution," these include artificial intelligence or AI, the metaverse, the Internet of Things, the Internet of Bodies (in which our physical and health data is added into the mix to be processed by AI), and my personal favorite, police robots. This is a two-pronged effort involving both powerful corporations and government initiatives. These tech-based systems are operating "below the radar" and rarely discussed in the mainstream media. The world's biggest tech companies are now richer and more powerful than most countries. According to an article in PC Week in 2021 discussing Apple's dominance: "By taking the current valuation of Apple, Microsoft, Amazon, and others, then comparing them to the GDP of countries on a map, we can see just how crazy things have become… Valued at $2.2 trillion, the Cupertino company is richer than 96% of the world. In fact, only seven countries currently outrank the maker of the iPhone financially."
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The secret contract was finalized on Nov. 8, 2021, a deal between a company that has acted as a front for the United States government and the American affiliate of a notorious Israeli hacking firm. Under the arrangement, the Israeli firm, NSO Group, gave the U.S. government access to one of its most powerful weapons — a geolocation tool that can covertly track mobile phones around the world without the phone user’s knowledge or consent. Only five days earlier, the Biden administration had announced it was taking action against NSO, whose hacking tools for years had been abused by governments around the world to spy on political dissidents, human rights activists and journalists. The White House placed NSO on a Commerce Department blacklist, declaring the company a national security threat. The secret contract ... violates the Biden administration’s public policy, and still appears to be active. The contract, reviewed by The Times, stated that the “United States government” would be the ultimate user of the tool, although it is unclear which government agency authorized the deal and might be using the spyware. Elements of America’s expansive national security apparatus in recent years have bought the weapons, deployed them against drug traffickers, and have quietly pushed to consolidate control of them into the hands of the United States and its closest allies. The F.B.I. purchased access in 2019 to NSO’s most powerful hacking tool, known as Pegasus, which invades mobile phones and mines their contents.
Note: Read how journalists and activists have been targeted with NSO Group spyware. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Human rights activists, journalists and lawyers across the world have been targeted by authoritarian governments using hacking software sold by the Israeli surveillance company NSO Group, according to an investigation into a massive data leak. The investigation by the Guardian and 16 other media organisations suggests widespread and continuing abuse of NSO’s hacking spyware, Pegasus. Pegasus is a malware that infects iPhones and Android devices to enable operators of the tool to extract messages, photos and emails, record calls and secretly activate microphones. The leak contains a list of more than 50,000 phone numbers that, it is believed, have been identified as those of people of interest by clients of NSO since 2016. The numbers of more than 180 journalists are listed in the data, including reporters, editors and executives at the Financial Times, CNN, the New York Times, France 24, the Economist, Associated Press and Reuters. The phone number of a freelance Mexican reporter, Cecilio Pineda Birto, was found in the list, apparently of interest to a Mexican client in the weeks leading up to his murder, when his killers were able to locate him at a carwash. He was among at least 25 Mexican journalists apparently selected as candidates for surveillance. The broad array of numbers in the list belonging to people who seemingly have no connection to criminality suggests some NSO clients are breaching their contracts with the company, spying on pro-democracy activists and journalists.
Note: Read more about how NSO Group spyware was used against journalists and activists by the Mexican government. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
The Covid-19 pandemic is now giving Russian authorities an opportunity to test new powers and technology, and the country's privacy and free-speech advocates worry the government is building sweeping new surveillance capabilities. Perhaps the most well-publicized tech tool in Russia's arsenal for fighting coronavirus is Moscow's massive facial-recognition system. Rolled out earlier this year, the surveillance system had originally prompted an unusual public backlash, with privacy advocates filing lawsuits over unlawful surveillance. Coronavirus, however, has given an unexpected public-relations boost to the system. Last week, Moscow police claimed to have caught and fined 200 people who violated quarantine and self-isolation using facial recognition and a 170,000-camera system. Some of the alleged violators who were fined had been outside for less than half a minute before they were picked up by a camera. And then there's the use of geolocation to track coronavirus carriers. Prime Minister Mikhail Mishustin earlier this week ordered Russia's Ministry of Communications to roll out a tracking system based on "the geolocation data from the mobile providers for a specific person" by the end of this week. According to a description in the government decree, information gathered under the tracking system will be used to send texts to those who have come into contact with a coronavirus carrier, and to notify regional authorities so they can put individuals into quarantine.
Note: For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus pandemic and the disappearance of privacy from reliable major media sources.
Like the 9/11 terrorist attacks in the U.S., the coronavirus pandemic is a crisis of such magnitude that it threatens to change the world in which we live, with ramifications for how leaders govern. Governments are locking down cities with the help of the army, mapping population flows via smartphones and jailing or sequestering quarantine breakers using banks of CCTV and facial recognition cameras backed by artificial intelligence. The restrictions are unprecedented in peacetime and made possible only by rapid advances in technology. And while citizens across the globe may be willing to sacrifice civil liberties temporarily, history shows that emergency powers can be hard to relinquish. A primary concern is that if the public gives governments new surveillance powers to contain Covid-19, then governments will keep these powers after the public health crisis ends, said Adam Schwartz ... at the non-profit Electronic Frontier Foundation. Nearly two decades after the 9/11 attacks, the U.S. government still uses many of the surveillance technologies it developed in the immediate wake. In part, the Chinese Communist Partys containment measures at the virus epicenter in Wuhan set the tone, with what initially seemed shocking steps to isolate the infected being subsequently adopted in countries with no comparable history of Chinas state controls. For Gu Su ... at Nanjing University, Chinas political culture made its people more amenable to the draconian measures.
Note: For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus and the disappearance of privacy from reliable major media sources.
Mr. Ton-That an Australian techie and onetime model did something momentous: He invented a tool that could end your ability to walk down the street anonymously. His tiny company, Clearview AI, devised a groundbreaking facial recognition app. You take a picture of a person, upload it and get to see public photos of that person, along with links to where those photos appeared. The system whose backbone is a database of more than three billion images that Clearview claims to have scraped from Facebook, YouTube, Venmo and millions of other websites goes far beyond anything ever constructed by the United States government or Silicon Valley giants. Without public scrutiny, more than 600 law enforcement agencies have started using Clearview in the past year. The computer code underlying its app ... includes programming language to pair it with augmented-reality glasses; users would potentially be able to identify every person they saw. The tool could identify activists at a protest or an attractive stranger on the subway, revealing not just their names but where they lived, what they did and whom they knew. And its not just law enforcement: Clearview has also licensed the app to at least a handful of companies for security purposes. Because the police upload photos of people theyre trying to identify, Clearview possesses a growing database of individuals who have attracted attention from law enforcement. The company also has the ability to manipulate the results that the police see.
Note: For lots more on this disturbing new technology, read one writer's personal experience with it. For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
A new generation of technology such as the Beware software being used in Fresno has given local law enforcement officers unprecedented power to peer into the lives of citizens. But the powerful systems also have become flash points for civil libertarians and activists, who say they represent a troubling intrusion on privacy, have been deployed with little public oversight and have potential for abuse or error. This is something thats been building since September 11, said Jennifer Lynch ... at the Electronic Frontier Foundation. First funding went to the military to develop this technology, and now it has come back to domestic law enforcement. Its the perfect storm of cheaper and easier-to-use technologies and money from state and federal governments to purchase it. Perhaps the most controversial and revealing technology is the threat-scoring software Beware. Fresno is one of the first departments in the nation to test the program. As officers respond to calls, Beware automatically runs the address. The searches return the names of residents and scans them against a range of publicly available data to generate a color-coded threat level for each person or address: green, yellow or red. Exactly how Beware calculates threat scores is something that its maker, Intrado, considers a trade secret, so it is unclear how much weight is given to a misdemeanor, felony or threatening comment on Facebook. The fact that only Intrado not the police or the public knows how Beware tallies its scores is disconcerting.
Note: Learn more in this informative article. For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
During New York Gov. Andrew Cuomos daily coronavirus briefing on Wednesday, the somber grimace that has filled our screens for weeks was briefly replaced by something resembling a smile. The inspiration ... was a video visit from former Google CEO Eric Schmidt, who joined the governors briefing to announce that he will be heading up a blue-ribbon commission to reimagine New York states post-Covid reality, with an emphasis on permanently integrating technology into every aspect of civic life. Just one day earlier, Cuomo had announced a similar partnership with the Bill and Melinda Gates Foundation to develop a smarter education system. It has taken some time to gel, but something resembling a coherent Pandemic Shock Doctrine is beginning to emerge. Call it the Screen New Deal. Far more high-tech than anything we have seen during previous disasters, the future that is being rushed into being as the bodies still pile up treats our past weeks of physical isolation not as a painful necessity to save lives, but as a living laboratory for a permanent and highly profitable no-touch future. This is a future in which, for the privileged, almost everything is home delivered, either virtually via streaming and cloud technology, or physically via driverless vehicle or drone, then screen shared on a mediated platform. Its a future in which our every move, our every word, our every relationship is trackable, traceable, and data-mineable by unprecedented collaborations between government and tech giants.
Note: For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus pandemic and the disappearance of privacy from reliable major media sources.
On Sept. 7, 2017, the world heard an alarming announcement from credit ratings giant Equifax: In a brazen cyberattack, somebody had stolen sensitive personal information from more than 140 million people, nearly half the population of the U.S. The information included Social Security numbers, driver's license numbers, information from credit disputes and other personal details. Then, something unusual happened. The data disappeared. Completely. CNBC talked to eight experts. All of them agreed that a breach happened, and personal information from 143 million people was stolen. But none of them knows where the data is now. Security experts haven't seen the data used in any of the ways they'd expect in a theft like this not for impersonating victims, not for accessing other websites, nothing. Most experts familiar with the case now believe that the thieves were working for a foreign government and are using the information not for financial gain, but to try to identify and recruit spies. One former senior intelligence official ... summarized the prevailing expert opinion on how the foreign intelligence agency is using the data. First, he said, the foreign government is probably combining this information with other stolen data, then analyzing it using artificial intelligence or machine learning to figure out who's likely to be or to become a spy for the U.S. government. Second, credit reporting data provides compromising information that can be used to turn valuable people into agents of a foreign government.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
Even before he became director of the FBI, [J. Edgar] Hoover was conducting secret intelligence operations against U.S. citizens he suspected were anarchists, radical leftists or communists. After a series of anarchist bombings went off across the United States in 1919, Hoover sent five agents to infiltrate the newly formed Communist Party. "From that day forward, he planned a nationwide dragnet of mass arrests to round up subversives, round up communists, round up Russian aliens," [author Tim] Weiner says. On Jan. 1, 1920, Hoover sent out the arrest orders, and at least 6,000 people were arrested and detained throughout the country. "When the dust cleared, maybe 1 in 10 was found guilty of a deportable offense," says Weiner. Hoover, Attorney General Mitchell Palmer and Secretary of the Navy Franklin Delano Roosevelt all came under attack for their role in the raids. Hoover started amassing secret intelligence on "enemies of the United States" — a list that included terrorists, communists, spies — or anyone Hoover or the FBI had deemed subversive. Later on, anti-war protesters and civil rights leaders were added to Hoover's list. "Hoover saw the civil rights movement from the 1950s onward and the anti-war movement from the 1960s onward, as presenting the greatest threats to the stability of the American government since the Civil War," [Weiner] says. "These people were enemies of the state, and in particular Martin Luther King [Jr.] was an enemy of the state."
Note: Read more about the FBI's COINTELPRO program. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the erosion of civil liberties from reliable major media sources.
China’s ambition to collect a staggering amount of personal data from everyday citizens is more expansive than previously known. Phone-tracking devices are now everywhere. The police are creating some of the largest DNA databases in the world. And the authorities are building upon facial recognition technology to collect voice prints from the general public. The Times’ Visual Investigations team and reporters in Asia spent over a year analyzing more than a hundred thousand government bidding documents. The Chinese government’s goal is clear: designing a system to maximize what the state can find out about a person’s identity, activities and social connections. In a number of the bidding documents, the police said that they wanted to place cameras where people go to fulfill their common needs — like eating, traveling, shopping and entertainment. The police also wanted to install facial recognition cameras inside private spaces, like residential buildings, karaoke lounges and hotels. Authorities are using phone trackers to link people’s digital lives to their physical movements. Devices known as WiFi sniffers and IMSI catchers can glean information from phones in their vicinity. DNA, iris scan samples and voice prints are being collected indiscriminately from people with no connection to crime. The government wants to connect all of these data points to build comprehensive profiles for citizens — which are accessible throughout the government.
Note: For more on this disturbing topic, see the New York Times article “How China is Policing the Future.” For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Even if you have never set foot in China, Hikvision’s cameras have likely seen you. By 2017, Hikvision had captured 12 percent of the North American market. Its cameras watched over apartment buildings in New York City, public recreation centers in Philadelphia, and hotels in Los Angeles. Police departments used them to monitor streets in Memphis, Tennessee, and in Lawrence, Massachusetts. London and more than half of Britain’s 20 next-largest cities have deployed them. A recent search for the company’s cameras, using Shodan, a tool that locates internet-connected devices, yielded nearly 5 million results, including more than 750,000 devices in the United States. Among the policies that Hikvision’s products have supported is China’s wide-ranging crackdown against the predominantly Muslim Uyghurs and other minority groups in the western province of Xinjiang. Far from being appalled by Hikvision’s role in China’s atrocities, however, plenty of foreign leaders are intrigued. They see an opportunity to acquire tools that could reduce crime and spur growth. Of course, the authoritarian-leaning among them also see a chance to monitor their domestic challengers and cement their control. The use of military language ... heightens the sense that these tools can easily become weapons. Cameras can be set to “patrol.” “Intrusion detection” sounds like a method for defending a bank or a military base. Hikvision’s cameras do not check identities. They “capture” faces.
Note: For more, see this Bloomberg article titled “Blacklisted Chinese Tech Found Inside Top Secret UK Lab.” For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
A video showing a mobile device snapping infrared images of an iPhone user is circulating around the internet. In the Tik Tok shared by user Brie Thomason, a digital camera using an infrared lens is seen filming an iPhone user observing their home screen. As the iPhone user stares blatantly at the device, Thomason’s digital camera captures the iPhone snapping multiple infrared images every 5-10 seconds. While this discovery may cause some users to panic, Apple claims this is actually just an aspect of the iPhone that allows users to control their face ID and Animoji (the animated emoji function). According to Apple, this feature was first debuted as the iPhone X’s most groundbreaking function; since it is not even discernible at first glance, even though it literally stares you in the face. The company calls this feature: the new TrueDepth IR camera. This camera, housed in the black notch at the top of the display, includes a number of high-tech components such as a “flood illuminator,” infrared (IR) camera, and an infrared emitter. Officials say as an iPhone is used, the latter emits 30,000 infrared dots in a known pattern when a face is detected, enabling the iPhone X to generate a 3D map of a user’s face. According to the team, this TrueDepth IR camera can also do this fast enough to support the creation of 3D motion data as well. So, yes, your iPhone is essentially taking “invisible” photos of you, but not for the reasons you would think.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
Netflixs brilliant new 90-minute docu-drama, The Social Dilemma ... might be the most important watch of recent years. The film, which debuted at Sundance Film Festival in January, takes a premise thats unlikely to set the world alight ... ie that Facebook, Twitter, Instagram et al arent exactly creating a utopia. Its masterstroke is in recruiting the very Silicon Valley insiders that built these platforms to explain their terrifying pitfalls which theyve realised belatedly. You dont get a much clearer statement of social medias dangers than an ex-Facebook executives claim that: In the shortest time horizon Im most worried about civil war. The commonly held belief that social media companies sell users data is quickly cast aside the data is actually used to create a sophisticated psychological profile of you. What theyre selling is their ability to manipulate you, or as one interviewee puts it: Its the gradual, slight, imperceptible change in your own behaviour and perception. Its the only thing for them to make money from: changing what you do, how you think, who you are. Despite it being public knowledge that Vote Leave and Trumps 2016 election campaign harvested voters Facebook data on a gigantic scale, The Social Dilemma still manages to find fresh and vital tales of how these platforms destabilise modern politics. Russias Facebook hack to influence the 2016 US election? The Russians didnt hack Facebook. They used the tools that Facebook made for legitimate advertisers, laments one of the companys ex-investors.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and media manipulation from reliable sources.
A secret British spy unit created to mount cyber attacks on Britains enemies has waged war on the hacktivists of Anonymous and LulzSec, according to documents taken from the National Security Agency by Edward Snowden and obtained by NBC News. The blunt instrument the spy unit used to target hackers, however, also interrupted the web communications of political dissidents who did not engage in any illegal hacking. It may also have shut down websites with no connection to Anonymous. A division of Government Communications Headquarters (GCHQ), the British counterpart of the NSA, shut down communications among Anonymous hacktivists by launching a denial of service (DDOS) attack the same technique hackers use to take down bank, retail and government websites making the British government the first Western government known to have conducted such an attack. The documents ... show that the unit known as the Joint Threat Research Intelligence Group, or JTRIG, boasted of using the DDOS attack which it dubbed Rolling Thunder - and other techniques to scare away 80 percent of the users of Anonymous internet chat rooms. Among the methods listed in the document were jamming phones, computers and email accounts and masquerading as an enemy in a "false flag" operation. A British hacktivist known as T-Flow, who was prosecuted for hacking, [said] no evidence of how his identity was discovered ever appeared in court documents.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption from reliable major media sources.
Police in the U.S. recently combined two existing dystopian technologies in a brand new way to violate civil liberties. A police force in California recently employed the new practice of taking a DNA sample from a crime scene, running this through a service provided by US company Parabon NanoLabs that guesses what the perpetrators face looked like, and plugging this rendered image into face recognition software to build a suspect list. Parabon NanoLabs ... alleges it can create an image of the suspect’s face from their DNA. Parabon NanoLabs claim to have built this system by training machine learning models on the DNA data of thousands of volunteers with 3D scans of their faces. The process is yet to be independently audited, and scientists have affirmed that predicting face shapes—particularly from DNA samples—is not possible. But this has not stopped law enforcement officers from seeking to use it, or from running these fabricated images through face recognition software. Simply put: police are using DNA to create a hypothetical and not at all accurate face, then using that face as a clue on which to base investigations into crimes. This ... threatens the rights, freedom, or even the life of whoever is unlucky enough to look a little bit like that artificial face. These technologies, and their reckless use by police forces, are an inherent threat to our individual privacy, free expression, information security, and social justice.
Note: Law enforcement officers in many U.S. states are not required to reveal that they used face recognition technology to identify suspects. For more along these lines, see concise summaries of important news articles on police corruption and the erosion of civil liberties from reliable major media sources.
In 2015, the journalist Steven Levy interviewed Elon Musk and Sam Altman, two founders of OpenAI. A galaxy of Silicon Valley heavyweights, fearful of the potential consequences of AI, created the company as a non-profit-making charitable trust with the aim of developing technology in an ethical fashion to benefit “humanity as a whole”. Musk, who stepped down from OpenAI’s board six years ago ... is now suing his former company for breach of contract for having put profits ahead of the public good and failing to develop AI “for the benefit of humanity”. In 2019, OpenAI created a for-profit subsidiary to raise money from investors, notably Microsoft. When it released ChatGPT in 2022, the model’s inner workings were kept hidden. It was necessary to be less open, Ilya Sutskever, another of OpenAI’s founders and at the time the company’s chief scientist, claimed in response to criticism, to prevent those with malevolent intent from using it “to cause a great deal of harm”. Fear of the technology has become the cover for creating a shield from scrutiny. The problems that AI poses are not existential, but social. From algorithmic bias to mass surveillance, from disinformation and censorship to copyright theft, our concern should not be that machines may one day exercise power over humans but that they already work in ways that reinforce inequalities and injustices, providing tools by which those in power can consolidate their authority.
Note: Read more about the dangers of AI in the hands of the powerful. For more along these lines, see concise summaries of deeply revealing news articles on media manipulation and the disappearance of privacy from reliable sources.
In 2018 ... the government was buying up reams of consumer data — information scraped from cellphones, social media profiles, internet ad exchanges and other open sources — and deploying it for often-clandestine purposes like law enforcement and national security in the U.S. and abroad. The places you go, the websites you visit, the opinions you post — all collected and legally sold to federal agencies. The data is used in a wide variety of law enforcement, public safety, military and intelligence missions, depending on which agency is doing the acquiring. We’ve seen it used for everything from rounding up undocumented immigrants or detecting border tunnels. We’ve also seen data used for man hunting or identifying specific people in the vicinity of crimes or known criminal activity. And generally speaking, it’s often used to identify patterns. It’s often used to look for outliers or things that don’t belong. So say you have a military facility, you could look for devices that appear suspicious that are lingering near that facility. Did you know that your car tires actually broadcast a wireless signal to the central computer of your car, telling it what the tire pressure is? It’s there for perfectly legitimate safety reasons. Governments have ... figured out that the car tire is a proxy for the car. And if you just put little sensors somewhere or you run the right code on devices that you scatter around the world, then you can kind of track people with car tires.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
The annual “Trouble in Toyland” report, produced by the U.S. Public Interest Research Group (PIRG) and released before the holiday season, historically has focused on safety hazards found in traditional children’s toys. According to the 38th annual “Trouble in Toyland” report, released in mid-November, “Toys that spy on children are a growing threat.” The threats “stem from toys with microphones, cameras and trackers, as well as recalled toys, water beads, counterfeits and Meta Quest VR headsets.” “The riskiest features of smart toys are those that can collect information, especially without our knowledge or used in a way that parents didn’t agree to,” said Teresa Murray, Consumer Watchdog at the U.S. PIRG Education Fund and author of the report. “It’s chilling to learn what some of these toys can do,” Murray said. Smart toys include “stuffed animals that listen and talk, devices that learn their habits, games with online accounts, and smart speakers, watches, play kitchens and remote cars that connect to apps or other technology,” according to PIRG. Smart toys can pose the risk of data breaches, hacking, potential violations of children’s privacy laws such as the Children’s Online Privacy Protection Act of 1998 (COPPA), and exposure to “inappropriate or harmful material without proper filtering and parental controls.” According to PIRG, “We don’t know with certainty when our child plays with a connected toy that the company isn’t recording us or collecting our data.”
Note: A 2015 New York Times article called smart objects a "trainwreck in privacy and security." For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
Google maintains one of the world’s most comprehensive repositories of location information. Drawing from phones’ GPS coordinates, plus connections to Wi-Fi networks and cellular towers, it can often estimate a person’s whereabouts to within several feet. It gathers this information in part to sell advertising, but police routinely dip into the data to further their investigations. The use of search data is less common, but that, too, has made its way into police stations throughout the country. Traditionally, American law enforcement obtains a warrant to search the home or belongings of a specific person, in keeping with a constitutional ban on unreasonable searches and seizures. Warrants for Google’s location and search data are, in some ways, the inverse of that process, says Michael Price, the litigation director for the National Association of Criminal Defense Lawyers’ Fourth Amendment Center. Rather than naming a suspect, law enforcement identifies basic parameters—a set of geographic coordinates or search terms—and asks Google to provide hits, essentially generating a list of leads. By their very nature, these Google warrants often return information on people who haven’t been suspected of a crime. In 2018 a man in Arizona was wrongly arrested for murder based on Google location data. Google says it received a record 60,472 search warrants in the US last year, more than double the number from 2019. The company provides at least some information in about 80% of cases.
Note: For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
Palantir’s founding team, led by investor Peter Thiel and Alex Karp, wanted to create a company capable of using new data integration and data analytics technology — some of it developed to fight online payments fraud — to solve problems of law enforcement, national security, military tactics, and warfare. Palantir, founded in 2003, developed its tools fighting terrorism after September 11, and has done extensive work for government agencies and corporations though much of its work is secret. Palantir’s MetaConstellation platform allows the user to task ... satellites to answer a specific query. Imagine you want to know what is happening in a certain location and time in the Arctic. Click on a button and MetaConstelation will schedule the right combination of satellites to survey the designated area. The platform is able to integrate data from multiple and disparate sources — think satellites, drones, and open-source intelligence — while allowing a new level of decentralised decision-making. Just as a deep learning algorithm knows how to recognise a picture of a dog after some hours of supervised learning, the Palantir algorithms can become extraordinarily apt at identifying an enemy command and control centre. Alex Karp, Palantir’s CEO, has argued that “the power of advanced algorithmic warfare systems is now so great that it equates to having tactical nuclear weapons against an adversary with only conventional ones.”
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
A MintPress News investigation has found dozens of ex-U.S. State Department officials working in key positions at TikTok. Many more individuals with backgrounds in the FBI, CIA and other departments of the national security state also hold influential posts at the social media giant, affecting the content that over one billion users see. The influx of State Department officials into TikTok’s upper ranks is a consequence of “Project Texas,” an initiative the company began in 2020 in the hopes of avoiding being banned altogether in the United States. During his time in office, Secretary of State Mike Pompeo led the charge to shut the platform down, frequently labeling it a “spying app” and a “propaganda tool for the Chinese Communist Party.” It was widely reported that the U.S. government had forced the sale of TikTok to Walmart and then Microsoft. But in late 2020, as Project Texas began, those deals mysteriously fell through, and the rhetoric about the dangers of TikTok from officials evaporated. Project Texas is a $1.5 billion security operation to move the company’s data to Austin. In doing so, it announced that it was partnering with tech giant Oracle, a corporation that, as MintPress has reported on, is the CIA in all but name. Evidently, Project Texas also secretly included hiring all manner of U.S. national security state personnel to oversee the company’s operations – and not just from the State Department. Virtually every branch of the national security state is present at TikTok.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corruption in intelligence agencies and in the corporate world from reliable major media sources.
In March 2003, the newly christened Department of Homeland Security, or DHS, opened its doors. The department took everything from immigration enforcement and counterterrorism to airport security and disaster response under one gargantuan bureaucracy. Despite these wide-ranging missions, the department's unifying logic in the post 9/11 era has been to wage the so-called war on terror at home. The result has been systemic abuse of minority communities, a dangerous militarization of American life, and a massive waste of money that sapped resources from addressing the real threats to our homeland. DHS agencies have militarized U.S. streets, sending officers in tactical gear to respond to civilian protests and conducting surveillance of U.S. citizens engaged in constitutionally protected activities. There are stories of DHS drones surveilling Indigenous water and land protectors and DHS forces spying on Black Lives Matter protesters. DHS even monitored journalists who reported on the department's tactics. None of these abuses have come cheap. Since its founding in 2003, the U.S. has spent $1.4 trillion on the agency. That's more than seven times what the government spent over the same period on the Centers for Disease Control and Prevention (CDC), including the CDC's COVID-19 pandemic response—and more than five times more than on the Environmental Protection Agency. The [DHS] was supposed to be about making the U.S. safer. But it has failed.
Note: A thorough investigation reveals details on the DHS "Disinformation Governance Board," an unsuccessful effort in 2022 to police online speech it considers inaccurate and dangerous. Now, the DHS board and its key subcommittees are undergoing sweeping changes as public concern grows over social media censorship and government overreach.
The fingerprints of unvaccinated New York City teachers were reportedly sent to the FBI with "problem code" flags, prompting outrage from former educators who lost their jobs over the mandate. Earlier this month, John Bursch, who is representing teachers who are suing the city over the mandate, said teachers who refused the shot now have a "flag in their file," which will impact their ability to get another job. "When the city puts these problem codes on employees who have been terminated because of their unconstitutional policies, not only do they have this flag in their files, but their fingerprints are sent with that flag to the FBI and the New York Criminal Justice Services, so it impacts their ongoing ability to get employment at other places," Bursch said Feb. 8. Investigative journalist Betsy Combier wrote an affidavit uncovering how the Education Department was allegedly able to "flag" certain teachers without sufficient evidence of wrongdoing. "I found out that the DOE has right now an agency called the Office of Personnel Investigation, and what they do is they have employees of the DOE who, forgive me, call themselves investigators, but they're not," Combier said. "So they work for OPI, and when they get an accusation from anybody, it doesn't matter who, well, the principals send it to them, but the original complaint against somebody could be made by anybody that this employee, that employee did something wrong."
Note: For more along these lines, see concise summaries of deeply revealing news articles on coronavirus vaccines from reliable major media sources.
The US government’s new mobile app for migrants to apply for asylum at the US-Mexico border is blocking many Black people from being able to file their claims because of facial recognition bias in the tech, immigration advocates say. The app, CBP One, is failing to register many people with darker skin tones, effectively barring them from their right to request entry into the US. People who have made their way to the south-west border from Haiti and African countries, in particular, are falling victim to apparent algorithm bias in the technology that the app relies on. The government announced in early January that the new CBP One mobile app would be the only way migrants arriving at the border can apply for asylum and exemption from Title 42 restrictions. Racial bias in face recognition technology has long been a problem. Increasingly used by law enforcement and government agencies to fill databases with biometric information including fingerprints and iris scans, a 2020 report by Harvard University called it the “least accurate” identifier, especially among darker-skinned women with whom the error rate is higher than 30%. Emmanuella Camille, a staff attorney with the Haitian Bridge Alliance ... said the CBP One app has helped “lighter-skin toned people from other nations” obtain their asylum appointments “but not Haitians” and other Black applicants. Besides the face recognition technology not registering them ... many asylum seekers have outdated cellphones – if they have cellphones at all – that don’t support the CBP One app.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the erosion of civil liberties from reliable major media sources.
Google wants to know where you go so badly that it records your movements even when you explicitly tell it not to. An Associated Press investigation found that many Google services on Android devices and iPhones store your location data even if you've used privacy settings that say they will prevent it from doing so. Computer-science researchers at Princeton confirmed these findings at the AP's request. Storing your minute-by-minute travels carries privacy risks. So the company will let you "pause" a setting called Location History. Google's support page on the subject states: "You can turn off Location History at any time. With Location History off, the places you go are no longer stored." That isn't true. Even with Location History paused, some Google apps automatically store time-stamped location data without asking. For example, Google stores a snapshot of where you are when you merely open its Maps app. And some searches that have nothing to do with location, like "chocolate chip cookies," or "kids science kits," pinpoint your precise latitude and longitude - accurate to the square foot - and save it to your Google account. Since 2014, Google has let advertisers track the effectiveness of online ads at driving foot traffic, a feature that Google has said relies on user location histories. The company is pushing further into such location-aware tracking to drive ad revenue, which rose 20 percent last year to $95.4 billion.
Note: This article instructs you how to effectively delete Google's tracking of your movements. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
Research unveiled today shows how vulnerabilities in smart city technology could be compromised by hackers. Bugs were found in major cities in the U.S. and Europe, with teams from IBM and Threatcare disclosing a series of disturbing scenarios that could soon play out for real. These included the abuse of flood warnings, radiation alarms and, yes, traffic networks. If someone ... were to abuse vulnerabilities like the ones we documented in smart city systems, the effects could range from inconvenient to catastrophic, a report said. The experts were inspired by the recent incident in Hawaii in which an alert warned citizens that a ballistic missile was inbound. The blaring island alarms, made in error, caused mass panic. Research found 17 major flaws in four smart city systems, eight of which were labeled critical. They spotted basic errors, including weak passwords and basic authentication flaws. Security around these sensors and controls must be a lot more stringent, wrote IBMs Daniel Crowley. Attackers could manipulate water level sensor responses to report flooding in an area where there is none - creating panic, evacuations and destabilization, Crowley wrote. In another example, he said: Controlling additional systems could enable an attacker to set off a string of building alarms or trigger gunshot sounds on audio sensors across town, further fueling panic.
Note: This 2015 New York Times article calls 'smart' devices, "a train wreck in privacy and security." Watch an excellent documentary uncovering the serious dangers of smart meters. For more along these lines, see concise summaries of deeply revealing news articles on corruption in government and the disappearance of privacy.
[Here's] how much of your information ... Facebook and Google store about you. Google stores your location ... every time you turn on your phone. You can see a timeline of where youve been from the very first day you started using Google on your phone. Google stores search history across all your devices. Even if you delete your search history and phone history on one device, it may still have data saved from other devices. Google creates an advertisement profile based on your information, including your location, gender, age, hobbies, career, interests, relationship status, possible weight ... and income. Google offers an option to download all of the data it stores about you. Ive requested to download it and the file is 5.5GB big, which is roughly 3m Word documents. Facebook offers a similar option to download all your information. Mine was roughly 600MB, which is roughly 400,000 Word documents. Facebook also stores what it thinks you might be interested in based off the things youve liked and what you and your friends talk about. The data they collect includes tracking where you are, what applications you have installed, when you use them, what you use them for, access to your webcam and microphone at any time, your contacts, your emails, your calendar, your call history, the messages you send and receive, the files you download, the games you play, your photos and videos, your music, your search history, your browsing history, even what radio stations you listen to.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
Sitting in a hotel bar, Alexander Nix, who runs the political data firm Cambridge Analytica, had a few ideas for a prospective client looking for help in a foreign election. The firm could send an attractive woman to seduce a rival candidate and secretly videotape the encounter, Mr. Nix said, or send someone posing as a wealthy land developer to pass a bribe. We have a long history of working behind the scenes, Mr. Nix said. The prospective client, though, was actually a reporter. The encounter was secretly filmed as part of a monthslong investigation into Cambridge Analytica, the data firm with ties to President Trumps 2016 campaign. The results of Channel 4s work were broadcast ... days after reports ... that the firm had harvested the data from more than 50 million Facebook profiles in its bid to develop techniques for predicting the behavior of individual American voters. Less noticed has been the work that Cambridge Analytica and its parent company, the SCL Group, have done outside the United States. Many of our clients dont want to be seen to be working with a foreign company, he told the Channel 4 reporter. We can set up fake IDs and websites. Mr. Nix ... boasted that Cambridge Analytica employs front companies and former spies on behalf of political clients. The information that is uncovered ... is then put into the bloodstream to the internet, said Mark Turnbull, another Cambridge executive. Then watch it grow, he added. It has to happen without anyone thinking, Thats propaganda.
Note: Watch an astounding video revealing how Cambridge Analytica has successfully manipulated national elections around the world using sleazy tactics like pretty women to entrap candidates and offering major bribes while recording the exchange. And here is a video featuring the whistleblower who exposed this.
Regulators have approved the first drug with a sensor that alerts doctors when the medication has been taken. The digital pill combines two existing products: the former blockbuster psychiatric medication Abilify - long used to treat schizophrenia and bipolar disorder - with a sensor tracking system first approved in 2012. Experts say the technology could be a useful tool, but it will also change how doctors relate to their patients as theyre able to see whether they are following instructions. The pill has not yet been shown to actually improve patients medication compliance, a feature insurers are likely to insist on before paying for the pill. Additionally, patients must be willing to allow their doctors and caregivers to access the digital information. The technology carries risks for patient privacy, too, if there are breaches of medical data or unauthorized use as a surveillance tool, said James Giordano, a professor of neurology at Georgetown University Medical Center. Could this type of device be used for real-time surveillance? The answer is of course it could, said Giordano. The new pill, Abilify MyCite, is embedded with a digital sensor that is activated by stomach fluids, sending a signal to a patch worn by the patient and notifying a digital smartphone app that the medication has been taken.
Note: In 2010, it was quietly reported that Novartis AG would be seeking regulatory approval for such "chip-in-a-pill technology". For more along these lines, see concise summaries of deeply revealing news articles on microchip implants and the disappearance of privacy.
WikiLeaks has alleged that the CIA looked into vehicle interference methods that could potentially enable it to assassinate people without detection. According to the whistle-blowing organisation, the CIA explored the tactic in October 2014. It hasnt included any more details about the alleged practice. WikiLeaks included the claim in its release announcing Vault 7, a huge batch of documents, which Julian Assange claims to account for the CIAs entire hacking capacity. As of October 2014 the CIA was also looking at infecting the vehicle control systems used by modern cars and trucks, reads a passage in the release. The purpose of such control is not specified, but it would permit the CIA to engage in nearly undetectable assassinations. The CIA has also been accused of using malware and hacking tools to turn TVs into covert microphones and remotely break into smartphones. The latter, according to WikiLeaks, allowed it to bypass encryption on a number of popular messaging apps, including WhatsApp. WikiLeaks describes Vault 7 as the largest intelligence publication in history and says that the initial batch of 8,761 files is just the first in a series of releases.
Note: See the wikileaks webpage summarizing this most important leak. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
AT&T runs a secret program called Project Hemisphere that that searches millions and millions of call records and analyzes cellular data to help law enforcement spy on Americans, according to documents obtained by The Daily Beast. Police use the data to solve crimes by monitoring if specific cellular towers in the vicinity of wrongdoings picked up a known suspects cell phone. The surveillance project comes to light as the company is on the verge of acquiring Time Warner in one of the biggest media mergers in memory. Law enforcement agencies pay from $100,000 to over $1 million a year for Hemisphere access. Back in 2013, The New York Times called Hemisphere a partnership between AT&T and the government, but Daily Beast says its actually a product AT&T developed, marketed, and sold at a cost of millions of dollars per year to taxpayers. No warrant is required to access Hemisphere, but it does require a promise not to publicly disclose Hemisphere. AT&T owns significant shares in both the landline and cell phone space, which allows the company to possess information that is used by at least 28 intelligence centers. Documents show that AT&T wants to keep Hemisphere a secret, but suspects and anyone charged with a crime have the right to know the evidence against them. The Government agency agrees not to use the data as evidence in any judicial or administrative proceedings unless there is no other available and admissible probative evidence, documents obtained by the Beast said.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
For more than a decade, professional snoops have been able to search troves of ... addresses, DMV records, photographs of a persons car - and condense them into comprehensive reports costing as little as $10. Now they can combine that information with the kinds of things marketers know about you, such as which politicians you donate to, what you spend on groceries, and whether its weird that you ate in last night, to create a portrait of your life and predict your behavior. IDI, a year-old company in the so-called data-fusion business, is the first to centralize and weaponize all that information for its customers. Chief Executive Officer Derek Dubner says the system isnt waiting for requests from clients - its already built a profile on every American adult, including young people who wouldnt be swept up in conventional databases, which only index transactions. These personal profiles include all known addresses, phone numbers, and e-mail addresses; every piece of property ever bought or sold, plus related mortgages; past and present vehicles owned; criminal citations, from speeding tickets on up; voter registration; hunting permits; and names and phone numbers of neighbors. The reports also include photos of cars taken by private companies using automated license plate readers - billions of snapshots tagged with GPS coordinates and time stamps to help PIs surveil people or bust alibis. IDI also runs two coupon websites ... that collect purchasing and behavioral data.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the erosion of privacy.
The secretive British spy agency GCHQ has developed covert tools to seed the internet with false information, including the ability to manipulate the results of online polls, artificially inflate pageview counts on web sites, amplif[y] sanctioned messages on YouTube, and censor video content judged to be extremist. The capabilities, detailed in documents provided by NSA whistleblower Edward Snowden, even include an old standby for pre-adolescent prank callers everywhere: A way to connect two unsuspecting phone users together in a call. The tools were created by GCHQs Joint Threat Research Intelligence Group (JTRIG), and constitute some of the most startling methods of propaganda and internet deception contained within the Snowden archive. Previously disclosed documents have detailed JTRIGs use of fake victim blog posts, false flag operations, honey traps and psychological manipulation to target online activists, monitor visitors to WikiLeaks, and spy on YouTube and Facebook users. A newly released top-secret GCHQ document called JTRIG Tools and Techniques provides a comprehensive, birds-eye view of just how underhanded and invasive this units operations are. The documentavailable in full hereis designed to notify other GCHQ units of JTRIGs weaponised capability when it comes to the dark internet arts, and serves as a sort of hackers buffet for wreaking online havoc.
Note: For more on this, see concise summaries of deeply revealing intelligence agency operations news articles from reliable major media sources.
Ordinary Internet users, American and non-American alike, far outnumber legally targeted foreigners in the communications intercepted by the National Security Agency from U.S. digital networks, according to a four-month investigation by The Washington Post. [90% of] account holders found in a large cache of intercepted conversations, which former NSA contractor Edward Snowden provided in full to The Post, were not the intended surveillance targets but were caught in a net the agency had cast for somebody else. Many of them were Americans. [Many] files, described as useless by the analysts but nonetheless retained, have a startlingly intimate, even voyeuristic quality. They tell stories of love and heartbreak, illicit sexual liaisons, mental-health crises, political and religious conversions, financial anxieties and disappointed hopes. The daily lives of more than 10,000 account holders who were not targeted are catalogued and recorded nevertheless. The cache Snowden provided came from domestic NSA operations under the broad authority granted by Congress in 2008 with amendments to the Foreign Intelligence Surveillance Act. FISA content is generally stored in closely controlled data repositories, and for more than a year. The files offer an unprecedented vantage point on the changes wrought by Section 702 of the FISA amendments, which enabled the NSA to make freer use of methods that for 30 years had required probable cause and a warrant from a judge.
Note: For more on this, see concise summaries of deeply revealing government surveillance news articles from reliable major media sources.
Britain's surveillance agency GCHQ, with aid from the US National Security Agency, intercepted and stored the webcam images of millions of internet users not suspected of wrongdoing, secret documents reveal. GCHQ files dating between 2008 and 2010 explicitly state that a surveillance program codenamed Optic Nerve collected still images of Yahoo webcam chats in bulk and saved them to agency databases, regardless of whether individual users were an intelligence target or not. In one six-month period in 2008 alone, the agency collected webcam imagery including substantial quantities of sexually explicit communications from more than 1.8 million Yahoo user accounts globally. Yahoo ... denied any prior knowledge of the program, accusing the agencies of "a whole new level of violation of our users' privacy". Optic Nerve, the documents provided by NSA whistleblower Edward Snowden show, began as a prototype in 2008 and was still active in 2012. The system, eerily reminiscent of the telescreens evoked in George Orwell's Nineteen Eighty-Four, was used for experiments in automated facial recognition, to monitor GCHQ's existing targets, and to discover new targets of interest. Such searches could be used to try to find terror suspects or criminals making use of multiple, anonymous user IDs. Rather than collecting webcam chats in their entirety, the program saved one image every five minutes from the users' feeds ... to avoid overloading GCHQ's servers. The documents describe these users as "unselected" intelligence agency parlance for bulk rather than targeted collection.
Note: For more on government surveillance, see the deeply revealing reports from reliable major media sources available here.
The U.S. National Security Agency is involved in industrial espionage and will grab any intelligence it can get its hands on regardless of its value to national security, former NSA contractor Edward Snowden told a German TV network. ARD TV quoted Snowden saying the NSA does not limit its espionage to issues of national security and he cited German engineering firm, Siemens as one target. "If there's information at Siemens that's beneficial to U.S. national interests - even if it doesn't have anything to do with national security - then they'll take that information nevertheless," Snowden said. Snowden's claim the NSA is engaged in industrial espionage follows a New York Times report earlier this month that the NSA put software in almost 100,000 computers around the world, allowing it to carry out surveillance on those devices and could provide a digital highway for cyberattacks. The NSA planted most of the software after gaining access to computer networks, but has also used a secret technology that allows it entry even to computers not connected to the Internet, the newspaper said, citing U.S. officials, computer experts and documents leaked by Snowden. Frequent targets of the programme, code-named Quantum, included units of the Chinese military and industrial targets.
Note: For more on the realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
The White House's expert NSA panel may have made headlines ... for telling President Barack Obama to knock off the collection of Americans' meta-data, but surveillance experts said they were surprised that the panel also took to task some controversial non-NSA-related spy tactics as well. One recommendation was to impose much stricter oversight on the FBI's ability to issue National Security Letters (NSLs), which have been used to obtain telephone call records and credit reports in terrorism and espionage cases. Another even more peculiar recommendation by the five national security experts ... was their advice that "governments" shouldn't hack into bank accounts and drain funds. "Governments should not use their offensive cyber capabilities to change the amounts held in financial accounts or otherwise manipulate the financial systems," the unanimous Review Group on Intelligence and Communications Technologies report warned Obama. "That was a strangely specific recommendation for something nobody was talking about," Kel McClanahan, executive director of government transparency group National Security Counselors, told ABC News. Michelle Richardson, the American Civil Liberties Union's legislative council in Washington, also said the findings on "NSLs" and government hacking were unexpected -- but welcomed.
Note: The fact that this expert panel would even mention governments manipulating financial accounts suggests that if it hasn't already happened, some were seriously considering this. For lots more on this strange news, click here. For more on the realities of intelligence agency activities, see the deeply revealing reports from reliable major media sources available here.
British and American intelligence agencies had a comprehensive list of surveillance targets that included the EU's competition commissioner, German government buildings in Berlin and overseas, and the heads of institutions that provide humanitarian and financial help to Africa, top-secret documents reveal. The papers show GCHQ [and the NSA were] targeting organisations such as the United Nations development programme, the UN's children's charity Unicef and Mdecins du Monde, a French organisation that provides doctors and medical volunteers to conflict zones. The head of the Economic Community of West African States (Ecowas) also appears in the documents, along with text messages he sent to colleagues. One GCHQ document, drafted in January 2009, makes clear that the agencies were targeting an email address listed as belonging to another important American ally the "Israeli prime minister". Ehud Olmert was in office at the time. Three further Israeli targets appeared on GCHQ documents, including another email address understood to have been used to send messages between the then Israeli defence minister, Ehud Barak, and his chief of staff, Yoni Koren. The names and details are the latest revelations to come from documents leaked by the whistleblower Edward Snowden. They provoked a furious reaction. The disclosures reflect the breadth of targets sought by the agencies, which goes far beyond the desire to intercept the communications of potential terrorists and criminals, or diplomats and officials from hostile countries.
Note: Later reports revealed that GHCQ also targeted the global human rights organization Amnesty International. For more on the realities of intelligence agency activities, see the deeply revealing reports from reliable major media sources available here.
Its not just the NSA that has been caught spying on Americans. Some of our nations largest corporations have been conducting espionage as well, against civic groups. Thats the lesson of a new report on corporate espionage against nonprofit organizations by ... Essential Information. The title of the report is Spooky Business, and it is apt. Spooky Business is like a Canterbury Tales of corporate snoopery: Hiring investigators to pose as volunteers and journalists. Hacking. Wiretapping. Information warfare. Physical intrusion. Investigating the private lives of nonprofit leaders. Dumpster diving using an active duty police officer to gain access to trash receptacles. Electronic surveillance. Many different types of nonprofit civic organizations have been targeted by corporate spies: environmental, public interest, consumer, food safety, animal rights, pesticide reform, nursing home reform, gun control and social justice. A diverse constellation of corporations has planned or executed corporate espionage against these nonprofit civic organizations. Food companies like Kraft, Coca-Cola, Burger King, McDonalds and Monsanto. Oil companies like Shell, BP and Chevron. Chemical companies like Dow and Sasol. Also involved are the retailers (Wal-Mart), banks (Bank of America), and, of course, the nations most powerful trade association: the U.S. Chamber of Commerce. Plenty of mercenary spooks have joined up to abet them, including former officials at the FBI, CIA, NSA, Secret Service and U.S. military. Sometimes even government contractors are part of the snooping.
Note: For more on corporate corruption, see the deeply revealing reports from reliable major media sources available here.
When Ban Ki-moon, the United Nations secretary general, sat down with President Obama at the White House in April to discuss Syrian chemical weapons, Israeli-Palestinian peace talks and climate change, it was a cordial, routine exchange. The National Security Agency nonetheless went to work in advance and intercepted Mr. Bans talking points for the meeting, a feat the agency later reported as an operational highlight in a weekly internal brag sheet. It was emblematic of an agency that for decades has operated on the principle that any eavesdropping that can be done on a foreign target of any conceivable interest now or in the future should be done. After all, American intelligence officials reasoned, whos going to find out? From thousands of classified documents, the National Security Agency emerges as an electronic omnivore of staggering capabilities, eavesdropping and hacking its way around the world to strip governments and other targets of their secrets, all the while enforcing the utmost secrecy about its own operations. It spies routinely on friends as well as foes, as has become obvious in recent weeks; the agencys official mission list includes using its surveillance powers to achieve diplomatic advantage over such allies as France and Germany and economic advantage over Japan and Brazil, among other countries. The scale of eavesdropping by the N.S.A., with 35,000 workers and $10.8 billion a year, sets it apart.
Note: For more on the realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
The National Security Agency monitored the phone conversations of 35 world leaders after being given the numbers by an official in another US government department, according to a classified document provided by whistleblower Edward Snowden. The confidential memo reveals that the NSA encourages senior officials in its "customer" departments, such as the White House, State and the Pentagon, to share their "Rolodexes" so the agency can add the phone numbers of leading foreign politicians to their surveillance systems. The document notes that one unnamed US official handed over 200 numbers, including those of the 35 world leaders, none of whom is named. These were immediately "tasked" for monitoring by the NSA. The revelation is set to add to mounting diplomatic tensions between the US and its allies, after the German chancellor Angela Merkel ... accused the US of tapping her mobile phone. The NSA memo obtained by the Guardian suggests that such surveillance was not isolated, as the agency routinely monitors the phone numbers of world leaders and even asks for the assistance of other US officials to do so. The memo, dated October 2006 and which was issued to staff in the agency's Signals Intelligence Directorate (SID), was titled "Customers Can Help SID Obtain Targetable Phone Numbers". In the wake of the Merkel row, the US is facing growing international criticism that any intelligence benefit from spying on friendly governments is far outweighed by the potential diplomatic damage.
Note: For more on the hidden realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
The problem and the risk [with surveillance by GCHQ] comes in the area of mass capture of data, or strategic surveillance. This is the kind of intelligence gathering that sucks in data from everyone, everywhere: from phones, internet use from email to website visits, social networking, instant messaging and video calls, and even areas such as video gaming; in short, everything digital. In the US, the Prism programme may have given the NSA access to the servers of companies such as Google and Facebook; in the UK, GCHQ has gained a similar degree of access via its Tempora programme, and the two of them together have a cable- and network-tapping capabilities collectively called Upstream, which have the ability to intercept anything that travels over the internet. This data is fed into a database called XKeyscore, which allows analysts to extract information "in real time", ie immediately. What this adds up to is a new thing in human history: with a couple of clicks of a mouse, an agent of the state can target your home phone, or your mobile, or your email, or your passport number, or any of your credit card numbers, or your address, or any of your log-ins to a web service. Using that "selector", the state can get access to all the content of your communications, via any of those channels; can gather information about anyone you communicate with, can get a full picture of all your internet use, can track your location online and offline. It can, in essence, know everything about you, including thanks to the ability to look at your internet searches what's on your mind.
Note: For an excellent 15-minute BBC Newsnight interview with Glenn Greenwald defending Edward Snowden's release of secret documents, click here. For more on government privacy invasions, see the deeply revealing reports from reliable major media sources available here.
The owner of the e-mail service [Lavabit, Ladar Levison,] said he closed it down after the government, in pursuit of Edward J. Snowden, sought untrammeled access to the protected messages of all his customers. Mr. Levison was willing to allow investigators with a court order to tap Mr. Snowdens e-mail account; he had complied with similar narrowly targeted requests involving other customers about two dozen times. But they wanted more, he said: the passwords, encryption keys and computer code that would essentially allow the government untrammeled access to the protected messages of all his customers. That, he said, was too much. On Aug. 8, Mr. Levison closed Lavabit rather than, in his view, betray his promise of secure e-mail to his customers. On [October 2], a federal judge unsealed documents in the case, allowing the tech entrepreneur to speak candidly for the first time about his experiences. He had been summoned to testify to a grand jury in Virginia; forbidden to discuss his case; held in contempt of court and fined $10,000 for handing over his private encryption keys on paper and not in digital form; and, finally, threatened with arrest for saying too much when he shuttered his business. While Mr. Levisons struggles have been with the F.B.I., hovering in the background is the N.S.A., which has worked secretly for years to undermine or bypass encrypted services like Lavabit so that their electronic message scrambling cannot obstruct the agencys spying. Mr. Levisons case shows how law enforcement officials can use legal tools to pry open messages, no matter how well protected.
Note: For an excellent 15-minute BBC Newsnight interview with Glenn Greenwald defending Edward Snowden's release of secret documents, click here. For more on government privacy invasions, see the deeply revealing reports from reliable major media sources available here.
The US National Security Agency spied on civil rights leader Martin Luther King and boxer Muhammad Ali during the height of the Vietnam War protests, declassified documents reveal. The documents show the NSA also tracked journalists from the New York Times and the Washington Post and two senators. Some NSA officials later described the programme as "disreputable if not outright illegal", the documents show. The operation, dubbed "Minaret", was originally exposed in the 1970s. However, the names of those on the phone-tapping "watch list" had been kept secret until now. The secret papers were published after a government panel ruled in favour of researchers at George Washington University. The university's National Security Archive - a research institute that seeks to check government secrecy - described the names on the NSA's watch-list as "eye-popping". The agency eavesdropped on civil rights leaders Martin Luther King and Whitney Young as well as boxing champion Muhammad Ali, New York Times journalist Tom Wicker and Washington Post columnist Art Buchwald. The NSA also monitored the overseas phone calls of two prominent US senators - Democrat Frank Church and Republican Howard Baker. In 1967 the strength of the anti-war campaign led President Lyndon Johnson to ask US intelligence agencies to find out if some protests were being stoked by foreign governments. Many of those targeted were considered to be critics of US involvement in the Vietnam War. The NSA worked with other spy agencies to draw up the "watch lists" of anti-war critics, tapping their phone calls. The programme continued after Richard Nixon entered the White House in 1969.
Note: These names were kept secret until now allegedly for reason of "national security." Note how this term is repeatedly used to cover up illegal government activity solely to protect those who commit these crimes. For more on the hidden realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
One of the most overlooked aspects of the NSA reporting in the US has been just how global of a story this has become. Last week it was revealed that Belgium's largest telecom, Belgacom, was the victim of a massive hacking attack which systematically compromised its system for as long as two years. Last week, using documents obtained from NSA whistleblower Edward Snowden, Laura Poitras and other Der Spiegel journalists reported in that paper that it was the GCHQ, Britain's intelligence agency, that was behind the attack. According to that report, the attack was carried out by targeting individual engineers at the telecom with malware that allowed GCHQ agents to "own" their computer and thus exploit their access to the telecommunications system. As the US and UK run around the world protesting the hacking activities of others and warning of the dangers of cyber-attacks, that duo is one of the most aggressive and malicious, if not the most aggressive and malicious, perpetrators of those attacks of anyone on the planet. Nobody hacks as prolifically and aggressively as the two countries who most vocally warn of the dangers of hacking. A coalition called Stop Watching Us has been formed by privacy and civil liberties groups from across the political spectrum. On October 26, the 12th anniversary of the enactment of the Patriot Act, they will hold an anti-surveillance rally in Washington DC.
Note: For more on the hidden realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
Today's high-end televisions are almost all equipped with "smart" PC-like features, including Internet connectivity, apps, microphones and cameras. But a recently discovered security hole in some Samsung Smart TVs shows that many of those bells and whistles aren't ready for prime time. The flaws in Samsung Smart TVs, which have now been patched, enabled hackers to remotely turn on the TVs' built-in cameras without leaving any trace of it on the screen. While you're watching TV, a hacker anywhere around the world could have been watching you. Hackers also could have easily rerouted an unsuspecting user to a malicious website to steal bank account information. Samsung quickly fixed the problem after security researchers at iSEC Partners informed the company about the bugs. Samsung sent a software update to all affected TVs. But the glitches speak to a larger problem of gadgets that connect to the Internet but have virtually no security to speak of. Security cameras, lights, heating control systems and even door locks and windows are now increasingly coming with features that allow users to control them remotely. Without proper security controls, there's little to stop hackers from invading users' privacy, stealing personal information or spying on people. In the case of Samsung Smart TVs, iSEC researchers found that they could tap into the TV's Web browser with ease, according to iSEC security analyst Josh Yavor. That gave hackers access to all the functions controlled by the browser, including the TV's built-in camera. "If there's a vulnerability in any application, there's a vulnerability in the entire TV," said Aaron Grattafiori, also an analyst at iSEC.
Note: For how deep this problem goes, read this article. For more on corporate and government privacy invasions, see the deeply revealing reports from reliable major media sources available here.
GCHQ has received at least 100 million from the US to help fund intelligence gathering, raising questions over American influence on the British agencies. The money was paid across a range of projects over three years and resulted in GCHQ spying on behalf of America, according to leaked documents. It also emerged that the intelligence agency wants the ability to exploit any phone, anywhere, any time and that some staff have raised concerns over the morality and ethics of their operational work. The payments from the US National Security Agency (NSA) are detailed in GCHQs annual investment portfolios, leaked by Mr Snowden to The Guardian. The NSA paid GCHQ 22.9 million in 2009, 39.9 million in 2010 and 34.7 million in 2011/12. The 2010 funding included ... 17.2 million for the agencys Mastering the Internet project, which gathers raw information from the web to be analysed. In return, GCHQ has to have the American view in mind when prioritising work, the papers claim. One strategy briefing disclosed the pressure on GCHQ to meet NSA demands, saying: GCHQ must pull its weight and be seen to pull its weight. In another document, from 2010, GCHQ apparently acknowledged that the US had raised a number of issues with regards to meeting NSAs minimum expectations.
Note: For more on government corruption, see the deeply revealing reports from reliable major media sources available here.
A top secret National Security Agency program allows analysts to search with no prior authorization through vast databases containing emails, online chats and the browsing histories of millions of individuals, according to documents provided by whistleblower Edward Snowden. The NSA boasts in training materials that the program, called XKeyscore, is its "widest-reaching" system for developing intelligence from the internet. The files shed light on one of Snowden's most controversial statements, made in his first video interview published by the Guardian on June 10. "I, sitting at my desk," said Snowden, could "wiretap anyone, from you or your accountant, to a federal judge or even the president, if I had a personal email". Training materials for XKeyscore detail how analysts can use it and other systems to mine enormous agency databases by filling in a simple on-screen form giving only a broad justification for the search. The request is not reviewed by a court or any NSA personnel before it is processed. One presentation claims the program covers "nearly everything a typical user does on the internet", including the content of emails, websites visited and searches, as well as their metadata. Analysts can also use XKeyscore and other NSA systems to obtain ongoing "real-time" interception of an individual's internet activity. XKeyscore provides the technological capability [to target] US persons for extensive electronic surveillance without a warrant provided that some identifying information, such as their email or IP address, is known to the analyst.
Note: For more on government privacy invasions, see the deeply revealing reports from reliable major media sources available here.
In the era of intense government surveillance and secret court orders, a murky multimillion-dollar market has emerged. Paid for by U.S. tax dollars, but with little public scrutiny, surveillance fees charged in secret by technology and phone companies can vary wildly. AT&T, for example, imposes a $325 "activation fee" for each wiretap and $10 a day to maintain it. Smaller carriers Cricket and U.S. Cellular charge only about $250 per wiretap. But snoop on a Verizon customer? That costs the government $775 for the first month and $500 each month after that. Regardless of price, the surveillance business is growing. The U.S. government long has enjoyed access to phone networks and high-speed Internet traffic under the U.S. Communications Assistance for Law Enforcement Act to catch suspected criminals and terrorists. More recently, the FBI has pushed technology companies like Google and Skype to guarantee access to real-time communications on their services. As the number of law enforcement requests for data grew and carriers upgraded their technology, the cost of accommodating government surveillance requests increased. AT&T, for example, said it devotes roughly 100 employees to review each request and hand over data. Likewise, Verizon said its team of 70 employees works around the clock, seven days a week to handle the quarter-million requests it gets each year.
Note: For more on government and corporate attacks on privacy, see the deeply revealing reports from reliable major media sources available here.
Britain's spy agency GCHQ has secretly gained access to the network of cables which carry the world's phone calls and internet traffic and has started to process vast streams of sensitive personal information which it is sharing with its American partner, the National Security Agency (NSA). The sheer scale of the agency's ambition is reflected in the titles of its two principal components: Mastering the Internet and Global Telecoms Exploitation, aimed at scooping up as much online and telephone traffic as possible. This is all being carried out without any form of public acknowledgement or debate. One key innovation has been GCHQ's ability to tap into and store huge volumes of data drawn from fibre-optic cables for up to 30 days so that it can be sifted and analysed. GCHQ and the NSA are consequently able to access and process vast quantities of communications between entirely innocent people, as well as targeted suspects. This includes recordings of phone calls, the content of email messages, entries on Facebook and the history of any internet user's access to websites all of which is deemed legal, even though the warrant system was supposed to limit interception to a specified range of targets. The existence of the programme has been disclosed in documents shown to the Guardian by the NSA whistleblower Edward Snowden. Britain's technical capacity to tap into the cables that carry the world's communications ... has made GCHQ an intelligence superpower. A total of 850,000 NSA employees and US private contractors with top secret clearance had access to GCHQ databases.
Note: For solid evidence spy agencies targeted even top politicians, click here. For more on intelligence agency corruption, see the deeply revealing reports from reliable major media sources available here.
Foreign politicians and officials who took part in two G20 summit meetings in London in 2009 had their computers monitored and their phone calls intercepted on the instructions of their British government hosts. Some delegates were tricked into using internet cafes which had been set up by British intelligence agencies to read their email traffic. The disclosure raises new questions about the boundaries of surveillance by GCHQ [Government Communications Headquarters] and its American sister organisation, the National Security Agency [NSA], whose access to phone records and internet data has been defended as necessary in the fight against terrorism and serious crime. There have often been rumours of this kind of espionage at international conferences, but it is highly unusual for hard evidence to confirm it and spell out the detail. The evidence is contained in documents classified as top secret which were uncovered by the NSA whistleblower Edward Snowden and seen by the Guardian. They reveal that during G20 meetings in April and September 2009 GCHQ used what one document calls "ground-breaking intelligence capabilities" to intercept the communications of visiting delegations. This included: Setting up internet cafes where they used an email interception programme and key-logging software to spy on delegates' use of computers; Penetrating the security on delegates' BlackBerrys to monitor their email messages and phone calls; Supplying 45 analysts with a live round-the-clock summary of who was phoning who at the summit.
Note: For deeply revealing reports from reliable major media sources on the hidden realities of intelligence agencies, click here
Since 9/11, there has been, at first secretly but increasingly openly, a revocation of the bill of rights for which this country fought over 200 years ago. In particular, the fourth and fifth amendments of the US constitution, which safeguard citizens from unwarranted intrusion by the government into their private lives, have been virtually suspended. The United States is not now a police state. But given the extent of this invasion of people's privacy, we do have the full electronic and legislative infrastructure of such a state. These powers are extremely dangerous. There are legitimate reasons for ... secrecy about communications intelligence. But what is not legitimate is to use a secrecy system to hide programs that are blatantly unconstitutional. In 1975, Senator Frank Church spoke of the National Security Agency in these terms: "I know the capacity that is there to make tyranny total in America, and we must see to it that this agency and all agencies that possess this technology operate within the law and under proper supervision, so that we never cross over that abyss. That is the abyss from which there is no return." The dangerous prospect of which he warned was that America's intelligence gathering capability which is today beyond any comparison with what existed in his pre-digital era "at any time could be turned around on the American people and no American would have any privacy left." That has now happened. That is what [Edward] Snowden has exposed, with official, secret documents. We have fallen into Senator Church's abyss.
Note: The above was written by Daniel Ellsberg, a former US military analyst who in 1971 leaked the Pentagon Papers, showing how the US public had been misled about the Vietnam war. For more along these lines, see concise summaries of deeply revealing news articles about questionable intelligence agency practices and the erosion of privacy.
The National Security Agency and the FBI are tapping directly into the central servers of nine leading U.S. Internet companies, extracting audio and video chats, photographs, e-mails, documents, and connection logs. The program, code-named PRISM, has not been made public until now. It may be the first of its kind. Equally unusual is the way the NSA extracts what it wants, according to the document: Collection directly from the servers of these U.S. Service Providers: Microsoft, Yahoo, Google, Facebook, PalTalk, AOL, Skype, YouTube, Apple. GCHQ, Britains equivalent of the NSA, also has been secretly gathering intelligence from the same internet companies through an operation set up by the NSA. PRISM was launched from the ashes of President George W. Bushs secret program of warrantless domestic surveillance in 2007, after news media disclosures, lawsuits and the Foreign Intelligence Surveillance Court forced the president to look for new authority. Congress obliged with the Protect America Act in 2007 and the FISA Amendments Act of 2008, which immunized private companies that cooperated voluntarily with U.S. intelligence collection. Government officials and the document itself made clear that the NSA regarded the identities of its private partners as PRISMs most sensitive secret, fearing that the companies would withdraw from the program if exposed. 98 percent of PRISM production is based on Yahoo, Google and Microsoft; we need to make sure we dont harm these sources, the briefings author wrote in his speakers notes.
Note: For graphs and lots more on the Prism program, see the Guardian article at this link. Technically, U.S. officials are not allowed to mine personal data from U.S. citizens. Yet if U.K. authorities mine data on U.S. citizens, they can share it freely with officials in the U.S. and vice versa. There is evidence that this happens quite frequently, thus circumventing privacy protections. For an excellent article which goes deep into this issue, click here.
Through Freedom of Information Act requests and interviews with officials at numerous agencies, The Wall Street Journal has reconstructed the clash over the counterterrorism program within the administration of President Barack Obama. The attorney general [has] signed the changes into effect. The rules now allow the little-known National Counterterrorism Center to examine the government files of U.S. citizens for possible criminal behavior, even if there is no reason to suspect them. That is a departure from past practice, which barred the agency from storing information about ordinary Americans unless a person was a terror suspect or related to an investigation. Now, NCTC can copy entire government databasesflight records, casino-employee lists, the names of Americans hosting foreign-exchange students and many others. The agency has new authority to keep data about innocent U.S. citizens for up to five years, and to analyze it for suspicious patterns of behavior. Previously, both were prohibited. Data about Americans "reasonably believed to constitute terrorism information" may be permanently retained. "It's breathtaking" in its scope, said a former senior administration official. The Fourth Amendment of the Constitution says that searches of "persons, houses, papers and effects" shouldn't be conducted without "probable cause" that a crime has been committed.
Note: This article requires subscription to view at the link above. To read it for free, click here. For analysis of this sweeping increase in government privacy invasions, click here. For deeply revealing reports from reliable major media sources on government privacy invasions, click here.
Most Americans have gotten used to regular news reports about military and CIA drones attacking terrorist suspects including US citizens in Pakistan, Yemen, and elsewhere abroad. But picture thousands of drone aircraft buzzing around the United States. By some government estimates, as many as 30,000 drones could be part of intelligence gathering and law enforcement here in the United States within the next ten years. Operated by agencies down to the local level, this would be in addition to the 110 current and planned drone activity sites run by the military services in 39 states, reported this week by the Federation of American Scientists, a non-government research project. Civil libertarians warn that unmanned aircraft carrying cameras raise the prospect of a significant new avenue for the surveillance of American life, as the American Civil Liberties Union put it in a report last December. The technology is quickly becoming cheaper and more powerful, interest in deploying drones among police departments is increasing, and our privacy laws are not strong enough to ensure that the new technology will be used responsibly and consistently with democratic values, reported the ACLU. In short, all the pieces appear to be lining up for the eventual introduction of routine aerial surveillance in American life.
Note: For deeper analysis of the threats posed to American citizens by military and police drones in the skies, click here. For information on a federal recent law compelling the Federal Aviation Administration to allow drones to fly in US skies, click here. For more information on the use of drones by police in the US, click here. For lots more from reliable sources on surveillance in the US, click here.
The Supreme Court on Monday ruled by a 5-to-4 vote that officials may strip-search people arrested for any offense, however minor, before admitting them to jails even if the officials have no reason to suspect the presence of contraband. Justice Anthony M. Kennedy, joined by the courts conservative wing, wrote that courts are in no position to second-guess the judgments of correctional officials. The procedures endorsed by the majority are forbidden by statute in at least 10 states. According to a supporting brief filed by the American Bar Association, international human rights treaties also ban the procedures. Justice Stephen G. Breyer, writing for the four dissenters, said the strip searches the majority allowed were a serious affront to human dignity and to individual privacy and should be used only when there was good reason to do so. Justice Breyer said that the Fourth Amendment should be understood to bar strip searches of people arrested for minor offenses not involving drugs or violence, unless officials had a reasonable suspicion that they were carrying contraband. People have been subjected to the humiliation of a visual strip search after being arrested for driving with a noisy muffler, failing to use a turn signal and riding a bicycle without an audible bell. A nun was strip-searched ... after an arrest for trespassing during an antiwar demonstration. In a study of 23,000 people admitted to a correctional facility in Orange County, N.Y., using that standard, there was at most one instance of contraband detected that would not otherwise have been found.
Note: For an abundance of major media articles showing severe erosion of civil liberties, click here.
When Annie Brown's daughter, Isabel, was a month old, her pediatrician asked Brown and her husband to sit down because he had some bad news to tell them: Isabel carried a gene that put her at risk for cystic fibrosis. While grateful to have the information -- Isabel received further testing and she doesn't have the disease -- the Mankato, Minnesota, couple wondered how the doctor knew about Isabel's genes in the first place. After all, they'd never consented to genetic testing. It's simple, the pediatrician answered: Newborn babies in the United States are routinely screened for a panel of genetic diseases. Since the testing is mandated by the government, it's often done without the parents' consent, according to Brad Therrell, director of the National Newborn Screening & Genetics Resource Center. In many states, such as Florida, where Isabel was born, babies' DNA is stored indefinitely, according to the resource center. Many parents don't realize their baby's DNA is being stored in a government lab, but sometimes when they find out, as the Browns did, they take action. Parents in Texas, and Minnesota have filed lawsuits, and these parents' concerns are sparking a new debate about whether it's appropriate for a baby's genetic blueprint to be in the government's possession.
Note: For many reliable reports on the increasing governmental and corporate threats to privacy, click here.
Behind the county hospital's tall cinderblock walls, a 27-year-old tuberculosis patient ... sits in a jail cell equipped with a ventilation system that keeps germs from escaping. Robert Daniels has been locked up indefinitely, perhaps for the rest of his life, since last July. But he has not been charged with a crime. Instead, he suffers from an extensively drug-resistant strain of tuberculosis. It is considered virtually untreatable. County health authorities obtained a court order to lock him up as a danger to the public because ... he did not heed doctors' instructions to wear a mask in public. "I'm being treated worse than an inmate," Daniels said. "I'm all alone. Four walls. Even the door to my room has been locked. I haven't seen my reflection in months." He said sheriff's deputies will not let him take a shower -- he cleans himself with wet wipes -- and have taken away his television, radio, personal phone and computer. His only visitors are masked medical staff members who come in to give him his medication. Though Daniels' confinement is extremely rare, health experts say it is a situation that U.S. public health officials may have to confront more and more because of the spread of drug-resistant TB and the emergence of diseases such as SARS and avian flu.
Note: If the above link fails, click here. What possible reason is there for taking away this man's TV, radio, cell phone, and computer? Are we being prepared for mass quarantines and imprisonment due to disease? For more, click here.
Let's say your teenager is a habitual truant and there is nothing you can do about it. A Washington area politician thinks he might have the solution: Fit the child with a Global Positioning System chip, then have police track him down. "It allows them to get caught easier," said Maryland Delegate Doyle Niemann (D-Prince George's), who recently co-sponsored legislation in the House that would use electronic surveillance as part of a broader truancy reduction plan. "It's going to be done unobtrusively. The chips are tiny and can be put into a hospital ID band or a necklace." Niemann's legislation mirrors a bill sponsored by state Sen. Gwendolyn Britt (D-Prince George's). Both would provide truants and their parents with better access to social services, such as mental health evaluations and help with schoolwork. Electronic monitoring would be a last resort. Still, the prospect of tagging children and using them in some "catch and release" hunt by police casts a pall over everything that's good about the plan. Odd how billions and billions of dollars keep going to a war that almost nobody wants, but there's never enough to fund the educational programs that nearly everybody says are needed. Aimed solely at students in Prince George's the only predominantly black county in the Washington area the truancy effort is called a "pilot program," a first-of-its-kind experiment. It would cost $400,000 to keep track of about 660 students a year.
Note: For more reliable information on the push to microchip the entire population, click here.
When Kevin Warwick enters his office building on the campus of Reading University, strange things happen. As Warwick heads down the main hall, lights turn on. When he turns to the right, an office door unbolts and opens. Each step is clocked and recorded. The building knows who he is, where he is, and what he expects to happen. The building [even] says, Hello Professor Warwick. The structure knows Warwick because of the electrical fuse-sized smart card implanted in his left arm. In Britain, hes been dubbed The Cyborg Man, the first person known to have a microchip implanted in his body for communication with outside machines. Warwick predicts chip implants will one day replace time cards, criminal tracking devices, even credit cards. Capable of carrying huge amounts of data, they may, he says, one day be used to identify individuals by Social Security numbers, blood type, even their banking information. No one knows yet how the body will respond to this type of invasion. Warwick is not blind to the ethical questions of this technology. Implants ostensibly designed to clock workers in and out might be misused to monitor where people are at all times and who they are meeting. Governments could move to use implants instead of I.D. cards and passports, but what would stop them from using this new science to invade privacy? I feel mentally different. When I am in the building I feel much more closely connected with the computer.
Note: Those who would like to control the public named these implants "smart cards" to encourage us to accept them. For more reliable information on important topic, click here and here.
Over the last two months, Chinese citizens have had to adjust to a new level of government intrusion. Getting into ones apartment compound or workplace requires scanning a QR code, writing down ones name and ID number, temperature and recent travel history. Telecom operators track peoples movements while social media platforms like WeChat and Weibo have hotlines for people to report others who may be sick. Some cities are offering people rewards for informing on sick neighbours. Chinese companies are meanwhile rolling out facial recognition technology that can detect elevated temperatures in a crowd or flag citizens not wearing a face mask. A range of apps use the personal health information of citizens to alert others of their proximity to infected patients. Experts say the virus ... has given authorities a pretext for accelerating the mass collection of personal data to track citizens. Its mission creep, said Maya Wang, senior China researcher for Human Rights Watch. According to Wang, the virus is likely to be a catalyst for a further expansion of the surveillance regime. Citizens are particularly critical of a system called Health Code, which users can sign up for through Alipay or WeChat, that assigns individuals one of three colour codes based on their travel history, time spent in outbreak hotspots and exposure to potential carriers of the virus. The software, used in more than 100 cities, will soon allow people to check the colours of other residents when their ID numbers are entered.
Note: Learn in this New York Times article how everyone in China is given a red, yellow, or green code which determines how free they are to move about and even enter businesses. This article shows how foreigners are being stopped instantly from making live podcasts from China using facial recognition technology. For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus and the disappearance of privacy from reliable major media sources.
Everywhere you go online, you’re being tracked. Almost every time you visit a website, trackers gather data about your browsing and funnel it back into targeted advertising systems, which build up detailed profiles about your interests and make big profits in the process. At the end of last year, thousands of websites started being more transparent about how many companies your data is being shared with. A WIRED analysis of the top 10,000 most popular websites shows that dozens of sites say they are sharing data with more than 1,000 companies, while thousands of other websites are sharing data with hundreds of firms. Quiz and puzzle website JetPunk tops the pile, listing 1,809 “partners” that may collect personal information, including “browsing behavior or unique IDs.” More than 20 websites from publisher Dotdash Meredith—including Investopedia.com, People.com, and Allrecipes.com—all say they can share data with 1,609 partners. The newspaper The Daily Mail lists 1,207 partners, while internet speed-monitoring firm Speedtest.net, online medical publisher WebMD, and media outlets Reuters, ESPN, and BuzzFeed all state they can share data with 809 companies. DuckDuckGo keeps a record of the companies that have the biggest tracking footprint across the web. Among the most common trackers, Google has its technology on 79 percent of websites, while those from five other companies are on more than 20 percent of websites.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The nation’s largest pharmacy chains have handed over Americans’ prescription records to police and government investigators without a warrant, a congressional investigation found, raising concerns about threats to medical privacy. Though some of the chains require their lawyers to review law enforcement requests, three of the largest — CVS Health, Kroger and Rite Aid, with a combined 60,000 locations nationwide — said they allow pharmacy staff members to hand over customers’ medical records in the store. Pharmacies’ records hold some of the most intimate details of their customers’ personal lives, including years-old medical conditions and the prescriptions they take for mental health and birth control. Because the chains often share records across all locations, a pharmacy in one state can access a person’s medical history from states with more-restrictive laws. The Health Insurance Portability and Accountability Act, or HIPAA, regulates how health information is used and exchanged among “covered entities” such as hospitals and doctor’s offices. But the law gives pharmacies leeway as to what legal standard they require before disclosing medical records to law enforcement. In briefings, officials with eight American pharmacy giants — Walgreens Boots Alliance, CVS, Walmart, Rite Aid, Kroger, Cigna, Optum Rx and Amazon Pharmacy — told congressional investigators that they required only a subpoena, not a warrant, to share the records.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
On the morning of 10 June 2013 ... the journalist Glenn Greenwald and film-maker Laura Poitras published on the Guardian site a video revealing the identity of the NSA whistleblower behind one of the most damning leaks in modern history. It began: "My name is Ed Snowden." William Fitzgerald, then a 27-year-old policy employee at Google, knew he wanted to help. Fitzgerald found himself waiting in the lobby of the Hong Kong W Hotel to meet Greenwald and introduce him to Robert Tibbo and Jonathan Man – the men who became Snowden's legal representatives and hid him in the homes of Tibbo's refugee clients. The Snowden files told a ... sinister story, revealing mass surveillance by the US National Security Agency (NSA). The NSA files suggested that some tech firms, including Google, Facebook and Apple, were aware. Google and other tech firms worked to distance themselves from the NSA's efforts. But over time [Google's] culture appeared to shift, reflecting the changing needs of various governments. Google stopped promoting its transparency report to the media, free expression advocates were replaced by more traditional business-focused executives, and then there was Project Maven – the controversial Department of Defense drone project that Google signed on to build artificial intelligence for. Google isn't alone in vying for government contracts – Microsoft, Amazon, IBM have all since made a play for or struck multimillion-dollar deals to build tools of surveillance for various entities including the Pentagon.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
In the pandemic’s bewildering early days, millions worldwide believed government officials who said they needed confidential data for new tech tools that could help stop coronavirus’ spread. In return, governments got a firehose of individuals’ private health details, photographs that captured their facial measurements and their home addresses. Now, from Beijing to Jerusalem to Hyderabad, India, and Perth, Australia, The Associated Press has found that authorities used these technologies and data to halt travel for activists and ordinary people, harass marginalized communities and link people’s health information to other surveillance and law enforcement tools. In some cases, data was shared with spy agencies. China’s ultra-strict zero-COVID policies recently ignited the sharpest public rebuke of the country’s authoritarian leadership since ... 1989. Just as the balance between privacy and national security shifted after the Sept. 11 terrorist attacks, COVID-19 has given officials justification to embed tracking tools in society that have lasted long after lockdowns. What use will ultimately be made of the data collected and tools developed during the height of the pandemic remains an open question. Australia’s intelligence agencies were caught “incidentally” collecting data from the national COVIDSafe app. In the U.S. ... the federal government took the opportunity to build out its surveillance toolkit, including two contracts in 2020 worth $24.9 million to the data mining and surveillance company Palantir Technologies Inc.
Note: Read an essay by constitutional attorney John W. Whitehead on COVID and the surveillance state. Detroit police recently sought COVID relief funds to install ShotSpotter microphones throughout the city. For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus and the disappearance of privacy from reliable major media sources.
A whistleblower who works in Project Nightingale, the secret transfer of the personal medical data of up to 50 million Americans from one of the largest healthcare providers in the US to Google, has expressed anger to the Guardian that patients are being kept in the dark about the massive deal. The anonymous whistleblower has posted a video on the social media platform Daily Motion that contains a document dump of hundreds of images of confidential files relating to Project Nightingale. The secret scheme ... involves the transfer to Google of healthcare data held by Ascension, the second-largest healthcare provider in the US. The data is being transferred with full personal details including name and medical history and can be accessed by Google staff. Unlike other similar efforts it has not been made anonymous through a process of ... de-identification. The disclosed documents include highly confidential outlines of Project Nightingale, laying out the four stages or pillars of the secret project. By the time the transfer is completed next March, it will have passed the personal data of 50 million or more patients in 21 states to Google, with 10 million or so files already having moved across with no warning having been given to patients or doctors. Google has entered into similar partnerships on a much smaller scale with clients such as the Colorado Center for Personalized Medicine. But in that case all the data handed over to the search giant was encrypted, with keys being held only on the medical side.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
Over time, the CIA upper echelon has secretly developed all kinds of policy statements and legal rationales to justify routine, widespread surveillance on U.S. soil of citizens who arent suspected of terrorism or being a spy. Newly declassified documents from 2014 ... reveal the CIA not only intercepted emails of U.S. citizens but they were emails of the most sensitive kind written to Congress and involving whistleblowers reporting alleged wrongdoing within the Intelligence Community. The disclosures, kept secret until now, are two letters of congressional notification from the Intelligence Community inspector general at the time, Charles McCullough. He stated that during routine counterintelligence monitoring of government computer systems, the CIA collected emails between congressional staff and the CIAs head of whistleblowing and source protection. McCullough added that he was concerned about the CIAs potential compromise to whistleblower confidentiality and the consequent chilling effect. The March 2014 intercepts ... happened amid whats widely referred to as the Obama administrations war on whistleblowers and mass surveillance scandals. The evidence points to bad actors targeting candidate Donald Trump and his associates in part to keep them - and us - from learning about and digging into an even bigger scandal: our Intelligence Community increasingly spying on its own citizens, journalists, members of Congress and political enemies for the better part of two decades.
Note: The above article was written by Emmy award winning investigative journalist and former news anchor for CBS and CNN Sharyl Attkisson. She has been attacked numerous times for questioning the safety of vaccines and investigating too deeply into the lives of certain politicians. Her top-selling book Stonewalled describes her fight for truth against powerful political forces. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
It's no secret that computers are insecure. The risks are about to get worse, because computers are being embedded into physical devices and will affect lives, not just our data. Many of todays new computers are not just screens that we stare at, but objects in our world with which we interact. A refrigerator is now a computer that keeps things cold; a car is now a computer with four wheels and an engine. These computers sense us and our environment, and they affect us and our environment. They talk to each other over networks ... and they have physical agency. They drive our cars, pilot our planes, and run our power plants. They control traffic, administer drugs ... and dispatch emergency services. These connected computers and the network that connects them - collectively known as the internet of things - affect the world in a direct physical manner. Computers fail differently than most other machines: It's not just that they can be attacked remotely - they can be attacked all at once. Its impossible to take an old refrigerator and infect it with a virus or recruit it into a denial-of-service botnet, and a car without an internet connection simply cant be hacked remotely. But that computer with four wheels and an engine? It - along with all other cars of the same make and model - can be made to run off the road, all at the same time. Do we want to allow vulnerable automobiles on the streets and highways during the weeks before a new security patch is written, tested, and distributed?
Note: A 2015 New York Times article called the Internet of Things a "train wreck in privacy and security". Read how a hacked vehicle may have resulted in journalist Michael Hastings' death in 2013. For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy and the risks of wireless technologies.
At least 75 companies receive anonymous, precise location data from apps whose users enable location services. Several of those businesses claim to track up to 200 million mobile devices in the United States about half those in use last year. The database reviewed by The Times ... reveals peoples travels in startling detail, accurate to within a few yards and in some cases updated more than 14,000 times a day. These companies sell, use or analyze the data to cater to advertisers, retail outlets and even hedge funds. Its a hot market, with sales of location-targeted advertising reaching an estimated $21 billion this year. Businesses say their interest is in the patterns, not the identities, that the data reveals. They note that the information apps collect is tied not to someones name or phone number but to a unique ID. But those with access to the raw data including employees or clients could still identify a person without consent. They could follow someone they knew, by pinpointing a phone that regularly spent time at that persons home address. More than 1,000 popular apps contain location-sharing code from such companies. Googles Android system was found to have about 1,200 apps with such code, compared with about 200 on Apples iOS.
Note: For more along these lines, see concise summaries of deeply revealing privacy news articles from reliable major media sources.
By now, almost everyone knows what Edward Snowden did. He leaked top-secret documents revealing that the National Security Agency was spying on hundreds of millions of people. The key to Snowdens effectiveness, according to Thomas Devine, the legal director of the Government Accountability Project (GAP), was that he practised civil disobedience rather than lawful whistleblowing. None of the lawful whistleblowers who tried to expose the governments warrantless surveillance ... had any success, Devine told me. They came forward ... but the government just said, Theyre lying. Were not doing those things. And the whistleblowers couldnt prove their case because the government had classified all the evidence. The NSA whistleblowers were not leftwing peace nuts. They had spent their professional lives inside the US intelligence apparatus devoted, they thought, to the protection of the homeland and defense of the constitution. They were political conservatives, highly educated, respectful of evidence, careful with words. And they were saying, on the basis of personal experience, that the US government was being run by people who were willing to break the law and bend the states awesome powers to their own ends. They were saying that laws and technologies had secretly been put in place that threatened to overturn the democratic governance Americans took for granted and shrink their liberties to a vanishing point.
Note: The article above was is adapted from Mark Hertsgaards book, Bravehearts: Whistle Blowing in the Age of Snowden. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
The disastrous situation at the US-Mexico border is, and has been, intentionally produced. Illegal crossings have risen to unprecedented levels. There is a bipartisan consensus about what must be done. Tellingly, the same “solution” is also being quietly rolled out at all American ports of entry that are not currently being “overrun”, such as airports. That solution, of course, is biometric surveillance, enabled by AI, facial recognition/biometrics and autonomous devices. This “solution” is not just being implemented throughout the United States as an alleged means of thwarting migrants, it is also being rapidly implemented throughout the world in apparent lockstep. Global policy agendas, ratified by nearly every country in the world ... seek both to restrict the extent of people’s freedom of movement and to surveil people’s movements ... through the global implementation of digital identity. The defense tech firm Anduril ... is one of the main beneficiaries of government contracts to build autonomous surveillance towers along the US-Mexico border, which are now also being rolled out along the US-Canada border. Anduril will create “a digital wall that is not a barrier so much as a web of all-seeing eyes, with intelligence to know what it sees.” While Anduril is one of the main companies building the “virtual wall,” they are not alone. General Dynamics, a defense firm deeply connected to organized crime, espionage scandals and corruption, has developed several hundred remote video surveillance systems (RVSS) towers for CBP while Google, another Big Tech firm with CIA connections, has been tapped by CBP to have its AI used in conjunction with Anduril’s towers, which also utilize Anduril’s own AI operating system known as Lattice.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Axon, maker of Tasers and police body cameras, has acquired a surveillance company that allows police to tap into camera networks in schools, retail stores, and other locations in cities and towns across America and apply AI technology to the footage. Axon acquired Fusus for an undisclosed sum. Fusus operates what it calls “real time crime centers (RTCC)” which allow police and other public agencies to analyze a wide array of video sources at a single point and apply AI that detects objects and people. These centers are reminiscent of the Department of Homeland Security’s Fusion Centers—where intelligence from a diverse number of sources is collected and shared among agencies—and have already expanded to over 250 cities and counties. Last week, Axon announced a new line of cameras called Axon Body Workforce designed to be worn by workers in retail and in healthcare. Despite pushing the cameras as deterrents, data shows no evidence that they’ve been effective in reducing police violence or increasing transparency. The rise of Fusus is concerning to rights groups like the Electronic Frontier Foundation, which has raised alarm over the expansion of law enforcement’s ability to easily surveil Americans. Notably, the concept behind Fusus’ solution is similar to technology that has been deployed in South Africa for years, and which experts have said exacerbates inequality in the country.
Note: Axon has ties to paid experts who are used to exonerate police after deaths in custody. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
United States officials fought to conceal details of arrangements between US spy agencies and private companies tracking the whereabouts of Americans. Obtaining location data from US phones normally requires a warrant, but police and intelligence agencies routinely pay companies instead for the data, effectively circumventing the courts. Ron Wyden, the US senator from Oregon, informed the nation’s intelligence chief, Avril Haines, on Thursday that the Pentagon only agreed to release details about the data purchases, which had always been unclassified, after Wyden hindered the Senate's efforts to appoint a new director of the National Security Agency. “The secrecy around data purchases was amplified,” Wyden wrote, “because intelligence agencies have sought to keep the American people in the dark." Pentagon offices known to have purchased location data from these companies include the Defense Intelligence Agency and the NSA, among others. Wyden's letter ... indicates that the NSA is also “buying Americans' domestic internet metadata.” Wyden's disclosure comes amid a fight in the US House of Representatives over efforts to outlaw the purchases. Members of the House Judiciary Committee attached legislation doing so ... to a bill reauthorizing a contentious surveillance program known as Section 702. Biden administration officials and members of the intelligence committee staged a campaign against the privacy-enhancing measures.
Note: Learn more about mission creep in our comprehensive Military-Intelligence Corruption Information Center. For more, see concise summaries of deeply revealing news articles on military corruption and the disappearance of privacy from reliable major media sources.
Mental health apps have become increasingly common over the past few years, particularly due to the rise in telehealth during the coronavirus pandemic. However, there's a problem: Data privacy is being compromised in the process. In 2023 the Federal Trade Commission ordered the mental health platform BetterHelp, which is owned by Teladoc (TDOC), to pay a $7.8 million fine to consumers for sharing their mental health data for advertising purposes with Facebook (META) and Snapchat (SNAP) after previously promising to keep the information private. Cerebral, a telehealth startup, admitted last year to exposing sensitive patient information to companies like Google (GOOG, GOOGL), Meta, TikTok, and other third-party advertisers. This info included patient names, birth dates, insurance information, and the patient's responses to mental health self-evaluations through the app. Overall, according to the Mozilla Foundation’s Privacy Not Included online buyer’s guide, only two out of the 27 mental health apps available to users met Mozilla's privacy and security standards in 2023. A December 2022 study of 578 mental health apps published in the Journal of the American Medical Association found that 44% shared data they collected with third parties. A February 2023 report from Duke University found that out of 37 different data brokers that researchers contacted ... firms “were ultimately willing and able to sell the requested mental health data.”
Note: For more along these lines, see concise summaries of deeply revealing news articles on health and the disappearance of privacy from reliable major media sources.
Apple has said it now requires a judge’s order to hand over information about its customers’ push notification to law enforcement, putting the iPhone maker’s policy in line with rival Google and raising the hurdle officials must clear to get app data about users. It follows the revelation from Oregon Senator Ron Wyden that officials were requesting such data from Apple as well as from Google. Apps of all kinds rely on push notifications to alert smartphone users to incoming messages, breaking news, and other updates. These are the audible “dings” or visual indicators users get when they receive an email or their sports team wins a game. What users often do not realize is that almost all such notifications travel over Google and Apple’s servers. In a letter first disclosed by Reuters last week, Wyden said the practice gave the two companies unique insight into traffic flowing from those apps to users, putting them “in a unique position to facilitate government surveillance of how users are using particular apps.” Apple and Google both acknowledged receiving such requests. Apple added a passage to its guidelines saying such data was available “with a subpoena or greater legal process.” The passage has now been updated to refer to more stringent warrant requirements. Wyden said in a statement that Apple was “doing the right thing by matching Google and requiring a court order to hand over push notification related data.”
Note: Read more about the controversial geofence warrants that use Big Tech data. As an older article about the Apple court order articulates, law enforcement can "intercept your messages, access your health records or financial data, track your location, or even access your phone’s microphone or camera without your knowledge." For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
In the 1970s, congressional investigators revealed that the FBI, NSA, and CIA had spent decades illegally surveilling and harassing the civil rights and anti-war movements. These abuses shocked the American public and led Congress to implement a series of intelligence reforms, including the Foreign Intelligence Surveillance Act (FISA), which set strict limitations on when and how intelligence agencies could perform domestic spying. In the decades since the 9/11 attacks, changing laws and aggressive executive branch lawyering have significantly relaxed the rules that govern surveillance of Americans. We are once again seeing abuses of these powers, including instances of intelligence agents seeking access to the communications of politicians, protesters, and journalists. Today, a bipartisan group of lawmakers ... introduced the Government Surveillance Reform Act of 2023 (GSRA) to reverse this erosion of privacy rights. The GSRA begins by tackling Section 702, a controversial surveillance law that expires at the end of this year. Section 702 allows the government to collect the communications of non-Americans located abroad without a warrant. But Americans’ private phone calls, emails, and text messages are inevitably captured, too — and intelligence officials frequently perform warrantless searches for them. Intelligence officials conducted more than 200,000 of these “backdoor searches” for Americans’ communications last year alone.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
New Yorkers may have noticed an unwelcome guest hovering round their parties. In the lead-up to Labour Day weekend the New York Police Department (NYPD) said that it would use drones to look into complaints about festivities, including back-yard gatherings. Snooping police drones are an increasingly common sight in America. According to a recent survey by researchers at the Northwestern Pritzker School of Law, about a quarter of police forces now use them. Among the NYPD’s suppliers is Skydio, a Silicon Valley firm that uses artificial intelligence (AI) to make drones easy to fly. The NYPD is also buying from BRINC, another startup, which makes flying machines equipped with night-vision cameras that can smash through windows. Facial-recognition software is now used more widely across America, too, with around a tenth of police forces having access to the technology. A report released in September by America’s Government Accountability Office found that six federal law-enforcement agencies, including the FBI and the Secret Service, were together executing an average of 69 facial-recognition searches every day. Among the top vendors listed was Clearview AI. Surveillance capabilities may soon be further fortified by generative AI, of the type that powers ChatGPT, thanks to its ability to work with “unstructured” data such as images and video footage. The technology will let users “search the Earth for objects”, much as Google lets users search the internet.
Note: For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
The FBI has amassed 21.7 million DNA profiles — equivalent to about 7 percent of the U.S. population — according to Bureau data reviewed by The Intercept. The FBI aims to nearly double its current $56.7 million budget for dealing with its DNA catalog with an additional $53.1 million, according to its budget request for fiscal year 2024. “The requested resources will allow the FBI to process the rapidly increasing number of DNA samples collected by the U.S. Department of Homeland Security,” the appeal for an increase says. “When we’re talking about rapid expansion like this, it’s getting us ever closer to a universal DNA database,” Vera Eidelman, a staff attorney at the American Civil Liberties Union, [said]. “I think the civil liberties implications here are significant.” The rapid growth of the FBI’s sample load is in large part thanks to a Trump-era rule change that mandated the collection of DNA from migrants who were arrested or detained by immigration authorities. Until recently, the U.S. DNA database surpassed even that of authoritarian China, which launched an ambitious DNA collection program in 2017. That year, the BBC reported, the U.S. had about 4 percent of its population’s DNA, while China had about 3 percent. While DNA has played an important role in prosecuting crimes, less than 3 percent of the profiles have assisted in cases, the Bureau’s data reveals. By comparison, fingerprints collected by the FBI from current and former federal employees linked them to crimes at a rate of 12 percent each year.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
If you call 911 to report an emergency, the odds are increasing that a drone will be the first unit sent to respond. More than 1,500 departments across the country now use them, “mostly for search and rescue as well as to document crime scenes and chase suspects,” according to ... MIT Technology Review. Generally, police drones don’t carry weapons and are used primarily for video surveillance. It is possible for small drones to deliver chemical irritants like tear gas, however, a technology that police in Israel have used against Palestinians. In a report published on Thursday, American Civil Liberties Union Senior Policy Analyst Jay Stanley worries that these kinds of drone programs may normalize usage and “usher in an era of pervasive, suspicionless, mass aerial surveillance.” He notes far more invasive turns that police drone usage could take, including warrantless surveillance of specific people, crime “hotspots” or even whole neighborhoods or cities. Stanley wonders if drone usage won’t just ... “amplify the problems with the deeply broken U.S. criminal legal system.” Many of the cities using drones in policing are doing so from so-called “real-time crime centers.” These units function as centralized hubs to connect the various bits of surveillance and data that police collect from things like stationary cameras, drones, license plate readers and technology that listens for possible gunshots. Some centers can even integrate police body cameras and video from Ring doorbells.
Note: Police have been using military predator drones for domestic law enforcement since 2011. For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
An industrial estate in Yorkshire is an unlikely location for ... an artificial intelligence (AI) company used by the Government to monitor people’s posts on social media. Logically has been paid more than £1.2 million of taxpayers’ money to analyse what the Government terms “disinformation” – false information deliberately seeded online – and “misinformation”, which is false information that has been spread inadvertently. It does this by “ingesting” material from more than hundreds of thousands of media sources and “all public posts on major social media platforms”, using AI to identify those that are potentially problematic. It has a £1.2 million deal with the Department for Culture, Media and Sport (DCMS), as well as another worth up to £1.4 million with the Department of Health and Social Care to monitor threats to high-profile individuals within the vaccine service. It also has a “partnership” with Facebook, which appears to grant Logically’s fact-checkers huge influence over the content other people see. A joint press release issued in July 2021 suggests that Facebook will limit the reach of certain posts if Logically says they are untrue. “When Logically rates a piece of content as false, Facebook will significantly reduce its distribution so that fewer people see it, apply a warning label to let people know that the content has been rated false, and notify people who try to share it,” states the press release.
Note: Read more about how NewsGuard, a for-profit company, works closely with government agencies and major corporate advertisers to suppress dissenting views online. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and media manipulation from reliable sources.
An AI-based decoder that can translate brain activity into a continuous stream of text has been developed, in a breakthrough that allows a person’s thoughts to be read non-invasively for the first time. The decoder could reconstruct speech with uncanny accuracy while people listened to a story – or even silently imagined one – using only fMRI scan data. Previous language decoding systems have required surgical implants. Large language models – the kind of AI underpinning OpenAI’s ChatGPT ... are able to represent, in numbers, the semantic meaning of speech, allowing the scientists to look at which patterns of neuronal activity corresponded to strings of words with a particular meaning rather than attempting to read out activity word by word. The decoder was personalised and when the model was tested on another person the readout was unintelligible. It was also possible for participants on whom the decoder had been trained to thwart the system, for example by thinking of animals or quietly imagining another story. Jerry Tang, a doctoral student at the University of Texas at Austin and a co-author, said: “We take very seriously the concerns that it could be used for bad purposes and have worked to avoid that. We want to make sure people only use these types of technologies when they want to and that it helps them.” Prof Tim Behrens, a computational neuroscientist ... said it opened up a host of experimental possibilities, including reading thoughts from someone dreaming.
Note: This technology has advanced considerably since Jose Delgado first stopped a charging bull using radio waves in 1965. For more along these lines, see concise summaries of deeply revealing news articles on mind control and the disappearance of privacy from reliable major media sources.
The United States Federal Bureau of Investigation has acknowledged for the first time that it purchased US location data rather than obtaining a warrant. The disclosure came today during a US Senate hearing. Senator Ron Wyden ... put the question of the bureau’s use of commercial data to its director, Christopher Wray: “Does the FBI purchase US phone-geolocation information?” Wray said his agency was not currently doing so. “To my knowledge, we do not currently purchase commercial database information that includes location data derived from internet advertising,” Wray said. “I understand that we previously—as in the past—purchased some such information for a specific national security pilot project. But that’s not been active for some time.” In its landmark Carpenter v. United States decision, the Supreme Court held that government agencies accessing historical location data without a warrant were violating the Fourth Amendment’s guarantee against unreasonable searches. The decision left open a glaring loophole that allows the government to simply purchase whatever it cannot otherwise legally obtain. US Customs and Border Protection (CBP) and the Defense Intelligence Agency are among the list of federal agencies known to have taken advantage of this loophole. The Department of Homeland Security ... purchased the geolocations of millions of Americans from private marketing firms. The data were derived from ... benign sources, such as mobile games and weather apps.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
A study published Monday ... outlines how expansive the market for people’s health data has become. After contacting data brokers to ask what kinds of mental health information she could buy, researcher Joanne Kim reported that she ultimately found 11 companies willing to sell bundles of data that included information on what antidepressants people were taking, whether they struggled with insomnia or attention issues, and details on other medical ailments, including Alzheimer’s disease or bladder-control difficulties. Some of the data was offered in an aggregate form that would have allowed a buyer to know, for instance, a rough estimate of how many people in an individual Zip code might be depressed. But other brokers offered personally identifiable data featuring names, addresses and incomes, with one data-broker sales representative pointing to lists named “Anxiety Sufferers” and “Consumers With Clinical Depression in the United States.” Some even offered a sample spreadsheet. The Health Insurance Portability and Accountability Act, known as HIPAA, restricts how hospitals, doctors’ offices and other “covered health entities” share Americans’ health data. But the law doesn’t protect the same information when it’s sent anywhere else, allowing app makers and other companies to legally share or sell the data. Some of the data brokers offered ... opt-out forms. But ... many people probably didn’t realize the brokers had collected their information in the first place. Privacy advocates have for years warned about the unregulated data trade, saying the information could be exploited by advertisers or misused for predatory means. The health-data issue has in some ways gotten worse, in large part because of the increasing sophistication with which companies can collect and share people’s personal information — including not just in defined lists, but through regularly updated search tools and machine-learning analyses.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The outbreak of Covid-19 has been anathema for most of Chinas economy but the novel coronavirus was a shot in the arm for the states surveillance apparatus, which has expanded rapidly in pursuit of the epidemics spread. Facial recognition cameras, phone tracking technology and voluntary registrations have all been deployed to monitor the flow of people and the possible transmission of disease. The Chinese surveillance systems currently ... has two purposes: the first is to monitor public health and the second is to maintain political control, says Francis Lee, a professor ... at the Chinese University of Hong Kong. Once the outbreak is controlled, however, its unclear whether the government will retract its new powers. While facial recognition provides a way to monitor crowds from a distance, governments have deployed close-range means of tracking individuals too. The municipal government of Hangzhou worked with ecommerce giant Alibaba to launch a feature through the companys mobile wallet app, AliPay, that assesses the users risk of infection. The app generates a QR code. Guards at checkpoints in residential buildings and elsewhere can then scan that code to gain details about the user. John Bacon-Shone ... at Hong Kong University thinks that the ongoing threat of outbreaks will provide a constant justification for the new systems. I am rather pessimistic that there will be full rollback of data collection once it has been implemented, Bacon-Shone says.
Note: Remember all of the privacy and freedoms given up after 9/11? How many of those have been given back? Learn more about the serious risk of the Coronavirus increasing the surveillance state in this excellent article. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Federal investigators have ordered Google to provide information on all viewers of select YouTube videos. In a just-unsealed case from Kentucky ... undercover cops sought to identify the individual behind the online moniker “elonmuskwhm,” who they suspect of buying bitcoin for cash. In conversations with the user in early January, undercover agents sent links of YouTube tutorials for mapping via drones and augmented reality software, then asked Google for information on who had viewed the videos, which collectively have been watched over 30,000 times. The court orders show the government telling Google to provide the names, addresses, telephone numbers and user activity for all Google account users who accessed the YouTube videos between January 1 and January 8, 2023. The government also wanted the IP addresses of non-Google account owners who viewed the videos. The cops argued, “There is reason to believe that these records would be relevant and material to an ongoing criminal investigation, including by providing identification information about the perpetrators.” The court granted the order and Google was told to keep the request secret. Privacy experts said the orders were unconstitutional because they threatened to undo protections in the 1st and 4th Amendments covering free speech and freedom from unreasonable searches. Albert Fox-Cahn, executive director at the Surveillance Technology Oversight Project [says that] “no one should fear a knock at the door from police simply because of what the YouTube algorithm serves up. I’m horrified that the courts are allowing this.”
Note: The article refers to federal investigators and to undercover cops, but it doesn't specify who was actually doing the investigating. What agency or agencies were involved in these secret operations? For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
As war in Ukraine continues, controversial defense contractors and adjacent companies like Palantir, Anduril, and Clearview AI are taking advantage to develop and level-up controversial AI-driven weapons systems and surveillance technologies. These organizations’ common link? The support of the controversial, yet ever-more powerful Silicon Valley billionaire Peter Thiel. Thiel-backed groups’ involvement in war serves to develop not only problematic and unpredictable weapons technologies and systems, but also apparently to advance and further interconnect a larger surveillance apparatus formed by Thiel and his elite allies’ collective efforts across the public and private sectors, which arguably amount to the entrenchment of a growing technocratic panopticon aimed at capturing public and private life. What’s more, Thiel’s funding efforts signal interest in developing expansive surveillance technologies, especially in the name of combatting “pre-crime” through “predictive policing” style surveillance. As an example, Thiel’s provided significant funds to Israeli intelligence-linked startup Carbyne911 (as did Jeffrey Epstein), which develops call-handling and call-identification capacities for emergency services, and has ... a predictive-policing component. Thiel also assisted in the development and subsequent privatized spinoffs of the US Government’s Defense Advanced Research Projects Agency’s (DARPA) Total Information Awareness project.
Note: Peter Thiel was also recently reported to be an FBI informant. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The U.S. Army Cyber Command told defense contractors it planned to surveil global social media use to defend the "NATO brand," according to a 2022 webinar recording reviewed by The Intercept. "NATO is one of our key brands that we are pushing, as far as our national security alliance," [Lt. Col. David Beskow] explained. The mass social media surveillance appears to be just one component of a broader initiative to use private-sector data mining to advance the Army's information warfare efforts. Beskow expressed an interest in purchasing access to nonpublic commercial web data, corporate ownership records, supply chain data, and more. While the U.S. national security establishment frequently warns against other countries' "weaponization" of social media and the broader internet, recent reporting has shown the Pentagon engages in some of the very same conduct. Researchers from Graphika and the Stanford Internet Observatory uncovered a network of pro-U.S. Twitter and Facebook accounts covertly operated by U.S. Central Command, an embarrassing revelation that led to a “sweeping audit of how it conducts clandestine information warfare." Despite years of alarm in Washington over the threat posed by deepfake video fabrications to democratic societies, The Intercept reported last month that U.S. Special Operations Command is seeking vendors to help them make their own deepfakes to deceive foreign internet users.
Note: For more along these lines, see concise summaries of deeply revealing news articles on military corruption and media manipulation from reliable sources.
The FBI and the Defense Department were actively involved in research and development of facial recognition software that they hoped could be used to identify people from video footage captured by street cameras and flying drones, according to thousands of pages of internal documents that provide new details about the government's ambitions to build out a powerful tool for advanced surveillance. The documents, revealed in response to an ongoing Freedom of Information Act lawsuit the American Civil Liberties Union filed against the FBI, show how closely FBI and Defense officials worked with academic researchers to refine artificial-intelligence techniques that could help in the identification or tracking of Americans without their awareness or consent. Many of the records relate to the Janus program, a project funded by the Intelligence Advanced Research Projects Agency, or IARPA. The improved facial recognition system was ultimately folded into a search tool, called Horus, and made available to the Pentagon's Combating Terrorism Technical Support Office, which helps provide military technologies to civilian police forces. No federal laws regulate how facial recognition systems can be used. The tool's use in domestic mass surveillance would be a "nightmare scenario," said Nathan Wessler, a deputy director at the ACLU. "It could give the government the ability to pervasively track as many people as they want for as long as they want. There's no good outcome for that in a democratic society."
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Caleb Kenyon, a defense attorney in Florida, saw a geofence warrant was when a new client received an alarming email from Google in January 2020. Police were requesting personal data from the client, Zachary McCoy, and Kenyon had just seven days to stop Google from turning it over, the email said. The geofence warrant included a map and GPS coordinates, and instructed Google to provide identifying information for every user whose device was found within the radius of that location at a certain date and time. “It was so bizarre that I just didn’t even have a concept for what I was dealing with,” he said. Kenyon is not alone. As tech firms build ever more sophisticated means of surveilling people and their devices – technology that law enforcement is eager to take advantage of – the legal community is scrambling to keep up. The National Association of Criminal Defense Lawyers (NACDL) ... recently created the Fourth Amendment Center, named for the constitutional right against unreasonable searches. The center is one of the few resources available for helping attorneys better understand how new technology is being used against their clients. It can be years before the defense community catches wind of the newest surveillance tools. Unlike other search warrants, geofence warrants don’t require probable cause or a specific suspect in mind; they gather information on anyone within the vicinity of an alleged crime. Advocates argue this violates the fourth amendment.
Note: For more along these lines, see concise summaries of deeply revealing news articles on court system corruption and the disappearance of privacy from reliable major media sources.
Under a post-9/11 surveillance program known as “Upstream”, the NSA is systematically searching Americans’ internet communications as they enter and leave the United States. The agency sifts through these streams of data looking for “identifiers” associated with its many thousands of foreign targets – identifiers like email addresses and phone numbers. The NSA does all of this without warrants, without any individual judicial approval, and without showing that any of the people it is surveilling – including countless Americans – have done anything wrong. This surveillance raises serious constitutional concerns, but no court has ever considered a legal challenge to it because the government has claimed that allowing a suit against Upstream surveillance to go forward would implicate “state secrets”. In 2007, for example, an appeals court dismissed a lawsuit filed by Khaled El-Masri claiming that, in a case of mistaken identity, he had been kidnapped and tortured by the CIA. The court acknowledged the public evidence of El-Masri’s mistreatment but held that state secrets were too central to the case to allow it to go forward. And in 2010, a different appeals court dismissed a lawsuit filed by five individuals who claimed that one of Boeing’s subsidiary companies had flown the planes carrying them to the black sites where they were tortured by the CIA. This use of the state secrets privilege – to dismiss cases – departs from the supreme court’s narrow framing of the privilege.
Note: For more along these lines, see concise summaries of deeply revealing news articles on court system corruption and the disappearance of privacy from reliable major media sources.
The Central Intelligence Agency has for years been collecting in bulk, without a warrant, some kind of data that can affect Americans’ privacy. At the same time, [the C.I.A.] declared that a report about the same topic, which had prompted the letter, must remain fully classified. That report, called “Deep Dive II,” was part of a set of studies by a watchdog board scrutinizing intelligence community operations under Executive Order 12333. In March 2021, the Senate Intelligence Committee received a copy of the report. Two Democrats on the panel, Senators Ron Wyden of Oregon and Martin Heinrich of New Mexico, urged Avril D. Haines, the director of national intelligence, and William J. Burns, the C.I.A. director, to declassify the activity. The senators suggested that its hidden existence cut against Americans’ understanding that various pieces of legislation enacted in recent years “limit and, in some cases, prohibit the warrantless collection of Americans’ records.” In 2015, Congress banned bulk collection of telecommunications metadata under the Patriot Act and limited other types of bulk collection by the F.B.I. under laws governing domestic activities like the Foreign Intelligence Surveillance Act, or FISA. Yet “the C.I.A. has secretly conducted its own bulk program” under Executive Order 12333, the senators wrote. “It has done so entirely outside the statutory framework that Congress and the public believe govern this collection, and without any of the judicial, congressional or even executive branch oversight.”
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
MIT researchers have now developed a novel way to record a patient’s vaccination history: storing the data in a pattern of dye, invisible to the naked eye, that is delivered under the skin at the same time as the vaccine. The researchers showed that their new dye, which consists of nanocrystals called quantum dots, can remain for at least five years under the skin, where it emits near-infrared light that can be detected by a specially equipped smartphone. The researchers designed their dye to be delivered by a microneedle patch rather than a traditional syringe and needle. Such patches are now being developed to deliver vaccines for measles, rubella, and other diseases. “It’s possible someday that this ‘invisible’ approach could create new possibilities for data storage, biosensing, and vaccine applications that could improve how medical care is provided, particularly in the developing world,” [study co-author Robert] Langer says. Tests using human cadaver skin showed that the quantum-dot patterns could be detected by smartphone cameras after up to five years of simulated sun exposure. The research was funded by the Bill and Melinda Gates Foundation and the Koch Institute Support (core) Grant from the National Cancer Institute.
Note: Could these quantum dots be used for tracking and monitoring people? This revealing article shows patents by Moderna suggesting their use in human vaccines. For more along these lines, see concise summaries of deeply revealing news articles on vaccines and the disappearance of privacy from reliable major media sources.
Samsung is warning customers about discussing personal information in front of their smart television set. The warning applies to TV viewers who control their Samsung Smart TV using its voice activation feature. When the feature is active, such TV sets "listen" to what is said and may share what they hear with Samsung or third parties, it said. Privacy campaigners said the technology smacked of the telescreens, in George Orwell's 1984, which spied on citizens. The warning came to light via a story in ... the Daily Beast which published an excerpt of a section of Samsung's privacy policy for its net-connected Smart TV sets. These record what is said when a button on a remote control is pressed. The policy explains that the TV set will be listening to people in the same room to try to spot when commands or queries are issued via the remote. It goes on to say: "If your spoken words include personal or other sensitive information, that information will be among the data captured and transmitted to a third party." Corynne McSherry, an intellectual property lawyer for the Electronic Frontier Foundation, [said] that the third party was probably the company providing speech-to-text conversion for Samsung. She added: "If I were the customer, I might like to know who that third party was, and I'd definitely like to know whether my words were being transmitted in a secure form." The third party handling the translation from speech to text is a firm called Nuance, which specialises in voice recognition, Samsung has confirmed to the BBC.
Note: Read more about Samsung's privacy issues in this 2013 Houston Chronicle article. For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
The US National Security Agency (NSA) tried to persuade its British counterpart to stop the Guardian publishing revelations about secret mass data collection from the NSA contractor, Edward Snowden. Sir Iain Lobban, the head of Government Communications Headquarters (GCHQ) ... rebuffed the suggestion that his agency should act as a censor on behalf of its US partner in electronic spying. British refusal to shut down publication of the leaks ... caused rifts within the Five Eyes signals intelligence coalition [according to] a new book ... by Richard Kerbaj. Kerbaj reports that the US-UK intelligence relationship was further strained when the head of the NSA, Gen Keith Alexander, failed to inform Lobban that the Americans had identified Snowden ... leaving the British agency investigating its own ranks in the search for the leaker. The Five Eyes allies were outraged that a contractor like Snowden, working as a computer systems administrator, could get access to their secrets, and that because of US government outsourcing, there were 1.5 million Americans with top security clearance like Snowden. Allies were not prepared to challenge the Americans out of anxiety that they could be cut off from the flow of intelligence. British officials also decided to bite their tongues ... because of the value of the intelligence and funding provided by the NSA. Sir Kim Darroch, the former UK national security adviser, is quoted ... saying: “The US give us more than we give them so we just have to basically get on with it.”
Note: Read more on how US and UK spy agencies undermine privacy and security in this news article reported by The Guardian. For a guide from The Guardian on how to remain secure against NSA surveillance, click here.
The digital Covid vaccination certification, or “passport,” is a mobile app that instantaneously affirms the vaccinated status, Covid test results, birth date, gender, and/or other identifiers of its holder. The information is usually mosaicked in a QR code, read by a proprietary scanner, and linked to a government registry. Led by New York, California, and Louisiana, as many as 30 states are rolling them out. The Biden administration announced last spring that it would wrangle them under national standards but so far it hasn’t. Internationally, the EU and a growing number of countries are adopting them, from repressive regimes like Bahrain to democracies like Denmark. Twenty U.S. states have banned the passes, and hashtags like #NoVaccinePassports are proliferating. “Spoiler alert,” tweeted British DJ ... Lange. “They are not planning on removing vax passports once introduced. This is just the first step to get you conditioned to accepting government restrictions in your daily life via your mobile phone. This digital ID is going to expand to all aspects of your life.” New York, for one, is not expecting to mothball the technology when Covid wanes. State bureaucrats are “exploring how the platform could be retrofitted to verify other types of records and credentials.” The surveillance technologies of the War on Contagion are inherited from the War on Terror, and the software is encoded with the same forever-war mentality: Both fight risk rather than actual threat.
Note: For more along these lines, see concise summaries of deeply revealing news articles on coronavirus vaccines and the disappearance of privacy from reliable major media sources.
When the government tracks the location of a cellphone it achieves near perfect surveillance, as if it had attached an ankle monitor to the phones user, wrote John Roberts, the chief justice of the Supreme Court, in a 2018 ruling that prevented the government from obtaining location data from cellphone towers without a warrant. We decline to grant the state unrestricted access to a wireless carriers database of physical location information, Chief Justice Roberts wrote in the decision, Carpenter v. United States. With that judicial intent in mind, it is alarming to read a new report in The Wall Street Journal that found the Trump administration has bought access to a commercial database that maps the movements of millions of cellphones in America and is using it for immigration and border enforcement. The data used by the government comes not from the phone companies but from a location data company, one of many that are quietly and relentlessly collecting the precise movements of all smartphone-owning Americans through their phone apps. Many apps weather apps or coupon apps, for instance gather and record location data without users understanding what the code is up to. That data can then be sold to third party buyers including, apparently, the government. The courts are [an] imperfect venue for protecting Fourth Amendment rights. The Carpenter ruling applies only to location data captured by cellphone towers and not to location data streamed from smartphone apps.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Hardware that breaks into your phone; software that monitors you on the internet; systems that can recognize your face and track your car: The New York State Police are drowning in surveillance tech. Last year alone, the Troopers signed at least $15 million in contracts for powerful new surveillance tools. Surveillance technology has far outpaced traditional privacy laws. In New York, lawmakers launched a years-in-the-making legislative campaign last year to rein in police intrusion. None of their bills have made it out of committee. A report from the U.S. Office of the Director of National Intelligence, put it succinctly: “The government would never have been permitted to compel billions of people to carry location tracking devices on their persons at all times, to log and track most of their social interactions, or to keep flawless records of all their reading habits.” That report called specific attention to the “data broker loophole”: law enforcement’s practice of obtaining data for which they’d otherwise have to obtain a warrant by buying it from brokers. The New York State Police have taken greater and greater advantage of the loophole in recent years. They’ve also spent millions on mobile device forensic tools, or MDFTs, powerful hacking hardware and software that allow users to download full, searchable copies of a cellphone’s data, including social media messages, emails, web and search histories, and minute-by-minute location information.
Note: For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
The FBI spends "every day, all day long" interrogating people over their Facebook posts. At least, that's what agents told Stillwater, Oklahoma, resident Rolla Abdeljawad when they showed up at her house to ask her about her social media activity. Three FBI agents came to Abdeljawad's house and said that they had been given "screenshots" of her posts by Facebook. Her lawyer Hassan Shibly posted a video of the incident. "Facebook gave us a couple of screenshots of your account," one agent in a gray shirt said in the video. "So we no longer live in a free country and we can't say what we want?" replied Abdeljawad. "No, we totally do. That's why we're not here to arrest you or anything," a second agent in a red shirt added. "We do this every day, all day long. It's just an effort to keep everybody safe and make sure nobody has any ill will." Shibly says that he doesn't know which Facebook post caught the agents' attention, and that it was the first time he had heard of Facebook's parent company, Meta, preemptively reporting posts to law enforcement. [Abdeljawad] made multiple angry posts per day about the war in Gaza, referring to Israel as "Israhell." But none of the posts on her feed call for violence. Ironically, Abdeljawad had also posted a warning about exactly the kind of government monitoring she was later subjected to. "Don't fall for their games. Our community is being watched & they are just waiting for any reason to round us up," Abdeljawad wrote.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the erosion of civil liberties from reliable major media sources.
In November 2020 ... a ballot initiative known as Measure J passed with 57 percent support, amending the LA County charter so that jailing people before trial would be treated as a last resort. In June, LA County signed over the handling of changes to pretrial detention under Measure J to the consulting firm Accenture, a behemoth in the world of biometric databases and predictive policing. Accenture has pushed counterterror and policing strategies around the globe: The company built the world’s biggest biometric identification system in India, which has used similar technologies to surveil protesters and conduct crowd control as part of efforts by Prime Minister Narendra Modi’s Bharatiya Janata Party to investigate the citizenship of Muslim residents. Accenture ballooned into a giant in federal consulting over the course of the “war on terror,” winning hundreds of millions of dollars in lucrative contracts from federal agencies like the Department of Homeland Security for projects from a “virtual border” to recruiting and hiring Customs and Border Protection and Border Patrol agents. In 2006, Accenture won a $10 million contract for a DHS biometric ID program, the world’s second biggest, to collect and share biometric data on foreign nationals entering or leaving the U.S. Several LA-based advocates told The Intercept that the contract is yet another development that calls into question the county’s commitment to real criminal justice reform.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The Department of Homeland Security (DHS) is likely the single largest collector and consumer in the U.S. government of detailed, often intimate, information about Americans and foreigners alike. The department stores and analyzes this information using vast data systems to determine who can enter the country and who is subjected to intrusive inspections, including by parsing through travel records, social media data, non-immigrant visa applications, and other information to detect patterns of behavior that the department has determined are worthy of scrutiny. As we explain in a new Brennan Center report, these systems ... are too often deployed in discriminatory ways that violate Americans’ constitutional rights and civil liberties. It is past time for DHS to stop improvising how it designs and implements its automated systems, with inadequate mechanisms for evaluation and oversight, weak standards, and disproportionate impacts on marginalized communities and individuals. DHS must disclose additional information about its systems, including the policies that govern their operations and reports explaining how they are used. An independent body should undertake a rigorous investigation of DHS’s automated systems, evaluating whether they are useful and accurate, assessing how they function, and determining whether they contain sufficient safeguards to protect privacy, civil rights, and civil liberties.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Public schools ... are the focus of a new report on surveillance and kids by the American Civil Liberties Union (ACLU). "Over the last two decades, a segment of the educational technology (EdTech) sector that markets student surveillance products to schools — the EdTech Surveillance industry — has grown into a $3.1 billion a year economic juggernaut," begins Digital Dystopia The Danger in Buying What the EdTech Surveillance Industry is Selling. "The EdTech Surveillance industry accomplished that feat by playing on school districts' fears of school shootings, student self-harm and suicides, and bullying — marketing them as common, ever-present threats." As the authors detail, among the technologies are surveillance cameras. These are often linked to software for facial recognition, access control, behavior analysis, and weapon detection. That is, cameras scan student faces and then algorithms identify them, allow or deny them entry based on that ID, decide if their activities are threatening, and determine if objects they carry may be dangerous or forbidden. "False hits, such as mistaking a broomstick, three-ring binder, or a Google Chromebook laptop for a gun or other type of weapon, could result in an armed police response to a school," cautions the report. Students are aware that they're being observed. Of students aged 14–18 surveyed by the ACLU ... thirty-two percent say, "I always feel like I'm being watched."
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
An effort by United States lawmakers to prevent government agencies from domestically tracking citizens without a search warrant is facing opposition internally from one of its largest intelligence services. Officials at the National Security Agency (NSA) have approached lawmakers charged with its oversight about opposing an amendment that would prevent it from paying companies for location data instead of obtaining a warrant in court. Introduced by US representatives Warren Davidson and Sara Jacobs, the amendment ... would prohibit US military agencies from "purchasing data that would otherwise require a warrant, court order, or subpoena" to obtain. The ban would cover more than half of the US intelligence community, including the NSA, the Defense Intelligence Agency, and the newly formed National Space Intelligence Center, among others. A government report declassified by the Office of the Director of National Intelligence last month revealed that US intelligence agencies were avoiding judicial review by purchasing a "large amount" of "sensitive and intimate information" about Americans, including data that can be used to trace people's whereabouts over extended periods of time. The sensitivity of the data is such that "in the wrong hands," the report says, it could be used to "facilitate blackmail," among other undesirable outcomes. The report also acknowledges that some of the data being procured is protected under the US Constitution's Fourth Amendment.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
These blank-looking warehouses are home to an artificial intelligence (AI) company used by the Government to monitor people’s posts on social media. Logically has been paid more than £1.2 million of taxpayers’ money to analyse what the Government terms “disinformation” – false information deliberately seeded online – and “misinformation”, which is false information that has been spread inadvertently. It does this by “ingesting” material from more than hundreds of thousands of media sources and “all public posts on major social media platforms”, using AI to identify those that are potentially problematic. It has a £1.2 million deal with the Department for Culture, Media and Sport (DCMS), as well as another worth up to £1.4 million with the Department of Health and Social Care to monitor threats to high-profile individuals within the vaccine service. Other blue-chip clients include US federal agencies, the Indian electoral commission, and TikTok. It also has a “partnership” with Facebook, which appears to grant Logically’s fact-checkers huge influence over the content other people see. A joint press release issued in July 2021 suggests that Facebook will limit the reach of certain posts if Logically says they are untrue. “When Logically rates a piece of content as false, Facebook will significantly reduce its distribution so that fewer people see it, apply a warning label to let people know that the content has been rated false, and notify people who try to share it,” states the press release.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
The Pentagon’s intelligence branch is developing new tech to help it track the mass movement of people around the globe and flag “anomalies.” The project is called the Hidden Activity Signal and Trajectory Anomaly Characterization (HAYSTAC) program and it “aims to establish ‘normal’ movement models across times, locations, and populations and determine what makes an activity atypical,” according to a press release from the Office of the Director of National Intelligence (DNI). HAYSTAC will be run by the DNI’s Intelligence Advanced Research Projects Activity (IARPA). It’s kind of like DARPA, the Pentagon’s blue-sky research department, but with a focus on intelligence projects. According to the agency, the project will analyze data from internet-connected devices and “smart city” sensors using AI. “An ever-increasing amount of geospatial data is created every day,” Jack Cooper, HAYSTAC’s program manager, said. Cooper also mentioned privacy, or rather a lack of it. “Today you might think that privacy means going to live off the grid in the middle of nowhere,” he said. “That’s just not realistic in today’s environment. Sensors are cheap. Everybodys got one. There’s no such thing as living off the grid.” In one project, [contractor] AIS simulated a cyber attack. “Devices included traditional desktop systems, laptops, tablets, and mobile platforms,” the firm said. “The technology tracks users through biometric features, including keystroke biometrics, mouse movement behavior, and gait detection.”
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
New details about the FBI’s failures to comply with restrictions on the use of foreign intelligence for domestic crimes have emerged. Section 702 of the Foreign Intelligence Surveillance Act (FISA) ... grants the government the ability to intercept the electronic communications of overseas targets who are unprotected by the Fourth Amendment. That authority is set to expire at the end of the year. But errors in the FBI’s secondary use of the data—the investigation of crimes on US soil—are likely to inflame an already fierce debate over whether law enforcement agents can be trusted with such an invasive tool. Central to this tension has been a routine audit by the Department of Justice’s (DOJ) national security division and the office of the director of national intelligence (ODNI) ... which unearthed new examples of the FBI failing to comply with rules limiting access to intelligence ostensibly gathered to protect US national security. Such “errors,” they said, have occurred on a “large number” of occasions. A report on the audit, only recently declassified, found that in the first half of 2020, FBI personnel unlawfully searched raw FISA data on numerous occasions. In one incident, agents reportedly sought evidence of foreign influence linked to a US lawmaker. In another, an inappropriate search pertained to a local political party. In what privacy and civil liberties lawyers have termed a “backdoor search,” the FBI regularly searches through unminimized data during investigations, and routinely prior to launching them.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Since Buzzfeed reported in June that employees of TikTok’s Chinese parent company ByteDance had access to US consumer data, TikTok has been the focus of rare bipartisan calls for regulation and inquiry. Those inquiries became more pressing when in July, the FBI director, Christopher Wray, called Chinese espionage the “greatest long-term threat to our nation’s ... economic vitality”. TikTok is a relatively new player in the arena of massive global social media platforms but it’s already caught the eye of regulators in Europe. New laws around child safety and general internet safety in the UK and the EU have forced the company to become more transparent about the way it operates and the way content spreads on its platform. In the US, moves to rein in the video platform have gained momentum only relatively recently, although there’s little debate that the round of regulatory pressure is warranted. With 1 billion users, the platform, which uses an algorithmic feed to push users short-form videos, has had its fair share of run-ins with misinformation, data privacy and concerns about child safety. Experts the Guardian spoke with did not question the cybersecurity threat China posed. However, some said they worried regulators’ hyper-focus on TikTok’s China connection could distract from other pressing concerns, including TikTok’s algorithm and how much user data the company collects, stores and shares. There are currently no federal regulations that protect such information.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The web browser used within the TikTok app can track every keystroke made by its users, according to new research that is surfacing as the Chinese-owned video app grapples with U.S. lawmakers’ concerns over its data practices. The research from Felix Krause, a privacy researcher and former Google engineer, did not show how TikTok used the capability, which is embedded within the in-app browser that pops up when someone clicks an outside link. But Mr. Krause said the development was concerning because it showed TikTok had built in functionality to track users’ online habits if it chose to do so. Collecting information on what people type on their phones while visiting outside websites, which can reveal credit card numbers and passwords, is often a feature of malware and other hacking tools. Apps sometimes use in-app browsers to prevent people from visiting malicious sites or to make online browsing easier with the auto-filling of text. But while Facebook and Instagram can use in-app browsers to track data like what sites a person visited ... TikTok goes further by using code that can track each character entered by users. As with many apps, TikTok offers few chances for people to click away from its service. Instead of redirecting to mobile web browsers like Safari or Chrome, an in-app browser appears when users click on ads or links embedded within the profiles of other users. These are often the moments people enter key information like credit card details or passwords.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
NSO Group [is] the world’s most notorious maker of spyware. The F.B.I. had bought a version of Pegasus, NSO’s premier spying tool. It could ... crack the encrypted communications of any iPhone or Android smartphone. Since NSO had introduced Pegasus to the global market in 2011, it had helped Mexican authorities capture Joaquín Guzmán Loera, the drug lord known as El Chapo. European investigators have quietly used Pegasus to thwart terrorist plots, fight organized crime and, in one case, take down a global child-abuse ring. Mexico deployed the software not just against gangsters but also against journalists and political dissidents. The United Arab Emirates used the software to hack the phone of a civil rights activist. Saudi Arabia used it against women’s rights activists. During a presentation to officials in Washington, the company demonstrated a new system, called Phantom, that could hack any number in the United States that the F.B.I. decided to target. A slick brochure ... says that Phantom allows American law enforcement and spy agencies to get intelligence “by extracting and monitoring crucial data from mobile devices.” It is an “independent solution” that requires no cooperation from AT&T, Verizon, Apple or Google. The system, it says, will “turn your target’s smartphone into an intelligence gold mine.” The Phantom presentation triggered a discussion among government lawyers. Last summer ... the F.B.I. finally decided not to deploy the NSO weapons.
Note: Read more about how NSO Group spyware was used against journalists and activists by the Mexican government. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Bloomberg Businessweek published an alarming story: Operatives working for China’s People’s Liberation Army had secretly implanted microchips into motherboards made in China and sold by U.S.-based Supermicro. This allegedly gave Chinese spies clandestine access to servers belonging to over 30 American companies, including Apple, Amazon, and various government suppliers, in an operation known as a “supply chain attack,” in which malicious hardware or software is inserted into products before they are shipped to surveillance targets. U.S. spy agencies ... assessed that China was adept at corrupting the software bundled closest to a computer’s hardware at the factory, threatening some of the U.S. government’s most sensitive machines, according to documents provided by National Security Agency whistleblower Edward Snowden. The documents also detail how the U.S. and its allies have themselves systematically targeted and subverted tech supply chains, with the NSA conducting its own such operations, including in China, in partnership with the CIA and other intelligence agencies. The documents also disclose supply chain operations by German and French intelligence. Computer hardware can be altered at various points along the supply chain, from design to manufacturing to storage to shipment. The U.S. is among the small number of countries that could, in theory, compromise devices at many different points in this pipeline, thanks to its resources and geographic reach.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
A review of hundreds of Facebooks patent applications reveals that the company has considered tracking almost every aspect of its users lives: where you are, who you spend time with, whether youre in a romantic relationship, which brands and politicians youre talking about. The company has even attempted to patent a method for predicting when your friends will die. Taken together, Facebooks patents show a commitment to collecting personal information, despite widespread public criticism of the companys privacy policies and a promise from its chief executive to do better. A patent portfolio is a map of how a company thinks about where its technology is going, said Jason M. Schultz, a law professor at New York University. One patent application discusses predicting whether youre in a romantic relationship using information such as how many times you visit another users page [and] the number of people in your profile picture. Another proposes using your posts and messages to infer personality traits ... then using those characteristics to select which news stories or ads to display. Another patent application discusses tracking your weekly routine and sending notifications to other users of deviations from the routine. In addition, it describes using your phones location in the middle of the night to establish where you live. As long as Facebook keeps collecting personal information, we should be wary.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
Last year an American company microchipped dozens of its workers. Of the 90 people who work at [Three Square Market] headquarters, 72 are now chipped. Two months ago, the company ... started chipping people with dementia. If someone wanders off and gets lost, police can scan the chip and they will know all their medical information, what drugs they can and cant have, theyll know their identity. So far, Three Square Market has chipped 100 people, but plans to do 10,000. The company has just launched a mobile phone app that pairs the chip with the phones GPS, enabling the implantees location to be tracked. Last week, it started using it with people released from prison on probation. Some Chinese companies are using sensors in helmets and hats to scan workers brainwaves. There are tech companies selling products that can ... monitor keystrokes and web usage, and even photograph [employees] using their computers webcams. All this can be done remotely. Monitoring is built into many of the jobs that form the so-called gig economy. Its not easy to object to the constant surveillance when youre desperate for work. What has surprised [Cass Business School professor Andr Spicer] is how willingly people in better-paid jobs have taken to it. Spicer has watched the shift away from monitoring something like emails to monitoring peoples bodies the rise of bio-tracking basically. The monitoring of your vital signs, emotions, moods.
Note: Author James Bloodworth describes the high tech monitoring of workers at Amazon warehouses in his new book, "Hired: Six Months Undercover in Low-Wage Britain". For more along these lines, see concise summaries of deeply revealing news articles on microchip implants and the disappearance of privacy.
Chinese companies are picking their employees brains - literally - with mind-reading devices designed to improve efficiency and performance. Workers are being outfitted with safety helmet-like caps that monitor brain waves and send the information to computers that use artificial intelligence algorithms to detect emotional spikes, like depression, anxiety and rage. The Orwellian technology has been used on factory employees, train conductors and workers at State Grid Zhejian Electric Power. State Grid, which has 40,000 employees ... said the companys profits have increased by about $315 million since it implemented the surveillance caps in 2014. The government-funded brain-monitoring project, called Neuro Cap, has been implemented in more than a dozen factories and businesses. Jin Jia, an associate professor of brain science and cognitive psychology at Ningbo University, which is hosting the project, said the brain caps allow workers to be better managed. Qiao Zhian, professor of management psychology at Beijing Normal University, said the devices could give companies a competitive boost - but warned they could also violate privacy in the worst way. There is no law or regulation to limit the use of this kind of equipment in China. The employer may have a strong incentive to use the technology for higher profit, and the employees are usually in too weak a position to say no, he said. The selling of Facebook data is bad enough. Brain surveillance can take privacy abuse to a whole new level.
Note: While slightly less invasive than microchip implants, the use of devices like these by government and industry threatens to fully eliminate privacy.
At 24, [Christopher Wylie] came up with an idea that led to the foundation of a company called Cambridge Analytica, a data analytics firm that went on to claim a major role in the Leave campaign for Britains EU membership referendum, and later became a key figure in digital operations during Donald Trumps election campaign. In 2014, Steve Bannon ... was Wylies boss. And Robert Mercer, the secretive US hedge-fund billionaire and Republican donor, was Cambridge Analyticas investor. The idea they bought into was to bring big data and social media to an established military methodology information operations then turn it on the US electorate. By [2017], Steve Bannon had become Trumps chief strategist. Cambridge Analyticas parent company, SCL, had won contracts with the US State Department and was pitching to the Pentagon, and Wylie was genuinely freaked out. Its insane, he told me one night. The company has created psychological profiles of 230 million Americans. And now they want to work with the Pentagon? Its like Nixon on steroids. He ended up showing me a tranche of documents that laid out the secret workings behind Cambridge Analytica. Wylie ... came up with a plan to harvest the Facebook profiles of millions of people in the US, and to use their private and personal information to create sophisticated psychological and political profiles. And then target them with political ads designed to work on their particular psychological makeup.
Note: Billionaire Robert Mercer used this new new technology to build a corporate empire capable of swinging elections by using military propaganda strategies on civilian populations. The above article further details how mass media is being combined with Big Data to produce powerful new forms of mind control. Watch an astounding video revealing how Cambridge Analytica has successfully manipulated national elections around the world.
New smart energy meters that the Government wants to be installed in millions of homes will leave householders vulnerable to cyber attacks. The intelligence agency GCHQ ... raised concerns over the security of the meters, which could enable hackers to steal personal details and defraud consumers by tampering with their bills. The Government wants every home in the country to have a smart meter, but only 8 million out of 27 million households have so far signed up to the 11 billion scheme. Cyber security experts say that making the meters universal will make them more attractive to hackers because the potential returns are so much greater if they can hack every meter using the same software. In some foreign countries hackers have already attacked smart meter networks to defraud customers. Criminals are able to artificially inflate meter readings, making bills higher. They then try to intercept payments, and if they simply skim off the difference between the real reading and the false reading, energy companies will think the bill has been paid normally. Another potential problem is the meters being used as a Trojan horse to access other computers and gadgets around the home if the meters are able to talk to the other devices. That would potentially give hackers the ability to steal personal information that could be sold on to other criminals.
Note: This 2015 New York Times article calls 'smart' devices like these meters, "a train wreck in privacy and security." The networked computerization of everyday objects often means that these objects can spy on you, accelerating the disappearance of privacy in the name of convenience. Watch an excellent documentary uncovering the serious dangers of smart meters.
The National Security Agency has apparently been way ahead of Apple or Amazon. The agency has at its disposal voice recognition technology that it employs to identify terrorists, government spies, or anyone they choose with just a phone call, according to a report by The Intercept. By using recorded audio, the NSA is able to create a "voiceprint," or a map of qualities that mark a voice as singular, and identify the person speaking. According to a classified memo ... the agency has employed this technology since at least 2006, with the document referencing technology "that identifies people by the sound of their voices." In fact, the NSA used such technology during Operation Iraqi Freedom, when analysts were able to verify audio thought to be of Saddam Hussein speaking. It suggests that national security operatives had access to high-level voice technology long before Amazon, Apple and Google's solutions became cultural touchstones. A "voiceprint" is "a dynamic computer model of the individual's vocal characteristics," the publication explained, created by an algorithm analyzing features like pitch and mouth shape. Then, using the NSA's formidable bank of recorded audio files, the agency is able to match the speaker to an identity. Identifying people through their voiceprints is a skill at which the "NSA reigns supreme," according to a leaked document from 2008. And, they're only getting better.
Note: As this BBC article from 1999 shows, mass surveillance systems with voice recognition capability have been in use for many years. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
Two New York Times reporters learned in 2004 that the George W. Bush administration was secretly wiretapping Americans, and collecting their phone and email records. The reporters attempt to publish their findings were thwarted by the administrations intense and successful lobbying of their editors. That effort ... had an unlikely ally: Rep. Jane Harman of Los Angeles, the senior Democrat on the House Intelligence Committee. Details of the far-reaching, legally unauthorized surveillance program remained secret until the Times published the article in late 2005. The newspapers interactions with administration officials, and Harmans role, were described by former Times reporter James Risen this month in the Intercept, the investigative publication where he now works. The story on the program known as Stellar Wind was ready for publication before the November 2004 election, when Bush was on the ballot, but NSA Director Michael Hayden and other administration officials told Times editors, in phone calls and face-to-face meetings, that publication would damage national security and endanger lives, Risen said. He said the officials were joined in that effort by Harman, one of a handful of congressional leaders who had been briefed on the program and were enlisted by the White House to contact the Times. Members of Congress learned later that the NSA had not been seeking warrants from a secret court, as required by law, before wiretapping calls.
Note: James Risen is a courageous hero who shared two Pulitzer Prizes for his reporting around 9/11 and massive government surveillance. His recent article in The Intercept describes how a "marketplace of secrets in Washington" supports the US national security apparatus, and is used by corrupt government officials to manipulate the news.
Forget swiping a credit card or badge to buy food at work. One Wisconsin-based tech firm is offering to install rice-size microchips in its employees' hands. Three Square Market will be the first firm in the U.S. to use the device, which was approved by the FDA in 2004, CEO Todd Westby told CNBC on Monday. "We think it's the right thing to do for advancing innovation just like the driverless car basically did in recent months," he said. The company, which provides technology for break-room markets or mini-market kiosks, is anticipating over 50 employees to be voluntarily chipped. Westby said he and his family will be chipped, too. The chip, which costs $300 per implant, is inserted with a needle between the thumb and forefinger. Once an employee has the chip installed, he or she can purchase food in the break room, open doors and log into computers. And for those who may be concerned about Big Brother watching, Westby said there is no way for employees to be tracked. "Unlike your cell phone that is trackable and traceable pretty much no matter where you are, this device is only readable if you're within six inches of a proximity reader," he said. Three Square Market's partner, BioHax International in Sweden, has already started using the microchips in about 150 of its employees.
Note: A Swedish company's chief executive was recently "chipped" live on stage to promote this dubious technology. And do you really think they are not trackable? Read about the agenda to chip all people in this powerful essay and these news articles.
Forty-five states and the District of Columbia are mounting a bipartisan rebellion against President Donald Trumps commission on vote fraud by either declining to release any of the requested data or by providing only limited information to the panel. The Presidential Advisory Commission on Voter Integrity's request for extensive personal information about voters has ignited a firestorm in many states, including from both Republican and Democrat officials who oversee elections. The panel is seeking "dates of birth, political party (if recorded in your state), last four digits of social security number if available, voter history (elections voted in) from 2006 onward, active/inactive status, cancelled status, information regarding any felony convictions, information regarding voter registration in another state, information regarding military status, and overseas citizen information." Nineteen states - both red and blue - and D.C. are flat-out refusing to comply with the request, citing privacy concerns and some claiming the 15-member vote fraud panel is politically-motivated. Many officials have expressed disbelief and outrage at the commission's call to hand over a staggering amount of voter data, some of which they say is confidential or sensitive. It is unclear how the commission plans to move forward after the backlash. The panel is slated to meet later this month.
Note: After several lawsuits, the voting panel is now telling states to hold off on sending data. For more along these lines, see concise summaries of deeply revealing elections corruption news articles from reliable major media sources. And don't miss the critically important information provided in our Elections Information Center.
Sensitive personal details relating to almost 200 million US citizens have been accidentally exposed by a marketing firm contracted by the Republican National Committee. The 1.1 terabytes of data includes birthdates, home addresses, telephone numbers and political views of nearly 62% of the entire US population. The data was available on a publicly accessible Amazon cloud server. Anyone could access the data. The information seems to have been collected from a wide range of sources - from posts on controversial banned threads on the social network Reddit, to committees that raised funds for the Republican Party. The information was stored in spreadsheets uploaded to a server owned by Deep Root Analytics. It had last been updated in January. Although it is known that political parties routinely gather data on voters, this is the largest breach of electoral data in the US to date and privacy experts are concerned about the sheer scale of the data gathered. "This is not just sensitive, it's intimate information, predictions about people's behaviour, opinions and beliefs that people have never decided to disclose to anyone," [said] Privacy International's policy officer Frederike Kaltheuner. However, the issue of data collection and using computer models to predict voter behaviour is not just limited to marketing firms - Privacy International says that the entire online advertising ecosystem operates in the same way.
Note: Elites like hedge fund billionaire Robert Mercer have been backing a major effort to produce powerful new forms of mind control by combining mass media with Big Data. As the data collected for this purpose becomes increasingly accessible, privacy disappears.
The C.I.A. developed tools to spy on Mac computers by injecting software into the chips that control the computers fundamental operations, according to the latest cache of classified government documents published on Thursday by WikiLeaks. All of the surveillance tools that have been disclosed were designed to be installed on individual phones or computers. But the effects could be much wider. Cisco Systems, for example, warned customers this week that many of its popular routers, the backbone of computer networks, could be hacked using the C.I.A.s techniques. Julian Assange, the founder of WikiLeaks, has offered to share the precise software code used by the C.I.A.s cyberweapons with the affected companies. But major tech companies have been reluctant to directly engage with him for fear of violating American laws. The spy software described in the latest documents was designed to be injected into a Macs firmware, a type of software preloaded in the computers chips. It would then act as a listening post, broadcasting the users activities to the C.I.A. whenever the machine was connected to the internet. Tools that operate at the chip level can hide their existence and avoid being wiped out by routine software updates. Under an agreement struck during the Obama administration, intelligence agencies were supposed to share their knowledge of most security vulnerabilities with tech companies. The C.I.A. documents suggest that some key vulnerabilities were kept secret.
Note: For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
In a heavily protected military base some 15 miles south of Washington, D.C., sits the massive headquarters of a spy agency few know exists. The [National Geospatial-Intelligence Agency, or] NGA remains by far the most shadowy member of the Big Five spy agencies, which include the CIA and the National Security Agency. Despite its lack of name recognition, the NGAs headquarters is the third-largest building in the Washington metropolitan area. The NGA is to pictures what the NSA is to voices. Its principal function is to analyze the billions of images and miles of video captured by drones ... and spy satellites. The agency has never been involved in domestic spy scandals. However, theres reason to believe that this will change. In March 2016, the Pentagon released the results of an investigation initiated by the Department of Defenses Office of Inspector General to examine military spy drones in the United States. The report ... revealed that the Pentagon used unarmed surveillance drones over American soil. The investigation also quoted from an Air Force law review article pointing out the growing concern that technology designed to spy on enemies abroad may soon be turned around to spy on citizens at home. In 2016, unbeknownst to many city officials, police in Baltimore began conducting persistent aerial surveillance using a system developed for military use in Iraq. Few civilians have any idea how advanced these military eye-in-the-sky drones have become.
Note: This article was written by former ABC News producer James Bamford, whose 2001 article on Operation Northwoods revealed that the top Pentagon generals signed off on top-secret plans which stated, "We could blow up a U.S. ship in Guantanamo Bay and blame Cuba," and, "casualty lists in U.S. newspapers would cause a helpful wave of national indignation." And showing the level of major media complicity, only ABC News reported on this. For more, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
British journalist Julia Breen's scoop about racism at her local police force didn't just get her on the front page, it got her put under surveillance. Investigators logged her calls, those of her colleague Graeme Hetherington and even their modest-sized newspaper's busy switchboard in an effort to unmask their sources. The [Northern Echo newspaper] has often provided painful reading for Cleveland Police, a department responsible for a Chicago-sized patch of England's industrial northeast. The small force has weathered a series of scandals. A minority officer, Sultan Alam, was awarded 800,000 pounds ... after allegedly being framed by colleagues in retaliation for a discrimination lawsuit. The judgment made national headlines. Cleveland Police issued a statement insisting the force wasn't racist. The next day, an anonymous caller told Breen an internal police report suggested otherwise. The following morning her byline was across the front page beneath the words: "Institutional racism uncovered within Cleveland Police." Breen ... eventually forgot the episode. Cleveland Police didn't. The force secretly began logging calls to and from Breen, Hetherington and a third journalist from another newspaper. It was later calculated that the surveillance covered over 1 million minutes of calling time. The Echo isn't unique. Britain's wiretapping watchdog ... revealed in 2015 that 82 journalists' communications records had been seized as part of leak investigations across the country over a three-year period.
Note: For more along these lines, see concise summaries of deeply revealing news articles about police corruption and the disappearance of privacy.
Over his two terms, Obama has created the most powerful surveillance state the world has ever seen. From 22,300 miles in space, where seven Advanced Orion [spy satellites] now orbit; to a 1-million-square-foot building in the Utah desert that stores data intercepted from personal phones, emails, and social media accounts; to taps along the millions of miles of undersea cables that encircle the Earth like yarn, U.S. surveillance has expanded exponentially since Obamas inauguration on Jan. 20, 2009. The effort to wire the world ... has cost American taxpayers more than $100 billion. Yet has the presidents blueprint for spying succeeded on its own terms? An examination of the unprecedented architecture reveals that the Obama administration may only have drowned itself in data. Privacy hasnt been traded for security, but for the government hoarding more data than it knows how to handle. A panel set up by Obama [in 2013] to review the NSAs operations concluded that the agency had stopped no terrorist attacks. Beyond failures to create security, there is the matter of misuse or abuse of U.S. spying, the effects of which extend well beyond violations of Americans constitutional liberties. Obama, meanwhile, has taken virtually no steps to fix what ails his spying apparatus, [but] has gone after people blowing the whistle on intelligence abuses. The Justice Department has charged eight leakers more than double the number under all previous presidents combined.
Note: The above was written by James Bamford, whistleblower and author of "The Shadow Factory: The Ultra-Secret NSA From 9/11 to the Eavesdropping on America." Former US Senator Frank Church warned of the dangers of creating a surveillance state in 1975. By 2013, it had become evident that the US did not heed his warning. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
A photo circulating online of Facebook CEO Mark Zuckerberg's personal laptop has ignited a conversation about data security. The photo shows a smiling Zuckerberg sitting next to his laptop. His computer's camera and microphone are covered with tape. Tape? Yes, tape. Covering a computer's camera doesn't protect the device from being hacked, but it does prevent a hacker from being able to see whatever the camera sees. Covering a laptop's microphone can muffle the audio enough to prevent a hacker from listening in, uninvited. Security experts say it's not paranoid - it's good sense. A hacker can get access to your entire computer, without your knowledge, relatively easily. [Security professional Dave] Lewis said he's been able to breach a system and take control of a person's laptop camera without their knowledge. "And it doesn't even always trip the light that shows the camera is live," he added. Unsurprisingly to many, women tend to be targets for this kind of hacking. It's more common than we think, said John Scott-Railton, a senior researcher at the ... University of Toronto. Scott-Railton said this practice is called "ratting," adding sometimes hackers will trade access to hacked computers. He said the same kind of software used to hack women's webcams is used to hack political dissidents, members of activist groups, and journalists. "These are people that are regularly targeted by different hacking groups because of their work. We have evidence that they're spied on through their webcams," he said.
Note: For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy.
From 2013 to 2015, the NSA and CIA doubled the number of warrantless searches they conducted for Americans data in a massive NSA database ostensibly collected for foreign intelligence purposes, according to a new intelligence community transparency report. The estimated number of search terms concerning a known U.S. person to get contents of communications within what is known as the 702 database was 4,672 - more than double the 2013 figure. And that doesnt even include the number of FBI searches on that database. A recently released ... court ruling confirmed that the FBI is allowed to run any number of searches it wants on that database, not only for national security probes but also to hunt for evidence of traditional crimes. No estimates have ever been released of how often that happens. The missing data from the FBI is of great concern to privacy advocates. The USA Freedom Act, passed in June 2015, conspicuously exempts the FBI from disclosing how often it searches the 702 database, the Project on Government Oversight (POGO) wrote in a letter to the Director of National Intelligence, James Clapper, in October 2015. There is every reason to believe the number of FBI queries far exceeds those of the CIA and NSA, POGO wrote. It is essential that you work with the attorney general to release statistics on the FBIs use of U.S. person queries. The new report also leaves unanswered how many Americans communications are collected in the first place.
Note: For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
The Obama administration on Thursday announced new rules that will let the NSA share vast amounts of private data gathered without warrant, court orders or congressional authorization with 16 other agencies, including the FBI, the Drug Enforcement Agency, and the Department of Homeland Security. The new rules allow ... those agencies to sift through raw data collected under a broad, Reagan-era executive order that gives the NSA virtually unlimited authority to intercept communications abroad. Previously, NSA analysts would filter out information they deemed irrelevant and mask the names of innocent Americans before passing it along. The last-minute adoption of the procedures is one of many examples of the Obama administration making new executive powers established by the Bush administration permanent, on the assumption that the executive branch could be trusted to police itself. Executive Order 12333 ... serves as authorization for the NSAs most massive surveillance programs. In 2014, a former state department official described NSA surveillance under 12333 as a universe of collection and storage beyond what Congress has authorized. This massive database inevitably includes vast amount of Americans communications swept up when they speak to people abroad, when they go abroad themselves, or even if their domestic communications are simply routed abroad. Thats why access was previously limited to data that had already been screened to remove unrelated information and information identifying U.S. persons.
Note: For an important viewpoint on the real complexities going on with recent reporting on Trump links to Russia, CIA involvement in Syria, and media manipulations, don't miss this provocative article by Glenn Greenwald and this interview he gave to Fox News. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
The Wall Street Journal reported yesterday that the NSA under President Obama targeted Israeli Prime Minister Benjamin Netanyahu and his top aides for surveillance. In the process, the agency ended up eavesdropping on ... U.S. lawmakers and American-Jewish groups. People who spent many years cheering for and defending ... programs of mass surveillance are suddenly indignant now that they know the eavesdropping included them. Long-time GOP chairman of the House Intelligence Committee and unyielding NSA defender Pete Hoekstra last night was truly indignant: "WSJ report that NSA spied on Congress and Israel communications very disturbing. Actually outrageous. Maybe unprecedented abuse of power ... NSA and Obama officials need to be investigated and prosecuted. NSA loses all credibility. Scary." This pattern - whereby political officials who are vehement supporters of the Surveillance State transform overnight into crusading privacy advocates once they learn that they themselves have been spied on - is one that has repeated itself over and over. So now, with yesterdays WSJ report, we witness the tawdry spectacle of large numbers of people who for years were fine with, responsible for, and even giddy about NSA mass surveillance suddenly objecting. Overnight, privacy is of the highest value because now its their privacy, rather than just yours, that is invaded.
Note: Read the full Wall Street Journal article on how the US government is secretly spying on Israeli leaders and more. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
Its a wretched yet predictable ritual after each new terrorist attack: Certain politicians and government officials waste no time exploiting the tragedy for their own ends. The remarks on Monday by John Brennan, the director of the Central Intelligence Agency, took that to a new and disgraceful low ... after coordinated terrorist attacks in Paris killed 129. Mr. Brennan complained about ... the sustained national outrage following the 2013 revelations by Edward Snowden, a former National Security Agency contractor, that the agency was using provisions of the Patriot Act to secretly collect information on millions of Americans phone records. It is hard to believe anything Mr. Brennan says. Last year, he bluntly denied that the C.I.A. had illegally hacked into the computers of Senate staff members conducting an investigation into the agencys detention and torture programs when, in fact, it did. In 2011 ... he claimed that American drone strikes had not killed any civilians, despite clear evidence that they had. And his boss, James Clapper Jr., the director of national intelligence, has admitted lying to the Senate on the N.S.A.s bulk collection of data. Even putting this lack of credibility aside, its not clear what extra powers Mr. Brennan is seeking. Most of the men who carried out the Paris attacks were already on the radar of intelligence officials in France and Belgium, where several of the attackers lived. The problem in this case was not a lack of data. In fact, indiscriminate bulk data sweeps have not been useful.
Note: The above is an excellent article by the New York Times editorial board. Yet the role of the largely subservient media, which strongly supported Bush's campaign to go to war in Iraq is ignored. Read this analysis to go even deeper. For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the disappearance of privacy.
The National Security Agencys ability to spy on vast quantities of Internet traffic passing through the United States has relied on its extraordinary, decades-long partnership with a single company: the telecom giant AT&T. The N.S.A.s top-secret budget in 2013 for the AT&T partnership was more than twice that of the next-largest such program, [and] the company installed surveillance equipment in at least 17 of its Internet hubs on American soil, far more than its similarly sized competitor, Verizon. After the terrorist attacks of Sept. 11, 2001, AT&T ... began turning over emails and phone calls within days after the warrantless surveillance began in October 2001. In 2011, AT&T began handing over 1.1 billion domestic cellphone calling records a day to the N.S.A. after a push to get this flow operational prior to the 10th anniversary of 9/11, according to an internal agency newsletter. In a 2006 lawsuit, a retired AT&T technician named Mark Klein claimed that ... he had seen a secret room in a company building in San Francisco where the N.S.A. had installed equipment. Mr. Klein claimed that AT&T was providing the N.S.A. with access to Internet traffic that AT&T transmits for other telecom companies. Such cooperative arrangements, known in the industry as peering, mean that communications from customers of other companies could end up on AT&Ts network.
Note: The story of Klein's lawsuit was initially suppressed by the NSA and major media including the L.A. Times. For more along these lines, see concise summaries of deeply revealing news articles about questionable intelligence agency practices and the erosion of privacy.
Retailers have the ability to scan your face digitally, and use that identification to offer you special prices or even recognize you as a prior shoplifter. But should they use it? Should they get your permission first? Privacy advocates announced Tuesday they have walked away from a government-run effort with industry intended to ... hash out voluntary protocols for facial recognition technology in a way that doesn't hurt consumers. The Commerce Department's National Telecommunications and Information Administration, or NTIA, was acting as mediator. The two sides had been meeting for 16 months ... until the nine major privacy groups said they had hit a dead end and that "people deserve more protection than they are likely to get in this forum. At a base minimum, people should be able to walk down a public street without fear that companies they've never heard of are tracking their every movement and identifying them by name using facial recognition technology," the groups said. "We have been unable to obtain agreement even with that basic, specific premise." The ability to apply a unique signature to a person's face, even if you don't identify them by name, is particularly invasive, according to privacy advocates. "You can change your password and your credit card number; you cannot change your fingerprints or the precise dimensions of your face. Through facial recognition, these immutable, physical facts can be used to identify you, remotely and in secret, without any recourse."
Note: Read this article for more in this matter. Remember, the same technologies that lead to the disappearance of privacy rights for individuals are also used by corrupt corporations against nonprofit civic organizations to undermine democracy.
Last summer ... I spent three days in Moscow hanging out with Edward Snowden for a Wired cover story. He told me that what finally drove him to leave his country and become a whistleblower was his conviction that the National Security Agency was conducting illegal surveillance on every American. Thursday, the Second Circuit Court of Appeals in New York ... ruled that the NSA program that secretly intercepts the telephone metadata of every American who calls whom and when was illegal. Its now up to Congress to vote on whether or not to modify the law ... by June 1, when they need to reauthorize the Patriot Act. A PEW survey in March revealed that 52 percent of the public is now concerned about government surveillance, while 46 percent is not. There is now a sort of acceptance of highly intrusive surveillance as the new normal, [while] the American public [remains] unaware of many of the agencys long list of abuses. It is little wonder that only slightly more than half the public is concerned. For that reason, I agree with Frederick A. O. Schwartz Jr., the former chief counsel of the Church Committee, which conducted a yearlong probe into intelligence abuses in the mid-1970s, that we need a similarly thorough ... investigation today. Now it is time for a new committee to examine our secret government closely again, he wrote in a recent Nation magazine article, particularly for its actions in the post-9/11 period.
Note: The author of this excellent article is James Bamford, the former ABC News producer who broke the story on Operation Northwoods and has written landmark books on the NSA. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the erosion of privacy rights from reliable major media sources.
Edward Snowdens most famous leak has just been vindicated. Since June 2013, when he revealed that the telephone calls of Americans are being logged en masse, his critics have charged that he took it upon himself to expose a lawful secret. They insisted that Congress authorized the phone dragnet when it passed the U.S.A. Patriot Act. A panel of judges on the Second Circuit Court of Appeals ruled last week that the program Snowden exposed was never legal. The Patriot Act does not authorize it, contrary to the claims of George W. Bush, Barack Obama, Michael Hayden, Keith Alexander, and James Clapper. Statutes to which the government points have never been interpreted to authorize anything approaching the breadth of the sweeping surveillance at issue here, Judge Gerard E. Lynch declared. Consider what this means. For many years, the executive branch carried out a hugely consequential policy change that the legislature never approved. Tens of millions of innocent U.S. citizens were thus subject to invasions of privacy that no law authorized. Officials classified the program as a state secret, keeping it out of Article III courts. By doing so, they prevented the judiciary from reviewing the statutory legitimacy of NSA surveillance, subverting a core check in our system of government. The consequence: An illegal program persisted for years. This is a perfect illustration of why secret government programs are an abomination in our democracy.
Note: For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the erosion of privacy rights from reliable major media sources.
American and British spies hacked into the internal computer network of the largest manufacturer of SIM cards in the world, stealing encryption keys used to protect the privacy of cellphone communications across the globe, according to top-secret documents provided to The Intercept by National Security Agency whistleblower Edward Snowden. The hack was perpetrated by a joint unit consisting of operatives from the NSA and its British counterpart Government Communications Headquarters, or GCHQ. The breach, detailed in a secret 2010 GCHQ document, gave the surveillance agencies the potential to secretly monitor a large portion of the worlds cellular communications, including both voice and data. The company targeted by the intelligence agencies, Gemalto, is a multinational firm incorporated in the Netherlands. With these stolen encryption keys, intelligence agencies can monitor mobile communications without seeking or receiving approval from telecom companies and foreign governments. Possessing the keys also sidesteps the need to get a warrant or a wiretap, while leaving no trace on the wireless providers network that the communications were intercepted.
Note: In an article that updates the story above, The Intercept reports that Gemalto has now acknowledged this security breach, but is misrepresenting its significance to prevent client and investor fears from harming the company's profitability. For more along these lines, see concise summaries of deeply revealing news articles about corruption in intelligence agencies and government.
The US justice department is reportedly using electronic equipment on aircraft to simulate cellphone towers so it can collect phone location and identifying information on a mass scale from users on the ground below. The US Marshals Service has for seven years flown Cessna aircraft ... that mimic cellular towers, permitting the collection of thousands of unique IDs and location data from users. The planes operate from at least five metropolitan airports, permitting a flying range covering most of the US population. [This] indiscriminate collection would permit ... justice department agencies to avoid having to seek records from the phone companies themselves, especially in criminal investigations where a court order may be required. The legal basis for the previously undisclosed program is unclear. It is not reportedly a national security or counterterrorism program. Michael German, a former FBI agent now with New York University Law School, said: The governments attitude seems to be if it can, it should, without regard to the violation of Americans rights, so long as nobody knows. This program is being kept secret so that the thousands of innocent Americans whose data is being collected improperly wont complain. We shouldnt have to just trust that the government will handle the data it intercepts about our communications properly.
Note: For more along these lines, see these concise summaries of deeply revealing government corruption and privacy news articles from reliable sources.
Prime Minister John Key ... has denied that New Zealands spy agency GCSB engages in mass surveillance, mostly as a means of convincing the country to enact a new law vesting the agency with greater powers. Let me be clear: any statement that mass surveillance is not performed in New Zealand, or that the internet communications are not comprehensively intercepted and monitored, or that this is not intentionally and actively abetted by the GCSB, is categorically false. If you live in New Zealand, you are being watched. At the NSA I routinely came across the communications of New Zealanders in my work with a mass surveillance tool we share with GCSB, called XKEYSCORE. It allows total, granular access to the database of communications collected in the course of mass surveillance. It is not limited to or even used largely for the purposes of cybersecurity, as has been claimed, but is instead used primarily for reading individuals private email, text messages, and internet traffic. I know this because it was my full-time job in Hawaii, where I worked every day in an NSA facility with a top secret clearance. The prime ministers claim to the public, that there is no and there never has been any mass surveillance is false. The GCSB, whose operations he is responsible for, is directly involved in the untargeted, bulk interception and algorithmic analysis of private communications sent via internet, satellite, radio, and phone networks. It means they have the ability see every website you visit, every text message you send, every call you make, every ticket you purchase, every donation you make, and every book you order online. From Im headed to church to I hate my boss to Shes in the hospital, the GCSB is there. Your words are intercepted, stored, and analyzed by algorithms long before theyre ever read by your intended recipient.
Note: New Zealand's prime minister has acknowledged that Snowden may be right, as reported in this article. For more on this, see concise summaries of deeply revealing government surveillance news articles from reliable major media sources.
Throughout the last year, the U.S. government has repeatedly insisted that it does not engage in economic and industrial espionage, in an effort to distinguish its own spying from Chinas infiltrations of Google, Nortel, and other corporate targets. [But] the NSA was caught spying on plainly financial targets such as the Brazilian oil giant Petrobras; economic summits; international credit card and banking systems; the EU antitrust commissioner investigating Google, Microsoft, and Intel; and the International Monetary Fund and World Bank. In response, the U.S. modified its denial to acknowledge that it does engage in economic spying, but unlike China, the spying is never done to benefit American corporations. But a secret 2009 report issued by [Director of National Intelligence James Clapper's] office explicitly contemplates doing exactly that. The document, the 2009 Quadrennial Intelligence Community Reviewprovided by NSA whistleblower Edward Snowdenis a fascinating window into the mindset of Americas spies. One of the principal threats raised in the report is a scenario in which the United States technological and innovative edge slips in particular, that the technological capacity of foreign multinational corporations could outstrip that of U.S. corporations. How could U.S. intelligence agencies solve that problem? The report recommends a multi-pronged, systematic effort to gather open source and proprietary information through overt means, clandestine penetration (through physical and cyber means), and counterintelligence.
Note: For more on this, see concise summaries of deeply revealing intelligence agency operations news articles from reliable major media sources.
Les Goldsmith, the CEO of ESD America [marketers of the Crytophone 500], points me to a map that he and his customers have created, indicating 17 different phony cell towers known as interceptors, detected by the CryptoPhone 500 around the United States during the month of July alone. Interceptors look to a typical phone like an ordinary tower. Once the phone connects with the interceptor, a variety of over-the-air attacks become possible, from eavesdropping on calls and texts to pushing spyware to the device. Interceptor use in the U.S. is much higher than people had anticipated, Goldsmith says. One of our customers took a road trip from Florida to North Carolina and he found 8 different interceptors on that trip. We even found one at South Point Casino in Las Vegas. Who is running these interceptors and what are they doing with the calls? Goldsmith says we cant be sure, but he has his suspicions. Are some of them U.S. government interceptors? [asks] Goldsmith. Interceptors vary widely in expense and sophistication but in a nutshell, they are radio-equipped computers with software that can use arcane cellular network protocols and defeat the onboard encryption. For governments or other entities able to afford a price tag of less than $100,000, says Goldsmith, high-quality interceptors are quite realistic. Some interceptors are limited, only able to passively listen to either outgoing or incoming calls. But full-featured devices like the VME Dominator, available only to government agencies, can not only capture calls and texts, but even actively control the phone, sending out spoof texts, for example.
Note: Do you think the government might have put up fake cell towers to nab more data? For more on this, see concise summaries of deeply revealing government surveillance news articles from reliable major media sources.
The National Security Agency is secretly providing data to nearly two dozen U.S. government agencies with a Google-like search engine built to share more than 850 billion records about phone calls, emails, cellphone locations, and internet chats, according to classified documents obtained by The Intercept. The documents provide the first definitive evidence that the NSA has for years made massive amounts of surveillance data directly accessible to domestic law enforcement agencies. ICREACH [as the search engine is called] contains information on the private communications of foreigners and, it appears, millions of records on American citizens who have not been accused of any wrongdoing. Details about its existence are contained in the archive of materials provided to The Intercept by NSA whistleblower Edward Snowden. Earlier revelations sourced to the Snowden documents have exposed a multitude of NSA programs for collecting large volumes of communications. The NSA has acknowledged that it shares some of its collected data with domestic agencies like the FBI, but details about the method and scope of its sharing have remained shrouded in secrecy. ICREACH has been accessible to more than 1,000 analysts at 23 U.S. government agencies that perform intelligence work, according to a 2010 memo. Information shared through ICREACH can be used to track peoples movements, map out their networks of associates, help predict future actions, and potentially reveal religious affiliations or political beliefs.
Note: For more on this, see concise summaries of deeply revealing government surveillance news articles from reliable major media sources.
A classified 2010 legal certification and other documents indicate the NSA has been given a far more elastic authority than previously known, one that allows it to intercept through U.S. companies not just the communications of its overseas targets but any communications about its targets as well. The certification approved by the Foreign Intelligence Surveillance Court and included among a set of documents leaked by former NSA contractor Edward Snowden lists 193 countries that would be of valid interest for U.S. intelligence. The certification also permitted the agency to gather intelligence about entities including the World Bank, the International Monetary Fund, the European Union and the International Atomic Energy Agency. The documents underscore the remarkable breadth of potential foreign intelligence collection. An affidavit in support of the 2010 foreign-government certification said the NSA believes that foreigners who will be targeted for collection possess, are expected to receive and/or are likely to communicate foreign intelligence information concerning these foreign powers. That language could allow for surveillance of academics, journalists and human rights researchers. A Swiss academic who has information on the German governments position in the run-up to an international trade negotiation, for instance, could be targeted if the government has determined there is a foreign-intelligence need for that information. If a U.S. college professor e-mails the Swiss professors e-mail address or phone number to a colleague, the Americans e-mail could be collected as well, under the programs court-approved rules.
Note: For more on this, see concise summaries of deeply revealing intelligence agency news articles from reliable major media sources.
The Obama administration has been quietly advising local police not to disclose details about surveillance technology they are using to sweep up basic cellphone data from entire neighborhoods. Citing security reasons, the U.S. has intervened in routine state public records cases and criminal trials regarding use of the technology. This has resulted in police departments withholding materials or heavily censoring documents in rare instances when they disclose any [information] about the purchase and use of such powerful surveillance equipment. One well-known type of this surveillance equipment is known as a Stingray. The equipment tricks cellphones into identifying some of their owners' account information, like a unique subscriber number, and transmitting data to police as if it were a phone company's tower. That allows police to obtain cellphone information without having to ask for help from service providers ... and can locate a phone without the user even making a call or sending a text message. The Obama administration is asking agencies to withhold common information about the equipment, such as how the technology is used and how to turn it on. "These extreme secrecy efforts are in relation to very controversial, local government surveillance practices using highly invasive technology," said Nathan Freed Wessler, a staff attorney with the American Civil Liberties Union, which has fought for the release of these types of records. "People should have the facts about what the government is doing to them."
Note: For more on this, see concise summaries of deeply revealing government surveillance news articles from reliable major media sources.
Government agencies are able to listen to phone conversations live and even track the location of citizens without warrants using secret cables connected directly to network equipment, admits Vodafone today. The company said that secret wires have been connected to its network and those belonging to competitors, giving government agencies the ability to tap in to phone and broadband traffic. In many countries this is mandatory for all telecoms companies, it said. Vodafone is today publishing its first Law Enforcement Disclosure Report which will describe exactly how the governments it deals with are eavesdropping on citizens. It is calling for an end to the use of direct access eavesdropping and transparency on the number of warrants issued giving access to private data. Gus Hosein, executive director of Privacy International, said: "Vodafone is taking a commendable step by taking this issue on at an international scale. And they are trying to identify the legal basis for governments' claimed powers. Governments around the world are unashamedly abusing privacy by demanding access to communications and data, and alarmingly, sometimes granting themselves direct access to the networks. Now that Vodafone has been more open, the entire industry has cover to take the necessary next step of pushing back. Pushing back against bad requests is a start, pushing back against bad laws is the next step. The usefulness of transparency reports hinges on governments abiding by the rule of law. We now know that these reports only provide a limited picture of what is going on.
Note: For more on government surveillance of the world's population, see the deeply revealing reports from reliable major media sources available here.
The National Security Agency has never said what it was seeking when it invaded the computers of Petrobras, Brazils huge national oil company, but angry Brazilians have guesses: the companys troves of data on Brazils offshore oil reserves, or perhaps its plans for allocating licenses for exploration to foreign companies. Nor has the N.S.A. said what it intended when it got deep into the computer systems of China Telecom, one of the largest providers of mobile phone and Internet services in Chinese cities. But documents released by Edward J. Snowden, the former agency contractor now in exile in Russia, leave little doubt that the main goal was to learn about Chinese military units, whose members cannot resist texting on commercial networks. The agencys interest in Huawei, the giant Chinese maker of Internet switching equipment, and Pacnet, the Hong Kong-based operator of undersea fiber optic cables, is more obvious: Once inside those companies proprietary technology, the N.S.A. would have access to millions of daily conversations and emails that never touch American shores. The [US] government does not deny it routinely spies to advance American economic advantage, which is part of its broad definition of how it protects American national security. While the N.S.A. cannot spy on Airbus and give the results to Boeing, it is free to spy on European or Asian trade negotiators and use the results to help American trade officials and, by extension, ... American industries.
Note: For more on the realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
Britains electronic surveillance agency, Government Communications Headquarters [GCHQ], has long presented its collaboration with the National Security Agencys massive electronic spying efforts as proportionate, carefully monitored, and well within the bounds of privacy laws. But according to a top-secret document in the archive of material provided to The Intercept by NSA whistleblower Edward Snowden, GCHQ secretly coveted the NSAs vast troves of private communications and sought unsupervised access to its data as recently as last year. The document, dated April 2013, reveals that GCHQ requested broad new authority to tap into data collected under a law that authorizes a variety of controversial NSA surveillance initiatives, including the PRISM program. PRISM is a system used by the NSA and the FBI to obtain the content of personal emails, chats, photos, videos, and other data processed by nine of the worlds largest internet companies, including Google, Yahoo!, Microsoft, Apple, Facebook, and Skype. The arrangement GCHQ proposed would also have provided the British agency with greater access to millions of international phone calls and emails that the NSA siphons directly from phone networks and the internet. The Snowden files do not indicate whether NSA granted GCHQs request, but they do show that the NSA was supportive of the idea, and that GCHQ was permitted extensive access to PRISM during the London Olympics in 2012. The request for the broad access was communicated at leadership level.
Note: For more on the construction of a total surveillance state, see the deeply revealing reports from reliable major media sources available here.
US intelligence chiefs have confirmed that the National Security Agency has [performed] warrantless searches on Americans communications. The NSA's collection programs are ostensibly targeted at foreigners, but in August the Guardian revealed a secret rule change allowing NSA analysts to search for Americans' details within the databases. Now, in a letter to Senator Ron Wyden, an Oregon Democrat on the intelligence committee, the director of national intelligence, James Clapper, has confirmed the use of this legal authority to search for data related to US persons. The legal authority to perform the searches, revealed in top-secret NSA documents provided ... by Edward Snowden, was denounced by Wyden as a backdoor search loophole. Many of the NSA's most controversial programs collect information under the law affected by the so-called loophole. These include Prism, which allows the agency to collect data from Google, Apple, Facebook, Yahoo and other tech companies, and the agency's Upstream program a huge network of internet cable taps. Confirmation that the NSA has searched for Americans communications in its phone call and email databases complicates President Barack Obamas initial defenses of the broad surveillance in June. Wyden and Udall [said] Todays admission by the Director of National Intelligence is further proof that meaningful surveillance reform must include closing the back-door searches loophole and requiring the intelligence community to show probable cause before deliberately searching through ... the communications of individual Americans."
Note: For more on the realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
The National Security Agency has built a surveillance system capable of recording 100 percent of a foreign countrys telephone calls, enabling the agency to rewind and review conversations as long as a month after they take place, according to people with direct knowledge of the effort and documents supplied by former contractor Edward Snowden. A senior manager for the program compares it to a time machine one that can replay the voices from any call without requiring that a person be identified in advance for surveillance. The voice interception program, called MYSTIC, began in 2009. Its RETRO tool, short for retrospective retrieval, and related projects reached full capacity against the first target nation in 2011. Planning documents two years later anticipated similar operations elsewhere. In the initial deployment, collection systems are recording every single conversation nationwide, storing billions of them in a 30-day rolling buffer that clears the oldest calls as new ones arrive, according to a classified summary. Analysts listen to only a fraction of 1 percent of the calls, but the absolute numbers are high. Each month, they send millions of voice clippings, or cuts, for processing and long-term storage. At the request of U.S. officials, The Washington Post is withholding details that could be used to identify the country where the system is being employed or other countries where its use was envisioned.
Note: Though technically it is illegal for the NSA to snoop on Americans without good cause, all they have to do is to share this technology with another country like the UK, and then ask the UK to do the snooping and send the results back to them, thereby circumventing the law. For more on NSA surveillance, see the deeply revealing reports from reliable major media sources available here.
The list of those caught up in the global surveillance net cast by the National Security Agency and its overseas partners, from social media users to foreign heads of state, now includes another entry: US lawyers. A top-secret document, obtained by former NSA contractor Edward J. Snowden, shows that a US law firm was monitored while representing a foreign government in trade disputes with the United States. The disclosure offers a rare glimpse of a specific instance of Americans ensnared by the eavesdroppers and is of particular interest because US lawyers with clients overseas have expressed growing concern that their confidential communications could be compromised by such surveillance. The government of Indonesia had retained the law firm for help in trade talks, according to the February 2013 document. The NSAs Australian counterpart, the Australian Signals Directorate, notified the agency that it was conducting surveillance of the talks, including communications between Indonesian officials and the US law firm, and offered to share information. The NSA is banned from targeting Americans, including businesses, law firms, and other organizations based in the United States, for surveillance without warrants, and intelligence officials have repeatedly said the NSA does not use spy services of its partners in the so-called Five Eyes alliance Australia, Britain, Canada, and New Zealand to skirt the law. The Australians told officials at an NSA liaison office in Canberra, that information covered by attorney-client privilege may be included in the intelligence gathering. Most attorney-client conversations do not get special protections under US law from NSA eavesdropping.
Note: For more on intense deception perpetrated by the intelligence community, see the deeply revealing reports from reliable major media sources available here.
An independent federal privacy watchdog has concluded that the National Security Agencys program to collect bulk phone call records has provided only minimal benefits in counterterrorism efforts, is illegal and should be shut down. The findings are laid out in a 238-page report [that represents] the first major public statement by the Privacy and Civil Liberties Oversight Board, which Congress made an independent agency in 2007 and only recently became fully operational. The Obama administration has portrayed the bulk collection program as useful and lawful. But in its report, the board lays out what may be the most detailed critique of the governments once-secret legal theory behind the program: that a law known as Section 215 of the Patriot Act, which allows the F.B.I. to obtain business records deemed relevant to an investigation, can be legitimately interpreted as authorizing the N.S.A. to collect all calling records in the country. The program lacks a viable legal foundation under Section 215, implicates constitutional concerns under the First and Fourth Amendments, raises serious threats to privacy and civil liberties as a policy matter, and has shown only limited value, the report said. As a result, the board recommends that the government end the program. The report also sheds light on the history of the once-secret bulk collection program. It contains the first official acknowledgment that the Foreign Intelligence Surveillance Court produced no judicial opinion detailing its legal rationale for the program until last August, even though it had been issuing orders to phone companies for the records and to the N.S.A. for how it could handle them since May 2006.
Note: The PCLOB report is titled "Report on the Telephone Records Program Conducted under Section 215 of the USA PATRIOT Act and on the Operations of the Foreign Intelligence Surveillance Court," and is available here. For more on government attacks to privacy, see the deeply revealing reports from reliable major media sources available here.
The National Security Agency has collected almost 200 million text messages a day from across the globe, using them to extract data including location, contact networks and credit card details, according to top-secret documents. The NSA program, codenamed Dishfire, collects pretty much everything it can, according to GCHQ documents, rather than merely storing the communications of existing surveillance targets. The NSA has made extensive use of its vast text message database to extract information on peoples travel plans, contact books, financial transactions and more including of individuals under no suspicion of illegal activity. On average, each day the NSA was able to extract: More than 5 million missed-call alerts, for use in contact-chaining analysis (working out someones social network from who they contact and when) Details of 1.6 million border crossings a day, from network roaming alerts More than 110,000 names, from electronic business cards, which also included the ability to extract and save images. Over 800,000 financial transactions, either through text-to-text payments or linking credit cards to phone users The agency was also able to extract geolocation data from more than 76,000 text messages a day, including from requests by people for route info and setting up meetings.
Note: For more on government surveillance, see the deeply revealing reports from reliable major media sources available here.
As a key part of a campaign to embed encryption software that it could crack into widely used computer products, the U.S. National Security Agency arranged a secret $10 million contract with RSA, one of the most influential firms in the computer security industry. Documents leaked by former NSA contractor Edward Snowden show that the NSA created and promulgated a flawed formula for generating random numbers to create a "back door" in encryption products, the New York Times reported in September. Reuters later reported that RSA became the most important distributor of that formula by rolling it into a software tool called Bsafe that is used to enhance security in personal computers and many other products. Undisclosed until now was that RSA received $10 million in a deal that set the NSA formula as the preferred, or default, method for number generation in the BSafe software, according to two sources familiar with the contract. Although that sum might seem paltry, it represented more than a third of the revenue that the relevant division at RSA had taken in during the entire previous year. The RSA deal shows one way the NSA carried out what Snowden's documents describe as a key strategy for enhancing surveillance: the systematic erosion of security tools. NSA documents released in recent months called for using "commercial relationships" to advance that goal, but did not name any security companies as collaborators.
Note: For more on the realities of intelligence agency activities, see the deeply revealing reports from reliable major media sources available here.
A 36-year NSA veteran, William Binney resigned from the agency and became a whistleblower after discovering that elements of a data-monitoring program he had helped develop - nicknamed ThinThread - were being used to spy on Americans. So 2005, December, The New York Times article comes out. ... How important was it? "It touched on that real issues," [said Binney]. "The warrantless wiretapping was not really a major component of it, but it touched on the data mining, which is really, really the big issue, data mining of the metadata and content. That was really the big issue, because that's how you can monitor the entire population simultaneously, whereas the warrantless wiretaps were isolated cases. You could pick an isolated number of them and do them, whereas in the mining process, you would do the entire population." The administration [used] this article to start an aggressive whistleblowing hunt. "[On July 22, 2005] the FBI was in my house ... pointing a gun at me when I was coming out of the shower. The raid took about seven hours. At the time we didn't know that Tom Drake had gone to The Baltimore Sun," [said Binney]. "Material [Tom Drake was indicted for] was clearly marked unclassified, and all they did was draw a line through it and classified that material, and then they charged him with having classified material. It's like framing him. The judge in the court ... knew they were framing him," [said Biney].
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
British and U.S. intelligence officials say they are worried about a "doomsday" cache of highly classified, heavily encrypted material they believe former National Security Agency contractor Edward Snowden has stored on a data cloud. The cache contains documents generated by the NSA and other agencies and includes names of U.S. and allied intelligence personnel, seven current and former U.S. officials and other sources briefed on the matter said. One source described the cache of still unpublished material as Snowden's "insurance policy" against arrest or physical harm. U.S. officials and other sources said only a small proportion of the classified material Snowden downloaded during stints as a contract systems administrator for NSA has been made public. Some Obama Administration officials have said privately that Snowden downloaded enough material to fuel two more years of news stories. "The worst is yet to come," said one former U.S. official who follows the investigation closely. Snowden ... is believed to have downloaded between 50,000 and 200,000 classified NSA and British government documents. [It is] estimated that the total number of Snowden documents made public so far is over 500. Glenn Greenwald, who met with Snowden in Hong Kong and was among the first to report on the leaked documents for the Guardian newspaper, said the former NSA contractor had "taken extreme precautions to make sure many different people around the world have these archives to insure the stories will inevitably be published."
Note: For more on the realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
The German, French, Spanish and Swedish intelligence services have all developed methods of mass surveillance of internet and phone traffic over the past five years in close partnership with Britain's GCHQ eavesdropping agency. The bulk monitoring is carried out through direct taps into fibre optic cables and the development of covert relationships with telecommunications companies. A loose but growing eavesdropping alliance has allowed intelligence agencies from one country to cultivate ties with corporations from another to facilitate the trawling of the web, according to GCHQ documents leaked by the former US intelligence contractor Edward Snowden. The files also make clear that GCHQ played a leading role in advising its European counterparts how to work around national laws intended to restrict the surveillance power of intelligence agencies. US intelligence officials have insisted the mass monitoring was carried out by the security agencies in the countries involved and shared with the US. The Guardian revealed the existence of GCHQ's Tempora programme, in which the electronic intelligence agency tapped directly into the transatlantic fibre optic cables to carry out bulk surveillance. GCHQ officials expressed admiration for the technical capabilities of German intelligence to do the same thing, [saying] the Federal Intelligence Service (BND) had "huge technological potential and good access to the heart of the internet they are already seeing some bearers running at 40Gbps and 100Gbps". Bearers is the GCHQ term for the fibre optic cables, and gigabits per second (Gbps) measures the speed at which data runs through them.
Note: For more on the realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
What are we to make of Edward Snowden? I know what I once made of him. He was no real whistleblower, I wrote, but ridiculously cinematic and narcissistic as well. As time has proved, my judgments were just plain wrong. Whatever Snowden is, he is curiously modest and has bent over backward to ensure that the information he has divulged has done as little damage as possible. As a traitor, he lacks the requisite intent and menace. But traitor is what Snowden has been roundly called. Harry Reid: I think Snowden is a traitor. John Boehner: Hes a traitor. Rep. Peter King: This guy is a traitor; hes a defector. And Dick Cheney not only denounced Snowden as a traitor but also suggested that he might have shared information with the Chinese. This innuendo, as with Saddam Husseins weapons of mass destruction, is more proof of Cheneys unerring determination to be cosmically wrong. The early denunciations of Snowden now seem both over the top and beside the point. If he is a traitor, then which side did he betray and to whom does he now owe allegiance? Snowden seems to have sold out to no one. In fact, a knowledgeable source says that Snowden has not even sold his life story and has rebuffed offers of cash for interviews. Maybe his most un-American act is passing up a chance at easy money. Someone ought to look into this. Snowdens residency in Russia has been forced upon him he had nowhere else to go. Snowden insists that neither the Russians nor, before them, the Chinese have gotten their grubby hands on his top-secret material.
Note: For more on the hidden realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
Federal grants of $7 million, initially intended to help thwart terror attacks at the port in Oakland, Calif., are instead going to a police initiative that will collect and analyze reams of surveillance data. The new system ... is the latest example of how cities are compiling and processing large amounts of information, known as big data, for routine law enforcement. And the system underscores how technology has enabled the tracking of people in many aspects of life. Like the Oakland effort, other pushes to use new surveillance tools in law enforcement are supported with federal dollars. The New York Police Department, aided by federal financing, has a big data system that links 3,000 surveillance cameras with license plate readers, radiation sensors, criminal databases and terror suspect lists. Police in Massachusetts have used federal money to buy automated license plate scanners. And police in Texas have bought a drone with homeland security money. [Critics] of the Oakland initiative, formally known as the Domain Awareness Center, [say] the program, which will create a central repository of surveillance information, will also gather data about the everyday movements and habits of law-abiding residents. Oakland has a contract with the Science Applications International Corporation, or SAIC, to build its system. That company has earned the bulk of its $12 billion in annual revenue from military contracts.
Note: For more on government privacy invasions, see the deeply revealing reports from reliable major media sources available here.
US and British intelligence agencies have successfully cracked much of the online encryption relied upon by hundreds of millions of people to protect the privacy of their personal data, online transactions and emails, according to top-secret documents revealed by former contractor Edward Snowden. The files show that the National Security Agency and its UK counterpart GCHQ have broadly compromised the guarantees that internet companies have given consumers to reassure them that their communications, online banking and medical records would be indecipherable to criminals or governments. The agencies, the documents reveal, have adopted a battery of methods in their systematic and ongoing assault on what they see as one of the biggest threats to their ability to access huge swathes of internet traffic "the use of ubiquitous encryption across the internet". Those methods include covert measures to ensure NSA control over setting of international encryption standards, the use of supercomputers to break encryption with "brute force", and the most closely guarded secret of all collaboration with technology companies and internet service providers themselves. Through these covert partnerships, the agencies have inserted secret vulnerabilities known as backdoors or trapdoors into commercial encryption software. "Backdoors are fundamentally in conflict with good security," said Christopher Soghoian, principal technologist and senior policy analyst at the American Civil Liberties Union. "Backdoors expose all users of a backdoored system, not just intelligence agency targets, to heightened risk of data compromise."
Note: For an excellent article in the New York Times on this, click here. For a guide from the Guardian on "How to remain secure against NSA surveillance", click here.
The New York Police Department has secretly labeled entire mosques as terrorism organizations, a designation that allows police to use informants to record sermons and spy on imams, often without specific evidence of criminal wrongdoing. Designating an entire mosque as a terrorism enterprise means that anyone who attends prayer services there is a potential subject of an investigation and fair game for surveillance. Since the 9/11 attacks, the NYPD has opened at least a dozen "terrorism enterprise investigations" into mosques, according to interviews and confidential police documents. Many TEIs stretch for years, allowing surveillance to continue even though the NYPD has never criminally charged a mosque or Islamic organization with operating as a terrorism enterprise. The documents show in detail how, in its hunt for terrorists, the NYPD investigated countless innocent New York Muslims and put information about them in secret police files. As a tactic, opening an enterprise investigation on a mosque is so potentially invasive that while the NYPD conducted at least a dozen, the FBI never did one, according to interviews with federal law enforcement officials. The revelations about the NYPD's massive spying operations are in documents recently obtained by The Associated Press and part of a new book, Enemies Within: Inside the NYPD's Secret Spying Unit... The book ... is based on hundreds of previously unpublished police files and interviews with current and former NYPD, CIA and FBI officials.
Note: For more on the realities of intelligence operations, see the deeply revealing reports from reliable major media sources available here.
Josh del Sol got curious in the summer of 2011 after a friend linked a serious illness to the recent installation of a "smart meter." Del Sol subsequently learned that electrical utilities across North America had been quietly installing "smart grids" that ... monitor Internet-connected meters and appliances in homes and businesses. Now, del Sol is on the verge of premiering a feature-length documentary ... titled Take Back Your Power, disclosing questionable industry practices in support of implementing networked control systems for power plants. The film links billing mistakes, invasive monitoring, even human illnesses to the rising use of smart grids in the U.S. and Europe. "Take Back Your Power delivers an ominous, powerful message about the energy industry's shift to closely watching how customers use energy in their home in an invasive, controversial manner," says Lee Waterworth, president of Yekra, a video-on-demand company. Del Sol says access to industry sources was tough. "We had a difficult time getting anyone in the industry to talk to us on camera once they found out that we were wanting to get to the bottom of some of these concerns," he says. The filmmaker was surprised by the contrast between the views of industry officials and those of ordinary citizens trying to get to the bottom of safety, privacy and health concerns. Del Sol hopes the documentary helps to prompt the electricity industry "to provide more transparency, accountability and clarity on the issues we explore in the film."
Note: You can find this documentary on the Internet. For more, read how solar providers are using "smart" systems to help their customers save money while traditional utilities use these systems only to cut their own costs. Meanwhile, concerns about the health impacts of wireless tech and the ongoing erosion of privacy rights continue to grow.
A Texas-based encrypted email service recently revealed to be used by Edward Snowden - Lavabit - announced yesterday it was shutting itself down in order to avoid complying with what it perceives as unjust secret US court orders to provide government access to its users' content. "After significant soul searching, I have decided to suspend operations," the company's founder, Ladar Levinson, wrote in a statement to users posted on the front page of its website. He said the US directive forced on his company "a difficult decision: to become complicit in crimes against the American people or walk away from nearly ten years of hard work by shutting down Lavabit." He chose the latter. CNET's Declan McCullagh ... speculates that Lavabit was served "with [a] federal court order to intercept users' passwords" to allow ongoing monitoring of emails; specifically: "the order can also be to install FedGov-created malware." After challenging the order in district court and losing - all in a secret court proceeding, naturally - Lavabit shut itself down to avoid compliance while it appeals to the Fourth Circuit. What is particularly creepy about the Lavabit self-shutdown is that the company is gagged by law even from discussing the legal challenges it has mounted and the court proceeding it has engaged. In other words, the American owner of the company believes his Constitutional rights and those of his customers are being violated by the US Government, but he is not allowed to talk about it. Lavabit has been told that they would face serious criminal sanctions if they publicly discuss what is being done to their company.
Note: For more on government and corporate privacy invasions, see the deeply revealing reports from reliable major media sources available here.
During last weeks Black Hat computer security conference in Las Vegas, researchers from iSEC Partners demonstrated a vulnerability in 2012 models of Samsungs line of Smart TVs, particularly the ones with that come with cameras designed for teleconferencing. The problem with the Samsung TVs highlights a much larger issue: The number of devices connected to the Internet is growing exponentially, and many of them have little or no security in place. Flaws may be found in almost any application on an Internet-connected platform that, if exploited, could allow access to the entire device, and then the users full network. Many of these unsecured devices can be found with a simple search. In fact, theres a search engine devoted just to scouring the so-called Internet of things called Shadon. Playing around with it is an eye-opener. For example, in late July a writer for Forbes discovered an entire home automation product line with Internet-connected features that could be set up without a default password, and were visible to search engines. This would enable a hacker to search and find these systems on the Net, then access them at will. To prove her point, Kashmir Hill breached the home automation systems of random strangers, called them on the phone and demonstrated the vulnerability by turning their lights on and off.
Note: For more on corporate and government privacy invasions, see the deeply revealing reports from reliable major media sources available here.
When you're watching TV ... you probably don't think someone could be on the other side watching you back. An alarming security flaw in Samsung's Smart-TVs makes this scenario possible. LAURIE SEGALL [CNN Money/Technology Correspondent]: We've spoken to a lot of folks and they're saying there are major vulnerabilities. YAVOR: One of the things we were able to do with the Smart-TV platform was abuse the browser so that we could actually gain access to the camera that's built into the TV. What we can prove here is that with a little bit of extra code, we can turn the camera on in your browser. This is something we can do invisibly and actually have it run behind the web page you're looking at. I could be sitting at a laptop in a cafe in Paris, and as long as I have a web connection, I would be able to get into your TV and access your camera. AARON GRATTAFIORI [security consultant]: The scary thing about it is that it doesn't give an indication that the camera is on and there is no LED that shows up when the camera is on. So they could actually be watching you and you would never even know. SEGALL: What is a Smart-TV, and why is it a playground, essentially, for hackers? GRATTAFIORI: It's a computer. So instead of being a tube and some other electronics, now it has a web browser and it has a lot of devices running Linux.
Note: To watch this video clip on CNN News, click here.
Computers and networks inherently produce data, and our constant interactions with them allow corporations to collect an enormous amount of intensely personal data about us as we go about our daily lives. Sometimes we produce this data inadvertently simply by using our phones, credit cards, computers and other devices. Sometimes we give corporations this data directly on Google, Facebook, [or] Apples iCloud ... in exchange for whatever free or cheap service we receive from the Internet in return. The NSA is also in the business of spying on everyone, and it has realized its far easier to collect all the data from these corporations rather than from us directly. The result is a corporate-government surveillance partnership, one that allows both the government and corporations to get away with things they couldnt otherwise. There are two types of laws in the U.S., each designed to constrain a different type of power: constitutional law, which places limitations on government, and regulatory law, which constrains corporations. Historically, these two areas have largely remained separate, but today each group has learned how to use the others laws to bypass their own restrictions. The government uses corporations to get around its limits, and corporations use the government to get around their limits. This partnership manifests itself in various ways. The government uses corporations to circumvent its prohibitions against eavesdropping domestically on its citizens. Corporations rely on the government to ensure that they have unfettered use of the data they collect.
Note: For more on government and corporate privacy invasions, see the deeply revealing reports from reliable major media sources available here.
In more than a dozen classified rulings, the nations surveillance court has created a secret body of law giving the National Security Agency the power to amass vast collections of data on Americans. The rulings, some nearly 100 pages long, reveal that the court has taken on a much more expansive role by regularly assessing broad constitutional questions and establishing important judicial precedents, with almost no public scrutiny. The 11-member Foreign Intelligence Surveillance Court, known as the FISA court, was once mostly focused on approving case-by-case wiretapping orders. But since major changes in legislation and greater judicial oversight of intelligence operations were instituted six years ago, it has quietly become almost a parallel Supreme Court, serving as the ultimate arbiter on surveillance issues and delivering opinions that will most likely shape intelligence practices for years to come. In one of the courts most important decisions, the judges have expanded the use in terrorism cases of a legal principle known as the special needs doctrine and carved out an exception to the Fourth Amendments requirement of a warrant for searches and seizures. Unlike the Supreme Court, the FISA court hears from only one side in the case the government and its findings are almost never made public.
Note: For more on government secrecy, see the deeply revealing reports from reliable major media sources available here.
Leslie James Pickering noticed something odd in his mail last September: a handwritten card, apparently delivered by mistake, with instructions for postal workers to pay special attention to the letters and packages sent to his home. Show all mail to supv supervisor for copying prior to going out on the street, read the card. It included Mr. Pickerings name, address and the type of mail that needed to be monitored. The word confidential was highlighted in green. It was a bit of a shock to see it, said Mr. Pickering, who with his wife owns a small bookstore in Buffalo. More than a decade ago, he was a spokesman for the Earth Liberation Front, a radical environmental group labeled eco-terrorists by the Federal Bureau of Investigation. As the world focuses on the high-tech spying of the National Security Agency, the misplaced card offers a rare glimpse inside the seemingly low-tech but prevalent snooping of the United States Postal Service. Mr. Pickering was targeted by a longtime surveillance system called mail covers, a forerunner of a vastly more expansive effort, the Mail Isolation Control and Tracking program, in which Postal Service computers photograph the exterior of every piece of paper mail that is processed in the United States about 160 billion pieces last year. It is not known how long the government saves the images. The Mail Isolation Control and Tracking program was created after the anthrax attacks in late 2001. It enables the Postal Service to retrace the path of mail at the request of law enforcement. No one disputes that it is sweeping.
Note: The exposure by whistleblower Edward Snowden of the NSA's massive domestic and global spying operations seems to have triggered a series of other revelations about surveillance of the US population, like this report on the US Postal Service's photographing all mail. Hardly a week goes by without another major revelation, such as a new digital photo-ID database utilized by the FBI and police forces, and the development by US police of a national DNA database on all "potential suspects". Since very few US citizens are terrorists, what is the real purpose behind this total surveillance?
Russ Tice, a former intelligence analyst and Bush-era NSA whistleblower, claimed Wednesday that the intelligence community has ordered surveillance on a wide range of groups and individuals, including high-ranking military officials, lawmakers and diplomats. They went after and I know this because I had my hands literally on the paperwork for these sort of things they went after high-ranking military officers. They went after members of Congress, both Senate and the House, especially on the intelligence committees and on the armed services committees," [said] Tice. But they went after other ones, too. They went after lawyers and law firms. They went after judges. One of the judges is now sitting on the Supreme Court. Two are former FISA court judges. They went after State Department officials. They went after people in the executive service that were part of the White House. Then Tice dropped the bombshell about Obama. "In summer of 2004, one of the papers that I held in my hand was to wiretap a bunch of numbers associated with a 40-something-year-old wannabe senator for Illinois ... thats the president of the United States now. FBI whistleblower Sibel Edmonds and Tice agreed that such wide-ranging surveillance of officials could provide the intelligence agencies with unthinkable power to blackmail their opponents. I was worried that the intelligence community now has sway over what is going on, Tice said. Tice first blew the whistle on ... domestic spying across multiple agencies in 2005.
Note: Listen to Tice's shocking revelations in this interview. For more along these lines, see concise summaries of deeply revealing news articles about corruption in government and throughout intelligence agencies.
Lawyers and intelligence experts with direct knowledge of two intercepted terrorist plots that the Obama administration says confirm the value of the NSA's vast data-mining activities have questioned whether the surveillance sweeps played a significant role, if any, in foiling the attacks. The defence of the controversial data collection operations ... has been led by Dianne Feinstein, chairwoman of the Senate intelligence committee, and her equivalent in the House, Mike Rogers. The two politicians have attempted to justify the NSA's use of vast data sweeps such as Prism and Boundless Informant by pointing to the arrests and convictions of would-be New York subway bomber Najibullah Zazi in 2009 and David Headley, who is serving a 35-year prison sentence for his role in the 2008 Mumbai attacks. But court documents lodged in the US and UK, as well as interviews with involved parties, suggest that data-mining through Prism and other NSA programmes played a relatively minor role in the interception of the two plots. Conventional surveillance techniques, in both cases including old-fashioned tip-offs from intelligence services in Britain, appear to have initiated the investigations. The Headley case is a peculiar choice for the administration to highlight as an example of the virtues of data-mining. The fact that the Mumbai attacks occurred, with such devastating effect, in itself suggests that the NSA's secret programmes were limited in their value as he was captured only after the event. Headley ... had been an informant working for the Drug Enforcement Administration perhaps as recently as 2005. There are suggestions that he might have then worked in some capacity for the FBI or CIA.
Note: For deeply revealing reports from reliable major media sources on the realities of intelligence agency activity, click here.
In 1982, long before most Americans ever had to think about warrantless eavesdropping, the journalist James Bamford published The Puzzle Palace: A Report on N.S.A., Americas Most Secret Agency, the first book to be written about the National Security Agency. In the book, Bamford describes the agency as free of legal restrictions while wielding technological capabilities for eavesdropping beyond imagination. He concludes with an ominous warning: Like an ever-widening sinkhole, N.S.A.s surveillance technology will continue to expand, quietly pulling in more and more communications and gradually eliminating more and more privacy. Three decades later, this pronouncement feels uncomfortably prescient: we were warned. Incredibly enough, the Department of Justice, under Jimmy Carter, complied with Bamfords Freedom of Information Act requests, supplying him with secret documents related to the Church Committee, the Senate group that, in 1975, investigated American intelligence agencies for potential transgression of their mandates. That the government would hand over sensitive information to Bamford predictably infuriated the N.S.A.; Reagan Administration lawyers tried to bully Bamford into ceding his goods, threatening him with the Espionage Act, while the N.S.A. attempted to sequester the documents hed uncovered. But because he was a lawyer, Bamford knew that he had done nothing wrong.
Note: As a producer for ABC News, Bamford was also the one who obtained startling declassified documents showing that the top Pentagon generals signed off on plans in the early 1960s to blow up a US ship in the Havana harbor or incite violent terrorism in US cities and blame it on Cuba. Strangely, ABC's article "U.S. Military Wanted to Provoke War With Cuba" was the only media report on this incredibly revealing document release. For more along these lines, see concise summaries of revealing news articles on intelligence agency corruption and the disappearance of privacy.
The Guardian [has] released a classified court order requiring Verizon to turn over records of all domestic phone calls to the National Security Agency. The revelation has led to a renewed debate over the legality and policy merits of indiscriminate government surveillance of Americans. The court order, issued by the secret Foreign Intelligence Surveillance court, only sought metadata a fancy word for information like what numbers you called, what time you made the calls, and how long the calls were. The order does not seek the audio of calls. Of course, its possible the NSA has other programs collecting the contents of calls. In 2006 a whistleblower reported the existence of a secret, NSA-controlled room in an AT&T switching facility in San Francisco. So its possible the NSA is using rooms like that to listen to everyones phone calls. But all we know for sure is that the NSA has been requesting information about our phone calls. We only have proof of spying on Verizon customers, but its hard to imagine the NSA limiting its surveillance program to one company. There are probably similar orders in effect for AT&T and CenturyLink, the other major telephone companies. The order includes hints that the NSA is also collecting information from cellular customers. In addition to phone numbers and call times, the order seeks information about the specific cell phone tower the customer used to connect to the network during each call. Cellphones make calls using the closest tower. So if the NSA knows you made a call using a specific tower, they can safely assume you were near that tower at the time of the call.
Note: For graphs and lots more on the Prism program, see the Guardian article at this link. Technically, U.S. officials are not allowed to mine personal data from U.S. citizens. Yet if U.K. authorities mine data on U.S. citizens, they can share it freely with officials in the U.S. and vice versa. There is evidence that this happens quite frequently, thus circumventing privacy protections. For an excellent article which goes deep into this issue, click here.
The Justice Department secretly obtained two months of telephone records of reporters and editors for The Associated Press in what the news cooperative's top executive called a "massive and unprecedented intrusion" into how news organizations gather the news. The records obtained by the Justice Department listed outgoing calls for the work and personal phone numbers of individual reporters, for general AP office numbers in New York, Washington and Hartford, Conn., and for the main number for the AP in the House of Representatives press gallery. In all, the government seized the records for more than 20 separate telephone lines assigned to AP and its journalists in April and May of 2012. The government would not say why it sought the records. Officials have previously said in public testimony that the U.S. attorney in Washington is conducting a criminal investigation into who may have provided information contained in a May 7, 2012, AP story about a foiled terror plot. The story disclosed details of a CIA operation in Yemen that stopped an al-Qaida plot in the spring of 2012 to detonate a bomb on an airplane bound for the United States. Prosecutors have sought phone records from reporters before, but the seizure of records from such a wide array of AP offices, including general AP switchboards numbers and an office-wide shared fax line, is unusual.
Note: For deeply revealing reports from reliable major media sources on government corruption, click here.
The Obama administration is drawing up plans to give all U.S. spy agencies full access to a massive database that contains financial data on American citizens and others who bank in the country, according to a Treasury Department document. The proposed plan represents a major step by U.S. intelligence agencies to spot and track down [targeted persons] by bringing together financial databanks, criminal records and military intelligence. Financial institutions that operate in the United States are required by law to file reports of "suspicious customer activity," such as large money transfers or unusually structured bank accounts, to Treasury's Financial Crimes Enforcement Network (FinCEN). The Federal Bureau of Investigation already has full access to the database. However, intelligence agencies, such as the Central Intelligence Agency and the National Security Agency, currently have to make case-by-case requests for information to FinCEN. The Treasury plan would give spy agencies the ability to analyze more raw financial data than they have ever had before. Financial institutions file more than 15 million "suspicious activity reports" every year, according to Treasury. Banks, for instance, are required to report all personal cash transactions exceeding $10,000.
Note: For deeply revealing reports from reliable major media sources on the games intelligence agencies play, click here.
Are unmanned aircraft, known to have difficulty avoiding collisions, safe to use in America's crowded airspace? And would their widespread use for surveillance result in unconstitutional invasions of privacy? Experts say neither question has been answered satisfactorily. Yet the federal government is rushing to open America's skies to tens of thousands of the drones - pushed to do so by a law championed by manufacturers of the unmanned aircraft. The 60-member House of Representatives' "drone caucus" - officially, the House Unmanned Systems Caucus - has helped push that agenda. And over the last four years, caucus members have drawn nearly $8 million in drone-related campaign contributions. Domestic use of drones began with limited aerial patrols of the nation's borders by Customs and Border Patrol authorities. But the industry and its allies pushed for more, leading to provisions in the FAA Modernization and Reform Act, signed into law on Feb. 14 of this year. The law requires the FAA to fully integrate the unmanned aerial vehicles into national airspace by September 2015. The FAA has predicted that 30,000 drones could be flying in the United States in less than 20 years. House members from California, Texas, Virginia and New York on the bipartisan "drone caucus" received the lion's share of the funds channeled to lawmakers from dozens of firms that are members of the Association for Unmanned Vehicle Systems International.
Note: For deeply revealing reports from reliable major media sources on drone killings and other war crimes committed by the US in its wars of aggression in the Middle East, Asia and Africa, click here.
The Petraeus scandal is receiving intense media scrutiny. Several of the emerging revelations are genuinely valuable, particularly those involving the conduct of the FBI and the reach of the US surveillance state. The FBI investigation began when Jill Kelley - a Tampa socialite friendly with Petraeus (and apparently very friendly with Gen. John Allen, the four-star U.S. commander of the war in Afghanistan) - received a half-dozen or so anonymous emails that she found vaguely threatening. She then informed a friend of hers who was an FBI agent, and a major FBI investigation was then launched that set out to determine the identity of the anonymous emailer. What is most striking is how sweeping, probing and invasive the FBI's investigation then became, all without any evidence of any actual crime - or the need for any search warrant. The FBI traced all of [Paula] Broadwell's physical locations, learned of all the accounts she uses, ended up reading all of her emails, investigated the identity of her anonymous lover (who turned out to be Petraeus), and then possibly read his emails as well. They also discovered "alleged inappropriate communication" to Kelley from Gen. Allen, who is not only the top commander in Afghanistan but was also just nominated by President Obama to be the Commander of US European Command and Supreme Allied Commander Europe (a nomination now "on hold"). This is a surveillance state run amok. It also highlights how any remnants of internet anonymity have been all but obliterated by the union between the state and technology companies.
Note: For deeply revealing reports from reliable major media sources on government surveillance, click here.
Rented computers from seven different companies secretly took photographs of their users, US authorities have said. The companies used software made by US company Designerware which could track key strokes and other personal data. The software, called PC Rental Agent, captured people engaging in "intimate acts", including sex. It is believed that PC Rental Agent has been installed in approximately 420,000 computers worldwide. The Federal Trade Commission ruling concerned a feature in the software, called Detective Mode, which would typically become activated if the user was late in returning equipment, or failed to pay for use. Detective Mode would assist the rental store in locating the overdue computer in order to pursue its return. Part of the process involved a pop-up window designed to look like a software registration screen. It would request personal information such as email addresses and telephone numbers that could then be used to pursue the users for payment and/or the return of equipment. In addition, the FTC said the software had access to much more sensitive information, including: usernames and passwords for email accounts, social media websites, and financial institutions. Among the other data collected were social security numbers; medical records; private emails to doctors; bank and credit card statements. Webcam pictures of children, partially undressed individuals, and intimate activities at home were also found. In the FTC's formal complaint document, it said the software had captured "couples engaged in sexual activities".
Note: Do you think other companies or intelligence agencies might be conducting similar monitoring? For more on this, click here.
Last week, New York Mayor Michael Bloomberg joined NYPD Commissioner Ray Kelly to unveil a major new police surveillance infrastructure, developed by Microsoft. The Domain Awareness System links existing police databases with live video feeds, including cameras using vehicle license plate recognition software. No mention was made of whether the system plans to use or already uses facial recognition software. But, at present, there is no law to prevent US government and law enforcement agencies from building facial recognition databases. And we know from industry newsletters that the US military, law enforcement, and the department of homeland security are betting heavily on facial recognition technology. As PC World notes, Facebook itself is a market leader in the technology but military and security agencies are close behind. According to Homeland Security Newswire, billions of dollars are being invested in the development and manufacture of various biometric technologies capable of detecting and identifying anyone, anywhere in the world via iris-scanning systems, already in use; foot-scanning technology (really); voice pattern ID software, and so on. What is very obvious is that this technology will not be applied merely to people under arrest, or to people under surveillance in accordance with the fourth amendment. No, the "targets" here [include] everyone. In the name of "national security", the capacity is being built to identify, track and document any citizen constantly and continuously.
Note: For deeply revealing reports from reliable major media sources on civil liberties, click here.
When two senators warned that the Patriot Act is being interpreted in a secret way that would alarm Americans if they knew the details, civil liberties activists could only speculate about what they meant. The activists' fear: that the government is using the anti-terrorism law to collect vast troves of personal information, including cellphone records, on Americans who have no link to terrorism. Sens. Ron Wyden of Oregon and Mark Udall of Colorado, both Democrats, proclaimed that the Patriot Act's surveillance powers are being used far more expansively than most Americans realize. "Today the American people do not know how their government interprets the language of the Patriot Act," Wyden said. "Someday they are going to find out, and a lot of them are going to be stunned. Some of them will undoubtedly ask their senators: 'Did you know what this law actually did? Why didn't you know? Wasn't it your job to know, before you voted on it?'" The warnings by two lawmakers with access to secret information underscore the extent to which government surveillance is shielded from view, in an age when nearly every American leaves a digital trail through the Internet and mobile devices. A clue about Wyden's concerns may be found in a separate bill he is proposing, to forbid the government from tracking, without a court order, the location of Americans through the GPS signals given out by their cellphones.
Note: For key reports from major media sources on government surveillance and other threats to privacy and civil liberties, click here and here.
Weeks after generating an uproar for the aggressive screening of a six-year-old child in New Orleans, the TSA is again facing criticism for an enhanced pat-down. Former Miss USA Susie Castillo says she was "molested" by a TSA screener at Dallas/Fort Worth International Airport after declining to go through a body scanner due to radiation concerns. According to a detailed account from the Dallas Morning News, Castillo wrote "My private area was grazed four times!" on a complaint card after the screening. Castillo immediately shot a tearful video recounting the episode more explicitly and posted it on YouTube. The Boston Herald quotes from the video: "That's why I'm crying, that's why I'm so upset. They're making me choose to either get molested, because that's what I feel like, or go through this machine that's completely unhealthy and dangerous." TSA spokesman Luis Casanova defended the screening procedure. "Everything [the screener] did was according to protocol," Casanova said.
Note: For key articles on increasing reductions of civil liberties by governments, click here.
Security researchers have discovered that Apple's iPhone keeps track of where you go and saves every detail of it to a secret file on the device which is then copied to the owner's computer when the two are synchronised. The file contains the latitude and longitude of the phone's recorded coordinates along with a timestamp, meaning that anyone who stole the phone or the computer could discover details about the owner's movements using a simple program. For some phones, there could be almost a year's worth of data stored, as the recording of data seems to have started with Apple's iOS 4 update to the phone's operating system, released in June 2010. "Apple has made it possible for almost anybody a jealous spouse, a private detective with access to your phone or computer to get detailed information about where you've been," said Pete Warden, one of the researchers. Only the iPhone records the user's location in this way, say Warden and Alasdair Allan, the data scientists who discovered the file and are presenting their findings at the Where 2.0 conference in San Francisco on [April 20]. "Alasdair has looked for similar tracking code in [Google's] Android phones and couldn't find any," said Warden.
Note: For key reports from reliable sources on threats to privacy, click here.
The US military is developing software that will let it secretly manipulate social media sites by using fake online personas to influence internet conversations and spread pro-American propaganda. A Californian corporation has been awarded a contract with United States Central Command (Centcom), which oversees US armed operations in the Middle East and Central Asia, to develop what is described as an "online persona management service" that will allow one US serviceman or woman to control up to 10 separate identities based all over the world. Critics are likely to complain that it will allow the US military to create a false consensus in online conversations, crowd out unwelcome opinions and smother commentaries or reports that do not correspond with its own objectives. The discovery that the US military is developing false online personalities known to users of social media as "sock puppets" could also encourage other governments, private companies and non-government organisations to do the same. Once developed, the software could allow US service personnel, working around the clock in one location, to respond to emerging online conversations with any number of co-ordinated messages, blogposts, chatroom posts and other interventions.
Note: The Pentagon claims that the "fake persona" software will not be used on social networks in the United States, because that would break laws against using propaganda on US citizens. How much credence should be given to this assurance?
Leaked U.S. diplomatic cables appear to show that the United States has been snooping on NATO's top official using secret sources on his own staff. Confidential cables from the U.S. mission to NATO released [on February 11] by WikiLeaks, ... said American diplomats received information on the private conversations of Secretary-General Anders Fogh Rasmussen from "a member of the NATO international staff." Instead of the staffer's name, the phrase "strictly protect" was inserted in a cable dated Sept. 10, 2009. The cable dealt with Fogh Rasmussen's proposal to improve ties with Russia by establishing contacts with the Collective Security Treaty Organization, a Russia-dominated security alliance. The cable was signed off by U.S. ambassador Ivo Daalder. There has been no known [previous] case in the past of a nation spying on the secretary-general.
Nine years after the terrorist attacks of 2001, the United States is assembling a vast domestic intelligence apparatus to collect information about Americans, using the FBI, local police, state homeland security offices and military criminal investigators. The system, by far the largest and most technologically sophisticated in the nation's history, collects, stores and analyzes information about thousands of U.S. citizens and residents, many of whom have not been accused of any wrongdoing. The months-long investigation [by The Washington Post], based on nearly 100 interviews and 1,000 documents, found that: * Technologies and techniques honed for use on the battlefields of Iraq and Afghanistan have migrated into the hands of law enforcement agencies in America. * The FBI is building a database with the names and certain personal information, such as employment history, of thousands of U.S. citizens and residents whom a local police officer or a fellow citizen believed to be acting suspiciously. * Law enforcement agencies have hired as trainers self-described experts whose extremist views on Islam and terrorism are considered inaccurate and counterproductive by the FBI and U.S. intelligence agencies. * The Department of Homeland Security sends its state and local partners intelligence reports with little meaningful guidance, and state reports have sometimes inappropriately reported on lawful meetings.
Note: This report is part of a series, "Top Secret America," by The Washington Post. For more, click here.
Novartis AG plans to seek regulatory approval within 18 months for a pioneering tablet containing an embedded microchip, bringing the concept of "smart-pill" technology a step closer. The initial program will use one of the Swiss firm's established drugs taken by transplant patients to avoid organ rejection. But Trevor Mundel, global head of development, believes the concept can be applied to many other pills. Novartis agreed in January to spend $24 million to secure access to chip-in-a-pill technology developed by privately owned Proteus Biomedical of Redwood City, California, putting it ahead of rivals. The biotech start-up's ingestible chips are activated by stomach acid and send information to a small patch worn on the patient's skin, which can transmit data to a smartphone or send it over the Internet to a doctor. Because the tiny chips are added to existing drugs, Novartis does not expect to have to conduct full-scale clinical trials to prove the new products work. Instead, it aims to do so-called bioequivalence tests to show they are the same as the original. A bigger issue may be what checks should be put in place to protect patients' personal medical data as it is transmitted from inside their bodies by wireless and Bluetooth.
Note: It's interesting that Fox News was the only major media to pick up this revealing Reuters story. This article seriously underplays the privacy concerns raised by this new corporate strategy. For more on this, click here. For many key reports on corporate and governmental threats to privacy, click here. For more on the dangers of microchips from reliable sources, click here.
That photo of the Rev. Dr. Martin Luther King, Jr. riding one of the first desegregated buses in Montgomery, Ala.? He took it. The well-known image of black sanitation workers carrying I Am a Man signs in Memphis? His. He was there in Room 306 of the Lorraine Hotel, Dr. Kings room, on the night he was assassinated. But now an unsettling asterisk must be added to the legacy of Ernest C. Withers, one of the most celebrated photographers of the civil rights era: He was a paid F.B.I. informer. On [September 12], The Commercial Appeal in Memphis published the results of a two-year investigation that showed Mr. Withers, who died in 2007 at age 85, had collaborated closely with two F.B.I. agents in the 1960s to keep tabs on the civil rights movement. From at least 1968 to 1970, Mr. Withers, who was black, provided photographs, biographical information and scheduling details to two F.B.I. agents in the bureaus Memphis domestic surveillance program, Howell Lowe and William H. Lawrence, according to numerous reports summarizing their meetings. The reports were obtained by the newspaper under the Freedom of Information Act and posted on its Web site. While he was growing close to top civil rights leaders, Mr. Withers was also meeting regularly with the F.B.I. agents, disclosing details about plans for marches and political beliefs of the leaders, even personal information like the leaders car tag numbers.
Note: For a fascinating CNN interview with civil rights leader and former Atlanta mayor Andrew Young on this issue, click here. For key reports from reliable sources raising unanswered questions about the assassination of Martin Luther King and other major US political leaders, click here.
All dogs are to be compulsorily microchipped so that their owners can be more easily traced under a crackdown on dangerous dogs. Under the scheme a microchip the size of a grain of rice is injected under the skin of the dog between its shoulder blades. The chip contains a unique code number, the dog's name, age, breed and health as well as the owner's name, address and phone number. When the chip is "read" by a handheld scanner the code number is revealed and the details can be checked on a national database. The measures will be set out by the home secretary, Alan Johnson, who will point to rising public concern that "status dogs" are being used by some irresponsible owners to intimidate communities or as a weapon by gangs. If the scheme were made compulsory owners would face a fine for failing to microchip their dogs.
Note: Once all dogs are required to be microchipped, what will come next? To be informed of some disturbing plans to microchip all of us, click here. For lots more on microchipping from reliable sources, click here.
Researchers are already using brain-computer interfaces to aid the disabled, treat diseases like Parkinson's and Alzheimer's, and provide therapy for depression and post-traumatic stress disorder. Work is under way on devices that may eventually let you communicate with friends telepathically, give you superhuman hearing and vision or even let you download data directly into your brain, a la "The Matrix." Researchers are practically giddy over the prospects. "We don't know what the limits are yet," says Melody Moore Jackson, director of Georgia Tech University's BrainLab. At the root of all this technology is the 3-pound generator we all carry in our head. It produces electricity at the microvolt level. But the signals are strong enough to move robots, wheelchairs and prosthetic limbs -- with the help of an external processor. One of the more controversial uses under development is telepathy. It would require at least two people to be implanted with electrodes that send and receive signals. DARPA, the Pentagon's technology research division, is currently working on an initiative called "Silent Talk," which would let soldiers on secret missions communicate with their thoughts alone. This stealth component is attractive, but naysayers fear that such soldiers could become manipulated for evil means.
Note: Remember that secret military research such as that undertaken by DARPA is often years ahead of capabilities publicly acknowledged.
On a remote edge of Utah's dry and arid high desert ... hard-hatted construction workers with top-secret clearances are preparing to build [a] mammoth $2 billion structure. It's being built by the ultra-secret National Security Agency ... to house trillions of phone calls, e-mail messages, and [electronic data trails of all kinds]. The NSA is also completing work on another data archive, this one in San Antonio, Texas, which will be nearly the size of the Alamodome. Just how much information will be stored in these windowless cybertemples? A recent report prepared by the MITRE Corporation, a Pentagon think tank, [states] "Sensor data volume could potentially increase to the level of Yottabytes [10-to-the-24th-power bytes] by 2015." Once vacuumed up and stored in these near-infinite "libraries," the data are then analyzed by powerful infoweapons, supercomputers running complex algorithmic programs, to determine who among us may be or may one day become a terrorist. Emerging [after 9/11] as the most powerful chief the spy world has ever known was the director of the NSA. He is in charge of an organization three times the size of the CIA and empowered in 2008 by Congress to spy on Americans to an unprecedented degree. These new centers in Utah, Texas, and possibly elsewhere will likely become the centralized repositories for the data intercepted by the NSA in America's version of the "big brother database."
Note: James Bamford, the author of this review of a new book on the history of the NSA, has himself written three important books on the agency. For many revealing reports from reliable sources on the developing capacity by government and corporate surveillance to construct a "Big Brother" states, click here.
The Justice Department has indicated that the Obama administration is in support of renewing [three] controversial sections of the USA Patriot Act that expire later this year. The provisions that will expire in December include Section 206, that allows "roving" wiretaps so FBI agents can tap multiple phones or computers (with court authorization) that a specific person (target) may use. Another expiring provision, Section 215, is the so-called "library provision," which allows investigators to obtain [library, medical, business, banking and other] records with approval from the Foreign Intelligence Surveillance Court. And the final provision which was nicknamed the "Lone Wolf" authorization, allows intelligence gathering of people not suspected of being part of a foreign government or known terrorist organization. Critics of the Patriot Act protested loudly that the FBI could obtain individuals' library records under the legislation. [But] section 215 is much more expansive than reviewing a suspected terrorist's summer reading list. [It] allows the FBI to obtain any business record, "any tangible things," like credit card and bank statements and also allows access to medical and mental health records. The provision has been used to obtain communication and subscriber information to help set up surveillance and monitoring of computers and telephones.
Note: The American Library Association, the national organization of professional librarians, was the first and strongest defender of civil liberties after the passage of the PATRIOT Act. For a discussion of the concerns of professional librarians over this decision by the Obama administration, click here.
The National Security Agency has been campaigning to lead the governments rapidly growing cybersecurity programs, raising privacy and civil liberties concerns among some officials who fear that the move could give the spy agency too much control over government computer networks. The security agencys interest in taking over the dominant role has met resistance, including the resignation of the Homeland Security Department official who was until last month in charge of coordinating cybersecurity efforts throughout the government. Rod Beckstrom, who resigned in March as director of the National Cyber Security Center at the Homeland Security Department, said ... that he feared that the N.S.A.s push for a greater role in guarding the governments computer systems could give it the power to collect and analyze every e-mail message, text message and Google search conducted by every employee in every federal agency. Mr. Beckstrom said he believed that an intelligence service that is supposed to focus on foreign targets should not be given so much control over the flow of information within the United States government. To detect threats against the computer infrastructure including hackers, viruses and intrusions by foreign agents and terrorists cybersecurity guardians must have virtually unlimited access to networks. Mr. Beckstrom argues that those responsibilities should be divided among agencies. I have very serious concerns about the concentration of too much power in one agency, he said. Power over information is so important, and it is so difficult to monitor, that we need to have checks and balances.
Note: For further disturbing reports from reliable sources on government efforts to establish total surveillance systems, click here.
The National Security Agency (NSA) is developing a tool that George Orwell's Thought Police might have found useful: an artificial intelligence system designed to gain insight into what people are thinking. The device will be able to respond almost instantaneously to complex questions posed by intelligence analysts. As more and more data is collectedthrough phone calls, credit card receipts, social networks like Facebook and MySpace, GPS tracks, cell phone geolocation, Internet searches, Amazon book purchases, even E-Z Pass toll records - it may one day be possible to know not just where people are and what they are doing, but what and how they think. The system is so potentially intrusive that at least one researcher has quit, citing concerns over the dangers in placing such a powerful weapon in the hands of a top-secret agency with little accountability. Known as Aquaint, which stands for "Advanced QUestion Answering for INTelligence," the project was run for many years by John Prange, an NSA scientist at the Advanced Research and Development Activity. A supersmart search engine, capable of answering complex questions ... would be very useful for the public. But that same capability in the hands of an agency like the NSA - absolutely secret, often above the law, resistant to oversight, and with access to petabytes of private information about Americans - could be a privacy and civil liberties nightmare. "We must not forget that the ultimate goal is to transfer research results into operational use," said ... Prange.
Note: Watch a highly revealing PBS Nova documentary providing virtual proof that the NSA could have stopped 9/11 but chose not to. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
The Justice Department's former top criminal prosecutor says the U.S. government's terror watch list likely has caused thousands of innocent Americans to be questioned, searched or otherwise hassled. Former Assistant Attorney General Jim Robinson would know: he is one of them. Robinson joined [with] the American Civil Liberties Union on Monday to urge fixing the list that's supposed to identify suspected terrorists. "It's a pain in the neck, and significantly interferes with my travel arrangements," said Robinson, the head of the Justice Department's criminal division during the Clinton administration. He believes his name matches that of someone who was put on the list in early 2005, and is routinely delayed while flying despite having his own government top-secret security clearances renewed last year. He [said] "I expect my story is similar to hundreds of thousands of people who are on this list who find themselves inconvenienced." [The watch list] was created after the Sept. 11, 2001 attacks to consolidate 12 existing lists. Audits of the watch list over the last several years ... have concluded that it has mistakenly flagged innocent people whose names are similar to those on it. More than 30,000 airline passengers had asked the Homeland Security Department to clear their names from the list as of October 2006. The ACLU predicted the watch list would include 1 million names as early as Monday. The civil liberties group reached that number by citing the 700,000 records on the watch list as of last September and adding 20,000 names each month, as forecast by the Justice Department's inspector general.
Note: For many disturbing reports on threats to civil liberties, click here.
Nearly 40 years ago, the FBI was roundly criticized for investigating Americans without evidence [that] they had broken any laws. Now, critics fear the FBI may be gearing up to do it again. Tentative Justice Department guidelines, to be released later this summer, would let agents investigate people whose backgrounds -- and potentially their race or ethnicity -- match the traits of terrorists. Such profiling ... echoes the FBI's now-defunct COINTELPRO, an operation under Director J. Edgar Hoover in the 1950s and 1960s to monitor and disrupt groups with communist and socialist ties. Before it was shut down in 1971, the domestic spying operation -- formally known as Counterintelligence Programs -- had expanded to include civil rights groups, anti-war activists, ... state legislators and journalists. Among the FBI's targets were Martin Luther King Jr., Malcolm X, and John Lennon, along with members of black [political] groups ... and student protesters. The new proposal to allow investigations of Americans with no evidence of wrongdoing is "COINTELPRO for the 21st century," said Barry Steinhardt of the American Civil Liberties Union. "But this is much more insidious because it could involve more people. In the days of COINTELPRO, they were watching only a few people. Now they could be watching everyone."
Note: For many disturbing reports on threats to civil liberties, click here.
The FBI is embarking on a $1 billion effort to build the world's largest computer database of peoples' physical characteristics, a project that would give the government unprecedented abilities to identify individuals in the United States and abroad. Digital images of faces, fingerprints and palm patterns are already flowing into FBI systems. Next month, the FBI intends to award a 10-year contract that would significantly expand the amount and kinds of biometric information it receives. And in the coming years, law enforcement authorities around the world will be able to rely on iris patterns, face-shape data, scars and perhaps even the unique ways people walk and talk, to ... identify [people]. The increasing use of biometrics for identification is raising questions about the ability of Americans to avoid unwanted scrutiny. It is drawing criticism from those who worry that people's bodies will become de facto national identification cards. "It's going to be an essential component of tracking," said Barry Steinhardt, director of the Technology and Liberty Project of the American Civil Liberties Union. "It's enabling the Always On Surveillance Society." The FBI's biometric database ... communicates with the Terrorist Screening Center's database of suspects and the National Crime Information Center database, which is the FBI's master criminal database of felons, fugitives and terrorism suspects. At the West Virginia University Center for Identification Technology Research (CITeR) ... researchers are working on capturing images of people's irises at distances of up to 15 feet, and of faces from as far away as 200 yards. Soon, those researchers will do biometric research for the FBI. Covert iris- and face-image capture is several years away, but it is of great interest to government agencies.
Note: For many important major-media reports on threats to privacy, click here.
Federal agents do not need a search warrant to monitor a suspect's computer use and determine the e-mail addresses and Web pages the suspect is contacting, a federal appeals court ruled Friday. In a drug case from San Diego County, the Ninth U.S. Circuit Court of Appeals in San Francisco likened computer surveillance to the "pen register" devices that officers use to pinpoint the phone numbers a suspect dials, without listening to the phone calls themselves. In Friday's ruling, the court said computer users should know that they lose privacy protections with e-mail and Web site addresses when they are communicated to the company whose equipment carries the messages. The search is no more intrusive than officers' examination of a list of phone numbers or the outside of a mailed package, neither of which requires a warrant, Judge Raymond Fisher said in the 3-0 ruling. Defense lawyer Michael Crowley disagreed. His client, Dennis Alba, was sentenced to 30 years in prison after being convicted of operating a laboratory in Escondido that manufactured the drug ecstasy. Some of the evidence against Alba came from agents' tracking of his computer use. The court upheld his conviction and sentence. Expert evidence in Alba's case showed that the Web addresses obtained by federal agents included page numbers that allowed the agents to determine what someone read online, Crowley said. The ruling "further erodes our privacy," the attorney said. "The great political marketplace of ideas is the Internet, and the government has unbridled access to it."
Note: So now every email you send and read can be monitored legally. Why didn't this make news headlines?
For at least a year before the 2004 Republican National Convention, teams of undercover New York City police officers traveled to cities across the country, Canada and Europe to conduct covert observations of people who planned to protest at the convention, according to police records and interviews. From Albuquerque to Montreal, San Francisco to Miami, undercover New York police officers attended meetings of political groups, posing as sympathizers or fellow activists. They made friends, shared meals, swapped e-mail messages and then filed daily reports with the departments Intelligence Division. In hundreds of reports stamped N.Y.P.D. Secret, the Intelligence Division chronicled the views and plans of people who had no apparent intention of breaking the law. These included members of street theater companies, church groups and antiwar organizations. Three New York City elected officials were cited in the reports. In at least some cases, intelligence on what appeared to be lawful activity was shared with police departments in other cities. In addition to sharing information with other police departments, New York undercover officers were active themselves in at least 15 places outside New York including California, Connecticut, Florida, Georgia, Illinois, Massachusetts, Michigan, Montreal, New Hampshire, New Mexico, Oregon, Tennessee, Texas and Washington, D.C. and in Europe. To date, as the boundaries of the departments expanded powers continue to be debated, police officials have provided only glimpses of its intelligence-gathering.
The Justice Department's inspector general revealed on March 9 that the FBI has been systematically abusing one of the most controversial provisions of the USA Patriot Act: the expanded power to issue "national security letters." It no doubt surprised most Americans to learn that between 2003 and 2005 the FBI issued more than 140,000 specific demands under this provision. It did not, however, come as any surprise to me. Three years ago, I received a national security letter (NSL) in my capacity as the president of a small Internet access and consulting business. The letter ordered me to provide sensitive information about one of my clients. There was no indication that a judge had reviewed or approved the letter, and it turned out that none had. The letter came with a gag provision that prohibited me from telling anyone, including my client, that the FBI was seeking this information. Based on the context of the demand -- a context that the FBI still won't let me discuss publicly -- I suspected that the FBI was abusing its power. Living under the gag order has been stressful and surreal. Under the threat of criminal prosecution, I must hide all aspects of my involvement in the case -- including the mere fact that I received an NSL -- from my colleagues, my family and my friends. When I meet with my attorneys I cannot tell my girlfriend where I am going or where I have been. I hide any papers related to the case in a place where she will not look. When clients and friends ask me whether I am the one challenging the constitutionality of the NSL statute, I have no choice but to look them in the eye and lie. At some point -- a point we passed long ago -- the secrecy itself becomes a threat to our democracy.
Under a secret Bush administration program initiated weeks after the Sept. 11 attacks, counterterrorism officials have gained access to financial records from a vast international database and examined banking transactions involving thousands of Americans and others in the United States. The program, run out of the Central Intelligence Agency and overseen by the Treasury Department ... is a significant departure from typical practice in how the government acquires Americans' financial records. Treasury officials did not seek individual court-approved warrants or subpoenas to examine specific transactions, instead relying on broad administrative subpoenas for millions of records. That access to large amounts of confidential data was highly unusual, several officials said, and stirred concerns inside the administration about legal and privacy issues. "The capability here is awesome or, depending on where you're sitting, troubling," said one former senior counterterrorism official who considers the program valuable. While tight controls are in place, the official added, "the potential for abuse is enormous." The program is separate from the National Security Agency's efforts to eavesdrop without warrants and collect domestic phone records, operations that have provoked fierce public debate and spurred lawsuits against the government and telecommunications companies.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
The military, technological, security and political classes in this country appear united in their desire to make robot dogs part of our future, and we should all be worried. On 1 February ... the Department of Homeland Security (DHS) issued a press release titled “Robot Dogs Take Another Step Towards Deployment at the Border”. DHS dressed up their statement with the kind of adorable language made to warm the hearts of dog lovers everywhere. A picture of the “four-legged ground drone” accompanied the release. These particular robot dogs are made by Ghost Robotics, which claims that its 100lb machine was “bred” to scale “all types of natural terrain including sand, rocks and hills, as well as human-built environments, like stairs”. Each robot dog is outfitted with a bevy of sensors and able to transmit real-time video and information feeds. A testing and evaluation program is under way in El Paso, Texas. As the Electronic Frontier Foundation notes, “people who live along the border are some of the most heavily surveilled people in the United States. A massive amalgamation of federal, state and local law enforcement and national security agencies are flying drones, putting up cameras and just generally attempting to negate civil liberties – capturing the general goings-on of people who live and work in proximity to the border.” Then there’s the question of lethal force. These specific ground drones may not be armed, but Ghost Robotics is already infamous for the combination of robot dog and robot rifle.
Note: Singapore used robot dogs to enforce pandemic distancing measures. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance from reliable major media sources.
Last year, the Republican chairman of the US House Permanent Select Committee on Intelligence (HPSCI) presented an image of Americans protesting the war in Gaza while implying possible ties between the protesters and Hamas, an allegation that was used to illustrate why surveillance reforms may prove detrimental to national security. In December, as many as 200 Republican staffers gathered behind closed doors to hear a presentation ... aimed at shoring up support for a US surveillance program known as Section 702. Section 702 authorizes the government to surveil foreigners located physically overseas ... but not Americans or individuals on US soil. While eavesdropping on foreigners is permitted, doing so for the explicit purpose of gaining access to an American’s communications—a practice commonly referred to as “reverse targeting”—is strictly forbidden. “Yes, it’s true, you cannot ‘target’ protesters under 702,” one aide, a legislative director for a Republican lawmaker, says. “But that doesn’t mean the FBI doesn't still have the power to access those emails or listen to their calls if it wants.” Between 2020 and early 2021, the FBI conducted “tens of thousands” of queries related to “civil unrest” in the United States. “Political protest is literally how America was founded. It’s in our DNA,” says Jason Pye, senior policy analyst at the nonprofit FreedomWorks. “Whether you agree with these protesters or not is irrelevant.”
Note: The FBI has a long history of spying on political activists. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
During a Senate briefing last week, a federal counterterrorism official cited the October 7 Hamas attack while urging Congress to reauthorize a sprawling and controversial surveillance program repeatedly used to spy on U.S. citizens on U.S. soil. “As evidenced by the events of the past month, the terrorist threat landscape is highly dynamic and our country must preserve [counterterrorism] fundamentals to ensure constant vigilance,” said Director of the National Counterterrorism Center Christine Abizaid. She pointed to Section 702 of the Foreign Intelligence Surveillance Act, which enables the U.S. government to gather vast amounts of intelligence — including about U.S. citizens ... without first seeking a warrant. Section 702 “provides key indications and warning on terrorist plans and ... gives us strategic insight into foreign terrorists and their networks overseas,” Abizaid said. “I respectfully urge Congress to reauthorize this vital authority.” The controversial program is set to expire at the end of the year, and lawmakers sympathetic to the intelligence community are scrambling to protect it. Sean Vitka ... at the civil liberties group Demand Progress [said] that now is the time to enact lasting and dramatic oversight of the 702 authority. “The government has completely failed to demonstrate that any of the privacy protections reformers have called for would impair national security ... so now we’re seeing people grasping at straws trying to turn everything into an excuse for reauthorization,” Vitka said.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
An advisory board to President Biden has recommended limiting the F.B.I.'s ability to use a controversial warrantless surveillance program to hunt for information about Americans, even as it urged lawmakers to renew the law that authorizes it. The panel, known as the President's Intelligence Advisory Board, suggested barring the bureau from searching a database of intercepted information when looking for evidence about Americans in criminal investigations that do not involve foreign intelligence. The board ... delivered the recommendation in a declassified 39-page report. It came as Congress was debating whether to extend the law authorizing the program, known as Section 702. Under Section 702, the government can collect – from American companies like Google and AT&T and without a warrant – the communications of targeted foreigners abroad, even when they are talking to or about Americans. The notion that Section 702 creates a backdoor to the Fourth Amendment by allowing the F.B.I. to read private communications to or from an American without a warrant in ordinary criminal contexts has raised particular alarm. But the board rejected as unjustified the more sweeping reform proposal: to require the government to obtain a court warrant before using Americans' identifiers to search the repository. Requiring a court order before doing so, the board said, would prevent intelligence agencies from discovering threats to the country in a timely manner.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
FBI officials repeatedly violated their own standards when they searched a vast repository of foreign intelligence for information related to the January 6 insurrection and racial justice protests in 2020, according court order released Friday. The violations were detailed in a secret court order issued last year by the foreign intelligence surveillance (Fisa) court, which has legal oversight of the US government’s spy powers. At issue are improper queries of foreign intelligence information collected under section 702 of the Foreign Intelligence Surveillance Act, which enables the government to gather the communications of targeted foreigners outside the US. That program, which is set to expire at the end of the year, creates a database of intelligence that US agencies can search. FBI searches must have a foreign intelligence purpose or be aimed at finding evidence of a crime. But congressional critics of the program have long raised alarm about what they say are unjustified searches of the database for information about Americans, along with more general concerns about surveillance abuses. In repeated episodes disclosed on Friday, the FBI’s own standards were not followed. The April 2022 order, for instances, details how the FBI queried the section 702 repository using the name of someone who was believed to have been at the Capitol during the January 6 riot. Officials obtained the information despite it not having any “analytical, investigative or evidentiary purpose”, the order said.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
The recent launch of a new mobile phone service introduced significant new privacy protections into the mobile phone system. This exciting new approach highlights the failure of the existing mobile phone infrastructure to protect privacy, and points the way forward for a wide variety of technologies. Today’s cellphones are generally a privacy disaster. Partly that’s the result of the two companies that control the operating system software on the vast majority of the world’s pocket computers. In order for your carrier to route calls and data to your phone, the network needs to constantly know which cell tower your phone is near. And when you make a call or use data, the provider can see where that traffic is going. Cell carriers track and store this accidental byproduct of the technology in order to record people’s location history and network activity for marketing purposes and, in certain circumstances, for sharing with law enforcement. The new phone service, called Pretty Good Phone Privacy (PGPP), uses encryption techniques to deliberately blind itself so that it can’t know that the user of a mobile device is you, or what data you are sending from that phone. You connect to the PGPP service for payment, and that’s all. With PGPP’s approach, the carrier simply does not have the data to turn over to anyone. It cannot be sold, leaked, or hacked, let alone offered to overreaching law enforcement agencies. Verizon, T-Mobile, AT&T, and their smaller competitors could be offering such a privacy-protecting service, but don’t want to.
Note: Explore a treasure trove of concise summaries of incredibly inspiring news articles which will inspire you to make a difference.
An offshore company that is trusted by the major web browsers and other tech companies to vouch for the legitimacy of websites has connections to contractors for U.S. intelligence agencies and law enforcement, according to security researchers, documents and interviews. Google’s Chrome, Apple’s Safari, nonprofit Firefox and others allow the company, TrustCor Systems, to act as what’s known as a root certificate authority, a powerful spot in the internet’s infrastructure that guarantees websites are not fake, guiding users to them seamlessly. The company’s Panamanian registration records show that it has the identical slate of officers, agents and partners as a spyware maker identified this year as an affiliate of Arizona-based Packet Forensics, which ... has sold communication interception services to U.S. government agencies for more than a decade. TrustCor’s products include an email service that claims to be end-to-end encrypted, though experts consulted by The Washington Post said they found evidence to undermine that claim. A test version of the email service also included spyware developed by a Panamanian company related to Packet Forensics. A person familiar with Packet Forensics’ work confirmed that it had used TrustCor’s certificate process and its email service, MsgSafe, to intercept communications and help the U.S. government catch suspected terrorists. The physical address in Toronto given in [TrustCor's] auditor’s report, 371 Front St. West, houses a UPS Store mail drop.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
I participated in an online forum called US CBDC—A Disaster in the making? We had a very productive discussion about the policy aspect of central bank digital currencies (CBDCs). I believe that the Fed should not launch a CBDC. Ever. And I think that Congress should amend the Federal Reserve Act, just to be on the safe side. I want to distinguish between a wholesale CBDC and retail CBDC. With a wholesale CBDC, banks can electronically transact with each other using a liability of the central bank. That is essentially what banks do now. But retail CBDCs are another animal altogether. Retail CBDCs allow members of the general public to make electronic payments of all kinds with a liability of the central bank. This feature–making electronic transactions using a liability of the Federal Reserve–is central to why Congress should make sure that the Fed never issues a retail CBDC. The problem is that the federal government, not privately owned commercial banks, would be responsible for issuing deposits. And while this fact might seem like a feature instead of bug, it’s a major problem for anything that resembles a free society. The problem is that there is no limit to the level of control that the government could exert over people if money is purely electronic and provided directly by the government. A CBDC would give federal officials full control over the money going into–and coming out of–every person’s account. This level of government control is not compatible with economic or political freedom.
Note: The above was written by Norbert Michel, Vice President and Director of the Cato Institute's Center for Monetary and Financial Alternatives. For more along these lines, see concise summaries of deeply revealing news articles on financial system corruption from reliable major media sources.
The digital Covid vaccination certification, or “passport,” is a mobile app that instantaneously affirms the vaccinated status, Covid test results, birth date, gender, and/or other identifiers of its holder. The information is usually mosaicked in a QR code, read by a proprietary scanner, and linked to a government registry. Led by New York, California, and Louisiana, as many as 30 states are rolling them out. The Biden administration announced last spring that it would wrangle them under national standards but so far it hasn’t. Internationally, the EU and a growing number of countries are adopting them, from repressive regimes like Bahrain to democracies like Denmark. Twenty U.S. states have banned the passes, and hashtags like #NoVaccinePassports are proliferating on both sides of the Atlantic. “Spoiler alert,” tweeted British DJ ... Lange. “They are not planning on removing vax passports once introduced. This is just the first step to get you conditioned to accepting government restrictions in your daily life via your mobile phone. This digital ID is going to expand to all aspects of your life.” Evidence supports the detractors’ suspicions. Every government introducing a vaccine certification vows that their use is voluntary and no personal information will be held beyond its necessity. But governments are far from unanimous even on such basics as ... how long and by whom our intimate information will be held, owned, or overseen. New York, for one, is not expecting to mothball the technology when Covid wanes.
Note: For more along these lines, see concise summaries of deeply revealing news articles on coronavirus vaccines and the disappearance of privacy from reliable major media sources.
The federal government has ramped up security and police-related spending in response to the coronavirus pandemic, including issuing contracts for riot gear, disclosures show. The purchase orders include requests for disposable cuffs, gas masks, ballistic helmets, and riot gloves, along with law enforcement protective equipment for federal police assigned to protect Veterans Affairs facilities. The orders were expedited under a special authorization in response to Covid-19 outbreak. Between 2005 and 2014, VA police departments acquired millions of dollars worth of body armor, chemical agents, night vision equipment, and other weapons and tactical gear, The Intercept reported last year. But an Inspector General report in December 2018 found there was little oversight. The CARES Act, the $2.2 trillion stimulus legislation passed in late March, also authorized $850 million for the Coronavirus Emergency Supplemental Funding program, a federal grant program to prepare law enforcement, correctional officers, and police for the crisis. The funds have been dispensed to local governments to pay for overtime costs, purchase protective supplies, and defray expenses related to emergency policing. The grants may also be used for the purchase of unmanned aerial aircraft and video security cameras for law enforcement. Motorola Solutions, a major supplier of police technology, has encouraged local governments to use the new money to buy a range of command center software and video analytics systems.
Note: For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus and the disappearance of privacy from reliable major media sources.
India has just 144 police officers for every 100,000 citizens. In recent years, authorities have turned to facial recognition technology to make up for the shortfall. India's government now ... wants to construct one of the world's largest facial recognition systems. The project envisions a future in which police from across the country's 29 states and seven union territories would have access to a single, centralized database. The daunting scope of the proposed network is laid out in a detailed 172-page document published by the National Crime Records Bureau, which requests bids from companies to build the project. The project would match images from the country's growing network of CCTV cameras against a database encompassing mug shots of criminals, passport photos and images collected by [government] agencies. It would also recognize faces on closed-circuit cameras and "generate alerts if a blacklist match is found." Security forces would be equipped with hand-held mobile devices enabling them to capture a face in the field and search it instantly against the national database, through a dedicated app. For privacy advocates, this is worrying. "India does not have a data protection law," says [Apar] Gupta [of the Internet Freedom Foundation]. "It will essentially be devoid of safeguards." It might even be linked up to Aadhaar, India's vast biometric database, which contains the personal details of 1.2 billion Indian citizens, enabling India to set up "a total, permanent surveillance state," he adds.
Note: Read an excellent article by The Civil Liberties Union for Europe about the 7 biggest privacy issues that concern facial recognition technology. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Apple contractors regularly hear confidential medical information, drug deals, and recordings of couples having sex, as part of their job providing quality control, or grading, the companys Siri voice assistant. Although Apple does not explicitly disclose it in its consumer-facing privacy documentation, a small proportion of Siri recordings are passed on to contractors working for the company around the world. Apple says the data is used to help Siri and dictation ... understand you better and recognise what you say. But the company does not explicitly state that that work is undertaken by humans who listen to the pseudonymised recordings. A whistleblower working for the firm, who asked to remain anonymous due to fears over their job, expressed concerns about this lack of disclosure, particularly given the frequency with which accidental activations pick up extremely sensitive personal information. The whistleblower said: There have been countless instances of recordings featuring private discussions. These recordings are accompanied by user data showing location, contact details, and app data. Although Siri is included on most Apple devices, the contractor highlighted the Apple Watch and the companys HomePod smart speaker as the most frequent sources of mistaken recordings. As well as the discomfort they felt listening to such private information, the contractor said they were motivated to go public about their job because of their fears that such information could be misused.
Note: For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
Apple and Google on Wednesday released long-awaited smartphone technology to automatically notify people if they might have been exposed to the coronavirus. The companies said 22 countries and several U.S. states are already planning to build voluntary phone apps using their software. It relies on Bluetooth wireless technology to detect when someone who downloaded the app has spent time near another app user who later tests positive for the virus. Many governments have already tried, mostly unsuccessfully, to roll out their own phone apps to fight the spread of the COVID-19 pandemic. Many of those apps have encountered technical problems on Apple and Android phones and haven’t been widely adopted. They often use GPS to track people’s location, which Apple and Google are banning from their new tool because of privacy and accuracy concerns. Public health agencies from Germany to the states of Alabama and South Carolina have been waiting to use the Apple-Google model, while other governments have said the tech giants’ privacy restrictions will be a hindrance because public health workers will have no access to the data. The companies said they’re not trying to replace contact tracing, a pillar of infection control that involves trained public health workers reaching out to people who may have been exposed to an infected person. But they said their automatic “exposure notification” system can augment that process and slow the spread of COVID-19.
Note: Watch an excellent video explanation of the dangers of contract tracing by a woman who applied to do this work. She shows how the claims of it being voluntary are far from the truth. For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus and the disappearance of privacy from reliable major media sources.
The CIA's chief technology officer outlined the agency's endless appetite for data in a far-ranging speech. Ira "Gus" Hunt said that the world is increasingly awash in information from text messages, tweets, and videos - and that the agency wants all of it. "The value of any piece of information is only known when you can connect it with something else that arrives at a future point in time," Hunt said. "Since you can't connect dots you don't have, it drives us into a mode of, we fundamentally try to collect everything and hang on to it forever." Hunt's comments come two days after Federal Computer Week reported that the CIA has committed to a massive, $600 million, 10-year deal with Amazon for cloud computing services. "It is really very nearly within our grasp to be able to compute on all human generated information," Hunt said. After that mark is reached, Hunt said, the agency would also like to be able to save and analyze all of the digital breadcrumbs people don't even know they are creating. "You're already a walking sensor platform," he said, noting that mobiles, smartphones and iPads come with cameras, accelerometers, light detectors and geolocation capabilities. "Somebody can know where you are at all times, because you carry a mobile device, even if that mobile device is turned off," he said. Hunt also spoke of mobile apps that will be able to control pacemakers - even involuntarily - and joked about a "dystopian" future. Hunt's speech barely touched on privacy concerns.
Note: The Internet of Things makes mass surveillance even easier. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
The National Park Service is continuing to convert dozens of its sites across the country to cashless payments only, drawing complaints and, now, a lawsuit. Starting in June last year, visitors to Rocky Mountain National Park in Colorado were told that they could not use cash to enter the park or use its campgrounds. The negative reactions were swift, with visitors raising privacy concerns and expressing confusion about why the American dollar would not be welcome in the U.S. parks system. Now these complaints are the subject of a lawsuit filed on March 6 in U.S. District Court in the District of Columbia, asserting that the service’s policies violate federal law defining cash as “legal tender” and the visitors’ “lawful right to pay in cash” at national sites, including those without bank accounts or cards or those who simply prefer to pay cash. In addition to the park service, its director, Charles F. Sams, III, and the Department of the Interior were named as defendants. One of the three plaintiffs, Toby Stover, a New York woman, drove to Hyde Park, N.Y., in January. She ... was not allowed to enter after trying to pay $10 in cash, the filing said. The plaintiffs’ lawyer, Ray L. Flores, II, said in an emailed reply to questions that the legal action is being financially backed by the Children’s Health Defense. Mr. Flores said in the email that cashless policies were “a key component — if not the linchpin — of the surveillance state.”
Note: This article is also available here. A 2018 Guardian piece titled "The cashless society is a con and big finance is behind it" describes some of the basic problems with the push to go cashless.
SpaceX is building a network of hundreds of spy satellites under a classified contract with a U.S. intelligence agency, five sources familiar with the program said. The network is being built by SpaceX's Starshield business unit under a $1.8 billion contract signed in 2021 with the National Reconnaissance Office (NRO), an intelligence agency that manages spy satellites. The plans show the extent of SpaceX's involvement in U.S. intelligence and military projects and illustrate a deeper Pentagon investment into vast, low-Earth orbiting satellite systems aimed at supporting ground forces. If successful, the sources said the program would significantly advance the ability of the U.S. government and military to quickly spot potential targets almost anywhere on the globe. Reuters reporting discloses for the first time that the SpaceX contract is for a powerful new spy system with hundreds of satellites bearing Earth-imaging capabilities that can operate as a swarm in low orbits. The planned Starshield network is separate from Starlink, SpaceX's growing commercial broadband constellation that has about 5,500 satellites in space. The classified constellation of spy satellites represents one of the U.S. government’s most sought-after capabilities in space because it is designed to offer the most persistent, pervasive and rapid coverage of activities on Earth. "No one can hide," one of the sources said of the system’s potential capability, when describing the network's reach.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Anything you purchase can be used against you. After the Jan. 6 Capitol clash, the Biden administration vastly expanded federal surveillance of average Americans. The Treasury Department’s Financial Crimes Enforcement Network (FinCEN) stretched its “suspicious behavior” definition, warning banks to track “‘extremism’ indicators that include ‘transportation charges, such as bus tickets, rental cars, or plane tickets, for travel to areas with no apparent purpose,’ or ‘the purchase of books (including religious texts),’” the House committee reported. If you bought a gun or ammo since 2021, Team Biden bureaucrats may have automatically classified you as a “potential active shooter.” FinCEN encouraged banks to use terms including “TRUMP” and “MAGA” for “identifying transactions on behalf of federal law enforcement,” the House Judiciary Committee reports. Rep. Jordan is seeking sworn testimony about the FBI’s “mass accumulation and use of Americans’ private information without legal process.” Jordan complained that the FBI “prepared an official report that broadly characterized certain political beliefs as indicative of domestic violent extremism.” The Canadian government used emergency decrees to freeze the bank accounts of anyone suspected of being tied to COVID “Freedom Convoy” protests in 2022.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Under ... Section 702 [of the Foreign Intelligence Surveillance Act], the US government collects hundreds of millions of phone calls, emails, and text messages each year. An inestimable chunk belongs to American citizens, permanent residents, and others in the United States neither suspected nor accused of any crime. Police and intelligence agencies buy their way around the Fourth Amendment by paying US companies for information that they’d otherwise demand a warrant to disclose. The House Intelligence Committee’s bill—the FISA Reform and Reauthorization Act, or FRRA—does nothing to address this privacy threat. What the FRRA does appear to do, despite its name, is explode the number of companies the US government may compel to cooperate with wiretaps under Section 702. That was the assessment on Friday of Marc Zwillinger, amicus curiae to the Foreign Intelligence Surveillance Court of Review (FISCR). Section 702 currently allows the government to compel a class of companies called “electronic communications providers” to collect communications. If the FRRA becomes law, according to Zwillinger, that category would be greatly expanded to include a slew of new businesses, including “data centers, colocation providers, business landlords, and shared workspaces,” as well as, he says, “hotels where guests connect to the internet.” Communications may be seized under 702 and only years later dug up for an entirely different reason.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
People around the world are getting their eyeballs scanned in exchange for a digital ID and the promise of free cryptocurrency. The Worldcoin project says it aims to create a new "identity and financial network" and that its digital ID will allow users to, among other things, prove online that they are human, not a bot. The project launched on Monday, with eyeball scans taking place in countries including Britain, Japan and India. At a crypto conference in Tokyo, people on Tuesday queued in front of a gleaming silver globe flanked by placards stating: "Orbs are here." Applicants lined up to have their irises scanned by the device, before waiting for the 25 free Worldcoin tokens the company says verified users can claim. Worldcoin's data-collection is a "potential privacy nightmare," said the Electronic Privacy Information Center. Worldcoin's privacy policy ... says that data may be passed to subcontractors and could be accessed by governments and authorities. UK privacy campaign group Big Brother Watch said there was a risk biometric data could be hacked or exploited. "Digital ID systems increase state and corporate control over individuals' lives and rarely live up to the extraordinary benefits technocrats tend to attribute to them," senior advocacy officer Madeleine Stone said. In a mall in Bengaluru, India, orb-operators approached passers-by on Tuesday and showed them how to sign up. Most interviewed by Reuters said they were not worried about privacy.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
When Edward Snowden blew the whistle on mass surveillance by the US government, he traded a comfortable existence in Hawaii, the paradise of the Pacific, for indefinite exile in Russia, now a pariah in much of the world. But 10 years after Snowden was identified as the source of the biggest National Security Agency (NSA) leak in history, it is less clear whether America underwent a similarly profound transformation in its attitude to safeguarding individual privacy. Was his act of self-sacrifice worth it – did he make a difference? On 6 June 2013, the Guardian published the first story based on Snowden's disclosures, revealing that a secret court order was allowing the US government to get Verizon to share the phone records of millions of Americans. The impact was dramatic. James Clapper, the director of national intelligence, who earlier that year had testified to Congress that the NSA did not collect data on millions of Americans, was forced to apologise and admit that his statement had been "clearly erroneous". The American Civil Liberties Union (ACLU) filed a constitutional lawsuit in federal court. It eventually led to a ruling that held the NSA telephone collection program was and always had been illegal, a significant breakthrough given that national security surveillance programs had typically been insulated from judicial review. You will not find any coherent statement by any US security official that says clearly what harm was done by these disclosures.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Footprints left on a beach. Air breathed in a busy room. Ocean water. Scientists have been able to collect and analyze detailed genetic data from human DNA from all these places, raising thorny ethical questions about consent, privacy and security when it comes to our biological information. The researchers from the University of Florida, who were using environmental DNA found in sand to study endangered sea turtles, said the DNA was of such high quality that the scientists could ... determine the genetic ancestry of populations living nearby. They could also match genetic information to individual participants who had volunteered to have their DNA recovered. Human DNA that has seeped into the environment through our spit, skin, sweat and blood could be used to help find missing persons, aid in forensic investigations to solve crimes, locate sites of archaeological importance, and for health monitoring. However, the ability to capture human DNA from the environment could have a range of unintended consequences — both inadvertent and malicious. These included privacy breaches, location tracking, data harvesting, and genetic surveillance of individuals or groups. [Researchers] retrieved DNA from footprints made in sand by four volunteers. They were able to sequence part of the participants’ genomes. Next, the researchers took samples of air from a ... room in an animal clinic. The team recovered DNA that matched the staff volunteers [and] animal patients.
Note: This research was published in the journal Nature Ecology & Evolution. For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy from reliable major media sources.
Frank Forrester Church sat in the US Senate for 24 years. He battled for civil rights and came to oppose the Vietnam war. He believed Americans were citizens, not subjects. Chairing the intelligence select committee was his most enduring accomplishment. James Risen, a Pulitzer-winning reporter now with the Intercept, sees him as a hero. The Last Honest Man is both paean and lament. “For decades ... the CIA’s operations faced only glancing scrutiny from the White House, and virtually none from Congress,” Risen writes. “True oversight would have to wait until 1975, and the arrival on the national stage of a senator from Idaho, Frank Church.” For 16 months, Church and his committee scrutinized the CIA, FBI and National Security Agency and their many abuses. Political assassinations, covert operations and domestic surveillance finally received scrutiny and oversight. A plot to kill Fidel Castro, with an assist from organized crime, made headlines. So did the personal ties that bound John F Kennedy, mob boss Sam Giancana and their shared mistress, Judith Campbell Exner. Giancana was murdered before he testified. Before John Rosselli, another mobster, could make a third appearance, his decomposed body turned up in a steel fuel drum near Miami. Against this grizzly but intriguing backdrop, Risen’s book is aptly subtitled: The CIA, the FBI, the Mafia, and the Kennedys – And One Senator’s Fight to Save Democracy.
Note: Read more about James Risen's courageous reporting on the intelligence community. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption from reliable major media sources.
The Georgia Army National Guard plans to combine two deeply controversial practices — military recruiting at schools and location-based phone surveillance — to persuade teens to enlist, according to contract documents reviewed by The Intercept. The federal contract materials outline plans by the Georgia Army National Guard to geofence 67 different public high schools throughout the state, targeting phones found within a one-mile boundary of their campuses with recruiting advertisements “with the intent of generating qualified leads of potential applicants for enlistment while also raising awareness of the Georgia Army National Guard.” Geofencing refers generally to the practice of drawing a virtual border around a real-world area. The ad campaign will make use of a variety of surveillance advertising techniques, including capturing the unique device IDs of student phones, tracking pixels, and IP address tracking. It will also plaster recruiting solicitations across Instagram, Snapchat, streaming television, and music apps. The campaign plans not only call for broadcasting recruitment ads to kids at school, but also for pro-Guard ads to follow these students around as they continue using the internet and other apps, a practice known as retargeting. While the state’s plan specifies targeting only high school juniors and seniors ages 17 and above, demographic ad targeting is known to be error prone, and experts told The Intercept it’s possible the recruiting messages could reach the phones of younger children.
Note: For more along these lines, see concise summaries of deeply revealing news articles on military corruption and the disappearance of privacy from reliable major media sources.
The reptilian annual World Economic Forum at Davos, where the masters of the universe meet to congratulate themselves on their benevolent dictatorship, is home to many sinister ideas. This year, one of the creepiest discussions of all was delivered under the guise of progress and productivity. Nita Farahany, a Duke University professor and futurist, gave a presentation at Davos about neurotechnology that is creating “brain transparency.” The new technologies, which Farahany says are being deployed in workplaces around the world ... include a variety of wearable sensors that read the brain’s electrical impulses and can show how fatigued you are, whether you’re focused on the task at hand or if your attention is wandering. According to Farahany, thousands of companies have hooked workers ranging from train drivers to miners up to these devices already, in the name of workplace safety. But what we are really discussing is workplace surveillance. Farahany paints a picture of a near future in which every office worker could be fitted with a small wearable that would constantly record brain activity, creating an omnipotent record of your thoughts, attention and energy that the boss could study at leisure. Farahany acknowledges that there could be drawbacks here: “Done poorly, it could become the most oppressive technology we’ve ever introduced on a wide scale.” All of this raises the question: what exactly is your employer buying when they give you a paycheck? For bosses, the answer is simple: “Everything.”
Note: Tune into a fascinating, 17 min. conversation about this issue that raises important questions about the overreliance on technology as a tool of control, under the guise of workplace safety. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption from reliable major media sources.
The internet has come a long way since Tim Berners-Lee invented the world wide web in 1989. Now, in an era of growing concern over privacy, he believes it’s time for us to reclaim our personal data. Through their startup Inrupt, Berners-Lee and CEO John Bruce have created the “Solid Pod” — or Personal Online Data Store. It allows people to keep their data in one central place and control which people and applications can access it, rather than having it stored by apps or sites all over the web. Users can get a Pod from a handful of providers. Not only is user data safe from corporations, and governments, it’s also less likely to be stolen by hackers, Bruce says. Launched in 2017, Inrupt reportedly raised $30 million in December 2021 and Berners-Lee says it will help deliver the next iteration of the web — “Web 3.” Paul Brody, a blockchain expert for analysts Ernst and Young, believes Web 3 could change the way we use the internet. “You’ll hear people talk about Web 3 and decentralization as being very similar in ideas and goals,” he says. “Owning your own data and really controlling your own commerce infrastructure is something that Web 3 will enable. It will be ultimately really transformational for users.” Berners-Lee hopes his platform will give control back to internet users. “I think the public has been concerned about privacy — the fact that these platforms have a huge amount of data, and they abuse it,” he says. “You need to get back to a situation where you have autonomy, you have control of all your data.”
Note: For more along these lines, see concise summaries of deeply revealing news articles on the erosion of privacy from reliable major media sources.
In a cheerfully animated promotional video, a woman narrates Cubic Transportation Systems’ vision for the future. Travelers will pay fares using a ticket-free mobile account. Real-time data will be aggregated, linked, and shared. “The more information that is gathered, the more powerful the system becomes,” the narrator tells us. “The piece of the puzzle missing ... is you.” Over the past decade, Cubic has taken the first steps toward actualizing its vision by snapping up contracts for the development of mobile-based, contactless fare collection systems in eight of America’s 10 largest public transit networks. Transit authorities have embraced tap-to-pay technology for its convenience and speed, but privacy advocates are worried that the new fare collection systems pose serious surveillance and security risks. In addition to its transit operation, Cubic is a vast military contractor doing hundreds of millions of dollars in business with the U.S. military and sales to foreign militaries. The company supplies surveillance technologies, training simulators, satellite communications equipment, computing and networking platforms, and other military hardware and software. As Cubic’s quiet grip on fare collection takes hold in more cities, the company’s ability to process rider data grows with it, creating a sprawling corporate apparatus that has the extraordinary potential to gather up reams of information on the very people it is supposed to serve.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
As protesters around the country have marched against police brutality and in support of the Black Lives Matter movement, activists have spotted a recurring presence in the skies: mysterious planes and helicopters hovering overhead, apparently conducting surveillance on protesters. A press release ... revealed that the Drug Enforcement Agency and U.S. Marshals Service were asked by the Justice Department to provide unspecified support to law enforcement during protests. A few days later, a memo obtained by BuzzFeed News ... revealed that shortly after protests began in various cities, the DEA had sought special authority from the Justice Department to covertly spy on Black Lives Matter protesters on behalf of law enforcement. Both the DEA and the Marshals possess airplanes outfitted with so-called stingrays or dirtboxes: powerful technologies capable of tracking mobile phones or, depending on how theyre configured, collecting data and communications from mobile phones in bulk. That data can be used to identify people protesters, for example and track their movements during and after demonstrations, as well as to identify others who associate with them. They also can inject spying software onto specific phones. Stingrays are routinely used to target suspects in drug and other criminal investigations, but activists also believe the devices were used during protests against the Dakota Access pipeline, and against Black Lives Matter protesters over the last three months.
Note: Read more about invasive "stingray" technology and the secrecy surrounding its use. Learn how Google is siphoning all information about you it can get. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Spies for centuries have trained their sights on those who shape destinies of nations: presidents, prime ministers, kings. And in the 21st century, most of them carry smartphones. Such is the underlying logic for some of the most tantalizing discoveries for an international investigation that in recent months scrutinized a list of more than 50,000 phone numbers that included — according to forensic analyses of dozens of iPhones — at least some people targeted by Pegasus spyware licensed to governments worldwide. The list contained the numbers of politicians and government officials by the hundreds. But what of heads of state and governments, arguably the most coveted of targets? Fourteen. Or more specifically: three presidents, 10 prime ministers and a king. Forensic testing that might have revealed infection by NSO’s signature spyware, Pegasus, was not possible. Nor was it possible to determine whether any NSO client attempted to deliver Pegasus to the phones of these country leaders — much less whether any succeeded in turning these highly personal devices into pocket spies capable of tracking a national leader’s nearly every movement, communication and personal relationship. According to NSO marketing materials and security researchers, Pegasus is designed to collect files, photos, call logs, location records, communications and other private data from smartphones, and can activate cameras and microphones as well for real-time surveillance at key moments.
Note: Read how this Pegasus spyware was used to target activists and journalists in Mexico. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
The FBI has come under intense criticism after a 2017 leak exposed that its counterterrorism division had invented a new, unfounded domestic terrorism category it called black identity extremism. A number of civil rights groups have filed public records requests to try to better understand who exactly the FBI is investigating under that designation. The latest batch of FBI documents ... reveals that between 2015 and 2018, the FBI dedicated considerable time and resources to opening a series of assessments into the activities of individuals and groups it mostly labeled black separatist extremists. This designation was eventually folded into the category of black identity extremism. Assessments differ from full-blown investigations - or predicated investigations, in the bureaus lingo - because they do not need to be predicated on a factual basis. As a new report by the civil liberties group Defending Rights & Dissent notes, when choosing targets for an assessment, agents are allowed to use ethnicity, religion, or speech protected by the First Amendment as a factor, as long as it is not the only one. As the report notes, Even though the standards for opening an assessment are extraordinarily low, the FBI is allowed to use extremely intrusive investigative techniques in performing them, including physical surveillance, use of informants, and pretextual interviews. The bureau has in recent years shifted its target from those espousing separatist views to the much larger group of those protesting police violence.
Note: Read more about the FBI's use of "Black Identity Extremism" as a label in its terrorism investigations. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the erosion of civil liberties from reliable major media sources.
Not only is Alexa listening when you speak to an Echo smart speaker, an Amazon employee is potentially listening, too. Amazon (AMZN) employs a global team that transcribes the voice commands captured after the wake word is detected and feeds them back into the software ... Bloomberg reports. Amazon reportedly employs thousands of full-time workers and contractors in several countries, including the United States, Costa Rica and Romania, to listen to as many as 1,000 audio clips in shifts that last up to nine hours. The audio clips they listen to were described as "mundane" and even sometimes "possibly criminal," including listening to a potential sexual assault. In a response to the story, Amazon confirmed to CNN Business that it hires people to listen to what customers say to Alexa. Amazon doesn't "explicitly" tell Alexa users that it employs people to listen to the recordings. Amazon said in its frequently asked question section that it uses "requests to Alexa to train our speech recognition and natural language understanding systems." People can opt out of Amazon using their voice recordings to improve the software in the privacy settings section of the Alexa app. Alexa auditors don't have access to the customers' full name or address, but do have the device's serial number and the Amazon account number associated with the device. Amazon previously has been embroiled in controversy for privacy concerns regarding Alexa.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
It is widely regarded as the world’s most potent spyware, capable of reliably cracking the encrypted communications of iPhone and Android smartphones. The software, Pegasus, made by an Israeli company, NSO Group, has been able to track terrorists and drug cartels. It has also been used against human rights activists, journalists and dissidents. Now, an investigation published Friday by The New York Times Magazine has found that Israel, which controls the export of the spyware ... has made Pegasus a key component of its national security strategy, using it to advance its interests around the world. The F.B.I. bought and tested NSO software for years with plans to use it for domestic surveillance until the agency finally decided last year not to deploy the tools. The F.B.I., in a deal never previously reported, bought the spyware in 2019. It also spent two years discussing whether to deploy a newer product, called Phantom, inside the United States. The discussions at the Justice Department and the F.B.I. continued until last summer. But Pegasus equipment is still in a New Jersey building used by the F.B.I. And the company also gave the agency a demonstration of Phantom, which could hack American phone numbers. A brochure ... says that Phantom allows American law enforcement and spy agencies to “turn your target’s smartphone into an intelligence gold mine.” In 2018 ... the C.I.A. bought Pegasus to help Djibouti, an American ally, fight terrorism, despite longstanding concerns about human rights abuses there.
Note: Read about how NSO Group spyware was used against journalists and activists by the Mexican government. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Vice-premier Sun Chunlan, one of the most senior government officials to visit the centre of the coronavirus outbreak [was] heckled by residents who yelled fake, fake, everything is fake as she inspected the work of a neighbourhood committee charged with taking care of quarantined residents. Videos posted online showed Sun and a delegation walking along the grounds while residents appeared to shout from their apartment windows, fake, fake, its all fake, as well as we protest. Since 12 February, all residential compounds in Wuhan have been put under lockdown, barring most residents from leaving their homes. In an unusual turn of events, on Friday various Chinese state media outlets reported the videos showing public discontent. Such videos are frequently censored. Yet, the Peoples Daily posted a video subtitled in English showing one person shouting fake, fake, which has since been removed. A government-affiliated account on WeChat ... said in an essay posted on Thursday that all the facts of the incident were basically true. According to state broadcaster CCTV, Sun held a meeting immediately after the incident to deal with the complaints. Staff have been dispatched to visit the residents one by one. Observers say state media may be trying to co-opt discussion of the videos, which circulated widely online, and provide their own narrative of events. Elsewhere in China, schools in provinces reporting no new cases for a number of days, started to set their opening dates in a sign of the country returning to normal. Wuhan reported 126 new coronavirus cases on Thursday but the wider province of Hubei excluding the capital recorded none for the first time during the outbreak.
Note: Remember all of the privacy and freedoms given up after 9/11? How many of those have been given back? Learn more about the serious risk of the Coronavirus increasing the surveillance state in this excellent article. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
From 2008 to 2010, as Edward Snowden has revealed, the National Security Agency (NSA) collaborated with the British Government Communications Headquarters to intercept the webcam footage of over 1.8 million Yahoo users. The agencies were analyzing images they downloaded from webcams and scanning them for known terrorists who might be using the service to communicate, matching faces from the footage to suspects with the help of a new technology called face recognition. In attempting to find faces, the Pentagon's Optic Nerve program recorded webcam sex by its unknowing targets—up to 11 percent of the material the program collected was "undesirable nudity" that employees were warned not to access. And that's just the beginning of what face recognition technology might mean for us in the digital era. The U.S. government is in the process of building the world's largest cache of face recognition data, with the goal of identifying every person in the country. The creation of such a database would mean that anyone could be tracked wherever his or her face appears, whether it's on a city street or in a mall. Today's laws don't protect Americans from having their webcams scanned for facial data. "If cameras connected to databases can do face recognition, it will become impossible to be anonymous in society," [attorney Jennifer] Lynch says. That means every person in the U.S. would be passively tracked at all times.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
More than 60 years ago, in his “Foundation” series, the science fiction novelist Isaac Asimov invented a new science — psychohistory — that combined mathematics and psychology to predict the future. Now social scientists are trying to mine the vast resources of the Internet — Web searches and Twitter messages, Facebook and blog posts, the digital location trails generated by billions of cellphones — to do the same thing. The government is showing interest in the idea. This summer a little-known intelligence agency began seeking ideas from academic social scientists and corporations for ways to automatically scan the Internet in 21 Latin American countries for “big data,” according to a research proposal. The three-year experiment ... is being financed by the Intelligence Advanced Research Projects Activity, or Iarpa. The automated data collection system is to focus on patterns of communication, consumption and movement of populations. It will use publicly accessible data, including Web search queries, blog entries, Internet traffic flow, financial market indicators, traffic webcams and changes in Wikipedia entries. It is intended to be an entirely automated system, a “data eye in the sky” without human intervention. Some social scientists and advocates of privacy rights are deeply skeptical of the project, saying it evokes queasy memories of Total Information Awareness, a post-9/11 Pentagon program that proposed hunting for potential attackers by identifying patterns in vast collections of public and private data.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Spit into a cup when you land in an airport, and your DNA is stored. Every phone in every city talks to every other nearby device. Cross-border travel is enabled only by governments sharing data about millions of private movements. These are all possible visions of a future that the coronavirus pandemic has rushed on us. But a lurch into an even more intense era of mass data-collection - the vast hoovering up of who went near whom and when, who is healthy to travel, and even scraps of personal DNA languishing in databases - appears to be on the verge of becoming the new reality. It took the attacks of September 11, 2001 to shove aside the previous decade's phobia of mass surveillance ... in exchange for keeping us safe from terror. Over the next 15 years, billions of people agreed to a tacit deal where Facebook or Google were permitted to learn a staggering amount about them. But the challenge presented by Covid-19 - and the urgent need to trace contacts and movements - is of another scale of intimacy. South Korea located over 10,000 cellphones near the latest outbreak and texted them. The UK government has toyed with a centralized database of movements and health records, secured by government cyber-spies, able potentially to see who has been sick and who they have been near. Russia and many others have issued QR codes. China is putting surveillance cameras right outside people's doors. Will we look back at 2020 as the moment privacy finally evaporated?
Note: For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus and the disappearance of privacy from reliable major media sources.
Emotion artificial intelligence uses biological signals such as vocal tone, facial expressions and data from wearable devices as well as text and how people use their computers, promising to detect and predict how someone is feeling. Over 50% of large employers in the U.S. use emotion AI aiming to infer employees’ internal states, a practice that grew during the COVID-19 pandemic. For example, call centers monitor what their operators say and their tone of voice. We wondered what workers think about these technologies. My collaborators Shanley Corvite, Kat Roemmich, Tillie Ilana Rosenberg and I conducted a survey. 51% of participants expressed concerns about privacy, 36% noted the potential for incorrect inferences employers would accept at face value, and 33% expressed concern that emotion AI-generated inferences could be used to make unjust employment decisions. Despite emotion AI’s claimed goals to infer and improve workers’ well-being in the workplace, its use can lead to the opposite effect: well-being diminished due to a loss of privacy. On concerns that emotional surveillance could jeopardize their job, a participant with a diagnosed mental health condition said: “They could decide that I am no longer a good fit at work and fire me. Decide I’m not capable enough and not give a raise, or think I’m not working enough.” Participants ... said they were afraid of the dynamic they would have with employers if emotion AI were integrated into their workplace.
Note: The above article was written by Nazanin Andalibi at the University of Michigan. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The $118bn bipartisan immigration bill that the US Senate introduced on Sunday is already facing steep opposition. The 370-page measure, which also would provide additional aid to Israel and Ukraine, has drawn the ire of both Democrats and Republicans over its proposed asylum and border laws. But privacy, immigration and digital liberties experts are also concerned over another aspect of the bill: more than $400m in funding for additional border surveillance and data-gathering tools. The lion’s share of that funding will go to two main tools: $170m for additional autonomous surveillance towers and $204m for “expenses related to the analysis of DNA samples”, which includes those collected from migrants detained by border patrol. The bill describes autonomous surveillance towers as ones that “utilize sensors, onboard computing, and artificial intelligence to identify items of interest that would otherwise be manually identified by personnel”. The rest of the funding for border surveillance ... includes $47.5m for mobile video surveillance systems and drones and $25m for “familial DNA testing”. The bill also includes $25m in funding for “subterranean detection capabilities” and $10m to acquire data from unmanned surface vehicles or autonomous boats. As of early January, CBP had deployed 396 surveillance towers along the US-Mexico border, according to the Electronic Frontier Foundation (EFF).
Note: Read more about the secret history of facial recognition technology and undeniable evidence indicating these tools do much more harm than good. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
The Transportation Security Administration (TSA) sparked privacy concerns after unveiling plans to roll out controversial facial recognition tech in over 400 US airports soon. “TSA is in the early stages of deploying its facial recognition capability to airport security checkpoints,” a spokesperson [said] regarding the ambitious program. They explained that the cutting-edge tech serves to both enhance and expedite the screening process for passengers. Dubbed CAT-2 machines, these automated identification systems accomplish this by incorporating facial recognition tech to snap real-time pictures of travelers. They then compare this biometric data against the flyer’s photo ID to verify that it’s the real person. These CAT-scans enable “traveler use of mobile driver’s licenses,” thereby improving the security experience, per the spokesperson. The TSA currently has 600 CAT-2 units deployed at about 50 airports nationwide and plans to expand them to 400 federalized airports in the future. Following the implementation of these synthetic security accelerators at US airports last winter, lawmakers expressed concerns that the machines present a major privacy issue. “The TSA program is a precursor to a full-blown national surveillance state,” said Oregon Senator Jeff Merkley. “Nothing could be more damaging to our national values of privacy and freedom. No government should be trusted with this power.”
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
For the past two weeks, I’ve been using a new camera to secretly snap photos and record videos of strangers in parks, on trains, inside stores and at restaurants. I was testing the recently released $300 Ray-Ban Meta glasses that Mark Zuckerberg’s social networking empire made in collaboration with the iconic eyewear maker. The high-tech glasses include a camera for shooting photos and videos, and an array of speakers and microphones for listening to music and talking on the phone. The glasses, Meta says, can help you “live in the moment” while sharing what you see with the world. Meta, Apple and Magic Leap have all been hyping mixed-reality headsets that use cameras to allow their software to interact with objects in the real world. To inform people that they are being photographed, the Meta Ray-Bans include a tiny LED light embedded in the right frame to indicate when the device is recording. When a photo is snapped, it flashes momentarily. When a video is recording, it is continuously illuminated. As I shot 200 photos and videos with the glasses in public, including on BART trains, on hiking trails and in parks, no one looked at the LED light or confronted me about it. And why would anyone? It would be rude to comment on a stranger’s glasses, let alone stare at them. The ubiquity of smartphones, doorbell cameras and dashcams makes it likely that you are being recorded anywhere you go. But Chris Gilliard, an independent privacy scholar who has studied the effects of surveillance technologies, said cameras hidden inside smart glasses would most likely enable bad actors — like the people shooting sneaky photos of others at the gym — to do more harm.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The Palestinian population is intimately familiar with how new technological innovations are first weaponized against them–ranging from electric fences and unmanned drones to trap people in Gaza—to the facial recognition software monitoring Palestinians in the West Bank. Groups like Amnesty International have called Israel an Automated Apartheid and repeatedly highlight stories, testimonies, and reports about cyber-intelligence firms, including the infamous NSO Group (the Israeli surveillance company behind the Pegasus software) conducting field tests and experiments on Palestinians. Reports have highlighted: “Testing and deployment of AI surveillance and predictive policing systems in Palestinian territories. In the occupied West Bank, Israel increasingly utilizes facial recognition technology to monitor and regulate the movement of Palestinians. Israeli military leaders described AI as a significant force multiplier, allowing the IDF to use autonomous robotic drone swarms to gather surveillance data, identify targets, and streamline wartime logistics.” The Palestinian towns and villages near Israeli settlements have been described as laboratories for security solutions companies to experiment their technologies on Palestinians before marketing them to places like Colombia. The Israeli government hopes to crystalize its “automated apartheid” through the tokenization and privatization of various industries and establishing a technocratic government in Gaza.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
School librarians [will] have less freedom to choose books and schoolchildren [will have] less ability to read books they find intriguing, experts say. In the past two years, six states have passed laws that mandate parental involvement in reviewing books, making it easier for parents to remove books or restrict the texts available at school, according to a tally kept by nonprofit EveryLibrary. Policies are proliferating at the district level, too. A Texas system will divide its library into "juvenile," "young adult" and "adult" sections, with parents choosing the "level" their child can access. "This is a state-sponsored purging of ideas and identities that has no precedent in the United States of America," said John Chrastka, EveryLibrary's executive director. "We're witnessing the silencing of stories and the suppressing of information [that will make] the next generation less able to function in society." A flurry of parent-staffed websites reviewing books for inappropriate content have appeared – including "Between the Book Covers," whose website says "professional review sites cannot be entrusted," and BookLook.info, "a place for taking a closer look at the books in our children's hands." There are also Facebook groups like Utah's "LaVerna in the Library," which "collects naughty children's books." As states and districts adjust their reading rules, parents and students are working to change things, too. Teens in Texas, for example, have formed "banned book clubs" – while in Missouri, students are suing their district to restore eight pulled books.
Note: For more along these lines, see concise summaries of the disappearance of privacy in our society. Whether in our schools, on social media, or in our news, read about the increasing issue of censorship that undermines democracy in our Mass Media Information Center.
“Would you like to sign in with your palm?” That was the question a cheerful Amazon employee posed when greeting me last week at the opening of a Whole Foods Market in Washington’s Glover Park neighborhood. For the next 30 minutes, I shopped. Then I simply walked out, no cashier necessary. Whole Foods — or rather Amazon — would bill my account later. More than four years ago, Amazon bought Whole Foods for $13 billion. Now the Amazon-ification of the grocery chain is physically complete. Amazon designed my local grocer to be almost completely run by tracking and robotic tools for the first time. The technology, known as Just Walk Out, consists of hundreds of cameras with a god’s-eye view of customers. Sensors are placed under each apple, carton of oatmeal and boule of multigrain bread. Deep-learning software analyzes the shopping activity to detect patterns and increase the accuracy of its charges. The Whole Foods in Glover Park ... has sparked a spirited local debate, with residents sparring on the Nextdoor community app and a neighborhood email list over the store’s “dystopian” feeling versus its “impressive technology.” Some ... said they had found errors in their bills and complained about the end of produce by the pound. Everything is now offered per item, bundle or box. Some mourned the disappearance of the checkout line, where they perused magazines. Many were suspicious of the tracking tech. “It’s like George Orwell’s ‘1984,’” said Allen Hengst, 72, a retired librarian.
Note: For more along these lines, see concise summaries of deeply revealing news articles on food system corruption and the disappearance of privacy from reliable major media sources.
It was an unusual forearm tattoo that the police said led them to Luis Reyes, a 35-year-old man who was accused of stealing packages from a Manhattan building’s mailroom in 2019. But the truth was more complicated: Mr. Reyes had first been identified by the New York Police Department’s powerful facial recognition software as it analyzed surveillance video of the crime. His guilty plea this year ... was part of the sprawling legacy of one of the city’s darkest days. Since the fall of the World Trade Center, the security apparatus born from the Sept. 11 attack on the city has fundamentally changed the way the country’s largest police department operates, altering its approach to finding and foiling terrorist threats, but also to cracking minor cases like Mr. Reyes’s. New Yorkers simply going about their daily lives routinely encounter post-9/11 digital surveillance tools like facial recognition software, license plate readers or mobile X-ray vans that can see through car doors. Surveillance drones hover above mass demonstrations and protesters say they have been questioned by antiterrorism officers after marches. The department’s Intelligence Division, redesigned in 2002 to confront Al Qaeda operatives, now uses antiterror tactics to fight gang violence and street crime. The department’s budget for intelligence and counterterrorism has more than quadrupled, spending more than $3 billion since 2006, and more through funding streams that are difficult to quantify, including federal grants and the secretive Police Foundation.
Note: For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy from reliable major media sources.
Few pause to think that their phones can be transformed into surveillance devices, with someone thousands of miles away silently extracting their messages, photos and location, activating their microphone to record them in real time. Such are the capabilities of Pegasus, the spyware manufactured by NSO Group, the Israeli purveyor of weapons of mass surveillance. The Guardian will be revealing the identities of many innocent people who have been identified as candidates for possible surveillance by NSO clients in a massive leak of data. Without forensics on their devices, we cannot know whether governments successfully targeted these people. But the presence of their names on this list indicates the lengths to which governments may go to spy on critics, rivals and opponents. Journalists across the world were selected as potential targets by these clients prior to a possible hack using NSO surveillance tools. People whose phone numbers appear in the leak ... include lawyers, human rights defenders, religious figures, academics, businesspeople, diplomats, senior government officials and heads of state. One phone that has contained signs of Pegasus activity belonged to our esteemed Mexican colleague Carmen Aristegui, whose number was in the data leak and who was targeted following her expos© of a corruption scandal involving her country's former president Enrique Pe±a Nieto. At least four of her journalist colleagues appear in the leak
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
For a second year, the nation’s surveillance court has pointed with concern to “widespread violations” by the F.B.I. of rules intended to protect Americans’ privacy when analysts search emails gathered without a warrant. In a 67-page ruling ... James E. Boasberg, the presiding judge on the Foreign Intelligence Surveillance Court, recounted several episodes uncovered by an F.B.I. audit where the bureau’s analysts improperly searched for Americans’ information in emails that the National Security Agency collected without warrants. Still, Judge Boasberg said he was willing to issue a legally required certification for the National Security Agency’s warrantless surveillance program to operate for another year. [The program] grew out of the once-secret Stellarwind project, which President George W. Bush started after the Sept. 11, 2001, attacks. In 2008, Congress legalized the practice. The surveillance is carried out by the National Security Agency, but three other entities — the C.I.A., the National Counterterrorism Center and the F.B.I. — also receive access to streams of “raw” messages. The F.B.I. receives only a small portion of the messages that the National Security Agency vacuums up: The bureau gets copies of intercepts to and from targets who are deemed relevant to a full and active F.B.I. national security investigation. In 2019, the most recent year for which data is public, the program had more than 200,000 targets.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Back in June, the World Economic Forum, best known for its annual Davos summit, kicked off a lunge for organizational relevance. The effort was called ... the Great Reset. And through articles, videos, webinars, podcasts, and a book by WEF founder Klaus Schwab, it provided a coronavirus-themed rebranding of all the things Davos does anyway, now hastily repackaged as a blueprint for reviving the global economy post-pandemic by “seeking a better form of capitalism.” The Great Reset was a place to hawk for-profit technofixes to complex social problems; to hear heads of transnational oil giants opine about the urgent need to tackle climate change; to listen to politicians say the things they say during crises: that this is a tragedy but also an opportunity. In short, the Great Reset encompasses some good stuff that won’t happen and some bad stuff that certainly will and, frankly, nothing out of the ordinary in our era of “green” billionaires readying rockets for Mars. None of this is to say that Schwab’s Reset push is benign and unworthy of scrutiny. All kinds of dangerous ideas are lurking under its wide brim, from a reckless push toward more automation in the midst of a joblessness crisis, to the steady move to normalize mass surveillance and biometric tracking tools, to the very real (though not new) problem of Bill Gates’s singular power over global health policy.
Note: The author of this article is courageous journalist Naomi Klein, who wrote the seminal book “The Shock Doctrine.” For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus from reliable major media sources.
Previous vaccines have taken a decade or more to develop, and more than half of the past 20 years have failed in clinical trials. However, four [COVID-19] vaccine candidates have entered the final phase of clinical trials prior to approval by the Food and Drug Administration. Operation Warp Speed ... organized government agencies and private companies with the goal of developing, manufacturing and distributing hundreds of millions of vaccine doses, with starting doses to be available by early 2021. At the head of the operation is Moncef Slaoui, a Moroccan-born Belgian-American scientist. Operation Warp Speed … has invested in six vaccine candidates (Moderna, Pfizer / BioNTech, Johnson & Johnson, AstraZeneca, Novavax, and Sanofi / GSK) with the hope that at least one ... will prove safe and effective in clinical trials. Four of the six vaccine candidates have already been shown to be safe and effective in the first two test phases, which test whether the vaccinations produce so-called neutralizing antibodies. Serious health problems regularly arise during vaccination attempts. "We know how to distribute vaccines to any location in the US," says Slaoui. "It happens every year for flu and shingles." Tracking systems need to be "incredibly precise" to ensure that patients are each given two doses of the same vaccine and to monitor them for adverse health effects. Operation Warp Speed … has selected medical distributor McKesson and cloud operators Google and Oracle to collect and track vaccine data.
Note: The above article is also available here. Don't miss this excellent article which raises many important questions about this operation. For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus and vaccines from reliable major media sources.
Seven years after former National Security Agency contractor Edward Snowden blew the whistle on the mass surveillance of Americans' telephone records, an appeals court has found the program was unlawful. The U.S. Court of Appeals for the Ninth Circuit said the warrantless telephone dragnet that secretly collected millions of Americans' telephone records violated the Foreign Intelligence Surveillance Act and may well have been unconstitutional. Snowden, who fled to Russia in the aftermath of the 2013 disclosures and still faces U.S. espionage charges, said on Twitter that the ruling was a vindication of his decision to go public with evidence of the National Security Agency's domestic eavesdropping operation. "I never imagined that I would live to see our courts condemn the NSA's activities as unlawful and in the same ruling credit me for exposing them," Snowden said. Evidence that the NSA was secretly building a vast database of U.S. telephone records ... was the first and arguably the most explosive of the Snowden revelations published by the Guardian newspaper in 2013. Up until that moment, top intelligence officials publicly insisted the NSA never knowingly collected information on Americans at all. After the program's exposure, U.S. officials fell back on the argument that the spying had played a crucial role in fighting domestic extremism. But the Ninth Circuit ruled Wednesday that those claims were "inconsistent with the contents of the classified record."
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
It's a fairly ordinary evening on TikTok, the video-sharing app. Things do not seem so different on Douyin, the Chinese version of TikTok, where a live streaming boom has minted new social media millionaires. Behind the scenes, however, Chinese streamers are subject to an elaborate regime of automated surveillance and censorship. One system can use facial recognition to scan live streamers' broadcasts and guess their age. Another checks whether users' faces match their state ID cards. Another system assigns streamers, who are expected to uphold "public order and good customs", a "safety rating", similar to a "credit score". If the score dips below a certain level, they are punished automatically. Meanwhile, speech and text recognition is used to ferret out sins such as "feudal superstition" [and] defamation of the Communist Party. These methods are laid bare in a little-known document from TikTok and Douyin's parent company, ByteDance, and unearthed by New York City journalist Izzy Niu, which explains how the apps have adapted China's strict internet censorship laws to the unprecedented speed and chaos of live streaming. The document raises difficult questions for TikTok, which faces privacy probes in the US and UK and has already been banned in India. Some of these methods are common in the West, too. Both Facebook and YouTube use AI to police their services, and have massively expanded their censorship during the pandemic.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy from reliable major media sources.
The White House and the Centers for Disease Control and Prevention are asking Facebook, Google and other tech giants to give them greater access to Americans' smartphone location data in order to help them combat the spread of the coronavirus, according to four people at companies involved in the discussions who are not authorized to speak about them publicly. Federal health officials say they could use anonymous, aggregated user data collected by the tech companies to map the spread of the virus a practice known as "syndromic surveillance" and prevent further infections. They could also use the data to see whether people were practicing "social distancing." The federal effort [was] first reported by The Washington Post. The government officials have held at least two calls in recent days with representatives from the companies, the sources said. Those officials are "very serious" about making this happen, a person at one of the tech companies said. Similar and more aggressive surveillance practices have already been put to use in China, South Korea and Israel. The moves have set off alarm bells among privacy advocates who fear what the government may do with users' data. Facebook already provides health researchers and nongovernmental organizations in some countries with anonymized data to help disease prevention efforts. Representatives from Facebook, Google, Twitter, Apple, Amazon, Microsoft, IBM and Cisco all took part in the call with White House and federal health officials.
Note: For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus pandemic and the disappearance of privacy from reliable major media sources.
While we all live under extensive surveillance, for government employees and contractors - especially those with a security clearance - privacy is virtually nonexistent. Everything they do on their work computers is monitored. Even when they try to outsmart their work computer by taking photos directly of their screen, video cameras in their workplace might be recording their every move. Government workers with security clearance promise never [to] divulge classified information to anyone who is not authorized to receive it. But for many whistleblowers, the decision to go public results from troubling insights into government activity, coupled with the belief that as long as that activity remains secret, the system will not change. The growing use of the Espionage Act, a 1917 law that criminalizes the release of national defense information by anyone with intent or reason to believe that it is to be used to the injury of the United States or to the advantage of a foreign nation, shows how the system is rigged against whistleblowers. Government insiders charged under the law are not allowed to defend themselves by arguing that their decision to share what they know was prompted by an impulse to help Americans confront and end government abuses. The act is blind to the possibility that the publics interest ... might outweigh the governments interest, Jameel Jaffer, head of the Knight First Amendment Institute, wrote recently. It is blind to the difference between whistle-blowers and spies.
Note: The above article includes the stories of four whistleblowers charged under the Espionage act. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Hundreds of apps can follow your movements and share the details with advertisers, retailers and even hedge funds. Its difficult to know for sure whether location data companies are tracking your phone. Any app that collects location data may share your information with other companies, as long as it mentions that somewhere in its privacy policy. You can head off much of the tracking on your own device by spending a few minutes changing settings. Heres how to limit the snooping. How do I stop location tracking on iOS? Some apps have internal settings where you can indicate that you dont want your location used for targeted advertising or other purposes. But the easiest method is to go through your devices main privacy menu. First, open Settings and select Privacy, which has a blue icon with a white hand. Then select Location Services, which is at the top and has a little arrow. Youll see a list of apps, along with the location setting for each. Tap on apps you want to adjust. Selecting Never blocks tracking by that app. The option While Using the App ensures that the app gets location only while in use. Choosing Always, allows the app to get location data even when not in use. How do I stop it on Android? First, open the Settings on your phone. On the main settings page, tap Security & location. On the next screen, tap Location, which can be found in the Privacy section. On the Location screen, tap App-level permissions. Youll see a list of apps. To turn off location for an app, slide the toggle to the left.
Note: For more details, read the entire article at the link above. For more along these lines, see concise summaries of deeply revealing privacy news articles from reliable major media sources.
In the summer of 2015, as Memphis exploded with protests over the police killing of a 19-year-old man, activists began hearing on Facebook from someone called Bob Smith. His profile picture [was] a Guy Fawkes mask, the symbol of anti-government dissent. Smith acted as if he supported the protesters. Over the next three years, dozens of them accepted his friend requests, allowing him to observe private discussions. He described himself as a far-left Democrat, a fellow protester and a man of color. But Smith was not real. He was the creation of a white detective in the Memphis Police Departments Office of Homeland Security whose job was to keep tabs on local activists. The detective, Tim Reynolds, outed himself in August under questioning by the American Civil Liberties Union of Tennessee, which sued the police department for allegedly violating a 1978 agreement that prohibited police from conducting surveillance of lawful protests. The revelation validated many activists distrust of local authorities. It also provided a rare look into the ways American law enforcement operates online. Social media monitoring - including the use of software to crunch data about peoples online activity - illustrates a policing revolution that has allowed authorities to not only track people but also map out their networks, said Rachel Levinson-Waldman, senior counsel at [the] Brennan Center for Justice. But there are few laws governing this kind of monitoring.
Note: Memphis police were recently reported to have systematically spied on community activists. For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the erosion of civil liberties.
A trove of documents released by the city of Memphis late last week appear to show that its police department has been systematically using fake social media profiles to surveil local Black Lives Matter activists, and that it kept dossiers and detailed power point presentations on dozens of Memphis-area activists. The surveillance project was operated through the Memphis police departments office of homeland security. In a deposition for a lawsuit filed by the American Civil Liberties Union over the information gathering, officials said it ... began to focus on local individuals or groups that were staging protests [around 2016]. This included the publication of daily joint information briefings on potential protests and known protesters. The briefings regularly included information about meetings on private property, panel discussions, town halls, and even innocuous events like Black Owned Food Truck Sunday. A good deal of that information appears to have been obtained by a fake MPD Facebook profile for a Bob Smith, which the ACLU said was used to view private posts, join private groups, and otherwise pose as a member of the activist community. The briefings, which contained ... photographs, dates of birth, addresses, and mental health histories were distributed beyond the department according to the ACLU lawsuit, to a number of local businesses including the regions largest employer FedEx and the county school district.
Note: For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the erosion of civil liberties.
All over the western world banks are shutting down cash machines and branches. They are trying to push you into using their digital payments and digital banking infrastructure. Financial institutions ... are trying to nudge us towards a cashless society and digital banking. The true motive is corporate profit. Payments companies such as Visa and Mastercard want to increase the volume of digital payments services they sell, while banks want to cut costs. The nudge requires two parts. First, they must increase the inconvenience of cash. Second, they must vigorously promote the alternative. But a cashless society is not in your interest. It is in the interest of banks and payments companies. Their job is to make you believe that it is in your interest too, and they are succeeding in doing that. The recent Visa chaos, during which millions of people who have become dependent on digital payment suddenly found themselves stranded when the monopolistic payment network crashed, was a temporary setback. Digital systems may be convenient, but they often come with central points of failure. Cash, on the other hand, does not crash. It does not rely on external data centres, and is not subject to remote control or remote monitoring. The cash system allows for an unmonitored off the grid space. This is also the reason why financial institutions and financial technology companies want to get rid of it. Cash transactions are outside the net that such institutions cast to harvest fees and data.
Note: For more on this questionable trend, see this article and this one in the UK's Guardian. For more along these lines, see concise summaries of deeply revealing news articles on financial industry corruption and the disappearance of privacy.
China is reversing the commonly held vision of technology as a great democratizer, bringing people more freedom and connecting them to the world. In China, it has brought control. Cameras scan train stations for Chinas most wanted. Billboard-size displays ... list the names of people who dont pay their debts. Facial recognition scanners guard the entrances to housing complexes. Already, China has an estimated 200 million surveillance cameras. Such efforts supplement other systems that track internet use and communications, hotel stays, train and plane trips and even car travel. Invasive mass-surveillance software has been set up in the west to track members of the Uighur Muslim minority and map their relations with friends and family. [At] the intersection south of Changhong Bridge in the city of Xiangyang ... police put up cameras linked to facial recognition technology and a big, outdoor screen. Photos of lawbreakers were displayed alongside their names and government I.D. numbers. Chinas surveillance companies are also looking to test the appetite for high-tech surveillance abroad. At home, China is preparing its people for next-level surveillance technology. A recent state-media propaganda film called Amazing China showed off a ... virtual map that provided police with records of utility use. If there are anomalies, the system sends an alert, a narrator says, as Chinese police officers pay a visit to an apartment with a record of erratic utility use.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy.
Thousands of people pass by the buildings each day and rarely give them a second glance, because their function is not publicly known. They are an integral part of one of the worlds largest telecommunications networks and they are also linked to a controversial National Security Agency surveillance program. Atlanta, Chicago, Dallas, Los Angeles, New York City, San Francisco, Seattle, and Washington, D.C.. In each of these cities, The Intercept has identified an AT&T facility containing networking equipment that transports large quantities of internet traffic across the United States and the world. A body of evidence including classified NSA documents, public records, and interviews with several former AT&T employees indicates that the buildings are central to an NSA spying initiative that has for years monitored billions of emails, phone calls, and online chats passing across U.S. territory. The NSA considers AT&T to be one of its most trusted partners and has lauded the companys extreme willingness to help. Little known, however, is that its scope is not restricted to AT&Ts customers. According to the NSAs documents, it values AT&T not only because it has access to information that transits the nation, but also because it maintains unique relationships with other phone and internet providers. The NSA exploits these relationships for surveillance purposes, commandeering AT&Ts massive infrastructure and using it as a platform to covertly tap into communications processed by other companies.
Note: The NSA was authorized in 2016 to share communications data it collected without warrants on Americans with 16 intelligence and law enforcement agencies. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
As Facebook sought to become the worlds dominant social media service, it struck agreements allowing phone and other device makers access to vast amounts of its users personal information. Facebook has reached data-sharing partnerships with at least 60 device makers - including Apple, Amazon, BlackBerry, Microsoft and Samsung. The partnerships ... raise concerns about the companys privacy protections and compliance with a 2011 consent decree with the Federal Trade Commission. Facebook allowed the device companies access to the data of users friends without their explicit consent, even after declaring that it would no longer share such information with outsiders. Some device makers could retrieve personal information even from users friends who believed they had barred any sharing. In interviews, several former Facebook software engineers and security experts said they were surprised at the ability to override sharing restrictions. Its like having door locks installed, only to find out that the locksmith also gave keys to all of his friends so they can come in and rifle through your stuff without having to ask you for permission, said Ashkan Soltani, a research and privacy consultant who formerly served as the F.T.C.s chief technologist.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
I downloaded a copy of my Facebook data last week. I didnt expect to see much. But when I opened my file, it was like opening Pandoras box. I learned that about 500 advertisers - many that I had never heard of, like Bad Dad, a motorcycle parts store, and Space Jesus, an electronica band - had my contact information, which could include my email address, phone number and full name. Facebook also had my entire phone book, including the number to ring my apartment buzzer. The social network had even kept a permanent record of the roughly 100 people I had deleted from my friends list over the last 14 years. Facebook said unfamiliar advertisers might appear [in the file] because they might have obtained my contact information from elsewhere, compiled it into a list of people they wanted to target and uploaded that list into Facebook. Brands can obtain your information [by] buying ... from a data provider like Acxiom, which has amassed one of the worlds largest commercial databases on consumers. Lets be clear: Facebook is just the tip of the iceberg when it comes to what information tech companies have collected on me. Knowing this, I also downloaded copies of my Google data with a tool called Google Takeout. The data sets were exponentially larger than my Facebook data. Here was the biggest surprise: In a folder labeled Ads, Google kept a history of many news articles I had read. Be warned: Once you see the vast amount of data that has been collected about you, you wont be able to unsee it.
Note: Those who want to download their own Facebook data can use this link. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
Bloomberg Government reports on a FedBizOpps.gov posting by the Department of Homeland Security (DHS) with the relatively benign-sounding subject Media Monitoring Services. The details of the attached Statement of Work, however, outline a plan to gather and monitor the public activities of media professionals and influencers and are enough to cause nightmares of constitutional proportions, particularly as the freedom of the press is under attack worldwide. As part of its "media monitoring," the DHS seeks to track more than 290,000 global news sources as well as social media. The successful contracting company will have "24/7 access to a password protected, media influencer database" ... in order to "identify any and all media coverage related to the Department of Homeland Security or a particular event." The database will be browsable by "location, beat and type of influencer," and for each influencer, the chosen contractor should "present contact details and ... an overview of the previous coverage published by the media influencer." Increasing government encroachment on the freedom of the press is the sinister backdrop to all of this. Freedom House ... recently concluded that global media freedom has reached its lowest level in the past 13 years. The independent watchdog organization blames "new threats to journalists and media outlets in major democracies" as well as "further crackdowns on independent media in authoritarian countries like Russia and China."
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the manipulation of public perception.
A US court will today hear a request from Monsanto for access to a huge batch of internal communications by Avaaz, in a move that the campaign group says could have grave repercussions for online activism and data privacy. Monsanto is seeking the release of all lobby documents ... where the firm or its herbicide ingredient glyphosate have been mentioned. Avaaz says this would include personal information about its employees, as well as the email addresses of more than four million signatories to petitions against Monsantos GM and glyphosate policies. A victory for Monsanto in todays hearing would cost the online advocacy group thousands of person-hours of work time, and hundreds of thousands of dollars, according to Avaazs lawyers. It could even raise the prospect of a migration out of online activism by campaigners concerned about corporate surveillance. Monsantos [request] demands all documents Avaaz employees have created, maintained, received, sent or copied, where these involve discussion about glyphosate, Monsanto, or the World Health Organizations International Agency for Research on Cancer, which found glyphosate to probably be carcinogenic. Monsanto filed its request shortly after a bitter EU regulatory battle ended with its license for glyphosate the core ingredient in Roundup being extended by just five years, rather than the 15 years originally sought.
Note: Read more on Avaaz and the power of online activism. Major lawsuits are beginning to unfold over Monsanto's lies to regulators and the public on the dangers of its products, most notably Roundup. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and health.
The White House can now direct US intelligence agencies to spend money and take covert action without approval of congressional oversight committees under a provision slipped into the bill that ended the government shutdown, leaders of the Senate intelligence committee say. A provision in the bill - requested by the White House and Pentagon - gives intelligence agencies an exemption from the law that requires them to get authorization from the intelligence committees before they spend taxpayer money, said Sen. Richard Burr, R-N.C., and chairman of the Senate panel. Section 504 of the National Security Act gives the committees the power to withhold money from the intelligence agencies if they object to surveillance programs or other intelligence activities. Burr and [Sen. Mark] Warner said the provision to weaken their oversight power comes just after they promised civil liberties advocates in the Senate that they would ensure that the FBI and other intelligence agencies don't overstep their bounds in carrying out a controversial surveillance program recently renewed by Congress. That surveillance program, Section 702 of the Foreign Intelligence Surveillance Act ... sweeps up emails, text messages, photos and other communication from an unknown number of Americans, and allows federal agents to search that data without a warrant. Burr and Warner both supported a six-year renewal of the program earlier this month.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
The use of fake internet domain names to trick consumers into giving up personal information is more widespread than experts originally thought. This is largely because of the heightened use of Internationalized Domain Names (IDNs), which use homographs carefully crafted to look exactly like their English counterparts. Hackers create domain names that replace an English-language character with a look-alike character from another language - replacing the Latin letter a with the Cyrillic letter a, for instance - as a way of luring users to fake websites where theyre prompted to enter their personal information. [A new] report from ... Farsight Security identified 125 different websites, from social networking giants like Facebook and Twitter to luxury brands like Gucci and financial websites like Wells Fargo, being imitated by fake domain addresses. Between Oct. 17 and Jan. 10, the group observed more than 116,000 imitator domains of these sites in real time. Take a popular financial site like BankofAmerica.com. Cybercriminals take this domain and ... create a website that looks strikingly similar to the original Bank of America page. A user types in their login information and password on this fake Bank of America site, automatically giving cybercriminals their credentials to log in to the real thing. Most phishing attempts reach internet users through email, so you should be suspicious of any emails that include ... login links to different accounts combined with demands to update information.
Note: Read the complete Farsight Security report for more information on these common cyberattacks and how to protect yourself from them.
The Trump administration has declared all-out war on leakers. But the administration is battling the wrong enemy with the wrong weapons. Digital secrets stolen from the National Security Agency represent the real ... security problem. More than half a billion pages have been swiped. The stolen data includes some of the NSAs most prized cyber weapons. Most were created by the agencys own hacker team, the Tailored Access Operations (TAO) unit. Government hackers search for ways to crack into widely used computer operating systems, such as Microsoft Windows. When they discover a way in ... rather than notify the companies that their products are dangerously flawed, the NSA often secretly stores these vulnerabilities and later converts them into powerful cyber weapons, known as exploits. Like burglars tools, the exploits can secretly open a crack in a system, such as Windows, and insert an implant containing NSA malware - enabling the agency to take control of any computer using that Windows program. Unknown to the public, the NSA has for years been negligent in protecting its top-secret material, including these cyber weapons. Meanwhile, the Trump administration continues searching for someone who passed a few tidbits about White House bickering to a reporter, rather than focus on the NSA losing potentially deadly cyber weapons.
Note: In 2014, it was reported that the NSA was developing tools to make it relatively easy to hack millions of computers at once. Two years later, a large collection of NSA hacking tools was leaked. Now, these tools are being used by criminals against people all over the world. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
The FBI counterterrorism divisions identification of a movement it calls black identity extremists is the latest addition to the list of protesters and dissidents the agency puts under the domestic terrorism umbrella. But many national security experts say the designation [is] simply a label that allows the FBI to conduct additional surveillance on basically anyone whos black and politically active, said Michael German, who left the FBI in 2004. While the practice of labeling certain protest groups as domestic terrorists is not unique to President Trumps administration, Hina Shamsi ... at the American Civil Liberties Union, said theres concern that abusive and unjustified investigations by the FBI are rising. The problem, Shamsi said, is partly in the overly broad definition of domestic terrorism in the Patriot Act as a violation of the criminal laws ... intended to influence the policy of a government by intimidation or coercion. Eighty-four members of Congress cited that intention to intimidate or coerce in a letter to the Justice Department last week that asked whether the department had labeled Dakota Access Pipeline protesters domestic terrorists. The Justice Department did not respond to questions about the letter. The FBI report that focused on black identity extremists ... had interest groups questioning whether the designation has been used to single out members of Black Lives Matter.
Note: The Department of Homeland Security has reportedly been monitoring the Black Lives Matter movement since 2014, in some cases producing "minute-by-minute reports on protesters movements". For more along these lines, read about Cointelpro, the program used by corrupt intelligence agencies to spy on and attack the U.S. civil rights movement beginning in the 1960's. See also concise summaries of deeply revealing news articles about the erosion of civil liberties.
The US government is seeking to unmask every person who visited an anti-Trump website in what privacy advocates say is an unconstitutional fishing expedition for political dissidents. The warrant appears to be an escalation of the Department of Justices (DoJ) campaign against anti-Trump activities, including the harsh prosecution of inauguration day protesters. On 17 July, the DoJ served a website-hosting company, DreamHost, with a search warrant for every piece of information it possessed that was related to a website that was used to coordinate protests during Donald Trumps inauguration. The warrant ... seeks to get the IP addresses of 1.3 million people who visited [the site], as well as the date and time of their visit and information about what browser or operating system they used. The warrant was made public Monday, when DreamHost announced its plans to challenge the government in court. The government has aggressively prosecuted activists arrested during the 20 January protests in Washington DC. In April, the US attorneys office in Washington DC filed a single indictment charging more than 217 people with identical crimes, including felony rioting. The Electronic Frontier Foundation, which has been advising DreamHost, characterized the warrant as unconstitutional. I cant conceive of a legitimate justification other than casting your net as broadly as possible, senior staff attorney Mark Rumold [said]. What they would be getting is a list of everyone who has ever been interested in attending these protests.
Note: In May, United Nations officials said that the US treatment of activists was increasingly "incompatible with US obligations under international human rights law". For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the erosion of privacy.
The Federal Reserves little-known role housing the assets of other central banks comes with a unique benefit to the United States: It serves as a source of foreign intelligence for Washington. Senior officials from the U.S. Treasury and other government departments have turned to these otherwise confidential accounts several times a year to analyze the asset holdings of the central banks of Russia, China, Iraq, Turkey, Yemen, Libya and others, according to more than a dozen current and former senior Fed and Treasury officials. The U.S. central bank keeps a tight lid on information contained in these accounts. But according to the officials interviewed by Reuters, U.S. authorities regularly use a need to know confidentiality exception in the Feds service contracts with foreign central banks. Some 250 foreign central banks and governments keep $3.3 trillion of their assets at the Federal Reserve Bank of New York, about half of the worlds official dollar reserves, using a service advertised in a 2015 slide presentation as safe and confidential. Other major central banks and some commercial banks offer similar services. But only the Fed offers direct access to U.S. debt markets and to the worlds reserve currency, the dollar. In all, the people interviewed by Reuters identified seven instances in the last 15 years in which the accounts gave U.S. authorities insights into the actions of foreign counterparts or market movements, at times leading to a specific U.S. response.
Note: It's quite telling that no other major media picked up this important piece. For more along these lines, see concise summaries of deeply revealing news articles on financial industry corruption and the disappearance of privacy.
As grocery shoppers work to digest Amazons massive acquisition of Whole Foods for $13.7 billion, the digital storefront recently scored a victory that aims to reinforce the companys growing investments in brick-and-mortar retail. Amazon was awarded a patent May 30 that could help it choke off a common issue faced by many physical stores: Customers use of smartphones to compare prices even as they walk around a shop. But Amazon now has the technology to prevent that type of behavior when customers enter any of its physical stores and log onto the WiFi networks there. Titled Physical Store Online Shopping Control, Amazons patent describes a system that can identify a customers Internet traffic and sense when the smartphone user is trying to access a competitors website. When that happens, Amazon may take one of several actions. It may block access to the competitors site, preventing customers from viewing comparable products from rivals. It might redirect the customer to Amazons own site or to other, Amazon-approved sites. It might notify an Amazon salesperson to approach the customer. Or it might send the customers smartphone a text message, coupon or other information designed to lure the person back into Amazons orbit.
Note: For more along these lines, see concise summaries of deeply revealing corporate corruption news articles from reliable major media sources.
Your perceptions of the outside world arise through brain activity. Scientists in China have managed to reverse-engineer this process, using brain activity to guess what people are looking at. Their algorithm, which analyses functional MRI brain scans collected while volunteers gaze at digits and letters, is able to furnish uncannily clear depictions of the original images. It has been termed a mind-reading algorithm; a more accurate, though less catchy, description would be a reconstruction of visual field algorithm. The algorithm, called the Deep Generative Multiview Model, was highlighted this month by MIT Technology Review as an emerging technology to watch. What is true for the visual cortex is also true for our auditory systems: if you hear a song, the auditory part of your brain whirrs into action. Scientists in the US have developed a programme that can turn the associated firing of neurons back into real sounds. These technologies are turning thoughts into pictures and sounds. In short, science is coming remarkably close to being able to access what is inside our heads. If such algorithms were to find their way into advertising, we may find ourselves digitally stalked not only by images of hotels and consumer goods that we once clicked on, but also by pictures we glanced at or by songs that we streamed. This requires access to brain signals, but who would bet against such a future? Millions of people, by wearing fitness bands, sign up to having their physiological signals charted round the clock.
Note: Software breakthroughs like this have many potential benefits. But these new technologies may also be used for electronic harassment or mind control. And a 2008 US Defense Intelligence Agency report described the brain as the "battlefield of future".
Cybersecurity experts were shocked Tuesday when a sixth grader showed them just how easy it would be to hack their mobile devices and weaponize a seemingly innocuous item - in this case, his smart teddy bear. At a cyber safety conference in the Hague, Netherlands, 11-year-old prodigy Reuben Paul used a small computer called a "raspberry pi" to hack into audience members' bluetooth devices and download phone numbers. Paul then reportedly used one of the numbers to hack into the teddy bear, which connects to the Internet via Bluetooth or WiFi, and used the toy to record a message from the audience by using a computer language program called Python. "I basically showed how I could connect to [a remote Internet-connected device], and send commands to it," Paul told AFP. He warned that Internet-enabled everyday objects "can be used and weaponized to spy on us or harm us," for example by scraping private information like passwords. Toys could even be programmed to say "meet me at this location and I will pick you up," he added. Though not yet a teenager, Paul is already well known among his community in Austin, Texas, and beyond. In 2014, the wunderkind founded his own company, an educational gaming website called PrudentGames. Paul is now the company's CEO.
Note: An internet-connected toy doll was recently banned in Germany because it operates "as an espionage device". A 2015 New York Times article called "smart objects" a "train wreck in privacy and security". For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
Approximately half of adult Americans photographs are stored in facial recognition databases that can be accessed by the FBI, without their knowledge or consent, in the hunt for suspected criminals. About 80% of photos in the FBIs network are non-criminal entries, including pictures from drivers licenses and passports. The algorithms used to identify matches are inaccurate about 15% of the time, and are more likely to misidentify black people than white people. These are just some of the damning facts presented at last weeks House oversight committee hearing, where politicians and privacy campaigners criticized the FBI and called for stricter regulation of facial recognition technology at a time when it is creeping into law enforcement and business. The FBI first launched its advanced biometric database ... in 2010, augmenting the old fingerprint database with further capabilities including facial recognition. The bureau did not inform the public ... nor did it publish a privacy impact assessment, required by law, for five years. The FBI made arrangements with 18 different states to gain access to their databases of drivers license photos. Last year, the US government accountability office (GAO) analyzed the FBIs use of facial recognition technology and found it to be lacking in accountability, accuracy and oversight. It doesnt know how often the system incorrectly identifies the wrong subject, explained the GAOs Diana Maurer. Innocent people could bear the burden of being falsely accused.
Note: For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the disappearance of privacy.
WikiLeaks on Tuesday released a significant cache of documents that it said came from a high-security network inside the Central Intelligence Agency. WikiLeaks called the documents Vault 7, and they lay out the capabilities of the agencys global covert hacking program. By the end of 2016, the C.I.A. program had 5,000 registered users, including government employees and contractors, [and] had produced more than a thousand hacking systems. The files have circulated among former United States government hackers and contractors in an unauthorized manner, one of whom provided WikiLeaks with portions of the archive, WikiLeaks said. The software targeted by the hacking program included the most popular smartphone operating systems. Apples iPhone software ... was a particular target, including the development of several zero day exploits - a term for attacking coding flaws the company would not have known about. Googles Android ... received even more attention. By 2016, the C.I.A. had 24 weaponized Android zero day software programs. The C.I.A. also targeted ... internet-connected computers and home and industrial devices running the Linux operating system. In 2010, the Obama administration promised to disclose newly discovered vulnerabilities to companies like Apple, Google and Microsoft. But the WikiLeaks documents indicate that the agency found security flaws, kept them secret and then used them for surveillance and intelligence gathering.
Note: See the wikileaks webpage summarizing this most important leak. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
Foreign travelers will now be asked to provide links to their social media accounts before they enter the U.S. after the government implemented a new policy designed to identify potential threats. The request to provide links to accounts on Facebook, Twitter, YouTube, Instagram, Google+ and LinkedIn is optional. But privacy advocates and some technology companies oppose the move on the grounds it violates civil liberties and freedom of expression. The new policy, which was originally proposed this summer, was adopted Dec. 19 for people arriving via the ... Electronic System for Travel Authorization, which now asks about social media accounts in its online form. There is no clear indication of how the information gathered will be used. An open-ended inquiry into online presence would give DHS a window into applicants private lives, a coalition of 28 civil rights and technology groups wrote in a letter in August in opposition to the proposal. Scrutiny of their sensitive or controversial online profiles would lead many visa-waiver applicants to self-censor or delete their accounts, with consequences for personal, business, and travel-related activity. The risk of discrimination based on analysis of social media content and connections is great and will fall hardest on Arab and Muslim communities, the letter said. It also poses significant risks to journalists, whose profession requires confidentiality and whose social media networks may convey a profile that, taken out of context, could be misconstrued.
Note: For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the erosion of privacy.
In the trove of documents provided by former National Security Agency contractor Edward Snowden is a treasure. It begins with a riddle: “What do the President of Pakistan, a cigar smuggler, an arms dealer, a counterterrorism target, and a combatting proliferation target have in common? They all used their everyday GSM phone during a flight.” This riddle appeared in 2010 in SIDtoday, the internal newsletter of the NSA’s Signals Intelligence Directorate, or SID, and it was classified “top secret.” It announced the emergence of a new field of espionage that had not yet been explored: the interception of data from phone calls made on board civil aircraft. In a separate internal document from a year earlier, the NSA reported that 50,000 people had already used their mobile phones in flight as of December 2008, a figure that rose to 100,000 by February 2009. In a 2012 presentation, Government Communications Headquarters, or GCHQ ... disclosed a program called “Southwinds,” which was used to gather all the cellular activity, voice communication, data, metadata, and content of calls on board commercial aircraft. To spy on a telephone, all that was required was that the aircraft be cruising at an altitude above 10,000 feet. Today, approximately 100 companies permit in-flight use of telephones. This will further extend the scope of espionage by providing a pool of potential targets comprising several hundreds of thousands of people. This implies a population that goes far beyond terrorist targets.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Investigators pursuing what they believe to be the largest case of mishandling classified documents in United States history have found that the huge trove of stolen documents in the possession of a National Security Agency contractor included top-secret N.S.A. hacking tools that two months ago were offered for sale on the internet. They have been hunting for electronic clues that could link those cybertools - computer code posted online for auction by an anonymous group calling itself the Shadow Brokers - to the home computers of the contractor, Harold T. Martin III, who was arrested in late August. But so far, the investigators have been frustrated in their attempt to prove that Mr. Martin deliberately leaked or sold the hacking tools. Mr. Martin ... has insisted that he got in the habit of taking material home so he could improve his skills and be better at his job. The material the F.B.I. found in his possession added up to many terabytes of information ... which would make it by far the largest unauthorized leak of classified material from the classified sector. That volume dwarfs the hundreds of thousands of N.S.A. documents taken by Edward J. Snowden. [Mr. Martin] long held a high-level clearance and for a time worked with the N.S.A.s premier hacking unit, called Tailored Access Operations, which breaks into the computer networks of foreign countries and which developed the hacking tools.
Note: It was reported in 2014 that the NSA had developed specialized tools to covertly hack into computers on a mass scale by using automated systems. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
Years before anyone had ever heard of [Edward] Snowden, [Bill] Binney, a gifted cryptologist and mathematician, was pushing back against the NSAs spying overreach. In October 2001 ... he resigned rather than participate in a clandestine, massively overpriced and questionably legal electronic spying system code-named Trailblazer. Eventually, the government came after him. [Binney] was thrilled by [Oliver] Stones powerful biopic of Snowden, who astounded the world with his massive exposure of the NSAs global spying programs. "I think it will help people understand what is really going on behind the scenes. They are invading the privacy of everyone," he says. "They can turn on your cellphone and listen to you. They can turn on your camera and watch you." In 2013 ... James Clapper, the director of national intelligence, [lied] under oath during a congressional hearing about the NSAs spying programs. Snowden was watching. He had also seen what had happened to Binney and fellow NSA executives Thomas Drake, Ed Loomis and Kirk Wiebe, whose homes were raided by FBI agents after The New York Times exposed the NSAs secret spying programs in 2005. Drake, prosecuted under the 1917 Espionage Act, was eventually acquitted ... but his career was ruined. [Snowden's] critics insist he should have pursued his complaints internally, despite the persuasive examples of Binney and his comrades that such resistance is futile, even risky.
Note: Watch a free trailer or rent the whole documentary on this webpage. Read a revealing, detailed New York Times article on Oliver Stone and his profound work to expose corruption and manipulation through film. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
Oliver Stone has taken aim at the US government for deceiving people about the levels of surveillance that exist in the country. His new film Snowden, about the controversial NSA informant Edward Snowden, received its world premiere. The drama ... tells of the former CIA employees discovery that the agency had constructed a system to spy on the public. Americans dont know anything about it because the government lies about it all the time, Stone said at a press conference. Whats going on now is pretty shocking. This story not only deals with eavesdropping but mass eavesdropping, drones and cyberwarfare. As Snowden said himself the other day, Its out of control, the world is out of control. The film also features a cameo from Snowden himself, who still resides at an undisclosed location in Russia while he searches for asylum elsewhere. Stone hopes that he may return to US ground but is doubtful. Obama could pardon him and we hope so, he said. But he has vigorously prosecuted eight whistleblowers under the espionage act, which is an all-time record for an American president, and hes been one of the most efficient managers of this surveillance world. It is the most extensive and invasive surveillance state that has ever existed and hes built it up. The film-maker ... likens [the current situation] to a George Orwell novel. I never thought this could happen, he said. But from 2001 on, its very clear that something radical has changed. Theres more to it that meets the eye and whatever they tell you, youve got to look beyond.
Note: For more along these lines, see concise summaries of deeply revealing news articles on questionable intelligence agency practices and the disappearance of privacy.
June 6 will be the third anniversary of The Guardians publication of top-secret documents provided by [Edward] Snowden that showed that the National Security Agency was collecting the telephone records of tens of millions of Americans. Mr. Snowden [has been] denounced ... as a traitor. [Former Secretary of State Hillary] Clinton said in a Democratic presidential debate [that], He could have gotten all of the protections of being a whistle-blower. Thomas Drake would disagree. Mr. Drake was a senior N.S.A. official who had also complained, 12 years earlier, about warrantless surveillance. He went up the chain of command [to] the Defense Departments Office of Inspector General. Things did not go well. F.B.I. agents raided his house. He was forced to resign and was indicted on 10 felony charges arising from an alleged scheme to improperly retain and disclose classified information. He ultimately pleaded guilty to a misdemeanor for exceeding authorized use of a government computer in exchange for the governments dropping the other charges. He now works at an Apple store. Mr. Snowden followed the Drake case closely in the news media and drew the obvious conclusion: Going through [official] channels was worse than a dead end. [John] Crane, a former assistant inspector general in the Defense Department who oversaw the whistle-blower program, has now come forward alleging that Mr. Drake was persecuted by the very officials in his office who were supposed to protect him.
Note: John Crane was forced out of the Pentagon in 2013. His story is told in a new book, titled, Bravehearts: Whistle Blowing In The Age of Snowden by Mark Hertsgaard. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
Edward Snowden has called for a complete overhaul of US whistleblower protections after a new source from deep inside the Pentagon came forward with a startling account of how the system became a trap for those seeking to expose wrongdoing. The account of John Crane ... appears to undermine Barack Obama, Hillary Clinton and [others] who argue that there were established routes for Snowden other than leaking to the media. Crane, a longtime assistant inspector general at the Pentagon, has accused his old office of retaliating against a major surveillance whistleblower, Thomas Drake. Not only did Pentagon officials provide Drakes name to criminal investigators, Crane told the Guardian, they destroyed documents relevant to his defence. Thomas Drakes legal ordeal ruined him financially. His case served as a prologue to Snowdens. In 2002, Drake and NSA colleagues contacted the Pentagon inspector general to blow the whistle on [a] tool, Trailblazer, for mass-data analysis. Crane, head of the offices whistleblower unit, assigned investigators. For over two years, with Drake as a major source, they ... prepared a lengthy secret report [that] eventually [helped] to kill the program. As far as Crane was concerned, the whistleblower system was working. But after an aspect of the NSAs warrantless mass surveillance leaked to the New York Times, Drake himself came under investigation and eventually indictment [for] hoarding documentation exactly what inspector-general investigators tell their whistleblowers to do.
Note: John Crane was forced out of the Pentagon in 2013. His story is told in a new book, titled, Bravehearts: Whistle Blowing In The Age of Snowden by Mark Hertsgaard. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
A national debate has played out over mass surveillance by the National Security Agency. [Meanwhile], a new generation of technology ... has given local law enforcement officers unprecedented power to peer into the lives of citizens. The powerful systems also have become flash points for civil libertarians and activists. This is something thats been building since September 11, said Jennifer Lynch, a senior staff attorney at the Electronic Frontier Foundation. First funding went to the military to develop this technology, and now it has come back to domestic law enforcement. Its the perfect storm of cheaper and easier-to-use technologies and money from state and federal governments to purchase it. But perhaps the most controversial and revealing technology is the threat-scoring software Beware. As officers respond to calls, Beware automatically runs the address. The searches return the names of residents and scans them ... to generate a color-coded threat level for each person or address: green, yellow or red. Exactly how Beware calculates threat scores is something that its maker, Intrado, considers a trade secret, so ... only Intrado - not the police or the public - knows how Beware tallies its scores. The system might mistakenly increase someones threat level by misinterpreting innocuous activity on social media, like criticizing the police, and trigger a heavier response by officers.
Note: For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the disappearance of privacy.
The Federal Bureau of Investigation has used a secretive authority to compel Internet and telecommunications firms to hand over customer data including an individuals complete web browsing history and records of all online purchases, a court filing released Monday shows. The documents are believed to be the first time the government has provided details of its so-called national security letters, which are used by the FBI to conduct electronic surveillance without the need for court approval. National security letters have been available as a law enforcement tool since the 1970s, but their frequency and breadth expanded dramatically under the USA Patriot Act, which was passed shortly after the Sept. 11, 2001 attacks. They are almost always accompanied by an open-ended gag order barring companies from disclosing the contents of the demand for customer data. The secretive orders have long drawn the ire of tech companies and privacy advocates, who argue NSLs allow the government to snoop on user content without appropriate judicial oversight. Last year, the Obama administration announced it would permit Internet companies to disclose more about the number of NSLs they receive. But they can still only provide a range such as between 0 and 999 requests. Twitter has sued in federal court seeking the ability to publish more details in its semi-annual transparency reports. Several thousand NSLs are now issued by the FBI every year. At one point that number eclipsed 50,000 letters annually.
Note: Read more about the FBI's use of these controversial secret letters. For more along these lines, see concise summaries of deeply revealing civil liberties news articles from reliable major media sources.
An elite group of security technologists has concluded that the American and British governments cannot demand special access to encrypted communications without putting the worlds most confidential data and critical infrastructure in danger. With security breaches and awareness of nation-state surveillance at a record high and data moving online at breakneck speeds, encryption has emerged as a major issue in the debate over privacy rights. Technology companies ... have been moving to encrypt more of their corporate and customer data after learning that the National Security Agency and its counterparts were siphoning off digital communications and hacking into corporate data centers. In Britain, Prime Minister David Cameron threatened to ban encrypted messages altogether. In the United States, Michael S. Rogers, the director of the N.S.A., proposed that technology companies be required to create a digital key to unlock encrypted data. The [technology group's] new paper is the first in-depth technical analysis of government proposals by leading cryptographers and security thinkers. In the report, the group said any effort to give the government exceptional access to encrypted communications ... would leave confidential data and critical infrastructure like banks and the power grid at risk. With government agency breaches now the norm, the security specialists said authorities could not be trusted to keep such keys safe from hackers and criminals.
Note: For more along these lines, see concise summaries of deeply revealing news articles about corrupt intelligence agencies that erode privacy rights in the U.S. and elsewhere
Three days after the New York Times revealed that the U.S. government was secretly monitoring the calls and emails of people inside the United States without court-approved warrants, the National Security Agency issued a top-secret assessment of the damage done to intelligence efforts by the story. The conclusion: the information could lead terrorists to try to evade detection. Yet the agency gave no specific examples of investigations that had been jeopardized. The December 2005 bombshell story, by James Risen and Eric Lichtblau, set off a debate about the George W. Bush administration's expansion of spying powers after the 9/11 attacks, and also about the Times editors' decision to delay its publication for a year. White House officials had warned the Times that revealing the program would have grave consequences for national security. "To this day we've never seen any evidence despite all the claims they made to keep us from publishing that it did any tangible damage to national security, " Lichtblau told The Intercept. "The reality was that the story ... didn't tell terrorists anything that they didn't know," he said. The NSA's damage assessment on the article ... is among the files provided by former NSA contractor Edward Snowden. The memo recounts meetings in 2004 and 2005 in which administration officials disclosed "certain details of the special program to select individuals from the New York Times to dissuade them from publishing a story on the program at that time."
Note: You can read the revealing memo mentioned at the link above. For more along these lines, see concise summaries of deeply revealing news articles on civil liberties from reliable major media sources. Then explore the excellent, reliable resources provided in our Media Information Center.
The National Security Agency and its closest allies planned to hijack data links to Google and Samsung app stores to infect smartphones with spyware, a top-secret document reveals. The surveillance project was launched by a joint electronic eavesdropping unit called the Network Tradecraft Advancement Team, which includes spies from each of the countries in the Five Eyes alliance the United States, Canada, the United Kingdom, New Zealand and Australia. The top-secret document, obtained from NSA whistleblower Edward Snowden ... outlines a series of tactics that the NSA and its counterparts in the Five Eyes were [using, which included] a method to hack and hijack phone users connections to app stores so that they would be able to send malicious implants to targeted devices. The implants could then be used to collect data from the phones without their users noticing. The agencies ... were also keen to find ways to hijack [app stores] as a way of sending selective misinformation to the targets handsets as part of so-called effects operations that are used to spread propaganda or confuse adversaries. Moreover, the agencies wanted to gain access to companies app store servers so they could secretly use them for harvesting information about phone users. The revelations are the latest to highlight tactics adopted by the Five Eyes agencies. Last year, The Intercept reported that the NSA ... was shown to have masqueraded as a Facebook server in order to hack into computers.
Note: For more along these lines, see concise summaries of deeply revealing news articles about corruption in the intelligence community and the manipulation of public perception.
Human rights campaigners have prepared a federal lawsuit aiming to permanently shut down the bulk collection of billions of US phone records not, this time, by the National Security Agency, but by the Drug Enforcement Agency. The program ... served as a template for the NSAs gigantic and ongoing bulk surveillance of US phone data after 9/11. The revelation of mass phone-records collection in the so-called war on drugs raises new questions about whether the Obama administration or its successors believe US security agencies continue to have legal leeway for warrantless bulk surveillance on American citizens. Starting in 1992, the so-called USTO effort operated without judicial approval, despite the US constitutions warrant requirement. Attorney general Eric Holder ended USTO in September 2013 out of fear of scandal following Snowdens disclosures. While Snowden did not expose USTO, several NSA programs he has exposed referenced the DEA as an NSA partner, giving the DEA another secret pathway to massive amounts of US communications records. The warrantless bulk records collection provides prosecutors the ability to enter into evidence incriminating material that could otherwise be thrown out of court, [and] has not stopped the upward growth of domestic narcotics consumption.
Note: In order to deny due process to people accused of crimes, the DEA's Special Operations Division constructs lies about the origins of data obtained from warrantless mass surveillance. Award-winning journalists have presented powerful evidence of direct DEA and CIA involvement in and support of drug running and drug cartels. For more along these lines, see concise summaries of deeply revealing news articles about corruption in government and in the intelligence community.
A powerful new surveillance tool being adopted by police departments across the country comes with an unusual requirement: To buy it, law enforcement officials must sign a nondisclosure agreement preventing them from saying almost anything about the technology. Any disclosure about the technology, which tracks cellphones and is often called StingRay, could allow criminals and terrorists to circumvent it, the F.B.I. has said in an affidavit. But the tool is adopted in such secrecy that communities are not always sure what they are buying or whether the technology could raise serious privacy concerns. What has opponents particularly concerned about StingRay is that the technology, unlike other phone surveillance methods, can also scan all the cellphones in the area where it is being used, not just the target phone. Its scanning the area. What is the government doing with that information? said Linda Lye, a lawyer for the American Civil Liberties Union of Northern California, which in 2013 sued the Justice Department to force it to disclose more about the technology. In November, in a response to the lawsuit, the government said it had asked the courts to allow the technology to capture content, not just identify subscriber location.
Note: For more along these lines, see concise summaries of deeply revealing news articles about the erosion of privacy rights from reliable major media sources.
Many Samsung "SmartTVs" come equipped with voice recognition, which allows you to bark commands at your TV. Since the television is always listening for your voice, Samsung has warned its SmartTV customers that every word is being captured and sent over the Internet. Samsung says it needs to send your voice commands to a third-party, because that company converts your speech to text. But Samsung also collects your voice commands to perform research and determine whether it needs to make improvements to the feature. Samsung noted that a microphone appears on the screen when the voice recognition feature is turned on, notifying customers that their voice is being captured. You can opt-out of the SmartTV voice recognition feature. But even if you opt out, your voice commands will still be captured. The SmartTV has a set of pre-programmed commands that it recognizes even if you opt out of voice recognition. Samsung will collect the text of those pre-programmed voice commands (though not your voice itself) and analyze how much you're using certain commands. "Samsung does not retain voice data or sell it to third parties," the company said in a statement. "If a consumer consents and uses the voice recognition feature ... the voice data is sent to a server, which searches for the requested content then returns the desired content to the TV."
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
Former CBS News correspondent Sharyl Attkisson has sued the Justice Department over the hacking of her computers, officially accusing the Obama administration of illegal surveillance while she was reporting on administration scandals. In a series of legal filings that seek $35 million in damages, Attkisson alleges that three separate computer forensic exams showed that hackers used sophisticated methods to surreptitiously monitor her work between 2011 and 2013. The intruders installed and periodically refreshed software to steal data and obtain passwords on her home and work computers. She also charges that the hackers monitored her audio using a Skype account. The award-winning reporter says she and her attorneys have "pretty good evidence" that these efforts were "connected" to the Justice Department. She said she was caught in a "Catch-22," forcing her to use the lawsuit and an administrative complaint to discover more about the surveillance through the discovery process and to learn the identities of the "John Does" named in the complaints. Attkisson learned through a Freedom of Information request that the FBI opened an investigation of the hacking case in May 2013, but says the bureau never interviewed her or even notified her of the probe. Attkisson resigned from CBS last March after complaining that she was increasingly unable to get her investigative stories on the air. She has published a best-selling book, "Stonewalled," about her battles against the network and the administration.
Note: Fox News was the only major media to cover this important case. Read a judge's supportive comments about this important case on Ms. Attkisson's website. For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the disappearance of privacy.
The director of the FBI savaged tech companies for their recent embrace of end-to-end encryption and suggested rewriting laws to ensure law enforcement access to customer data in a speech on Thursday. James Comey said data encryption such as that employed on Apples latest mobile operating system would deprive police and intelligence companies. Privacy advocates contend Comey is demagoguing the issue. It took a June supreme court ruling, they point out, for law enforcement to abandon its contention that it did not require warrants at all to search through smartphones or tablets, and add that technological vulnerabilities can be exploited by hackers and foreign intelligence agencies as well as the US government. Tech companies contend that their newfound adoption of encryption is a response to overarching government surveillance, much of which occurs ... without a warrant, subject to a warrant broad enough to cover indiscriminate data collection, or under a gag order following a non-judicial subpoena. Comey did not mention such subpoenas, often in the form of National Security Letters, in his remarks. Comey acknowledged that the Snowden disclosures caused justifiable surprise among the public about the breadth of government surveillance, but hoped to mitigate it through greater transparency and advocacy. Yet the FBI keeps significant aspects of its surveillance reach hidden even from government oversight bodies. Intelligence officials said in a June letter to a US senator that the FBI does not tally how often it searches through NSAs vast hoards of international communications, without warrants, for Americans identifying information. Comey frequently described himself as being technologically unprepared to offer specific solutions, and said he meant to begin a conversation, even at the risk of putting American tech companies at a competitive disadvantage.
Note: For more along these lines, see concise summaries of deeply revealing stories about questionable intelligence agency practices from reliable sources.
[National security letters], the reach of which was expanded under the Patriot Act in 2001, let the FBI get business records from telephone, banking, and Internet companies with just a declaration that the information is relevant to a counterterrorism investigation. The FBI can get such information with a subpoena or another method with some judicial oversight. Can the government make demands for data entirely in secret? That was the question yesterday before a federal appeals court in San Francisco, where government lawyers argued that National Security Letters FBI requests for information that are so secret they cant be publicly acknowledged by the recipients were essential to counterterrorism investigations. One of the judges seemed to question why there was no end-date on the gag orders, and why the burden was on the recipients of NSLs to challenge them. It leaves it to the poor person who is subject to those requirements to just constantly petition the government to get rid of it, said the judge, N. Randy Smith. The FBI sends out thousands of NSLs each year 21,000 in fiscal year 2012. Google, Yahoo, Facebook and Microsoft filed a brief in support of the NSL challenge, arguing that they want to publish more detailed aggregate statistics about the volume, scope and type of NSLs that the government uses to demand information about their users. Twitter also announced this week that it was suing the U.S. government over restrictions on how it can talk about surveillance orders. Tech companies can currently make public information about the number of NSLs or Foreign Intelligence Surveillance Court orders they receive in broad ranges, but Twitter wants to be more specific.
Note: For more along these lines, see concise summaries of deeply revealing civil liberties news articles from reliable major media sources.
Could your smartphone be recording video of you without you knowing it? And if so, who is on the other end watching it? A new Facebook Messenger App could be violating your privacy. If you download and install the social network's new messenger app to an android device, you're giving Facebook permission to call or text people from your phone, delete your personal data even access your camera microphone. Facebook says it only needs that access to make your messaging experience better, and that these terms have been in place for months. So why are we telling you about it now? That's because some mobile Facebook users are about to find out you won't be able to access your messages through the Facebook app anymore. Instead if you want to read a message from a friend or coworker you'll have to download the messenger app and consent to any fine print. The messenger app has over 6000 reviews on the iTunes app store. Most of them are not too positive. The real question is will people still download it? And as for the people who did download it, it seems a lot are just choosing to disconnect.
Note: Many apps have terms and conditions that people never read before downloading the allow the app developer to access and even change phone logs, record conversations, and much more. Learn more in this eye-opening video. For more along these lines, see concise summaries of deeply revealing news articles about the erosion of privacy rights from reliable major media sources.
Development of a U.S. counterattack for cyberterrorism that could do more harm than good was one of the final events that drove Edward Snowden to leak government secrets, the former National Security Agency contractor tells Wired magazine. Snowden ... said the MonsterMind program was designed to detect a foreign cyberattack and keep it from entering the country. But it also would automatically fire back. The problem, he said, is malware can be routed through an innocent third-party country. "These attacks can be spoofed," he told Wired. MonsterMind for example ... could accidentally start a war. And it's the ultimate threat to privacy because it requires the NSA to gain access to virtually all private communications coming in from overseas. "The argument is that the only way we can identify these malicious traffic flows and respond to them is if we're analyzing all traffic flows," he said. "And if we're analyzing all traffic flows, that means we have to be intercepting all traffic flows. That means violating the Fourth Amendment, seizing private communications without a warrant, without probable cause or even a suspicion of wrongdoing. For everyone, all the time. You get exposed to a little bit of evil, a little bit of rule-breaking, a little bit of dishonesty, a little bit of deceptiveness, a little bit of disservice to the public interest, and you can brush it off, you can come to justify it," Snowden told Wired. "But if you do that, it creates a slippery slope that just increases over time. And by the time you've been in 15 years, 20 years, 25 years, you've seen it all and it doesn't shock you. And so you see it as normal."
Note: Read the cover story from Wired magazine with a deep inside report on Snowden.
Bill Binney worked at the National Security Agency [for] nearly three decades as one of its leading crypto-mathematicians. He then became one of its leading whistleblowers. The NSA is overseen by Congress, the courts and other government departments. It's also supposed to be watched from the inside by its own workers. But over the past dozen years, whistleblowers like Binney have had a rough track record. Those who tried unsuccessfully to work within the system say Edward Snowden the former National Security Agency contractor who shared top-secret documents with reporters learned from their bitter experience. For Binney, the decision to quit the NSA and become a whistleblower began a few weeks after the terrorist attacks of Sept. 11, 2001, when he says he discovered the spy agency had begun using software he'd created to scoop up information on Americans all without a court order. "I had to get out of there, because they were using the program I built to do domestic spying, and I didn't want any part of it, I didn't want to be associated with it," he says. "I look at it as basically treason. They were subverting the Constitution." Binney says he and two other NSA colleagues who also quit tried sounding the alarm with congressional committees. But because they did not have documents to prove their charges, nobody believed them. Snowden, he says, did not repeat that mistake. "He recognized right away, it was very clear to me, that if he wanted anybody to believe him, he'd have to take a lot of documentation with him which is what he did," Binney says.
Note: For more on this, see concise summaries of deeply revealing intelligence agency operations news articles from reliable major media sources.
When Australia's Susie O'Neill claimed the gold medal at the 1996 Atlanta Olympics, she dedicated her victory to Scott Volkers, the swimming coach who had taken over her training two years earlier. By this time, three women who had been Volkers' students were losing belief in themselves and the swimming community. Julie Gilbert, Kylie Rogers and Simone Boyce took the stand at the royal commission into child abuse in Sydney this week to describe their mental breakdowns, eating disorders, anxiety and isolation from a swimming hierarchy that refused to believe them or failed to explore the possibility that Volkers molested them as girls aged 12 to 18 in the 1980s. Volkers remained on the payroll of elite Australian swimming institutions until 2010, when he was finally forced to move to Brazil, where he still works as a leading coach. Was it Australia's win-at-all-costs swimming culture that kept him in the presence of young athletes? An exasperated Andrew Boe, the lawyer representing Gilbert, Rogers and Boyce, pointed out: "This is not an examination of whether he was a good swimming coach or not." Nor is it an examination of the guilt or innocence of Volkers against whom charges concerning these three alleged victims were dropped in 2002 or other swimming coaches. It is an inquiry into the institutional responses to abuse. Swimming Australia's association with Volkers [ended] in 2005, when the coach's fourth accuser came forward with claims that Volkers had groped her breasts and attempted to stimulate her vagina in the late 1990s, when she was 15. The allegations were very similar to the earlier cases.
Note: For more on this, see concise summaries of deeply revealing sexual abuse scandals news articles from reliable major media sources.
The Supreme Court unequivocally ruled [on June 25] that privacy rights are not sacrificed to 21st-century technology, saying unanimously that police generally must obtain a warrant before searching the cellphone of someone they arrest. While the specific protection may not affect the average American, the court made a bold statement that the same concern about government prying that animated the nations birth applies to the abundance of digital information about an individual in the modern world. Modern cellphones hold for many Americans the privacies of life, Chief Justice John G. Roberts Jr. wrote for a court united behind the opinions expansive language. The fact that technology now allows an individual to carry such information in his hand does not make the information any less worthy of the protection for which the Founders fought. Roberts said that in most cases when police seize a cellphone from a suspect, the answer is simple: Get a warrant. The ruling has no impact on National Security Agency data-collection programs revealed in the past year or law enforcement use of aggregated digital information. But lawyers involved in those issues said the emphatic declarations signaled the justices interest in the dangers of government overreach. Stephen Vladeck, a law professor at American University, said the decision is more than simply a warning to government officials employing high-tech forms of government surveillance. This is a cruise missile across the bow of lawyers defending warrantless search programs, Vladeck said.
Note: For more on this, see concise summaries of deeply revealing privacy news articles from reliable major media sources.
The National Security Agency is harvesting huge numbers of images of people from communications that it intercepts through its global surveillance operations for use in sophisticated facial recognition programs, according to top-secret documents. The spy agencys reliance on facial recognition technology has grown significantly over the last four years as the agency has turned to new software to exploit the flood of images included in emails, text messages, social media, videoconferences and other communications. Agency officials believe that technological advances could revolutionize the way that the N.S.A. finds intelligence targets around the world. The agencys ambitions for this highly sensitive ability and the scale of its effort have not previously been disclosed. The agency intercepts millions of images per day including about 55,000 facial recognition quality images which translate into tremendous untapped potential, according to 2011 documents obtained from the former agency contractor Edward J. Snowden. It is not clear how many people around the world, and how many Americans, might have been caught up in the effort. Neither federal privacy laws nor the nations surveillance laws provide specific protections for facial images. Civil-liberties advocates and other critics are concerned that the power of the improving technology, used by government and industry, could erode privacy. Facial recognition can be very invasive, said Alessandro Acquisti, a researcher on facial recognition technology at Carnegie Mellon University.
Note: For another New York Times article showing how the NSA is using mobile phone apps to "snatch data revealing the players location, age, sex and other personal information," see this article.
The National Security Agency is secretly intercepting, recording, and archiving the audio of virtually every cell phone conversation on the island nation of the Bahamas. According to documents provided by NSA whistleblower Edward Snowden, the surveillance is part of a top-secret system code-named SOMALGET that was implemented without the knowledge or consent of the Bahamian government. SOMALGET is part of a broader NSA program called MYSTIC, which ... is being used to secretly monitor the telecommunications systems of the Bahamas and several other countries, including Mexico, the Philippines, and Kenya. But while MYSTIC scrapes mobile networks for so-called metadata information that reveals the time, source, and destination of calls SOMALGET is a cutting-edge tool that enables the NSA to vacuum up and store the actual content of every conversation in an entire country. The program raises profound questions about the nature and extent of American surveillance abroad. The U.S. intelligence community routinely justifies its massive spying efforts by citing the threats to national security posed by global terrorism and unpredictable rival nations like Russia and Iran. But the NSA documents indicate that SOMALGET has been deployed in the Bahamas to locate international narcotics traffickers and special-interest alien smugglers traditional law-enforcement concerns, but a far cry from derailing terror plots or intercepting weapons of mass destruction.
Note: For more on the realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
The opportunity those in power have to characterise political opponents as "national security threats" or even "terrorists" has repeatedly proven irresistible. In the past decade, the government ... has formally so designated environmental activists, broad swaths of anti-government rightwing groups, anti-war activists, and associations organised around Palestinian rights. One document from the Snowden files, dated 3 October 2012, chillingly underscores the point. It revealed that the agency has been monitoring the online activities of individuals it believes express "radical" ideas and who have a "radicalising" influence on others. Among the information collected about the individuals, at least one of whom is a "US person", are details of their online sex activities and "online promiscuity." The agency discusses ways to exploit this information to destroy their reputations and credibility. The record is suffused with examples of groups and individuals being placed under government surveillance by virtue of their dissenting views and activism Martin Luther King, the civil rights movement, anti-war activists, environmentalists. The NSA's treatment of Anonymous ... is especially troubling and extreme. Gabriella Coleman, a specialist on Anonymous at McGill University, said that [Anonymous] "is not a defined" entity but rather "an idea that mobilises activists to take collective action and voice political discontent. It is a broad-based global social movement with no centralised or official organised leadership structure. Some have rallied around the name to engage in digital civil disobedience, but nothing remotely resembling terrorism."
Note: This excerpt is from the new book No Place to Hide by Glenn Greenwald. For more on government surveillance, see the deeply revealing reports from reliable major media sources available here.
When NSA contractor Edward Snowden downloaded tens of thousands of top-secret documents from a highly secure government network, it led to the largest leak of classified information in history and sparked a fierce debate over privacy, technology and democracy in the post-9/11 world. Now, in "United States Of Secrets," FRONTLINE goes behind the headlines to reveal the dramatic inside story of how the U.S. government came to monitor and collect the communications of millions of people around the worldincluding ordinary Americansand the lengths they went to trying to hide the massive surveillance program from the public. This is as close to the complete picture as anyone has yet put together and its bigger and more pervasive than we thought, says veteran FRONTLINE filmmaker Michael Kirk. In part one ... Kirk [pieces] together the secret history of the unprecedented surveillance program that began in the wake of September 11 and continues today even after the revelations of its existence by Edward Snowden. Then, in part two, premiering Tuesday, May 20 ..., veteran FRONTLINE filmmaker Martin Smith continues the story, exploring the secret relationship between Silicon Valley and the National Security Agency, and investigating how the government and tech companies have worked together to gather and warehouse your data. Through in-depth interviews with more than 60 whistleblowers, elected officials, journalists, intelligence insiders and cabinet officials, we have woven together the secret narrative that reveals the scale and scope of the governments spying program, says Kirk.
Note: Don't miss this engaging program, available at this link. For more on government surveillance, see the deeply revealing reports from reliable major media sources available here.
On Sunday 9 June 2013, the Guardian published the story that revealed [Edward] Snowden to the world. The article told Snowden's story, conveyed his motives, and proclaimed that "Snowden will go down in history as one of America's most consequential whistleblowers, alongside Daniel Ellsberg and Bradley [now Chelsea] Manning." We quoted [a note from Snowden that said:] "I understand that I will be made to suffer for my actions but I will be satisfied if the federation of secret law, unequal pardon and irresistible executive powers that rule the world that I love are revealed even for an instant." The reaction to the article and the video was more intense than anything I had experienced as a writer. Ellsberg himself, writing the following day in the Guardian, proclaimed that "there has not been in American history a more important leak than Edward Snowden's release of NSA material and that definitely includes the Pentagon Papers 40 years ago". Several hundred thousand people posted the link to their Facebook accounts in the first several days alone. Almost three million people watched the interview on YouTube. Many more saw it on the Guardian's website. The overwhelming response was shock and inspiration at Snowden's courage.
Note: Don't miss the full, exciting story of how Snowden originally came to leak his stunning information at the link above. This excerpt is from the new book No Place to Hide by Glenn Greenwald. For more on government surveillance, see the deeply revealing reports from reliable major media sources available here.
Two news organizations' stories about National Security Agency surveillance, based upon documents leaked by Edward Snowden, have been awarded the Pulitzer Prize for public service, often described as the highest prize in American journalism. The Washington Post and ... The Guardian each received the prize on [April 14]. The recognition of the NSA reporting was most significant because of the questions raised by Snowden's leaks and the reaction to them. Snowden, who has been living in Russia while seeking asylum from U.S. prosecution, said in a statement that the Pulitzer board's recognition of the coverage was "vindication for everyone who believes that the public has a role in government." "We owe it to the efforts of the brave reporters and their colleagues who kept working in the face of extraordinary intimidation, including the forced destruction of journalistic materials, the inappropriate use of terrorism laws, and so many other means of pressure to get them to stop what the world now recognizes was work of vital public importance." While Snowden provided a trove of documents, reporters including Glenn Greenwald, working for the Guardian; Barton Gellman, working for The Post; and Laura Poitras, who worked with both, pored over the raw information, decided with their editors what parts were ethical to publish, and turned the information into stories that stunned readers around the world.
Note: For more on the historic Snowden revelations, see the deeply revealing reports from reliable major media sources available here.
This week, the Associated Press exposed a secret program run by the U.S. Agency for International Development to create a Twitter-like Cuban communications network run through secret shell companies in order to create the false appearance of being a privately owned operation. Unbeknownst to the services Cuban users was the fact that American contractors were gathering their private data in the hope that it might be used for political purposesspecifically, to manipulate those users in order to foment dissent in Cuba and subvert its government. This sort of operation is frequently discussed at western intelligence agencies, which have plotted ways to covertly use social media for propaganda, deception, mass messaging, and pushing stories. One previously undisclosed top-secret documentprepared by GCHQ for the 2010 annual SIGDEV gathering of the Five Eyes surveillance alliance comprising the UK, Canada, New Zealand, Australia, and the U.S.explicitly discusses ways to exploit Twitter, Facebook, YouTube, and other social media as secret platforms for propaganda. Those programs, carried out in secrecy and with little accountability ... threaten the integrity of the internet itself, as state-disseminated propaganda masquerades as free online speech and organizing. There is thus little or no ability for an internet user to know when they are being covertly propagandized by their government, which is precisely what makes it so appealing to intelligence agencies, so powerful, and so dangerous.
Note: For more on the realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
The National Security Agency has reportedly used automated systems to infect user computers with malware since 2010. At times the agency pretended to be Facebook to install its malware. The NSA has been using a program codenamed TURBINE to contaminate computers and networks with malware "implants" capable of spying on users, according to the Intercept, which cited documents provided by whistleblower Edward Snowden. Between 85,000 and 100,000 of these implants have been deployed worldwide thus far. To infect computers with malware, the NSA has relied on various tactics, including posing as Facebook. The federal agency performed what is known as a "man-on-the-side" attack in which it tricked users computers into thinking that they were accessing real Facebook servers. Once the user had been fooled, the NSA hacked into the user's computer and extracted data from their hard drive. Facebook said it had no knowledge of the NSA"s TURBINE program. However, [Facebook] said it is no longer possible for the NSA or hackers to attack users that way, but Facebook warned that other websites and social networks may still be vulnerable to those types of attacks. "This method of network level disruption does not work for traffic carried over HTTPS, which Facebook finished integrating by default last year," Facebook told the National Journal.
Note: For more on NSA surveillance, see the deeply revealing reports from reliable major media sources available here.
A federal judge in Newark has thrown out a lawsuit against the New York Police Department for spying on New Jersey Muslims, saying if anyone was at fault, it was the Associated Press for telling people about it. In his ruling ... U.S. District Court Judge William J. Martini simultaneously demonstrated the willingness of the judiciary to give law enforcement alarming latitude in the name of fighting terror, greenlighted the targeting of Muslims based solely on their religious beliefs, and blamed the media for upsetting people by telling them what their government was doing. The NYPDs clandestine spying on daily life in Muslim communities in the region with no probable cause, and nothing to show for it was exposed in a Pulitzer-Prize winning series of stories by the AP. The stories described infiltration and surveillance of at least 20 mosques, 14 restaurants, 11 retail stores, two grade schools, and two Muslim student associations in New Jersey alone. In a cursory, 10-page ruling issued before even hearing oral arguments, Martini essentially said that what the targets didnt know didnt hurt them: "None of the Plaintiffs injuries arose until after the Associated Press released unredacted, confidential NYPD documents and articles expressing its own interpretation of those documents. Nowhere in the Complaint do Plaintiffs allege that they suffered harm prior to the unauthorized release of the documents by the Associated Press. This confirms that Plaintiffs alleged injuries flow from the Associated Presss unauthorized disclosure of the documents. The harms are not fairly traceable to any act of surveillance."
Note: For more on government corruption, see the deeply revealing reports from reliable major media sources available here.
The National Security Agency has implanted software in nearly 100,000 computers around the world that allows the United States to conduct surveillance on those machines and can also create a digital highway for launching cyberattacks. While most of the software is inserted by gaining access to computer networks, the N.S.A. has increasingly made use of a secret technology that enables it to enter and alter data in computers even if they are not connected to the Internet, according to N.S.A. documents, computer experts and American officials. The technology, which the agency has used since at least 2008, relies on a covert channel of radio waves that can be transmitted from tiny circuit boards and USB cards inserted surreptitiously into the computers. In some cases, they are sent to a briefcase-size relay station that intelligence agencies can set up miles away from the target. In most cases, the radio frequency hardware must be physically inserted by a spy, a manufacturer or an unwitting user. Among the most frequent targets of the N.S.A. and its Pentagon partner, United States Cyber Command, have been units of the Chinese Army, which the United States has accused of launching regular digital probes and attacks on American industrial and military targets, usually to steal secrets or intellectual property. But the program, code-named Quantum, has also been successful in inserting software into Russian military networks and systems used by the Mexican police and drug cartels, trade institutions inside the European Union, and sometime partners against terrorism like Saudi Arabia, India and Pakistan.
Note: For more on government surveillance, see the deeply revealing reports from reliable major media sources available here.
National Security Agency leaker Edward Snowden wrote in a lengthy open letter to the people of Brazil that he has been inspired by the global debate ignited by his release of thousands of documents and that the NSAs culture of indiscriminate global espionage is collapsing. In the letter, Snowden commended the Brazilian government for its strong stand against U.S. spying. He wrote that he would be willing to help the South American nation investigate NSA spying on its soil but could not fully participate in doing so without being granted political asylum, because the U.S. government will continue to interfere with my ability to speak. The documents revealed that Brazil is the top NSA target in Latin America, in spying that has included the monitoring of Brazilian President Dilma Rousseffs cellphone and hacking into the internal network of the state-run oil company Petrobras. In his letter, Snowden dismissed U.S. explanations to the Brazilian government and others that the bulk metadata gathered on billions of e-mails and calls was more data collection than surveillance. There is a huge difference between legal programs, legitimate spying ... and these programs of dragnet mass surveillance that put entire populations under an all-seeing eye and save copies forever, he wrote. These programs were never about terrorism: theyre about economic spying, social control, and diplomatic manipulation. Theyre about power. Brazilian senators have asked for Snowdens help during hearings about the NSAs targeting of Brazil, an important transit hub for transatlantic fiber-optic cables that are hacked.
Note: To read Snowden's full, inspiring letter, click here.
A participant in a White House-sponsored review of surveillance activities described as shameful an apparent decision to leave most of the National Security Agencys controversial bulk spying intact. Sascha Meinrath, director of the Open Technology Institute, said [on December 13] that ... The review group was searching for ways to make the most modest pivot necessary to continue business as usual. Should the review groups report resemble descriptions that leaked ... the report does nothing to alter the lack of trust the global populace has for what the US is doing, and nothing to restore our reputation as an ethical internet steward, said Meinrath, who met with the advisory panel and White House officials twice to discuss the bulk surveillance programs that have sparked international outrage. Leaks about the review groups expected recommendations to the New York Times and Wall Street Journal strengthened Meinrath and other participants long-standing suspicions that much of the NSAs sweeping spy powers would survive. The Times quoted an anonymous official familiar with the group saying its report says we cant dismantle these programs, but we need to change the way almost all of them operate. According to the leaks, the review group will recommend that bulk collection of every Americans phone call data continue, possibly by the phone companies instead of the NSA, with tighter restrictions than the reasonable, articulable suspicion standard for searching through them that the NSA currently employs.
Note: For more on massive government intrusions of citizens' privacy, see the deeply revealing reports from reliable major media sources available here.
The National Security Agency isn't the only government entity secretly collecting data from people's cellphones. Local police are increasingly scooping it up, too. Armed with new technologies, including mobile devices that tap into cellphone data in real time, dozens of local and state police agencies are capturing information about thousands of cellphone users at a time, whether they are targets of an investigation or not. The records, from more than 125 police agencies in 33 states, reveal [that] about one in four law-enforcement agencies have used a tactic known as a "tower dump," which gives police data about the identity, activity and location of any phone that connects to the targeted cellphone towers over a set span of time, usually an hour or two. A typical dump covers multiple towers, and wireless providers, and can net information from thousands of phones. At least 25 police departments own a Stingray, a suitcase-size device that costs as much as $400,000 and acts as a fake cell tower. The system, typically installed in a vehicle so it can be moved into any neighborhood, tricks all nearby phones into connecting to it and feeding data to police. In some states, the devices are available to any local police department via state surveillance units. Organizations such as the American Civil Liberties Union and Electronic Privacy Information Center say the swelling ability by even small-town police departments to easily and quickly obtain large amounts of cellphone data raises questions about the erosion of people's privacy as well as their Fourth Amendment protections against unreasonable search and seizure.
Note: For more on massive government intrusions of citizens' privacy, see the deeply revealing reports from reliable major media sources available here.
Canada allowed the U.S. National Security Agency (NSA) to conduct widespread surveillance during the 2010 Group of 20 summit in Toronto, according to a media report that cited documents from former NSA contractor Edward Snowden. The report by the Canadian Broadcasting Corp ... cited briefing notes it said showed the United States turned its Ottawa embassy into a security command post during a six-day spying operation by the top-secret U.S. agency as President Barack Obama and other world leaders met that June. One of the bylines on the CBC report was Glenn Greenwald, the U.S. journalist who has worked with Snowden on several other NSA stories. CBC ... quoted an NSA briefing note describing the operation as "closely coordinated with the Canadian partner". The Canadian equivalent of the NSA is the Communications Security Establishment Canada, or CSEC. CBC said the documents did not reveal the targets of the NSA operation, but described part of the U.S. eavesdropping agency's mandate at the Toronto summit as "providing support to policymakers". CSEC, which has a very low public profile, employs about 2,000 people. It is part of the so-called Five Eyes intelligence-sharing network that also includes the United States, Britain, New Zealand and Australia. Last month, Brazil angrily demanded an explanation for media reports which said CSEC agents had targeted its mines and energy industry.
Note: For more on the realities of intelligence agency activities, see the deeply revealing reports from reliable major media sources available here.
The phone, internet and email records of UK citizens not suspected of any wrongdoing have been analysed and stored by America's National Security Agency under a secret deal that was approved by British intelligence officials, according to documents from the whistleblower Edward Snowden. In the first explicit confirmation that UK citizens have been caught up in US mass surveillance programs, an NSA memo describes how in 2007 an agreement was reached that allowed the agency to "unmask" and hold on to personal data about Britons that had previously been off limits. The memo ... says the material is being put in databases where it can be made available to other members of the US intelligence and military community. Until now, it had been generally understood that the citizens of each country were protected from surveillance by any of the others. But the Snowden material reveals that: In 2007, the rules were changed to allow the NSA to analyse and retain any British citizens' mobile phone and fax numbers, emails and IP addresses swept up by its dragnet. These communications were "incidentally collected" by the NSA, meaning the individuals were not the initial targets of surveillance operations and therefore were not suspected of wrongdoing. The NSA has been using the UK data to conduct so-called "pattern of life" or "contact-chaining" analyses, under which the agency can look up to three "hops" away from a target of interest examining the communications of a friend of a friend of a friend. Three hops for a typical Facebook user could pull the data of more than 5 million people into the dragnet.
Note: For more on government threats to privacy, see the deeply revealing reports from reliable major media sources available here.
A secret court order that authorised a massive trawl by the National Security Agency of Americans' email and internet data was published for the first time on [November 18], among a trove of documents that also revealed a judge's concern that the NSA "continuously" and "systematically" violated the limits placed on the program. Another later court order found that what it called "systemic overcollection" had taken place. In a heavily redacted opinion Colleen Kollar-Kotelly, the former presiding judge of the FISA court, placed legal weight on the methods of surveillance employed by the NSA, which had never before collected the internet data of an enormous volume of communications. The methods, known as pen registers and trap-and-trace devices, record the incoming and outgoing routing information of communications. Kollar-Kotelly ruled that acquiring the metadata, and not the content, of email and internet usage in bulk was harmonious with the purpose of Congress and prior court rulings even though no surveillance statute ever authorized it and top officials at the Justice Department and the FBI threatened to resign in 2004 over what they considered its dubious legality. The type of data collected under the program included information on the "to", "from" and "bcc" lines of an email rather than the content. Metadata, wrote Kollar-Kotelly, enjoyed no protection under the fourth amendment to the US constitution, a precedent established by the Supreme Court in 1979 in a single case on which the NSA relies currently.
Note: For more on government corruption, see the deeply revealing reports from reliable major media sources available here.
Edward J. Snowden, the former National Security Agency contractor, said in an extensive interview this month that he did not take any secret N.S.A. documents with him to Russia when he fled there in June, assuring that Russian intelligence officials could not get access to them. He also asserted that he was able to protect the documents from Chinas spies because he was familiar with that nations intelligence abilities, saying that as an N.S.A. contractor he had targeted Chinese operations and had taught a course on Chinese cybercounterintelligence. Theres a zero percent chance the Russians or Chinese have received any documents, he said. Mr. Snowden added that inside the spy agency theres a lot of dissent. But he said that people were kept in line through fear and a false image of patriotism, which he described as obedience to authority. He said he believed that if he tried to question the N.S.A.s surveillance operations as an insider, his efforts would have been buried forever, and he would have been discredited and ruined. Mr. Snowden said he finally decided to act when he discovered a copy of a classified 2009 inspector generals report on the N.S.A.s warrantless wiretapping program during the Bush administration. After reading about the program, which skirted the existing surveillance laws, he concluded that it had been illegal, he said. If the highest officials in government can break the law without fearing punishment or even any repercussions at all, he said, secret powers become tremendously dangerous.
Note: For more on the hidden realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
Since 2010, the National Security Agency has been exploiting its huge collections of data to create sophisticated graphs of some Americans social connections that can identify their associates, their locations at certain times, their traveling companions and other personal information, according to newly disclosed documents and interviews with officials. The spy agency began allowing the analysis of phone call and e-mail logs in November 2010 to examine Americans networks of associations for foreign intelligence purposes after N.S.A. officials lifted restrictions on the practice, according to documents provided by Edward J. Snowden, the former N.S.A. contractor. The agency was authorized to conduct large-scale graph analysis on very large sets of communications metadata without having to check foreignness of every e-mail address, phone number or other identifier, the document said. The agency can augment the communications data with material from public, commercial and other sources, including bank codes, insurance information, Facebook profiles, passenger manifests, voter registration rolls and GPS location information, as well as property records and unspecified tax data, according to the documents. They do not indicate any restrictions on the use of such enrichment data, and several former senior Obama administration officials said the agency drew on it for both Americans and foreigners. Almost everything about the agencys operations is hidden, and the decision to revise the limits concerning Americans was made in secret, without review by the nations intelligence court or any public debate.
Note: For an excellent 15-minute BBC Newsnight interview with Glenn Greenwald defending Edward Snowden's release of secret documents, click here. For more on government surveillance, see the deeply revealing reports from reliable major media sources available here.
Guardian editors on [August 20] revealed why and how the newspaper destroyed computer hard drives containing copies of some of the secret files leaked by Edward Snowden. The decision was taken after a threat of legal action by the government that could have stopped reporting on the extent of American and British government surveillance revealed by the documents. It resulted in one of the stranger episodes in the history of digital-age journalism. On Saturday 20 July, in a deserted basement of the Guardian's King's Cross offices, a senior editor and a Guardian computer expert used angle grinders and other tools to pulverise the hard drives and memory chips on which the encrypted files had been stored. As they worked they were watched by technicians from Government Communications Headquarters (GCHQ) who took notes and photographs, but who left empty-handed. The editor of the Guardian, Alan Rusbridger, had earlier informed government officials that other copies of the files existed outside the country and that the Guardian was neither the sole recipient nor steward of the files leaked by Snowden, a former National Security Agency (NSA) contractor. But the government insisted that the material be either destroyed or surrendered. The British government has attempted to step up its pressure on journalists, with the detention in Heathrow on Sunday of David Miranda, the partner of Glenn Greenwald, who has led the Guardian's US reporting on the files.
Note: For more on government attacks on civil liberties, see the deeply revealing reports from reliable major media sources available here.
The partner of the Guardian journalist [Glenn Greenwald], who has written a series of stories revealing mass surveillance programmes by the US National Security Agency, was held for almost nine hours ... by UK authorities as he passed through London's Heathrow airport on his way home to Rio de Janeiro. David Miranda ... was returning from a trip to Berlin when he was stopped by officers at 8.05am and informed that he was to be questioned under schedule 7 of the Terrorism Act 2000. The controversial law, which applies only at airports, ports and border areas, allows officers to stop, search, question and detain individuals. The 28-year-old was held for nine hours, the maximum the law allows before officers must release or formally arrest the individual. According to official figures, most examinations under schedule 7 over 97% last less than an hour, and only one in 2,000 people detained are kept for more than six hours. Miranda was released, but officials confiscated electronics equipment including his mobile phone, laptop, camera, memory sticks, DVDs and games consoles. "This is a profound attack on press freedoms and the news gathering process," Greenwald said. "To detain my partner for a full nine hours while denying him a lawyer, and then seize large amounts of his possessions, is clearly intended to send a message of intimidation to those of us who have been reporting on the NSA and GCHQ. The actions of the UK pose a serious threat to journalists everywhere. But the last thing it will do is intimidate or deter us in any way from doing our job as journalists. Quite the contrary: it will only embolden us more to continue to report aggressively."
Note: For more on government attacks on civil liberties, see the deeply revealing reports from reliable major media sources available here.
Two US senators on the intelligence committee said [that] thousands of annual violations by the National Security Agency on its own restrictions were "the tip of the iceberg." "The executive branch has now confirmed that the rules, regulations and court-imposed standards for protecting the privacy of Americans' have been violated thousands of times each year," said senators Ron Wyden and Mark Udall, two leading critics of bulk surveillance, who responded [to] a Washington Post story based on documents provided by whistleblower Edward Snowden. "We have previously said that the violations of these laws and rules were more serious than had been acknowledged, and we believe Americans should know that this confirmation is just the tip of a larger iceberg." On July 31, Wyden, backed by Udall, vaguely warned other senators in a floor speech that the NSA and the director of national intelligence were substantively misleading legislators by describing improperly collected data as a matter of innocent and anodyne human or technical errors. In keeping with their typically cautious pattern when discussing classified information, Wyden and Udall did not provide details about their claimed "iceberg" of surveillance malfeasance. But they hinted that the public still lacks an adequate understanding of the NSA's powers to collect data on Americans under its controversial interpretation of the Patriot Act. "We believe the public deserves to know more about the violations of the secret court orders that have authorized the bulk collection of Americans' phone and email records under the Patriot Act," [they] said.
Note: For more on massive surveillance, see the deeply revealing reports from reliable major media sources available here.
A secretive U.S. Drug Enforcement Administration unit is funneling information from intelligence intercepts, wiretaps, informants and a massive database of telephone records to authorities across the nation to help them launch criminal investigations of Americans. Documents reviewed by Reuters show that law enforcement agents have been directed to conceal how such investigations truly beginnot only from defense lawyers but also sometimes from prosecutors and judges. The undated documents show that federal agents are trained to "recreate" the investigative trail to effectively cover up where the information originated, a practice that some experts say violates a defendant's constitutional right to a fair trial. If defendants don't know how an investigation began, they cannot know to ask to review potential sources of exculpatory evidenceinformation that could reveal entrapment, mistakes or biased witnesses. "I have never heard of anything like this at all," said Nancy Gertner, a Harvard Law School professor who served as a federal judge from 1994 to 2011. Gertner and other legal experts said the program sounds more troubling than recent disclosures that the National Security Agency has been collecting domestic phone records. The NSA effort is geared toward stopping terrorists; the DEA program targets common criminals, primarily drug dealers. "It is one thing to create special rules for national security," Gertner said. "Ordinary crime is entirely different. It sounds like they are phonying up investigations."
Note: For more on government corruption, see the deeply revealing reports from reliable major media sources available here.
Glenn Greenwald the reporter who broke the story about the National Security Agencys surveillance programs claimed that those NSA programs allowed even low-level analysts to search the private emails and phone calls of Americans. The NSA has trillions of telephone calls and emails in their databases that theyve collected over the last several years, Greenwald told ABC News George Stephanopoulos. All an analyst has to do is enter an email address or an IP address, and [the program] searches that database and lets them listen to the calls or read the emails of everything that the NSA has stored, or look at the browsing histories or Google search terms that youve entered. Greenwald explained that ... these programs still allow analysts to search through data with little court approval or supervision. Greenwald said "these systems allow analysts to listen to whatever emails they want, whatever telephone calls, browsing histories, Microsoft Word documents. And its all done with no need to go to a court, with no need to even get supervisor approval on the part of the analyst, he added. Greenwald said the existence of these analyst search programs are in line with the claims of Edward Snowden, who first leaked details of the NSAs surveillance programs last month. Its an incredibly powerful and invasive tool, exactly of the type that Mr. Snowden described, Greenwald said. NSA officials are going to be testifying before the Senate on Wednesday, and I defy them to deny that these programs work exactly as I just said, Greenwald said.
Note: For more on government privacy invasions, see the deeply revealing reports from reliable major media sources available here.
As the 50th anniversary of the 1963 March on Washington approaches ... where Martin Luther King Jr gave his famous "I have a dream" speech, it is important to recall the extent to which King was targeted by the government. The FBI operation against King is one of the most shameful episodes in the long history of our government's persecution of dissenters. In a heavily redacted, classified FBI memo dated 4 January 1956 just a little more than a month after Rosa Parks was arrested for refusing to give up her seat on a bus to a white passenger stated that an agent "had been assigned ... to find out all he could about Reverend Martin L King, colored minister in Montgomery and leader in the bus boycott to uncover all the derogatory information he could about King." [FBI] director, J Edgar Hoover ... was deploying the vast resources he controlled against any and all perceived critics of the United States. The far-reaching clandestine surveillance, infiltration and disruption operation Hoover ran was dubbed "COINTELPRO", for counterintelligence program. The FBI's COINTELPRO activities ... were thoroughly investigated in 1975 by the Church Committee, [which] reported that the FBI "conducted a sophisticated vigilante operation aimed squarely at preventing the exercise of first amendment rights of speech and association." Among COINTELPRO's perverse activities was an FBI effort to threaten Martin Luther King Jr with exposure of an alleged extramarital affair, including the suggestion, made by the FBI to King, that he avoid embarrassment by killing himself. Deeply concerned about the crackdown on dissent happening under Obama, scholar Cornel West ... wondered if [King] "would not be invited to the very march in his name."
Note: This article fails to mention a key fact. At a 1999 court trial held in Memphis, the family of Rev. King accused elements of the U.S. government of complicity in King's death. After one month of hearings from 70 witnesses, a jury composed of six white and six black jurors took only one hour to find the U.S. government, the state of Tennessee, the city of Memphis, the Memphis police, and several individuals guilty of murdering King. Yet the mainstream media completely boycotted this trial. Thankfully, CBC (Canada's PBS) gave it some coverage. To see a six-minute CBC clip of this highly revealing trial, click here.
[There is] a growing debate over a little-known but increasingly important piece of equipment buried deep inside a car: the event data recorder, more commonly known as the black box. About 96 percent of all new vehicles sold in the United States have the boxes, and in September 2014, if the National Highway Traffic Safety Administration has its way, all will have them. Data stored in the devices is increasingly being used to identify safety problems in cars and as evidence in traffic accidents and criminal cases. And the trove of data inside the boxes has raised privacy concerns, including questions about who owns the information, and what it can be used for, even as critics have raised questions about its reliability. To consumer advocates, the data is only the latest example of governments and companies having too much access to private information. Once gathered, they say, the data can be used against car owners, to find fault in accidents or in criminal investigations. These cars are equipped with computers that collect massive amounts of data, said Khaliah Barnes of the Electronic Privacy Information Center, a Washington-based consumer group. Without protections, it can lead to all kinds of abuse. In [14] states, lawyers may subpoena the data for criminal investigations and civil lawsuits, making the information accessible to third parties, including law enforcement or insurance companies that could cancel a drivers policy or raise a drivers premium based on the recorders data.
Note: For more on government and corporate privacy invasions, see the deeply revealing reports from reliable major media sources available here.
The American Civil Liberties Union is warning that law enforcement officials are using license plate scanners to amass massive and unregulated databases that can be used to track law-abiding citizens as their go about their daily lives. In a new report, "You Are Being Tracked: How License Plate Readers Are Being Used to Record Americans' Movements," the ACLU discusses the data culled from license plate scanners - cameras mounted on patrol cars, overpasses and elsewhere to record your license plate number and location at a given time. There are tens of thousands such cameras now in operation, according to the group, with the data in some cases being stored indefinitely. The ACLU report is the result of an analysis of 26,000 pages of documents from police departments around the country, obtained through nearly 600 [FOIA] requests. It finds that while some jurisdictions keep the information gleaned from the scanners for a short time ... many hold onto the data for years. The organization complains that there are "virtually no rules in place" to keep officials from tracking "everybody all the time." The ACLU also warns that the data is being fed into larger databases, with the private National Vehicle Location Service now holding more than 800 million license plate records. The group's database is used by more than 2,200 law enforcement customers. The [ACLU] report warns that the data can be used in an official capacity to spy on protesters or target communities based on their religious beliefs, or unofficially by a police officer who wants to keep an eye on a romantic rival.
Note: For more on privacy, see the deeply revealing reports from reliable major media sources available here.
Have you noticed anything missing in the political discourse about the National Security Administration's unprecedented mass surveillance? There's at least been some conversation about the intelligence community's potential criminality and constitutional violations. But there have only been veiled references to how cash undoubtedly tilts the debate against those who challenge the national security state. Those indirect references have come in stories about Booz Allen Hamilton, the security contractor that employed Edward Snowden. CNN/Money notes that 99 percent of the firm's multibillion-dollar annual revenues now come from the federal government. Those revenues are part of a larger and growing economic sector within the military-industrial complex - a sector that, according to author Tim Shorrock, is "a $56 billion-a-year industry." Yet few in the Washington press corps mention that politicians' attacks on surveillance critics may have nothing to do with principle and everything to do with shilling for campaign donors. For a taste of what that kind of institutionalized corruption looks like, peruse the Influence Explorer site to see how much Booz Allen Hamilton and its parent company, the Carlyle Group, spend. As you'll see, from Barack Obama to John McCain, many of the politicians publicly defending the surveillance state have taken huge sums of money from the firms. Simply put, there are corporate forces with a vested financial interest in making sure the debate over security is tilted toward the surveillance state and against critics of that surveillance state.
Note: Tim Shorrock, quoted above, is the author of Spies for Hire: The Secret World of Intelligence Outsourcing.
FBI Director Robert Mueller acknowledged [to the Senate Judiciary Committee on June 19 that] the law enforcement agency uses drone aircraft in the United States for surveillance. He did not say how many unmanned surveillance vehicles (UAVs) the FBI has or how often they have been used. But a law enforcement official told CNN the FBI has used them a little more than a dozen times but did not say when that started. The official said drones are useful in hostage and barricade situations because they operate more quietly and are less visible than traditional aircraft such as helicopters. Bureau spokesman Paul Bresson said their use allows "us to learn critical information that otherwise would be difficult to obtain without introducing serious risk to law enforcement personnel." Bresson said the aircraft can only be used to perform surveillance on stationary subjects and the FBI must first get approval from the Federal Aviation Administration to fly in a "very confined geographic area." Senate Intelligence Committee Chairman Dianne Feinstein expressed concern over drone use domestically. "I think the greatest threat to the privacy of Americans is the drone and the use of the drone, and the very few regulations that are on it today and the booming industry of commercial drones," the California Democrat said. The FAA forecasts some 10,000 civilian drones will be in use in the United States within five years, including those for law enforcement and commercial purposes.
Note: For more on domestic US drone surveillance, click here. For deeply revealing reports from reliable major media sources on the hidden realities of intelligence agencies, click here.
When a National Security Agency contractor revealed top-secret details this month on the government's collection of Americans' phone and Internet records, one select group of intelligence veterans breathed a sigh of relief. Thomas Drake, William Binney and J. Kirk Wiebe belong to a select fraternity: the NSA officials who paved the way. For years, the three whistle-blowers had told anyone who would listen that the NSA collects huge swaths of communications data from U.S. citizens. They had spent decades in the top ranks of the agency, designing and managing the very data-collection systems they say have been turned against Americans. When they became convinced that fundamental constitutional rights were being violated, they complained first to their superiors, then to federal investigators, congressional oversight committees and, finally, to the news media. They have been investigated as criminals and forced to give up careers, reputations and friendships built over a lifetime. Today, they feel vindicated. They say the documents leaked by Edward Snowden, the 29-year-old former NSA contractor who worked as a systems administrator, proves their claims of sweeping government surveillance of millions of Americans not suspected of any wrongdoing. They say those revelations only hint at the programs' reach. On [June 15], USA TODAY brought Drake, Binney and Wiebe together for the first time since the story broke to discuss the NSA revelations. With their lawyer, Jesselyn Radack of the Government Accountability Project, they weighed their implications and their repercussions.
Note: See the link above for a great interview of these courageous whistleblowers. For deeply revealing reports from reliable major media sources on the hidden realities of intelligence agencies, click here
CNN's Out Front with Erin Burnett [has been] focused on the possible involvement in the Boston Marathon attack of Katherine Russell, the 24-year-old American widow of the deceased suspect, Tamerlan Tsarnaev. Anonymous government officials are claiming that they are now focused on telephone calls between Russell and Tsarnaev that took place both before and after the attack to determine if she had prior knowledge of the plot or participated in any way. Burnett interviewed Tim Clemente, a former FBI counterterrorism agent, about whether the FBI would be able to discover the contents of past telephone conversations between the two. He quite clearly insisted that they could: BURNETT: There's no way they actually can find out what happened, right, unless she tells them? CLEMENTE: No, there is a way. We certainly have ways in national security investigations to find out exactly what was said in that conversation. We certainly can find that out. BURNETT: So they can actually get that? People are saying, look, that is incredible. CLEMENTE: No, welcome to America. All of that stuff is being captured as we speak whether we know it or like it or not. On Thursday night, Clemente again appeared on CNN. He reiterated what he said the night before but added expressly that "all digital communications in the past" are recorded and stored. All digital communications - meaning telephone calls, emails, online chats and the like - are automatically recorded and stored and accessible to the government after the fact. To describe that is to define what a ubiquitous, limitless Surveillance State is.
Note: All of our communications have been monitored by government computers for years. BBC News reported in this this 1999 article about the Echelon network which monitors all communications globally. For deeply revealing reports from reliable major media sources on government and corporate threats to privacy, click here.
The use of drones by domestic US law enforcement agencies is growing rapidly, both in terms of numbers and types of usage. As a result, civil liberties and privacy groups led by the ACLU ... have been devoting increasing efforts to publicizing their unique dangers and agitating for statutory limits. The belief that weaponized drones won't be used on US soil is patently irrational. Police departments are already speaking openly about how their drones "could be equipped to carry nonlethal weapons such as Tasers or a bean-bag gun." The drone industry has already developed and is now aggressively marketing precisely such weaponized drones for domestic law enforcement use. Domestic weaponized drones will be much smaller and cheaper, as well as more agile - but just as lethal [as the large missile-firing drones used by the US military overseas]. The nation's leading manufacturer of small "unmanned aircraft systems" (UAS) ... is AeroVironment, Inc. (AV). AV is now focused on drone products - such as the "Qube" - that are so small that they can be "transported in the trunk of a police vehicle or carried in a backpack." AV's website ... touts a February, 2013 Defense News article describing how much the US Army loves [its] "Switchblade" [drone]. Time Magazine heralded this tiny drone weapon as "one of the best inventions of 2012", gushing: "the Switchblade drone can be carried into battle in a backpack. It's a kamikaze: the person controlling it uses a real-time video feed from the drone to crash it into a precise target. Its tiny warhead detonates on impact."
Note: This important article also discusses drones used by government agencies such as police for purposes of continuous surveillance. But it misses entirely another major dimension: privately owned and controlled drones, which are becoming dirt cheap and within the reach of virtually anyone. Will the new "DroneWorld" in the making combine the worst features of the Police State with the Wild West?
The Federal Bureau of Investigation used counterterrorism agents to investigate the Occupy Wall Street movement, including its communications and planning, according to newly disclosed agency records. The F.B.I. records show that as early as September 2011, an agent from a counterterrorism task force in New York notified officials of two landmarks in Lower Manhattan Federal Hall and the Museum of American Finance that their building was identified as a point of interest for the Occupy Wall Street. In the following months, F.B.I. personnel around the country were routinely involved in exchanging information about the movement with businesses, local law-enforcement agencies and universities. An October 2011 memo from the bureaus Jacksonville, Fla., field office was titled Domain Program Management Domestic Terrorist. The memo said agents discussed past and upcoming meetings of the movement, and its spread. It said agents should contact Occupy Wall Street activists to ascertain whether people who attended their events had violent tendencies. Since the Sept. 11, 2001, attacks, the F.B.I. has come under criticism for deploying counterterrorism agents to conduct surveillance and gather intelligence on organizations active in environmental, animal-cruelty and poverty issues. The records were obtained by the Partnership for Civil Justice Fund, a civil-rights organization in Washington, through a Freedom of Information request to the F.B.I.
Note: For analysis of these amazing documents revealing the use of joint government and corporate counterterrorism structures against peaceful protestors of financial corruption, click here and here. For a Democracy Now! video segment on this, click here.
[William] Binney, a 32-year veteran of the National Security Agency turned whistle-blower, ... described details about Stellar Wind, the N.S.A.s top-secret domestic spying program begun after 9/11, which was so controversial that it nearly caused top Justice Department officials to resign in protest, in 2004. The decision must have been made in September 2001, Mr. Binney told me [and] cinematographer Kirsten Johnson. Thats when the equipment started coming in. He resigned over this in 2001 and began speaking out publicly in the last year. [Binney] is among a group of N.S.A. whistle-blowers, including Thomas A. Drake, who have each risked everything their freedom, livelihoods and personal relationships to warn Americans about the dangers of N.S.A. domestic spying. The N.S.A. has technical abilities that are nearly impossible to defend against if you are targeted. The 2008 amendments to the Foreign Intelligence Surveillance Act, which oversees the N.S.A. activities, are up for renewal in December. Two members of the Senate Select Committee on Intelligence, Senators Ron Wyden of Oregon and Mark Udall of Colorado ... have been warning about secret interpretations of laws and backdoor loopholes that allow the government to collect our private communications. Thirteen senators have signed a letter expressing concern about a loophole in the law that permits the collection of United States data. The A.C.L.U. and other groups have also challenged the constitutionality of the law, and the Supreme Court will hear arguments in that case on Oct. 29.
Note: The video about this on the NY Times webpage at the link above is quite revealing. One potent comment of this 32-year NSA veteran in the video is "They wanted to highly classify the extreme impeachable crimes they were committing." For deeply revealing reports from reliable major media sources on government and corporate surveillance, click here.
[Trapwire is] a CCTV surveillance system that recognises people from their face or walk and analyses whether they might be about to commit a terrorist or criminal act. According to documents released online by WikiLeaks [it] is being used in a number of countries to try to monitor people and threats. Founded by former CIA agents, Trapwire uses data from a network of CCTV systems and numberplate readers to figure out the threat level in huge numbers of locations. The documents outlining Trapwire's existence and its deployment in the US were apparently obtained in a hack of computer systems belonging to the intelligence company Stratfor at the end of last year. Documents from the US department of homeland security show that it paid $832,000 to deploy Trapwire in Washington DC and Seattle. Stratfor describes Trapwire as "a unique, predictive software system designed to detect patterns of pre-attack surveillance and logistical planning". It serves "a wide range of law enforcement personnel and public and private security officials domestically and internationally", Stratfor says. Some have expressed doubts that Trapwire could really forecast [future] acts based on data from cameras. The claims might seem overblown, but then the idea that the US could have an international monitoring system seemed absurd until the discovery of the Echelon system, used by the US to eavesdrop on electronic communications internationally.
Note: For more on the growing use of this secret technology, click here. For deeply revealing reports from reliable major media sources on privacy, click here.
The days of secrecy at the Transportation Security Administration (TSA) may be coming to an end. Its a widely held belief that the agencys hasty embrace of expensive, X-rated x-ray machines has more to do with closed-door lobbying efforts of manufacturers than a deliberate consideration of the devices merits. The Electronic Privacy Information Center (EPIC) [has] pushed for some transparency by asking the D.C. Circuit U.S. Court of Appeals to compel the agency to hold a public notice-and-comment period on the use of pornographic scanners, as the law requires. EPIC has a good case because on July 15, 2011, the D.C. Circuit issued a ruling insisting TSA promptly come into compliance with Administrative Procedure Act requirements regarding public hearings. TSA believed it wasnt subject to such rules because the virtual strip-searching of women, children and the elderly is an essential security operation. The last thing TSA wants is the public-relations disaster of having to collect and publish the horror tales from Americans subjected to humiliation from the nude photography and intrusive pat-down groping sessions. Its time to admit the post-Sept. 11 experiment in having the government take over airport screening duties has been a colossal flop. TSA has defied the Administrative Procedures Act, an appellate court, the public will and common decency. Its not enough just to pull the plug on the scanners; the plug should be pulled on TSA itself.
Note: According to this PBS report, "European Union regulators recently banned any body scanner that uses X-rays, 'in order not to risk jeopardizing citizens' health and safety.'" It also states, "The TSA tested the devices behind closed doors, without scrutiny from independent scientists." For lots more on this topic important to all air travelers, click here.
The Department of Homeland Security will soon be using a laser at airports that can detect everything about you from over 160 feet away. This laser-based scanner ... could read everything from a persons adrenaline levels, to traces of gun powder on a persons clothes, to illegal substances and it can all be done without a physical search. It also could be used on multiple people at a time, eliminating random searches at airports. The scanner is called the Picosecond Programmable Laser. The device works by blasting its target with lasers which vibrate molecules that are then read by the machine that determine what substances a person has been exposed to. The inventor of this invasive technology is Genia Photonics. Active since 2009, they hold 30 patents on laser technology designed for scanning. In 2011, they formed a partnership with In-Q-Tel, a company chartered by the CIA and Congress to build a bridge between the Agency and a new set of technology innovators. Although the technology could be used by Big Brother, Genia Photonics states that the device could be far more beneficial being used for medical purposes to check for cancer in real time, lipids detection, and patient monitoring.
Note: For deeply revealing reports from reliable major media sources on government threats to privacy, click here.
The Obama administration is moving to relax restrictions on how counterterrorism analysts may retrieve, store and search information about Americans gathered by government agencies for purposes other than national security threats. Attorney General Eric H. Holder Jr. [has] signed new guidelines for the National Counterterrorism Center. The guidelines will lengthen to five years from 180 days the amount of time the center can retain private information about Americans when there is no suspicion that they are tied to terrorism, intelligence officials said. The guidelines are also expected to result in the center making more copies of entire databases and data mining them. They also set off civil-liberties concerns among privacy advocates who invoked the Total Information Awareness program. That program, proposed early in the George W. Bush administration and partially shut down by Congress after an outcry, proposed fusing vast archives of electronic records like travel records, credit card transactions, phone calls and more. Were all in the dark, and for all we know it could be a rerun of Total Information Awareness, which would have allowed the government to make a computerized database of everything on everybody, said Kate Martin, the director of the Center for National Security Studies, who criticized the administration for not making the draft guidelines public for scrutiny ahead of time.
Note: For excellent and insightful analyses of the disturbing growth of government surveillance and secrecy described in this NYT report, click here and here and here and here.
A new federal law, signed by the president on [February 14], compels the Federal Aviation Administration to allow drones to be used for all sorts of commercial endeavors. Local police and emergency services will also be freer to send up their own drones. But while businesses, and drone manufacturers especially, are celebrating the opening of the skies to these unmanned aerial vehicles, the law raises new worries about how much detail the drones will capture about lives down below and what will be done with that information. Some questions likely to come up: Can a drone flying over a house pick up heat from a lamp used to grow marijuana inside, or take pictures from outside someones third-floor fire escape? Can images taken from a drone be sold to a third party, and how long can they be kept? The American Civil Liberties Union and other advocacy groups are calling for new protections against what the A.C.L.U. has said could be routine aerial surveillance of American life. The new law, part of a broader financing bill for the F.A.A., came after intense lobbying by drone makers and potential customers. These manufacturers have been awaiting lucrative new opportunities at home. The market for drones is valued at $5.9 billion and is expected to double in the next decade, according to industry figures. Drones can cost millions of dollars for the most sophisticated varieties to as little as $300 for one that can be piloted from an iPhone.
Note: For more information on the use of drones by police in the US, click here. For more on the threats to civil liberties created by this new law, click here. For lots more from reliable sources on surveillance in the US, click here.
In a luxury Washington, DC, hotel last month, governments from around the world gathered to discuss surveillance technology they would rather you did not know about. The annual Intelligence Support Systems (ISS) World Americas conference is a mecca for representatives from intelligence agencies and law enforcement. But to the media or members of the public, it is strictly off limits. Behind the cloak of secrecy at the ISS World conference, tips are shared about the latest advanced ... methods used to spy on citizens computer hacking, covert bugging and GPS tracking. The use of such methods is more commonly associated with criminal hacking groups, who have used spyware and trojan viruses to infect computers and steal bank details or passwords. But as the internet has grown, intelligence agencies and law enforcement have adopted similar techniques. "The current method of choice would seem to be spyware, or trojan horses," said Chris Soghoian, a Washington-based surveillance and privacy expert. "When there are five or six conferences held in closed locations every year, where telecommunications companies, surveillance companies and government ministers meet in secret to cut deals, buy equipment, and discuss the latest methods to intercept their citizens' communications that I think meets the level of concern," he said. "Decades of history show that surveillance powers are abused usually for political purposes."
Note: For more on corporate and government threats to privacy and civil liberties, click here and here.
Military researchers are at work on another revolution in the air: shrinking unmanned drones ... to the size of insects and birds. The drones in development ... are designed to replicate the flight mechanics of moths, hawks and other inhabitants of the natural world. Were looking at how you hide in plain sight, said Greg Parker, an aerospace engineer, as he held up a prototype of a mechanical hawk that in the future might carry out espionage or kill. An explosion in aerial drones is transforming the way America fights and thinks about its wars. Predator drones ... are by now a brand name, known and feared around the world. But far less known is the sheer size, variety and audaciousness of a rapidly expanding drone universe, along with the dilemmas that come with it. The Pentagon now has some 7,000 aerial drones, compared with fewer than 50 a decade ago. Within the next decade the Air Force anticipates a decrease in manned aircraft but expects its number of multirole aerial drones like the Reaper the ones that spy as well as strike to nearly quadruple, to 536. Already the Air Force is training more remote pilots, 350 this year alone, than fighter and bomber pilots combined. Its a growth market, said Ashton B. Carter, the Pentagons chief weapons buyer. The Pentagon has asked Congress for nearly $5 billion for drones next year, and by 2030 envisions ever more stuff of science fiction: spy flies equipped with sensors and microcameras to detect enemies
Note: Ashton B. Carter, CIA director John Deutch, and executive director of the 9/11 Commission Philip Zelikow co-authored a 1998 article in the journal of the Council on Foreign Relations, Foreign Affairs, titled "Catastrophic Terrorism". It predicted, years in advance, a massive attack on the World Trade Center that would result in loss of civil liberties, detention without charge, torture, and endless wars abroad. The Pentagon's weapons-buying spree, now including billions of dollars for drones to be used over US soil, and for which Carter is the "chief weapons buyer," would have been impossible without the 9/11 attacks.
The Transportation Security Administration has come under fire for new body scanners and what some say are highly invasive pat-downs. Thomas Sawyer, a bladder cancer survivor, said he was humiliated after a pat-down broke his urostomy bag, leaving the 61-year-old covered in his own urine. Sawyer said he warned the TSA officials twice that the pat-down could break the seal. Cathy Bossi, a long-time flight attendant and breast cancer survivor, said the TSA made her take off her prosthetic breast. "She put her full hand on my breast and said, 'What is this?' I said 'It's a prosthesis because I've had a breast cancer,'" Bossi said. "And she said, 'You'll need to show me that.'" In recent days, several passengers have come forward to tell such shocking stories about their experiences with TSA officers. An ABC News employee said she was subject to a "demeaning" search at Newark Liberty International Airport Sunday morning. "The woman who checked me reached her hands inside my underwear and felt her way around," she said. "It was basically worse than going to the gynecologist. It was embarrassing. It was demeaning. It was inappropriate." The head of the Transportation Security Administration John Pistole ... has said the TSA would not change its pat-down procedures.
Note: For lots more from major media sources on increasing threats to privacy, click here.
Two of the largest pilots' unions in the nation are urging commercial pilots to rebel against current airport screening rules. In late October, the Transport Security Administration implemented more invasive patdown rules. Travelers and pilots were faced with a new dilemma -- have a revealing, full-body scan or what some are calling an X-rated patdown. Pilots are piping mad over the options, saying the full-body scanners emit dangerous levels of radiation and that the alternative public patdown is disgraceful for a pilot in uniform. Some pilots have said they felt so violated after a patdown, they were unfit to fly. The patdowns, implemented Oct. 29, allow TSA officers to pat down passengers with the front of their hands, instead of the backs of their hands. A security expert who demonstrated the new procedure on a mannequin for ABC News explained the changes. "You go down the body and up to the breast portion," said Charles Slepian of the Foreseeable Risk Analysis Center. "If it's a female passenger, you're going to see if there's anything in the bra." The new patdown protocol could be used at any of the nation's 450 airports on passengers who require additional screening. Tens of thousands of passengers are submitted to patdowns and full-body scanners every day. More than 300 full-body scanners are being used at 65 airports across the country.
Note: And what about the general public having to submit to being groped?
It started with a fingerprint of a 25-year-old college professor who opposed the Vietnam War and ended with a search for his remains, 32 years later, in a wooded area near Eveleth, Minn. The FBI's files on Paul and Sheila Wellstone [show that] the FBI initially took interest in Wellstone as part of the broader surveillance of the American left ... and, in the end, [sifted] through the wreckage of the fatal plane crash that killed Wellstone and seven others eight years ago. Wellstone's surviving sons declined to comment on the documents, which were obtained in response to a Freedom of Information Act request filed by MPR News. The FBI did not include 76 pages related to the National Transportation Safety Board, the agency that investigated the crash. A request for those records is pending. Coleen Rowley, the 9/11 whistleblower and former chief legal advisor in the FBI's Minneapolis office, said the documents from 1970 shed light on the FBI's far-reaching efforts to quash political dissent. "I think this really is valuable because it's basically history repeating what we have right now," she said, noting the recent FBI raids at the homes of several anti-war organizers in Minneapolis. Wellstone's arrest occurred less than a year before the official end of Cointelpro, a series of secret domestic surveillance programs created by FBI Director J. Edgar Hoover to monitor and disrupt groups deemed to be a threat to national security.
Note: For insights into the deeper implications of Senator Wellstone's mysterious plane crash, click here.
Every email, phone call and website visit is to be recorded and stored after the Coalition Government revived controversial Big Brother snooping plans. It will allow security services and the police to spy on the activities of every Briton who uses a phone or the internet. Moves to make every communications provider store details for at least a year will be unveiled later this year sparking fresh fears over a return of the surveillance state. It comes despite the Coalition Agreement promised to "end the storage of internet and email records without good reason". The plans are expected to involve service providers storing all users details for a set period of time. That will allow the security and police authorities to track every phone call, email, text message and website visit made by the public if they argue it is needed to tackle crime or terrorism. The information will include who is contacting whom, when and where and which websites are visited, but not the content of the conversations or messages. The move was buried in the Government's Strategic Defence and Security Review.
Note: For lots more from major media sources on increasing government and corporate threats to privacy, click here.
Yasir Afifi, a 20-year-old computer salesman and community-college student, took his car in for an oil change earlier this month and his mechanic spotted an odd wire hanging from the undercarriage. The wire was attached to a strange magnetic device that puzzled Afifi and the mechanic. They freed it from the car and posted images of it online, asking for help in identifying it. Two days later, FBI agents arrived at Afifi's Santa Clara apartment and demanded the return of their property a global-positioning-system tracking device now at the center of a raging legal debate over privacy rights. One federal judge wrote that the widespread use of the device was straight out of George Orwell's novel Nineteen Eighty-Four." By holding that this kind of surveillance doesn't impair an individual's reasonable expectation of privacy, the panel hands the government the power to track the movements of every one of us, every day of our lives," wrote Alex Kozinski, the chief judge of the 9th U.S. Circuit Court of Appeals, in a blistering dissent in which a three-judge panel from his court ruled that search warrants weren't necessary for GPS tracking. In his dissent, Chief Judge Kozinski noted that GPS technology is far different from tailing a suspect on a public road, which requires the active participation of investigators. "The devices create a permanent electronic record that can be compared, contrasted and coordinated to deduce all manner of private information about individuals," Kozinksi wrote.
Note: For an AP photo of this device, click here.
A privacy watchdog has uncovered a government memo that encourages federal agents to befriend people on a variety of social networks, to take advantage of their readiness to share -- and to spy on them. In response to a Freedom of Information request, the government released a handful of documents, including a May 2008 memo detailing how social-networking sites are exploited by the Office of Fraud Detection and National Security (FDNS). Facebook, Twitter, MySpace, and Digg had not commented on the report, which details the official government program to spy via social networking. Other websites the government is spying on include ... Craigslist and Wikipedia, according to the Electronic Frontier Foundation (EFF), which filed the FOIA request. "Narcissistic tendencies in many people fuel a need to have a large group of 'friends' link to their pages, and many of these people accept cyber-friends that they don't even know," stated one of the documents obtained by the EFF. "This provides an excellent vantage point for FDNS to observe the daily life of [members]," it said. Among the networks specifically cited for analysis "were general social networking sites like Facebook, MySpace, Twitter, and Flickr, as well as sites that focus specifically on certain demographic groups such as MiGente and BlackPlanet, news sites such as NPR, and political commentary sites DailyKos," the EFF wrote.
Note: For more information, read the full report at the Electronic Frontier Foundation.
News that the US is buying custom-made vans packed with something called backscatter X-ray capacity has riled privacy advocates and sparked internet worries about "feds radiating Americans." American Science & Engineering, a Billerica, Mass.-company, tells Forbes it [has] sold more than 500 ZBVs, or Z Backscatter Vans, to US and foreign governments. The Department of Defense has bought the most for war zone use, but US law enforcement has also deployed the vans to [use] inside the US, according to Joe Reiss, a company spokesman. On [September 28], a counterterror operation snarled truck traffic on I-20 near Atlanta, where Department of Homeland Security teams used mobile X-ray technology to check the contents of truck trailers. Authorities said the inspections weren't prompted by any specific threat. Backscatter X-ray is already part of an ongoing national debate about its use in so-called full body scanners being deployed in many US airports. [Critics] worry that radiating Americans without their knowledge is evidence of gradually eroding constitutional protections in the post-9/11 age. "This is another way in which the government is capturing information they may lose control over. I just have some real problems with the idea of even beginning a campaign of rolling surveillance of American citizens, which is what this essentially is said [Vermont-based privacy expert Frederick Lane, author of American Privacy.]
Note: For further reports from reliable sources on the militarization of US police forces, click here.
Government agents can sneak onto your property in the middle of the night, put a GPS device on the bottom of your car and keep track of everywhere you go. This doesn't violate your Fourth Amendment rights, because you do not have any reasonable expectation of privacy in your own driveway and no reasonable expectation that the government isn't tracking your movements. That is the bizarre and scary rule that now applies in California and eight other Western states. The U.S. Court of Appeals for the Ninth Circuit, which covers this vast jurisdiction, recently decided the government can monitor you in this way virtually anytime it wants with no need for a search warrant. It is a dangerous decision one that, as the dissenting judges warned, could turn America into the sort of totalitarian state imagined by George Orwell. It is particularly offensive because the judges added insult to injury with some shocking class bias: the little personal privacy that still exists, the court suggested, should belong mainly to the rich. Plenty of liberals have objected to this kind of spying, but it is the conservative Chief Judge Kozinski who has done so most passionately. "1984 may have come a bit later than predicted, but it's here at last," he lamented in his dissent. And invoking Orwell's totalitarian dystopia where privacy is essentially nonexistent, he warned: "Some day, soon, we may wake up and find we're living in Oceania."
Note: For key reports from reliable souces on increasing government threats to civil liberties, click here.
Mexico's sixth-largest city, Leon, is on the road to ... a future in which everyone is tracked wherever they go. Fast Company reports that U.S. biometrics firm Global Rainmakers and its Mexican partner announced yesterday that they have begun installing iris-scanning technology in the city of more than 1 million in Guanajuato state. The companies aim ... to create "the most secure city in the world." The first phase concentrates on law enforcement and security checkpoints. Then the iris scanners, which the firms say can "identify humans in motion and at a distance while ensuring liveness," will fill malls, pharmacies, mass transit, medical centers and banks, "among other public and private locations," Fast Company writes. "In the future, whether it's entering your home, opening your car, entering your workspace, getting a pharmacy prescription refilled, or having your medical records pulled up, everything will come off that unique key that is your iris," says Jeff Carter, CDO of Global Rainmakers. Before coming to GRI, Carter headed a think tank partnership between Bank of America, Harvard, and MIT. "Every person, place, and thing on this planet will be connected [to the iris system] within the next 10 years," he says.
Note: For lots more from reliable sources on threats to privacy, click here.
At a warehouse in New Jersey, 6,000 used copy machines sit ready to be sold. Almost every one of them holds a secret. Nearly every digital copier built since 2002 contains a hard drive ... storing an image of every document copied, scanned, or emailed by the machine. In the process, it's turned an office staple into a digital time-bomb packed with highly-personal or sensitive data. If you're in the identity theft business it seems this would be a pot of gold. "The type of information we see on these machines with the social security numbers, birth certificates, bank records, income tax forms," John Juntunen said, "that information would be very valuable." Juntunen's Sacramento-based company Digital Copier Security developed software called "INFOSWEEP" that can scrub all the data on hard drives. He's been trying to warn people about the potential risk - with no luck. All the major [digital copier] manufacturers told us they offer security or encryption packages on their products. One product from Sharp automatically erases an image from the hard drive. It costs $500. But evidence keeps piling up in warehouses that many businesses are unwilling to pay for such protection, and that the average American is completely unaware of the dangers posed by digital copiers.
Note: For lots more from reliable sources on threats to privacy, click here.
A federal judge ruled [on March 31] that the National Security Agencys program of surveillance without warrants was illegal, rejecting the Obama administrations effort to keep shrouded in secrecy one of the most disputed counterterrorism policies of former President George W. Bush. In a 45-page opinion, Judge Vaughn R. Walker ruled that the government had violated a 1978 federal statute requiring court approval for domestic surveillance when it intercepted phone calls of Al Haramain, a now-defunct Islamic charity in Oregon, and of two lawyers representing it in 2004. Declaring that the plaintiffs had been subjected to unlawful surveillance, the judge said the government was liable to pay them damages. The ruling by Judge Walker, the chief judge of the Federal District Court in San Francisco, rejected the Justice Departments claim first asserted by the Bush administration and continued under President Obama that the charitys lawsuit should be dismissed without a ruling on the merits because allowing it to go forward could reveal state secrets. The judge characterized that expansive use of the so-called state-secrets privilege as amounting to unfettered executive-branch discretion that had obvious potential for governmental abuse and overreaching.
Note: For illumination of the dark world of state secrecy, click here.
The CIA is to be given broad access to the bank records of millions of Britons under a European Union plan to fight terrorism. The Brussels agreement, which will come into force in two months time, requires the 27 EU member states to grant requests for banking information made by the United States under its terrorist finance tracking programme. The EU said it had agreed that Europeans would be compelled to release the information to the CIA as a matter of urgency. The records will be kept in a US database for five years before being deleted. Critics say the system is lopsided because there is no reciprocal arrangement under which the UK authorities can easily access the bank accounts of US citizens. They also say the plan to sift through cross-border and domestic EU bank accounts gives US intelligence more scope to consult our bank accounts than is granted to law enforcement agencies in the UK or the rest of Europe. This weekend civil liberties groups and privacy campaigners said the surveillance programme, introduced as an emergency measure in 2001, was being imposed on Britain without a proper debate. Shami Chakrabarti, director of Liberty, said: The massive scope for transferring personal information from Europe to the United States is extremely worrying, especially in the absence of public debate or parliamentary scrutiny either at EU or domestic level.
Note: For reports from major media sources on erosion of privacy by governments and corporations, click here.
In a case that raises questions about online journalism and privacy rights, the U.S. Department of Justice sent a formal request to an independent news site ordering it to provide details of all reader visits on a certain day. The grand jury subpoena also required the Philadelphia-based Indymedia.us Web site "not to disclose the existence of this request" unless authorized by the Justice Department, a gag order that presents an unusual quandary for any news organization. Kristina Clair, a 34-year old Linux administrator living in Philadelphia who provides free server space for Indymedia.us, said she was shocked to receive the Justice Department's subpoena. The subpoena ... demanded "all IP traffic to and from www.indymedia.us" on June 25, 2008. It instructed Clair to "include IP addresses, times, and any other identifying information," including e-mail addresses, physical addresses, registered accounts, and Indymedia readers' Social Security Numbers, bank account numbers, [and] credit card numbers. Clair [called] the Electronic Frontier Foundation in San Francisco, which represented her at no cost. Making this investigation more mysterious is that Indymedia.us is an aggregation site, meaning articles that appear on it were published somewhere else first, and there's no hint about what sparked the criminal probe. Clair, the system administrator, says that no IP (Internet Protocol) addresses are recorded for Indymedia.us, and non-IP address logs are kept for a few weeks and then discarded. "This is the first time we've seen them try to get the IP address of everyone who visited a particular site," [EFF's Kevin] Bankston said. "That it was a news organization was an additional troubling fact that implicates First Amendment rights."
Note: For many reports from major media sources of growing government threats to civil liberties, click here.
Suppose you're returning home from a vacation in Cancun. A customs agent asks you to open your suitcase so he can check its contents. So far, so good. Now, the agent asks you to log on to your laptop so he can read your e-mails and personal files and examine which Web sites you've visited. He makes a copy of your hard drive so the government can comb through its contents. You've done nothing to give the agent any cause for suspicion. That can't be legal - can it? Until recently, it would not have been allowed. Long-standing customs directives prohibited agents from reading travelers' personal documents unless they reasonably suspected them to be merchandise or evidence of illegal activity. Then the Bush administration changed the rules, allowing agents to "review and analyze" the contents of electronic devices, including laptops, cell phones and BlackBerrys "absent individualized suspicion." Agents also could make copies of the devices' contents and share them with other government agencies. In a Senate Judiciary Committee hearing in May, Secretary of Homeland Security Janet Napolitano promised to review the policy. Homeland Security has now released a new policy - and it is the same as the Bush policy in almost every relevant respect. The government may still search electronic devices without reasonable suspicion, retain copies indefinitely to complete its search and share information with other agencies. Both administrations have cited national security to justify suspicionless searches. There's no evidence, however, that a suspicionless search has ever turned up a security threat.
Note: The author of this op-ed, Elizabeth Goitein, is the director of the Liberty and National Security Project at the Brennan Center for Justice at NYU School of Law. For lots more on how politicians use "national security" as a means to protect their own manipulations at the expense of the public good, click here.
Climbing into his Volvo, outfitted with a Matrics antenna and a Motorola reader he'd bought on eBay for $190, Chris Paget cruised the streets of San Francisco with this objective: To read the identity cards of strangers, wirelessly, without ever leaving his car. It took him 20 minutes to strike hacker's gold. Zipping past Fisherman's Wharf, his scanner detected, then downloaded to his laptop, the unique serial numbers of two pedestrians' electronic U.S. passport cards embedded with radio frequency identification, or RFID, tags. Within an hour, he'd "skimmed" the identifiers of four more of the new, microchipped PASS cards from a distance of 20 feet. Paget's February experiment demonstrated something privacy advocates had feared for years: That RFID, coupled with other technologies, could make people trackable without their knowledge or consent. He filmed his drive-by heist, and soon his video went viral on the Web, intensifying a debate over a push by government, federal and state, to put tracking technologies in identity documents and over their potential to erode privacy. With advances in tracking technologies coming at an ever-faster rate, critics say, it won't be long before governments could be able to identify and track anyone in real time, 24-7, from a cafe in Paris to the shores of California. The key to getting such a system to work, these opponents say, is making sure everyone carries an RFID tag linked to a biometric data file. On June 1, it became mandatory for Americans entering the United States by land or sea from Canada, Mexico, Bermuda and the Caribbean to present identity documents embedded with RFID tags, though conventional passports remain valid until they expire.
Note: For lots more on corporate and government surveillance, click here.
The National Security Agency is facing renewed scrutiny over the extent of its domestic surveillance program, with critics in Congress saying its recent intercepts of the private telephone calls and e-mail messages of Americans are broader than previously acknowledged, current and former officials said. Since April, when it was disclosed that the intercepts of some private communications of Americans went beyond legal limits in late 2008 and early 2009, several Congressional committees have been investigating. Those inquiries have led to concerns in Congress about the agencys ability to collect and read domestic e-mail messages of Americans on a widespread basis, officials said. Supporting that conclusion is the account of a former N.S.A. analyst who, in a series of interviews, described being trained in 2005 for a program in which the agency routinely examined large volumes of Americans e-mail messages without court warrants. Two intelligence officials confirmed that the program was still in operation. Both the former analysts account and the rising concern among some members of Congress about the N.S.A.s recent operation are raising fresh questions about the spy agency. Representative Rush Holt, Democrat of New Jersey and chairman of the House Select Intelligence Oversight Panel, has been investigating the incidents and said he had become increasingly troubled by the agencys handling of domestic communications. In an interview, Mr. Holt disputed assertions by Justice Department and national security officials that the overcollection was inadvertent. Some actions are so flagrant that they cant be accidental, Mr. Holt said.
Note: For lots more from major media sources on the ever-increasing government and coroporate threats to privacy, click here.
The Pentagon plans to create a new military command for cyberspace ... stepping up preparations by the armed forces to conduct both offensive and defensive computer warfare. White House officials say Mr. Obama has not yet been formally presented with the Pentagon plan. But he is expected to sign a classified order in coming weeks that will create the military cybercommand, officials said. It is a recognition that the United States already has a growing number of computer weapons in its arsenal and must prepare strategies for their use as a deterrent or alongside conventional weapons in a wide variety of possible future conflicts. [A] main dispute has been over whether the Pentagon or the National Security Agency should take the lead in preparing for and fighting cyberbattles. Under one proposal still being debated, parts of the N.S.A. would be integrated into the military command so they could operate jointly. A classified set of presidential directives is expected to lay out the militarys new responsibilities and how it coordinates its mission with that of the N.S.A., where most of the expertise on digital warfare resides today. The decision to create a cybercommand is a major step beyond the actions taken by the Bush administration, which authorized several computer-based attacks but never resolved the question of how the government would prepare for a new era of warfare fought over digital networks. Officials declined to describe potential offensive operations, but said they now viewed cyberspace as comparable to more traditional battlefields.
Note: Combine this with the BBC's revealing article on US plans to fight the Internet, and there is reason for concern. For lots more on new developments in modern war planning, click here.
The National Security Agency intercepted private e-mail messages and phone calls of Americans in recent months on a scale that went beyond the broad legal limits established by Congress last year, government officials said in recent interviews. Several intelligence officials, as well as lawyers briefed about the matter, said the N.S.A. had been engaged in overcollection of domestic communications of Americans. They described the practice as significant and systemic. The legal and operational problems surrounding the N.S.A.s surveillance activities have come under scrutiny from the Obama administration, Congressional intelligence committees and a secret national security court. Congressional investigators say they hope to determine if any violations of Americans privacy occurred. It is not clear to what extent the agency may have actively listened in on conversations or read e-mail messages of Americans without proper court authority, rather than simply obtained access to them. While the N.S.A.s operations in recent months have come under examination, new details are also emerging about earlier domestic-surveillance activities, including the agencys attempt to wiretap a member of Congress, without court approval, on an overseas trip. After a contentious three-year debate that was set off by the disclosure in 2005 of the program of wiretapping without warrants that President George W. Bush approved after the Sept. 11 attacks, Congress gave the N.S.A. broad new authority to collect, without court-approved warrants, vast streams of international phone and e-mail traffic as it passed through American telecommunications gateways.
Note: For further disturbing reports from reliable sources on government efforts to establish total surveillance systems, click here.
The Maryland State Police surveillance of advocacy groups was far more extensive than previously acknowledged, with records showing that troopers monitored -- and labeled as terrorists -- activists devoted to such wide-ranging causes as promoting human rights and establishing bike lanes. Intelligence officers created a voluminous file on Norfolk-based People for the Ethical Treatment of Animals, calling the group a "security threat" because of concerns that members would disrupt the circus. Angry consumers fighting a 72 percent electricity rate increase in 2006 were targeted. The DC Anti-War Network, which opposes the Iraq war, was designated a white supremacist group, without explanation. One of the possible "crimes" in the file police opened on Amnesty International, a world-renowned human rights group: "civil rights." The [surveillance] ... confirmed the fears of civil liberties groups that have warned about domestic spying since the Sept. 11, 2001, attacks. "No one was thinking this was al-Qaeda," said Stephen H. Sachs, a former U.S. attorney and state attorney general appointed by Gov. Martin O'Malley (D) to review the case. "But 9/11 created an atmosphere where cutting corners was easier." Maryland has not been alone. The FBI and police departments in several cities, including Denver in 2002 and New York before the 2004 Republican National Convention, also responded to [dissent] by spying on activists.
Note: For wide coverage from reliable sources of disturbing threats to civil liberties, click here.
Using technology originally developed for mass disasters, Boston disease trackers are embarking on a novel experiment - one of the first in the country - aimed at eventually creating a citywide registry of everyone who has had a flu vaccination. The resulting vaccination map would allow swift intervention in neighborhoods left vulnerable to the fast-moving respiratory illness. The trial starts this afternoon, when several hundred people are expected to queue up for immunizations at the headquarters of the Boston Public Health Commission. Each of them will get a bracelet printed with a unique identifier code. Information about the vaccine's recipients, and the shot, will be entered into handheld devices similar to those used by delivery truck drivers. Infectious disease specialists in Boston and elsewhere predicted that the registry approach could prove even more useful if something more sinister strikes: a bioterrorism attack or the long-feared arrival of a global flu epidemic. In such crises, the registry could be used to track who received a special vaccine or antidote to a deadly germ. "Anything you can do to better pinpoint who's vaccinated and who's not, that's absolutely vital," said Michael Osterholm, director of the Center for Infectious Disease Research & Policy at the University of Minnesota. "I wish more cities were doing this kind of thing." When people arrive for their shots, they will get an ID bracelet with a barcode. Next, basic information - name, age, gender, address - will be entered into the patient tracking database. There will be electronic records, too, of who gave the vaccine and whether it was injected into the right arm or the left, and time-stamped for that day.
Note: For more on the serious risks and dangers posed by vaccines, click here and here.
Procurement documents released by the U.S. Air Force give a rare glimpse into Pentagon plans for developing an offensive cyber-war capacity that can infiltrate, steal data from and, if necessary, take down enemy information-technology networks. The Broad Area Announcement, posted ... by the Air Force Research Laboratory's Information Directorate, outlines a two-year, $11 million effort to develop capabilities to "access ... any remotely located open or closed computer information systems," lurk on them "completely undetected," "stealthily exfiltrate information" from them and ultimately "be able to affect computer information systems through Deceive, Deny, Disrupt, Degrade, Destroy (D5) effects." "Of interest," the announcement says, "are any and all techniques to enable user and/or root-level access to both fixed [and] mobile computing platforms ... [and] methodologies to enable access to any and all operating systems, patch levels, applications and hardware." The announcement is the latest stage in the Air Force's effort to develop a cyber-war capability and establish itself as the service that delivers U.S. military power in cyberspace. Last year, the Air Force announced it was setting up a Cyberspace Command ... and was developing military doctrine for the prosecution of cyber-war operations. The developments highlight the murky legal territory on which the cyber-wars of the future will be fought. More important, because of the difficulties in identifying attackers and immediately quantifying damage from a cyber-attack, it can be hard to determine when such attacks constitute an act of war as opposed to crime or even vandalism.
The FBI has withdrawn a secret administrative order seeking the name, address and online activity of a patron of the Internet Archive after the San Francisco-based digital library filed suit to block the action. It is one of only three known instances in which the FBI has backed off from such a data demand, known as a "national security letter," or NSL, which is not subject to judicial approval and whose recipient is barred from disclosing the order's existence. NSLs are served on phone companies, Internet service providers and other electronic communications service providers, but because of the gag order provision, the public has little way to know about them. FBI officials now issue about 50,000 such orders a year. The order against the Internet Archive was served Nov. 26, and the nonprofit challenged it based on a provision of the reauthorized USA Patriot Act, which protects libraries from such requests. The privacy advocacy group Electronic Frontier Foundation represented the archive in the suit, which was joined by the American Civil Liberties Union. The archive also alleged that the gag order that accompanied the data demand violated the Constitution. As part of their settlement, the FBI agreed to drop the gag order and the archive agreed to withdraw the complaint. The case was unsealed Monday. Yesterday, redacted versions of key documents were filed, allowing the parties to discuss the case. "We see this as an unqualified success," said Brewster Kahle, the archive's co-founder and digital librarian. "The goal here was to help other recipients of NSLs to understand that you can push back."
Note: The Internet Archive has now posted excellent information on how to deal with cases like this at http://government.zdnet.com/?p=3795. Three cheers for the Internet Archive!
Welcome to the new world of border security. Unsuspecting Americans are turning up at the Canadian border expecting clear sailing, only to find that their past -- sometimes their distant past -- is suddenly an issue. There was a time not long ago when a trip across the border from the United States to Canada was accomplished with a wink and a wave of a driver's license. Those days are over. Take the case of 55-year-old Lake Tahoe resident Greg Felsch. Stopped at the border in Vancouver this month at the start of a planned five-day ski trip, he was sent back to the United States because of a DUI conviction seven years ago. Not that he had any idea what was going on when he was told at customs: "Your next stop is immigration." Felsch was ushered into a room. "There must have been 75 people in line," he says. "We were there for three hours. One woman was in tears. A guy was sent back for having a medical marijuana card. I felt like a felon with an ankle bracelet." Or ask the well-to-do East Bay couple who flew to British Columbia this month for an eight-day ski vacation at the famed Whistler Chateau, where rooms run to $500 a night. They'd made the trip many times, but were surprised at the border to be told that the husband would have to report to "secondary" immigration. There, in a room he estimates was filled with 60 other concerned travelers, he was told he was "a person who was inadmissible to Canada." The problem? A conviction for marijuana possession ... in 1975. This is just the beginning. Soon other nations will be able to look into your past when you want to travel there.
Russell Tice, a longtime insider at the National Security Agency, is now a whistleblower the agency would like to keep quiet. For 20 years, Tice worked in the shadows as he helped the United States spy on other people's conversations around the world. "I specialized in what's called special access programs," Tice said of his job. "We called them 'black world' programs and operations." But now, Tice tells ABC News that some of those secret "black world" operations run by the NSA were operated in ways that he believes violated the law. He is prepared to tell Congress all he knows about the alleged wrongdoing in these programs run by the Defense Department and the NSA. Tice says the technology exists to track and sort through every domestic and international phone call...and to search for key words or phrases that a terrorist might use. President Bush has admitted that he gave orders that allowed the NSA to eavesdrop on a small number of Americans without the usual requisite warrants. But Tice disagrees. He says the number of Americans subject to eavesdropping by the NSA could be in the millions. The NSA revoked Tice's security clearance in May of last year based on what it called psychological concerns and later dismissed him. Tice calls that bunk and says that's the way the NSA deals with troublemakers and whistleblowers.
Note: For many years, both the U.S. and U.K. denied the existence of Echelon, which according to the BBC article below is a "spying network that can eavesdrop on every single phone call, fax or e-mail, anywhere on the planet." http://news.bbc.co.uk/1/hi/world/503224.stm
The FBI, while waging a highly publicized war against terrorism, has spent resources gathering information on antiwar and environmental protesters and on activists who feed vegetarian meals to the homeless, the agency's internal memos show. For years, the FBI's definition of terrorism has included violence against property. That definition has led FBI investigations to online discussion boards, organizing meetings and demonstrations of a wide range of activist groups. The FBI's encounters with activists are described in hundreds of pages of documents obtained by the American Civil Liberties Union under the Freedom of Information Act after agents visited several activists before the 2004 political conventions. ACLU attorneys acknowledge that the FBI memos are heavily redacted and contain incomplete portraits of some cases. Still, the attorneys say, the documents show that the FBI has monitored groups that were not suspected of any crime. FBI officials respond that there is nothing improper about agents attending a meeting or demonstration.
The first annual National Security Whistleblowers Conference...has to be one of the more unusual gatherings of intelligence veterans in recent years. The nearly 20 current or former officials from the FBI, CIA, Defense Intelligence Agency, and even the supersecret National Security Agency who make up the core of the conference share an unusual distinction: They are all deeply out of favor with their longtime employers. Most cannot discuss the allegations they are making in detail because the specifics are highly classified. The agencies they work for also refuse to answer questions. The current and former officials at the conference said that today's climate in Washington has never been worse for whistleblowers. One of the biggest names of the conference never even uttered a word. Lt. Col. Anthony Shaffer is the military intelligence operative who...went public with a controversial claim that a year before September 11, his top-secret task force "Able Danger" was able to identify the man who later turned out to be the lead hijacker [on 9/11]. Shaffer was slated to speak but instead sat quietly by as his lawyer, Mark Zaid, spoke for him. "Tony is not allowed to talk," Zaid said. "He is gagged from talking to Congress." The conference was organized by Sibel Edmonds, a former FBI translator who was pushed out of the bureau after raising accusations of wrongdoing by other FBI translators. She has been barred from discussing the details of her case by the FBI. She created the National Security Whistleblowers Coalition www.nswbc.org to bring whistleblowers like her together to push for legal reforms.
Note: For a detailed article in Vanity Fair on Sibel Edmonds' courageous efforts to expose the truth, click here. For the whistleblowing action which drew international media attention by WantToKnow.info founder Fred Burks, click here.
The only grade school in this rural town is requiring students to wear radio frequency identification badges that can track their every move. Some parents are outraged, fearing it will rob their children of privacy. The badges introduced at Brittan Elementary School on Jan. 18 rely on the same radio frequency and scanner technology that companies use to track livestock and product inventory. The system was imposed, without parental input, by the school as a way to simplify attendance-taking and potentially reduce vandalism and improve student safety. Some parents see a system that can monitor their children's movements on campus as something straight out of Orwell. This latest adaptation of radio frequency ID technology was developed by InCom Corp., a local company co-founded by the parent of a former Brittan student, and some parents are suspicious about the financial relationship between the school and the company. InCom has paid the school several thousand dollars for agreeing to the experiment, and has promised a royalty from each sale if the system takes off, said the company's co-founder, Michael Dobson, who works as a technology specialist in the town's high school.
Scientists have discovered a way of manipulating a gene that turns animals into drones that do not become bored with repetitive tasks. The experiments, conducted on monkeys, are the first to demonstrate that animal behaviour can be permanently changed, turning the subjects from aggressive to "compliant" creatures. The genes are identical in humans and although the discovery could help to treat depression and other types of mental illness, it will raise images of the Epsilon caste from Aldous Huxley's futuristic novel Brave New World. The experiments... involved blocking the effect of a gene called D2 in a particular part of the brain. This cut off the link between the rhesus monkeys' motivation and reward. Instead of speeding up with the approach of a deadline or the prospect of a "treat," the monkeys in the experiment could be made to work just as enthusiastically for long periods. The scientists say the identical technique would apply to humans. [They] found that they could make the monkeys work their hardest and fastest all the time, without any complaint or sign of slacking, just by manipulating D2 so that they forgot about the expectation of reward. Methods of manipulating human physical and psychological traits are just around the corner, and the technology will emerge first as a lucrative add-on available from in vitro fertilization clinics. "There's no doubt we will be able to influence behaviour," said Julian Savulescu, a professor of ethics at Oxford University.
Note: For lots more reliable information on how human behavior is already being manipulated, click here.
Queuing to get into one nightclub in Spain could soon be a thing of the past for regular customers thanks to a tiny computer chip implanted under their skin. The technology, known as a VeriChip, also means nightclubbers can leave their cash and cards at home and buy drinks using a scanner. The bill can then be paid later. Clubbers who want to join the scheme at Baja Beach Club in Barcelona pay 125 euros (about US $150) for the VeriChip -- about the size of a grain of rice -- to be implanted in their body. Then when they pass through a scanner the chip is activated and it emits a signal containing the individual's number, which is then transmitted to a secure data storage site. The club's director, Conrad Chase, said he began using the VeriChip, made by Applied Digital Solutions, in March 2004 because he needed something similar to a VIP card and wanted to provide his customers with better service. He said 10 of the club's regular customers, including himself, have been implanted with the chip, and predicted more would follow. "I know many people who want to be implanted," said Chase. "Almost everybody now has a piercing, tattoos or silicone. Why not get the chip and be original?" Chase said VeriChip could also boost security by speeding up checks at airports, for example. He denied the scheme had any drawbacks. The VeriChip is an in-house debit card and contains no personal information.
Note: Why is the media so upbeat about this? The article raises very few questions, yet seems to promote microchip implants in humans as the wave of the future for commerce.
Starting in the early 1900s, hundreds of thousands of American children were warehoused in institutions by state governments. And the federal government did nothing to stop it. The justification? The kids had been labeled feeble-minded, and were put away in conditions that can only be described as unspeakable. A large proportion of the kids who were locked up were not retarded at all. They were simply poor, uneducated kids with no place to go, who ended up in institutions like the Fernald School in Waltham, Mass. The Fernald School, and others like it, was part of a popular American movement in the early 20th century called the Eugenics movement. The idea was to separate people considered to be genetically inferior from the rest of society, to prevent them from reproducing. Eugenics is usually associated with Nazi Germany, but in fact, it started in America. Not only that, it continued here long after Hitler's Germany was in ruins. Few of the attendants [at Fernald] showed any kindness. And ... there was sexual abuse. The place was tailor made for it. The school [also] allowed them to be used as human guinea pigs. In 1994 Senate hearings, it came out that scientists from MIT had been giving radioactive oatmeal to the boys ... in a nutrition study for Quaker Oats. All they knew is that they'd been asked to join a science club. The boys were recruited with special treats [like] extra milk. But they forgot to mention the milk was radioactive, says David White-Lief, an attorney who worked on the state task force investigating the science club. These experiments, because of the lack of informed consent, violated the Nuremburg Code established just 10 years earlier, says White-Lief.
Note: The extreme racism of the Nazis was quite popular among certain groups in the U.S. For lots more on how these ideas came to pervade some groups in U.S. intelligence services, click here. For a powerful list of military and government sponsored experiments on human guinea pigs with links for verification, click here.
Jerome Dobson is not joking. The University of Kansas research professor, a respected leader in the field of geographic information technologies [speculates about] "geoslavery" -- a form of technological human control that could make "George Orwell's `Big Brother' nightmare ... look amateurish." He's talking about overlords electronically punishing errant workers. He's talking about the possibility of people hooked to, tracked by, and potentially shocked or burned using inexpensive electronic bracelets, manacles or implants. Dobson worked for 26 years at Tennessee's Oak Ridge National Laboratory creating, for the government, the maps used in global tracking. He is the president of the American Geographical Society. And he is not alone in his thoughts. [In] the journal published by the Institute of Electrical and Electronics Engineers, a paper titled "Geoslavery" is co-written by Dobson and Peter F. Fisher, British editor of the International Journal of Geographical Information Science. "Human tracking systems, currently sold commercially without restrictions, already empower those who would be masters. Safeguards have not yet evolved to protect those destined to be slaves," they wrote. With a laptop computer, employers can keep track of their drivers' every move. Implanted chips ... keep track of livestock or pets. Whereify Wireless Inc. sells its GPS Kids Locator for $400. The device, which also looks like a watch, can be locked to a child's wrist. Dobson said that ... none of the companies was thinking of anything nefarious. [Yet he] worries that where there is an evil will, there is an evil way. He hopes [to ] create debate and perhaps legislation or safeguards around the technology that will keep it from being misused.
Cybercriminal Eric Eoin Marques pleaded guilty in an American court this week. Marques faces up to 30 years in jail for running Freedom Hosting, which temporarily existed beyond reach of the law and ended up being used to host drug markets, money-laundering operations, hacking groups, and millions of images of child abuse. Investigators were somehow able to break the layers of anonymity that Marques had constructed, leading them to locate a crucial server in France. This discovery eventually led them to Marques himself. Marques was the first in a line of famous cybercriminals to be caught despite believing that using the privacy-shielding anonymity network Tor would make them safe behind their keyboards. The case demonstrates that government agencies can trace suspects through networks that were designed to be impenetrable. Marques has blamed the American NSAs world-class hackers, but the FBI has also been building up its efforts since 2002. And, some observers say, they often withhold key details of their investigations from defendants and judges alikesecrecy that could have wide-ranging cybersecurity implications across the internet. The FBI had found a way to break Tors anonymity protections, but the technical details of how it happened remain a mystery. Perhaps the greatest overarching question related to the investigation of this case is how the government was able to pierce Tors veil of anonymity, Marquess defense lawyers wrote in a recent filing.
Note: For more on this important case, see this informative article. For more along these lines, see concise summaries of deeply revealing news articles on sexual abuse scandals and the disappearance of privacy from reliable major media sources.
San Diego has installed thousands of microphones and cameras in so-called smart streetlamps in recent years as part of a program to assess traffic and parking patterns throughout the city. However, the technology over the last year caught the attention of law enforcement. Today, such video has been viewed in connection with more than 140 police investigations. Officers have increasingly turned to the footage to help crack cases, as frequently as 20 times a month. Police department officials have said that the video footage has been crucial in roughly 40 percent of these cases. Privacy groups have voiced concerns about a lack of oversight, as law enforcement has embraced the new technology. Groups, such as the American Civil Liberties Union, have pushed city councils across the country to adopt surveillance oversight ordinances that create strict rules around using everything from license plate readers to gunshot-detection systems to streetlamp cameras. San Diegos smart streetlamp program started around 2016. Three years later, its still unclear what the data will ultimately be used for. Right now, only the police department has the authority to view the actual video footage. This arrangement has disturbed Matt Cagle, technology and civil liberties attorney with the ACLU. This sounds like the quote, just trust us approach to surveillance technology, which is a recipe for invasive uses and abuse of these systems, he said.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
On Wednesday, Human Rights Watch released a troubling report, which it has since walked back, about a phone application made by the Chinese government. The app provides law enforcement with easy, daily access to data detailing the religious activity, blood type, and even the amount of electricity used by ethnic minority Muslims living in the western province of Xinjiang. The app relies heavily on facial recognition software supplied by Face++, a division of the Chinese startup Megvii. The flurry of media reports this week about Face++ ... and the role of the private sector in building China’s increasingly sprawling surveillance state, however, left out another prominent investor in the company: Hunter Biden. Hunter Biden’s investment company in China, known as Bohai Harvest RST, has pooled money, largely from state-owned venture capital, to buy or invest in a range of industries. In 2017, Bohai Harvest bought into Face++. Bohai Harvest ... has brought Hunter Biden into close proximity to influential Chinese government and business figures. The investment fund has also partnered with a subsidiary of HNA Group. The HNA Group has made unusually extensive efforts to cultivate U.S. officials. The company floated an offer to buy out the hedge fund owned by former White House official Anthony Scaramucci; retained the legal services of Gary Locke, the former U.S. ambassador to China, shortly before his confirmation; and provided financing to a private-equity firm backed by Jeb Bush.
Note: This informative video delves into the shady dealings of Hunter Biden. For more along these lines, see concise summaries of deeply revealing news articles on corruption in government and in the corporate world from reliable major media sources.
The U.S. government created a secret database of activists, journalists, and social media influencers tied to the migrant caravan and in some cases, placed alerts on their passports. At the end of 2018, roughly 5,000 immigrants from Central America made their way north through Mexico to the United States southern border. As the migrant caravan reached the San Ysidro Port of Entry in south San Diego County, so did journalists, attorneys, and advocates who were there to work and witness the events unfolding. But in the months that followed, journalists who covered the caravan, as well as those who offered assistance to caravan members, said they felt they had become targets of intense inspections and scrutiny by border officials. Documents leaked to NBC 7 Investigates show [that the] government had listed their names in a secret database of targets, where agents collected information on them. Some had alerts placed on their passports, keeping at least two photojournalists and an attorney from entering Mexico to work. The documents were provided to NBC 7 by a Homeland Security source on the condition of anonymity. The individuals listed include ten journalists, seven of whom are U.S. citizens, a U.S. attorney, and 48 people from the U.S. and other countries, labeled as organizers, instigators or their roles unknown. In addition to flagging the individuals for secondary screenings, the Homeland Security source told NBC 7 that the agents also created dossiers on each person listed.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the erosion of civil liberties.
Angeline Cheek is preparing for disaster. The indigenous organizer from the Fort Peck reservation in Montana fears that the proposed Keystone XL pipeline could break and spill. But environmental catastrophe is not the most immediate threat. The government has characterized pipeline opponents like her as extremists and violent criminals and warned of potential terrorism. Recently released records [suggest] that police were organizing to launch an aggressive response to possible Keystone protests, echoing the actions against the Standing Rock movement in North Dakota. There, officers engaged in intense surveillance and faced widespread accusations of excessive force. Documents obtained by the ACLU ... have renewed concerns from civil rights advocates about the governments treatment of indigenous activists known as water protectors. Notably, one record revealed that authorities hosted a recent anti-terrorism training session in Montana. The Department of Homeland Security (DHS) and the Federal Emergency Management Agency also organized a field force operations training to teach mass-arrest procedures, riot-control formations and other crowd-control methods.
Note: For more along these lines, see concise summaries of deeply revealing civil liberties news articles from reliable major media sources.
A former U.S. Secret Service agent named Peter Cavicchia III ran special ops for JPMorgan Chase & Co. His insider threat group ... used computer algorithms to monitor the banks employees. Aided by as many as 120 forward-deployed engineers from the data mining company Palantir Technologies Inc., which JPMorgan engaged in 2009, Cavicchias group vacuumed up emails and browser histories, GPS locations ... and transcripts of digitally recorded phone conversations. It all ended when the banks senior executives learned that they, too, were being watched. [The] spying scandal ... which has never been reported, also marked an ominous turn for Palantir. An intelligence platform designed for the global War on Terror was weaponized against ordinary Americans at home. Founded in 2004 by Peter Thiel and some fellow PayPal alumni, Palantir cut its teeth working for the Pentagon and the CIA. The U.S. Department of Health and Human Services uses Palantir. The FBI uses it. The Department of Homeland Security deploys it. Police and sheriffs departments in New York, New Orleans, Chicago, and Los Angeles have also used it, frequently ensnaring in the digital dragnet people who arent suspected of committing any crime. JPMorgans experience remains instructive. The world changed when it became clear everyone could be targeted using Palantir, says a former JPMorgan cyber expert who worked with Cavicchia at one point on the insider threat team. Everyones a suspect, so we monitored everything.
Note: Palantir was one of the private intelligence firms that reportedly conspired to discredit activists and journalist Glenn Greenwald, in part by submitting fake documents to WikiLeaks. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
Last week, the existence of a draft Department of Homeland Security (DHS) report came to light, which calls for long-term surveillance of Sunni Muslim immigrants. Internal documents obtained from the FBI and DHS last year also showed how the agencies are surveilling the Movement for Black Lives, bringing into mind tactics of Cointelpro, an FBI program which secretly and illegally conducted surveillance on the civil rights movement in order to disrupt Americans ability to organize politically. But these are not the only types of surveillance this administration is engaged in. On 18 October, DHS implemented a new rule to track the internet activity of all visa applicants, visa holders and legal permanent residents. The rule would also apply to naturalized US citizens. The new rule would track and store social media account information and other highly sensitive data as part of individuals immigration files. The policy would allow DHS to collect and track immigrants social media accounts handles as well as aliases, and search results from both public search engines as well as commercial databases. The rule ... seems like it was designed with the specific purpose of hampering our freedom of speech, in line with the Trump administrations other chilling tactics of attacks on the press and crackdowns on protesters who do not fall in line with the policies of this administration. This covert surveillance, now culminating in overt spying on immigrants, is designed as a tactic to control and fracture dissent.
Note: Read more about the FBI's infamous Cointelpro program. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
The story of Cambridge Analytica is one of the most profoundly unsettling of our time. SCL/Cambridge Analytica [is] effectively part of the ... defence establishment. This is not just a story about social psychology and data analytics. It has to be understood in terms of a military contractor using military strategies on a civilian population. David Miller, a professor of sociology ... and an authority in psyops and propaganda, says it is an extraordinary scandal that this should be anywhere near a democracy. David, [an] ex-Cambridge Analytica employee, [was] working at the firm when it introduced mass data-harvesting to its psychological warfare techniques. It brought psychology, propaganda and technology together in this powerful new way, David [said]. Facebook was the source of the psychological insights that enabled Cambridge Analytica to target individuals. The company ... bought consumer datasets on everything from magazine subscriptions to airline travel and uniquely it appended these with the psych data to voter files. The goal is to capture every single aspect of every voters information environment, said David. And the personality data enabled Cambridge Analytica to craft individual messages. Cambridge Analytica could target people high in neuroticism, for example, with images of immigrants swamping the country. Brexit came down to ... just over 1% of registered voters. Its not a stretch to believe that ... the global 1% found a way to influence this crucial 1% of British voters.
Note: Another Guardian article recently exposed how billionaire Robert Mercer used new technology to build a corporate empire capable of swinging elections. The above article further details how mass media is being combined with Big Data to produce powerful new forms of mind control.
WikiLeaks leader Julian Assanges revelation last week of the CIAs arsenal of hacking tools had a misplaced tone of surprise. Some scary initial stories argued that the CIA could crack Signal and WhatsApp phone encryption, not to mention your toaster and television. But ... the hardest question here is whether the CIA and other government agencies have a responsibility to disclose to software vendors the holes they discover in computer code, so they can be fixed quickly. This may sound like a no-brainer. The problem is that theres a global market for zero-day exploits (ones that are unknown on the day theyre used). U.S. intelligence agencies buy some of these exploits; so do other countries spy services, criminal gangs and the software vendors themselves. A recent report by the Rand Corp. [calculated that] there are about two dozen companies selling or renting exploits to the United States and its allies, with many of these contractors making between $1 million and $2.5 million annually. More than 200 zero-day exploits studied by Rand went undetected for an average of 6.9 years. Given this evidence, Rand argued, some may conclude that stockpiling zero-days may be a reasonable option to combat potential adversaries. But lets be honest: The real shocker in the WikiLeaks scoop is the demonstration ... that the U.S. government cant keep secrets. It makes little sense for the CIA to argue against disclosing its cyber-tricks to computer companies if this valuable information is going to get leaked ... anyway.
Note: For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
Protesters at the Standing Rock Sioux Reservation in Cannon Ball, N.D., rallying against the Dakota Access oil pipeline have been calling for reinforcements since summertime. As of this week, about 800 people had come. But in the course of just a few days, more than 1.5 million people marked themselves present at the pipeline protest using Facebook - even though they werent actually there. A recent report by the American Civil Liberties Union revealed that law enforcement agencies across the country use location tracking and social media data to identify activists. Protesters have reported phones turning on on their own, phone calls cutting out and live video streams being interrupted as evidence that theyre being spied on, said Jennifer Cook, the policy director for the ACLU of North Dakota. Law enforcement agencies ... said they are not relying on Facebooks check-in system to track protesters. Last week, video of violent clashes between lines of police and protesters circulated online, showing demonstrators running from officers as 142 people were arrested. Most of them were charged with rioting and criminal trespassing. About 300 people have been arrested since the protests began over the summer. Tensions have intensified in recent weeks as the pipelines construction moves closer to a river crossing that activists view as a critical water source that they fear will be compromised by the oil main, which many Native American tribes have said treads on sacred land.
Note: For more on this under-reported movement, see this Los Angeles Times article and this article in the UK's Guardian. For more, see concise summaries of deeply revealing news articles on government corruption and the erosion of civil liberties.
Google has launched a new site that shows absolutely everything it knows about its users. And theres an awful lot of it. The new My Activity page collects all of the data that Google has generated by watching its customers as they move around the web. And depending on your settings that could include a comprehensive list of the websites youve visited and the things youve done with your phone. Google has long allowed its users to see the kinds of information that is being generated as people use the companys products, including letting people listen in on automated recordings that it has made of its users. But the new page collects them together in a more accessible and potentially more terrifying way. The page shows a full catalogue of pages visited, things searched and other activity, grouped by time. It also lets people look at the same timeline through filters looking at specific dates, which go all the way into the past, and specific products like Google search, YouTube or Android. When users open up the page for the first time, pop-ups make the case for why it has been launched and why Google collects quite so much data. By tracking people around the internet it can tailor those ads but people can use the same site to opt out from the tracking entirely, or just delete information that they would rather wasnt used for advertising. Users arent automatically opted into the interest-based advertising tools, despite heavily rolling out the feature.
Note: For more along these lines, see concise summaries of deeply revealing news articles on the disappearance of privacy.
The tools European security agencies now have at their disposal ... would make any American or Canadian intelligence officer drool. Britain has literally created a surveillance state. The British Security Industry Authority estimated three years ago the government has installed about six million closed-circuit TV cameras in the public square; one for every 10 citizens. The French, too, have vastly expanded public video surveillance in recent years. And it's all been done with overwhelming support from the general public, which feels safer for the presence of the surveillance, never mind the lack of objective proof that they are more protected against outrages, which keep on occurring. Both England and France are former colonial powers that ... long ago subordinated individual rights to collective security. Canada and America more dearly cherish individual rights. Still, a surveillance state is growing here, too. David Lyon, a professor of surveillance studies at Queen's University, has identified several public surveillance trends, all of which he says are "increasing at an accelerating rate." Canada is not about to become Western Europe, he says, but "it is incumbent upon us as a society to think about the ethical consequences" of mass surveillance. [Some] would argue that the cameras are desperately needed tools, and that anyone who isn't doing anything wrong has nothing to worry about. That of course is the police state justification. They hate us because we are free, we are told. The fact that we've responded by giving up ever more freedom doesn't seem to matter.
Note: Many of the politicians publicly defending the surveillance state receive huge sums of money from private security companies. For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the disappearance of privacy.
When you watch your Smart TV, it could also be watching you. Vizio, a top television maker, automatically tracks the viewing habits of Smart TV owners and shares that information with advertisers in a way that could connect those preferences to what those customers do on their phones or other mobile devices. Vizio's "Smart Interactivity Program" is turned on by default for its 10 million Smart TV customers. The company analyzes snippets of what you watch, be it on Netflix or traditional television, and connects patterns in your viewing behavior with your Internet Protocol address - an online identifier that can be used to pinpoint every device connected from your home. That includes everything from your laptop and phone to your smart thermostat. That information is then shared with Vizio's partners. There are laws that limit how companies share information about video watching habits, including the Video Privacy Protection Act (VPPA). However, Vizio says that those laws do not apply to its tracking service because the company associates IP addresses with the data rather than a person's name or other "personally identifiable information." Some U.S. courts have held that IP addresses do not constitute personally identifiable information. However, privacy regulators in the European Union disagree. And IP addresses are increasingly used by data brokers to paint detailed portraits of who people are.
Note: In 21st century America, TV watches you. For more along these lines, see concise summaries of deeply revealing news articles about the disappearance of privacy.
The Justice Department has been building a national database to track in real time the movement of vehicles around the U.S., a secret domestic intelligence-gathering program that scans and stores hundreds of millions of records about motorists. The primary goal of the license-plate tracking program, run by the Drug Enforcement Administration, is to seize cars, cash and other assets to combat drug trafficking, according to one government document. But the database’s use has expanded to hunt for vehicles associated with numerous other potential crimes, from kidnappings to killings to rape suspects. Officials have publicly said that they track vehicles near the border with Mexico to help fight drug cartels. What hasn’t been previously disclosed is that the DEA has spent years working to expand the database “throughout the United States,’’ according to one email reviewed by The Wall Street Journal. Many state and local law-enforcement agencies are accessing the database for a variety of investigations ... putting a wealth of information in the hands of local officials who can track vehicles in real time on major roadways. The database raises new questions about privacy and the scope of government surveillance. The existence of the program and its expansion were described in interviews with current and former government officials, and in documents obtained by the American Civil Liberties Union through a Freedom of Information Act request. It is unclear if any court oversees or approves the intelligence-gathering.
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy from reliable major media sources.
Did you know that when you buy an airline ticket and make other travel reservations, the federal government keeps a record of the details in a file called Passenger Name Record or PNR? If airlines dont comply, they cant fly in the U.S., explains Ed Hasbrouck, a privacy expert with the Identity Project who has studied the records for years and is considered the nations top expert. Before each trip, the system creates a travel score for you, generated by your PNR. Before an airline can issue you a boarding pass, the system must approve your passage, Hasbrouck explains. Thats one way people on the No Fly List are targeted. The idea behind extensive use of PNRs, he says, is not necessarily to watch known suspects but to find new ones. Want to appeal the process? Its a secret administrative process based on the score you dont know, based on files you havent seen, Hasbrouck says. The program collects seemingly trivial details. If you have an argument with an airline gate agent and that agent enters a notation ... that record stays in your PNR. The U.S. government is getting the data and sharing it in ways we dont fully know about with other governments, Hasbrouck says. The information collected by the airlines is shared with third-party data companies who store it. Where? In the cloud. Make you feel safer? In Canada and the European Union, the collection of this information spurred public debate. But not here.
Note: Read this excellent article for lots more details on how the government spies on your travels. For more along these lines, see concise summaries of deeply revealing civil liberties news articles from reliable sources.
TERRY GROSS: James Risen [is] an investigative reporter for The New York Times. He, along with Eric Lichtbau, broke the story about warrantless wiretapping. Now Risen is facing a prison sentence for refusing to reveal his source or sources for that story. [Risen] has a new book called "Pay Any Price: Greed, Power And Endless War," which is a series of investigations into who's making money on the War on Terror and what are some of the secret operations within it. You recently wrote an article in The New York Times with Laura Poitras who broke the Edward Snowden story along with Glenn Greenwald. And you reported on how American intelligence is trying to harvest facial imagery with the intention of - what's it for? RISEN: Facial recognition ... in a way that no [one] really understood before has become a central focus of the NSA today. They can link that up with a signals intelligence, which is the communications that they intercept [and] basically find where you are, what you're doing, who you're seeing and virtually anything about you in real time. GROSS: So ... your big story turned out kind of differently than the celebrations facing Woodward and Bernstein. RISEN: I think the times have changed. We had this period in journalism for about 30 years where there was the government and the press. The government ... wouldn't go after whistleblowers or reporters very aggressively. It's only after the - after 9/11 and after the plane case, which you may remember where Judy Miller was sent to jail. I think the post-9/11 age, the government has decided to become much more aggressive against reporters and whistleblowers.
Note: The above quotes are from the transcript of a radio interview that you can listen to by clicking on the news story link provided. For more along these lines, see concise summaries of deeply revealing stories about high level manipulation of mass media from reliable sources.
[Google engineers] are making it far more difficult and far more expensive for the National Security Agency and the intelligence arms of other governments around the world to pierce their systems. As fast as it can, Google is sealing up cracks in its systems that Edward J. Snowden revealed the N.S.A. had brilliantly exploited. It is encrypting more data as it moves among its servers and helping customers encode their own emails. Facebook, Microsoft and Yahoo are taking similar steps. After years of cooperating with the government, the immediate goal now is to thwart Washington as well as Beijing and Moscow. The strategy is also intended to preserve business overseas in places like Brazil and Germany that have threatened to entrust data only to local providers. A year after Mr. Snowdens revelations, the era of quiet cooperation is over. Telecommunications companies say they are denying requests to volunteer data not covered by existing law. A.T.&T., Verizon and others say that compared with a year ago, they are far more reluctant to cooperate with the United States government in gray areas where there is no explicit requirement for a legal warrant. But governments are fighting back, harder than ever. The cellphone giant Vodafone reported ... that a small number of governments around the world have demanded the ability to tap directly into its communication networks [and] noted that some countries did not issue warrants to obtain phone, email or web-searching traffic, because the relevant agencies and authorities already have permanent access to customer communications via their own direct link.
Note: For more on this, see concise summaries of deeply revealing government surveillance news articles from reliable major media sources.
Just before Edward Snowden became a household name, the ACLU argued before the supreme court that the FISA Amendments Act one of the two main laws used by the NSA to conduct mass surveillance was unconstitutional. In a sharply divided opinion, the Supreme Court ruled, 5-4, that the case should be dismissed because the plaintiffs didn't have "standing". The court relied on two claims by the Justice Department to support their ruling: 1) that the NSA would only get the content of Americans' communications without a warrant when they are targeting a foreigner abroad for surveillance, and 2) that the Justice Department would notify criminal defendants who have been spied on under the Fisa Amendments Act, so there exists some way to challenge the law in court. It turns out that neither of those statements were true. One of the most explosive Snowden revelations exposed a then-secret technique known as "about" surveillance. As the New York Times first reported, the NSA "is searching the contents of vast amounts of Americans' e-mail and text communications into and out of the country, hunting for people who mention information about foreigners under surveillance." In other words, the NSA doesn't just target a contact overseas it sweeps up everyone's international communications into a dragnet and searches them for keywords. The Snowden leaks also pushed the Justice Department to admit ... that the government hadn't been notifying any defendants they were being charged based on NSA surveillance.
Note: For more on the realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
From 10,000 feet up, tracking an entire city at one glance: Ohio-based Persistent Surveillance Systems is trying to convince cities across the country that its surveillance technology can help reduce crime. Its new generation of camera technology is far more powerful than the police cameras to which America has grown accustomed. But these newer cameras have sparked some privacy concerns. A new, far more powerful generation is being quietly deployed [from small aircraft] that can track every vehicle and person across an area the size of a small city, for several hours at a time. Although these cameras cant read license plates or see faces, they provide such a wealth of data that police, businesses and even private individuals can use them to help identify people and track their movements. Already, the cameras have been flown above major public events such as the Ohio political rally where Sen. John McCain named Sarah Palin as his running mate in 2008. Theyve been flown above Baltimore; Philadelphia; Compton, Calif.; and Dayton [OH] in demonstrations for police. Theyve also been used for traffic impact studies, [and] for security at NASCAR races. Defense contractors are developing similar technology for the military, but its potential for civilian use is raising novel civil liberties concerns. In Dayton, where Persistent Surveillance Systems is based, city officials balked last year when police considered paying for 200 hours of flights, in part because of privacy complaints. The Supreme Court generally has given wide latitude to police using aerial surveillance as long as the photography captures images visible to the naked eye.
Note: For more on surveillance by government agencies and corporations, see the deeply revealing reports from reliable major media sources available here.
Taken together, the [Edward Snowden] revelations have brought to light a global surveillance system that cast off many of its historical restraints after the attacks of Sept. 11, 2001. Secret legal authorities empowered the NSA to sweep in the telephone, Internet and location records of whole populations. Six months after the first revelations ... Snowden agreed to reflect at length on the roots and repercussions of his choice. He was relaxed and animated over two days of nearly unbroken conversation. Snowden offered vignettes from his intelligence career and from his recent life as an indoor cat in Russia. But he consistently steered the conversation back to surveillance, democracy and the meaning of the documents he exposed. For me, in terms of personal satisfaction, the missions already accomplished, he said. I already won. As soon as the journalists were able to work, everything that I had been trying to do was validated. Because, remember, I didnt want to change society. I wanted to give society a chance to determine if it should change itself. All I wanted was for the public to be able to have a say in how they are governed, he said. Snowden ... had come to believe that a dangerous machine of mass surveillance was growing unchecked. Closed-door oversight by Congress and the Foreign Intelligence Surveillance Court was a graveyard of judgment, he said, manipulated by the agency it was supposed to keep in check. The NSAs business is information dominance, the use of other peoples secrets to shape events. At 29, Snowden upended the agency on its own turf.
Note: For more on the realities of intelligence agency activities, see the deeply revealing reports from reliable major media sources available here.
The Transportation Security Administration is expanding its screening of passengers before they arrive at the airport by searching a wide array of government and private databases that can include records like car registrations and employment information. It is unclear precisely what information the agency is relying upon to make these risk assessments, given the extensive range of records it can access, including tax identification number, past travel itineraries, property records, physical characteristics, and law enforcement or intelligence information. The measures go beyond the background check the government has conducted for years, called Secure Flight, in which a passengers name, gender and date of birth are compared with terrorist watch lists. Now, the search includes using a travelers passport number, which is already used to screen people at the border, and other identifiers to access a system of databases maintained by the Department of Homeland Security. I think the best way to look at it is as a pre-crime assessment every time you fly, said Edward Hasbrouck, a consultant to the Identity Project, one of the groups that oppose the prescreening initiatives. The default will be the highest, most intrusive level of search, and anything less will be conditioned on providing some additional information in some fashion. Critics argue that the problem with what the agency calls an intelligence-driven, risk-based analysis of passenger data is that secret computer rules, not humans, make these determinations. Civil liberties groups have questioned whether the agency has the legal authority to make these assessments.
Note: For more on the realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
When it comes to foreign policy, war, assassinations, drones, surveillance, secrecy, and civil liberties, President Obama's most stalwart, enthusiastic defenders are often found among the most radical precincts of the Republican Party. The extraordinary events that took place in the House of Representatives [on July 24] are perhaps the most vivid illustration yet of this dynamic. The House voted on an amendment sponsored by Justin Amash, the young Michigan lawyer elected in 2010 as a Tea Party candidate, and co-sponsored by John Conyers, the 24-term senior Democrat on the House Judiciary Committee. The amendment was simple. It would de-fund one single NSA program: the agency's bulk collection of the telephone records of all Americans. The amendment yesterday was defeated. A majority of House Democrats supported the Amash/Conyers amendment, while a majority of Republicans voted against it. As the New York Times put it in its account of yesterday's vote: "Conservative Republicans leery of what they see as Obama administration abuses of power teamed up with liberal Democrats long opposed to intrusive intelligence programs. The Obama administration made common cause with the House Republican leadership to try to block it." The fate of the amendment was sealed when the Obama White House ... announced its vehement opposition to it, and then sent NSA officials to the House to scare members that barring the NSA from collecting all phone records of all Americans would "Help The Terrorists."
Note: For more on government privacy invasions, see the deeply revealing reports from reliable major media sources available here.
Long before Edward Snowden walked out of the NSA with his trove of documents, whistleblowers there had been trying for years to bring attention to the massive turn toward domestic spying that the agency was making. Last year in my Wired cover story on the enormous new NSA data center in Utah, Bill Binney, the man who largely designed the agencys worldwide eavesdropping system, warned of the secret, nationwide surveillance. He told how the NSA had gained access to billions of billing records not only from AT&T but also from Verizon. I also wrote about Adrienne J. Kinne, an NSA intercept operator who attempted to blow the whistle on the NSAs illegal eavesdropping on Americans following the 9/11 attacks. She [attempted and failed] to end the illegal activity with appeals all the way up the chain of command to Major General Keith Alexander. The deception by General Alexander is especially troubling. In my new cover story for Wireds July issue ...I show how he has become the most powerful intelligence chief in the nations history. Never before has anyone in Americas intelligence sphere come close to his degree of power, the number of people under his command, the expanse of his rule, the length of his reign, or the depth of his secrecy. A four-star Army general, his authority extends across three domains: He is director of the worlds largest intelligence service, the National Security Agency; chief of the Central Security Service; and commander of the U.S. Cyber Command. As such, he has his own secret military, presiding over the Navys 10th Fleet, the 24th Air Force, and the Second Army.
Note: James Bamford, the author of this article, was the ABC producer responsible for breaking the story on Operation Northwoods, which proved a level of deception almost beyond belief at the very highest levels of the Pentagon. For more on this, click here. For deeply revealing reports from reliable major media sources on the realities of intelligence agency activity, click here.
Your OnStar-equipped car can share an awful lot about your driving habits -- even if you're no longer an OnStar customer. A senator from New York has asked the Federal Trade Commission to open an investigation into vehicle tracking by General Motors' OnStar division. Two other senators issued calls for the company to explain and reconsider its tracking policies. OnStar, which provides a variety of services including vehicle diagnostics, driving directions and automated 911 calls to owners of mostly GM vehicles, recently announced that it reserves the right to track and sell information about vehicles' location and speed even after the driver has stopped subscribing to the service. OnStar, which has around 6 million subscribers, relies on GPS tracking and other systems built into the car. Senator Charles Schumer, a Democrat from New York,... called the tracking "one of the most brazen invasions of privacy in recent memory." Senators Al Franken and Christopher Coons, both Democrats, sent a letter to OnStar last week saying that the company's actions "appear to violate basic principles of privacy and fairness." OnStar reserves the right to sell "anonymized" information collected from vehicles to outside companies. "Anonymized" data is aggregated on cannot be traced back to any individual vehicle or person. But hackers have been able to tease out individual user information from supposedly anonymized data, Schumer noted in his announcement.
Note: For more on corporate and government privacy invasions, see the deeply revealing reports from reliable major media sources available here.
What's good for the police apparently isn't good for the people - or so the law enforcement community would have us believe when it comes to surveillance. That's a concise summary of a new trend noted by National Public Radio last week - the trend whereby law enforcement officials have been trying to prevent civilians from using cell phone cameras in public places as a means of deterring police brutality. Oddly, the effort - which employs both forcible arrests of videographers and legal proceedings against them - comes at a time when the American Civil Liberties Union reports that "an increasing number of American cities and towns are investing millions of taxpayer dollars in surveillance camera systems." The assault on civil liberties in America is a very real problem. As USA Today reported under the headline "Police brutality cases on rise since 9/11," situations "in which police, prison guards and other law enforcement authorities have used excessive force or other tactics to violate victims' civil rights increased 25 percent" between 2001 and 2007. Last year alone, more than 1,500 officers were involved in excessive force complaints, according to the National Police Misconduct Statistics and Reporting Project.
Note: For lots more from major media sources on government and police threats to civil liberties and privacy, click here and here.
Giving Transportation Security Administration agents a peek under your clothes may soon be a practice that goes well beyond airport checkpoints. Newly uncovered documents show that as early as 2006, the Department of Homeland Security has been planning pilot programs to deploy mobile scanning units that can be set up at public events and in train stations, along with mobile x-ray vans capable of scanning pedestrians on city streets. The non-profit Electronic Privacy Information Center (EPIC) [has] published documents it obtained from the Department of Homeland Security showing that from 2006 to 2008 the agency planned a study of of new anti-terrorism technologies. The projects range from what the DHS describes as a walk through x-ray screening system that could be deployed at entrances to special events ... to covert inspection of moving subjects employing the same backscatter imaging technology currently used in American airports. The 173-page collection of contracts and reports, acquired through a Freedom of Information Act request, includes contracts with Siemens Corporations, Northeastern University, and Rapiscan Systems. One project allocated to Northeastern University and Siemens would mount backscatter x-ray scanners and video cameras on roving vans, along with other cameras on buildings and utility poles, to monitor groups of pedestrians, assess what they carried, and even track their eye movements. Its not clear to what degree the technologies outlined in the DHS documents have been implemented.
Note: When WantToKnow.info manager Fred Burks worked as a language interpreter with the US State Department, he accompanied foreign dignitaries on ride-alongs with police where they were already using equipment like this over 10 years ago in clear violation of privacy laws. For other major media articles revealing clear violations of civil liberties, click here.
The suspect's house, just west of this city, sat on a hilltop at the end of a steep, exposed driveway. Agents with the Texas Department of Public Safety believed the man inside had a large stash of drugs and a cache of weapons. The Texas agents did what no state or local law enforcement agency had done before in a high-risk operation: They launched a drone. A bird-size device called a Wasp floated hundreds of feet into the sky and instantly beamed live video to agents on the ground. The SWAT team stormed the house and arrested the suspect. "The nice thing is it's covert," said Bill C. Nabors Jr., chief pilot with the Texas DPS, "You don't hear it, and unless you know what you're looking for, you can't see it." The drone technology that has revolutionized warfare in Iraq, Afghanistan and Pakistan is entering the national airspace. The operation outside Austin presaged what could prove to be one of the most far-reaching and potentially controversial uses of drones: as a new and relatively cheap surveillance tool in domestic law enforcement. By 2013, the FAA expects to have formulated new rules that would allow police across the country to routinely fly lightweight, unarmed drones up to 400 feet above the ground - high enough for them to be largely invisible eyes in the sky. Such technology could allow police to record the activities of the public below with high-resolution, infrared and thermal-imaging cameras.
Note: For lots more from reliable sources on government and corporate threats to privacy, click here.
A business privacy case that comes before the U.S. Supreme Court today may rekindle a debate among the justices over whether corporations are like people, even to the point of suffering embarrassment. The case ... pits the Obama administration against AT&T Inc. over the release of documents stemming from a government investigation of the company. The question is whether corporations can invoke a Freedom of Information Act provision that protects against invasions of personal privacy. In siding with AT&T, a lower court said companies can be embarrassed and stigmatized just like human beings -- a contention the Obama administration scoffed at. The courts divisions were on display when it considered whether to overturn decades-old restrictions on corporate campaign spending. During arguments in 2009, Justice Sonia Sotomayor said that judges created corporations as persons and that they might have been wrong to have imbued a creature of state law with human characteristics. Justice Ruth Bader Ginsburg said that a corporation, after all, is not endowed by its creator with inalienable rights. The court majority disagreed, ruling in a 5-4 decision that corporations have the same constitutional right to spend money on campaign ads as individuals do.
Note: For lots more on government and corporate corruption, click here and here.
Federal law enforcement and national security officials are preparing to seek sweeping new regulations for the Internet, arguing that their ability to wiretap criminal and terrorism suspects is going dark as people increasingly communicate online instead of by telephone. Essentially, officials want Congress to require all services that enable communications including encrypted e-mail transmitters like BlackBerry, social networking Web sites like Facebook and software that allows direct peer to peer messaging like Skype to be technically capable of complying if served with a wiretap order. The mandate would include being able to intercept and unscramble encrypted messages. James X. Dempsey, vice president of the Center for Democracy and Technology, an Internet policy group, said the proposal had huge implications and challenged fundamental elements of the Internet revolution including its decentralized design. They are really asking for the authority to redesign services that take advantage of the unique, and now pervasive, architecture of the Internet, he said. They basically want to turn back the clock and make Internet services function the way that the telephone system used to function.
Note: For an analysis of this new government move to spy on US citizens, click here. For lots more from reliable sources on disturbing government threats to privacy and civil liberties, click here and here.
The federal government is launching an expansive program dubbed "Perfect Citizen" to detect cyber assaults on private companies and government agencies running such critical infrastructure as the electricity grid and nuclear-power plants. The surveillance by the National Security Agency, the government's chief eavesdropping agency, would rely on a set of sensors deployed in computer networks for critical infrastructure that would be triggered by unusual activity suggesting an impending cyber attack. Defense contractor Raytheon Corp. recently won a classified contract for the initial phase of the surveillance effort valued at up to $100 million. Some industry and government officials familiar with the program see Perfect Citizen as an intrusion by the NSA into domestic affairs. One internal Raytheon email, the text of which was seen by The Wall Street Journal [said,] "Perfect Citizen is Big Brother." Raytheon declined to comment on this email. The information gathered by Perfect Citizen could also have applications beyond the critical infrastructure sector, officials said, serving as a data bank that would also help companies and agencies who call upon NSA for help with investigations of cyber attacks, as Google did when it sustained a major attack late last year.
Note: For key reports of government and corporate surveillance from reliable sources, click here.
From 2004 through 2009, in a policy that has gotten completely out of control, New York City police officers stopped people on the street and checked them out nearly three million times, frisking and otherwise humiliating many of them. Upward of 90 percent of the people stopped are completely innocent of any wrongdoing. And yet the New York Police Department is compounding this intolerable indignity by compiling an enormous and permanent computerized database of these encounters between innocent New Yorkers and the police. They have been collecting the names and all sorts of other information about everybody who is stopped and frisked on the streets, said Donna Lieberman, the executive director of the New York Civil Liberties Union, which is fighting the departments stop-and-frisk policy and its compiling of data on people who are innocent. This is a massive database of innocent, overwhelmingly black and Latino people, she said. Police Commissioner Kelly has made it clear that this monstrous database, growing by a half-million or so stops each year, is to be a permanent feature of the departments operations.
Note: For lots more from major media sources on serious threats to civil liberties, click here.
In spring 2007, as one of many American air travelers who were inconvenienced when our names popped up on a federal "watch list," I never could get straight answers from my government. Was this a mistake, or was I being flagged for some reason? How many Americans were on that watch list? What were the criteria for getting on it? I filed my appeal with the Department of Homeland Security's Travel Redress Inquiry Program (TRIP). The Department of Homeland Security received 75,315 requests for redress under the TRIP program as of Oct. 31. Of those requests, 49,826 have been adjudicated, 7,217 are under review, and 18,272 are awaiting supporting documentation, according to the DHS. "Absolutely, the system didn't work as well as it should have," said Suzanne Trevino, a spokeswoman for the Transportation Security Administration. Once an airline receives a passenger's control number, along with full name, date of birth and gender, that information is transmitted to the government for clearance. Fewer than 2,500 known and suspected terrorists are actually on the "no fly" list, according to Trevino. And less than 10 percent of them are Americans. [Yet] the FBI's Terrorist Screening Center has acknowledged that its watch list has more than 1 million entries of names and aliases representing about 400,000 people [with] with an average of 1,600 people who presented a "reasonable suspicion" being added every day.
Note: For many revealing reports from major media sources on the worsening threats to civil liberties, click here.
President Obama's effort to revive the American car industry with a "cash-for-clunkers" scheme has become embroiled in a row over government snooping. The problems arose after the Department of Transportation claimed that when dealers logged on to the clunkers website their computers — and everything on them — become the property of the US Government. “This application provides access to the Department of Transportation (DoT) CARS system,” the warning message read. “When logged on to the CARS system, your computer is considered a Federal computer system and is the property of the United States Government. Any or all uses of this system and all files on this system may be intercepted, monitored, recorded, copied, audited, inspected, and disclosed to authorised CARS, DoT, and law enforcement personnel, as well as authorised officials of other agencies, both domestic and foreign." By the time the disclaimer had been circulated widely on blogs, posted on YouTube and become the subject of a ferocious on-air editorial by the conservative Fox News host Glenn Beck, the Department of Transportation had issued a statement saying that “we are working to revise the language”. No explanation was given as to why the original disclaimer was worded so aggressively. Members of the general public do not need to log on to the website so were not asked to agree to the same conditions as dealers. Mr Obama’s ... critics argue that the controversy is another example of the intrusiveness that will accompany the President’s plans to expand the role of government in the lives of Americans.
Note: Watch a revealing Fox news video report of this unbelievable development at this link. Big Brother at work.
The Obama administration will proceed with a Bush-era plan to use National Security Agency assistance in screening government computer traffic on private-sector networks, with AT&T as the likely test site, according to three current and former government officials. President Obama said in May that government efforts to protect computer systems from attack would not involve "monitoring private-sector networks or Internet traffic," and Department of Homeland Security officials say the new program will scrutinize only data going to or from government systems. But the program has provoked debate within DHS, the officials said, because of uncertainty about whether private data can be shielded from unauthorized scrutiny, how much of a role NSA should play and whether the agency's involvement in warrantless wiretapping during George W. Bush's presidency would draw controversy. Each time a private citizen visited a "dot-gov" Web site or sent an e-mail to a civilian government employee, that action would be screened for potential harm to the network. Under a classified pilot program approved during the Bush administration, NSA data and hardware would be used to protect the networks of some civilian government agencies. Part of an initiative known as Einstein 3, the plan called for telecommunications companies to route the Internet traffic of civilian agencies through a monitoring box that would search for and block computer codes designed to penetrate or otherwise compromise networks. AT&T, the world's largest telecommunications firm, was the Bush administration's choice to participate in the test. AT&T officials declined to comment. The prospect of NSA involvement in cybersecurity ... fuels concerns about unwarranted government snooping into private communication."
Note: For lots more on government and corporate threats to privacy, click here and here.
The Foreign Intelligence Surveillance Court, the special court that reviews government requests for warrants to spy on suspected foreign agents in the United States, seems to have forgotten that its job is to ensure that the government is accountable for following the law not to help the Bush administration keep its secrets. Last week, the court denied a request by the American Civil Liberties Union to release portions of past rulings that would explain how it has interpreted the Foreign Intelligence Surveillance Act, or FISA. The court should share its legal reasoning with the public. After the 9/11 attacks, the National Security Agency for years engaged in domestic spying that violated both FISA and the Constitution. Earlier this year, after a court ruled that the program was illegal, the Bush administration said that in the future it would conduct surveillance with the approval of the intelligence court. At the same time, it announced that a judge of the court had issued orders setting out how the program could proceed. The administration has repeatedly referred to these orders, but has refused to make them public. As a result, it is impossible for the American people and even some members of Congress to know how the court reached its conclusions, or the state of the law with respect to domestic surveillance. The idea of courts developing law in secret and handing down legal principles that the public cannot know about should not be part of the American legal system. That is especially true when the subject matter is as important as the government spying on its citizens, an issue the founders who drafted the Fourth Amendment cared about deeply. The people have a right to know how the act, which is in the process of being revised, is being interpreted so they can tell their elected representatives what they think the law should be.
The Constitution protects individuals against unreasonable searches, but for this protection to have practical meaning, the courts must enforce it. This week, the Supreme Court let stand a disturbing ruling out of California that allows law enforcement to barge into peoples homes without a warrant. The case has not prompted much outrage, perhaps because the people whose privacy is being invaded are welfare recipients, but it is a serious setback for the privacy rights of all Americans. San Diego Countys district attorney has a program called Project 100% that is intended to reduce welfare fraud. Applicants for welfare benefits are visited by law enforcement agents, who show up unannounced and examine the familys home, including the insides of cabinets and closets. The program does not meet the standards set out by the Fourth Amendment. For a search to be reasonable, there generally must be some kind of individualized suspicion of wrongdoing. These searches are done in the homes of people who have merely applied for welfare and have done nothing to arouse suspicion. The United States Court of Appeals for the Ninth Circuit, based in San Francisco, rejected a challenge brought by welfare recipients. In ruling that the program does not violate the Constitution, the majority made the bizarre assertion that the home visits are not searches. It is a fun-house mirrors version of constitutional analysis for a court to say that government agents are not conducting a search when they show up unannounced in a persons home and rifle through her bedroom dresser. Judge Harry Pregerson, writing for himself and six other Ninth Circuit judges who voted to reconsider the case, got it right. The majority decision upholding Project 100%, Judge Pregerson wrote, strikes an unprecedented blow at the core of Fourth Amendment protections. When the government is allowed to show up unannounced without a warrant and search peoples homes, it is bad news for all of us.
The Bush administration acknowledged for the first time that telecommunications companies assisted the government's warrantless surveillance program and were being sued as a result, an admission some legal experts say could complicate the government's bid to halt numerous lawsuits challenging the program's legality. "[U]nder the president's program, the terrorist surveillance program, the private sector had assisted us," Director of National Intelligence Mike McConnell said in an interview with the El Paso Times. His statement could help plaintiffs in dozens of lawsuits against the telecom companies, which allege that the companies participated in a wiretapping program that violated Americans' privacy rights. David Kris, a former Justice Department official, ... said McConnell's admission makes it difficult to argue that the phone companies' cooperation with the government is a state secret. "It's going to be tough to continue to call it 'alleged' when he's just admitted it," Kris said. McConnell has just added to "the list of publicly available facts that are no longer state secrets," increasing the plaintiffs' chances that their cases can proceed, Kris said. McConnell's statement "does serious damage to the government's state secrets claims that are at the heart of its defenses," said Greg Nojeim, senior counsel at the Center for Democracy and Technology. Bruce Fein, an associate deputy attorney general in the Reagan administration, said that McConnell's disclosure shows that "an important element of a program can be discussed publicly and openly without endangering the nation. These Cassandran cries that the earth is going to fall every time you have a discussion simply are not borne out by the facts," he said.
President Bush signed into law ... legislation that broadly [expands] the governments authority to eavesdrop on the international telephone calls and e-mail messages of American citizens without warrants. The law [goes] far beyond the small fixes that administration officials had said were needed to gather information about foreign terrorists [and will] sharply alter the legal limits on the governments ability to monitor millions of phone calls and e-mail messages going in and out of the United States. The new law for the first time [provides] a legal framework for much of the surveillance without warrants that was being conducted in secret by the National Security Agency and outside the Foreign Intelligence Surveillance Act, the 1978 law that is supposed to regulate the way the government can listen to the private communications of American citizens. This more or less legalizes the N.S.A. program, said Kate Martin, director of the Center for National Security Studies in Washington. Previously, the government needed search warrants approved by a special intelligence court to eavesdrop on ... electronic communications between individuals inside the United States and people overseas. The new law gives the attorney general and the director of national intelligence the power to approve the international surveillance, rather than the special intelligence court. The law also gave the administration greater power to force telecommunications companies to cooperate with such spying operations. The companies can now be compelled to cooperate by orders from the attorney general and the director of national intelligence.
An independent oversight board created to identify intelligence abuses after the CIA scandals of the 1970s did not send any reports to the attorney general of legal violations during the first 5 1/2 years of the Bush administration's counterterrorism effort, the Justice Department has told Congress. The President's Intelligence Oversight Board -- the principal civilian watchdog of the intelligence community -- is obligated under a 26-year-old executive order to tell the attorney general and the president about any intelligence activities it believes "may be unlawful." The board was vacant for the first two years of the Bush administration. The board's mandate is to provide independent oversight, so the absence of such communications has prompted critics to question whether the board was doing its job. "It's now apparent that the IOB was not actively employed in the early part of the administration. And it was a crucial period when its counsel would seem to have been needed the most," said Anthony Harrington, who served as the board's chairman for most of the Clinton administration. Senate Judiciary Committee chairman Patrick J. Leahy (D-Vt.) added: "It is deeply disturbing that this administration seems to spend so much of its energy and resources trying to find ways to ignore any check and balance on its authority and avoid accountability to Congress and the American public."
A secret FBI intelligence unit helped detain a group of war protesters in a downtown Washington parking garage in April 2002 and interrogated some of them on videotape about their political and religious beliefs. [Washington] D.C. police said authorities only recently found the logs of police responses to that day's events. That discovery came after three years of police assurances in federal court that no such records or logs existed showing the FBI's role. The FBI and D.C. police said they had no records of such an incident. And police told a federal court that no FBI agents were present when officers arrested more than 20 protesters that afternoon for trespassing; police viewed them as suspicious for milling around the parking garage entrance. Similar intelligence-gathering operations have been reported in New York, where a local police intelligence unit tried to infiltrate groups planning to protest at the Republican National Convention in 2004, and in Colorado, where records surfaced showing that the FBI collected names and license plates of people protesting timber industry practices at a 2002 industry convention.
One of the Bush administration's most far-reaching assertions of government power was revealed quietly last week when Attorney General Alberto Gonzales testified that habeas corpus -- the right to go to federal court and challenge one's imprisonment -- is not protected by the Constitution. "The Constitution doesn't say every individual in the United States or every citizen is hereby granted or assured the right of habeas," Gonzales told Sen. Arlen Specter, R-Pa., during a Senate Judiciary Committee hearing Jan. 17. Gonzales acknowledged that the Constitution declares "habeas corpus shall not be suspended unless ... in cases of rebellion or invasion the public safety may require it." But he insisted that "there is no express grant of habeas in the Constitution." Specter was incredulous, asking how the Constitution could bar the suspension of a right that didn't exist -- a right, he noted, that was first recognized in medieval England as a shield against the king's power to dispatch troublesome subjects to royal dungeons. Later in the hearing, Gonzales described habeas corpus as "one of our most cherished rights'' and noted that Congress had protected that right in the 1789 law that established the federal court system. But he never budged from his position on the absence of constitutional protection -- a position that seemingly would leave Congress free to reduce habeas corpus rights or repeal them altogether.
The New York Daily News today reports on a signing statement President Bush quietly issued two weeks ago, in which he asserts his right to open mail without a warrant. Signing statements have historically been used by presidents mostly to explain how they intend to enforce the laws passed by Congress; Bush has used them to quietly assert his right to ignore those laws. The President asserted his new authority when he signed a postal reform bill into law on Dec. 20. Bush then issued a 'signing statement' that declared his right to open people's mail under emergency conditions. That claim is contrary to existing law and contradicted the bill he had just signed, say experts who have reviewed it. The Postal Accountability and Enhancement Act ... explicitly reinforced protections of first-class mail from searches without a court's approval. Here is the signing statement in question. Here is information on the bill in question. Are these signing statements just a bunch of ideological bluster from overenthusiastic White House lawyers -- or are they actually emboldening administration officials to flout the laws passed by Congress? If the latter, Bush's unprecedented use of these statements constitutes a genuine Constitutional crisis.
An Ohio company has embedded silicon chips in two of its employees - the first known case in which US workers have been "tagged" electronically as a way of identifying them. A private video surveillance company said it was testing the technology as a way of controlling access to a room where it holds security video footage for government agencies and the police. Embedding slivers of silicon in workers is likely to add to the controversy over RFID technology, widely seen as one of the next big growth industries. RFID chips inexpensive radio transmitters that give off a unique identifying signal have been implanted in pets or attached to goods so they can be tracked in transit. "There are very serious privacy and civil liberty issues of having people permanently numbered," said Liz McIntyre, who campaigns against the use of identification technology. "There's nothing pulsing or sending out a signal," said Mr Darks, who has had a chip in his own arm. "It's not a GPS chip. My wife can't tell where I am." The technology's defenders say it is acceptable as long as it is not compulsory. But critics say any implanted device could be used to track the "wearer" without their knowledge.
Russell Tice, a longtime insider at the National Security Agency, is now a whistleblower the agency would like to keep quiet. For 20 years, Tice worked in the shadows. "I specialized in what's called special access programs," Tice said of his job. "We called them 'black world' programs and operations." Some of those secret "black world" operations run by the NSA were operated in ways that he believes violated the law. He is prepared to tell Congress all he knows. Tice says the technology exists to track and sort through every domestic and international phone call...and to search for key words or phrases that a terrorist might use. Tice...says the number of Americans subject to eavesdropping by the NSA could be in the millions if the full range of secret NSA programs is used. "For most Americans [who] placed an overseas communication, more than likely they were sucked into that vacuum." He told ABC News that he was a source for the [New York] Times. But Tice maintains that his conscience is clear. "We need to clean up the intelligence community. We've had abuses, and they need to be addressed." The NSA revoked Tice's security clearance in May of last year based on what it called psychological concerns and later dismissed him. Tice calls that bunk and says that's the way the NSA deals with troublemakers and whistleblowers.
The US passport is about to go electronic, with a tiny microchip embedded in its cover. The chip is the latest outpost in the battle to outwit tamperers. But it's also one that worries privacy advocates. The RFID (radio frequency identification) chip in each passport will contain the same personal data as now appear on the inside pages - name, date of birth, place of birth, issuing office - and a digitized version of the photo. But the 64K chip will be read remotely. And there's the rub. The scenario, privacy advocates say, could be as simple as you standing in line with your passport as someone walks by innocuously carrying a briefcase. Inside that case, a microchip reader could be skimming data from your passport to be used for identity theft. Or maybe authorities or terrorists want to see who's gathered in a crowd and surreptitiously survey your ID and track you. Why not choose a contact chip, where there would be no possibility of skimming, asks Barry Steinhardt, director of the ACLU's Technology and Liberty Project. "There was another way to go, which was to put an electronic strip in the passport that would require contact." The State Department says it's just following international standards set by the International Civil Aviation Organization (ICAO), under the umbrella of the United Nations. The ICAO specified the RFID ... at the behest of the United States. All countries that are part of the US visa-waiver program must use the new passports by Oct. 26, 2005. Mr. Steinhardt ... says the US pushed through the standards against the reservations of the Europeans. "Bush says at the G8 meeting, 'We have to adhere to the global standard,' as though we had nothing to do with it," he says in exasperation.
Note: If the above link fails, click here. For more on the risk of RFID chips, click here.
A U.S. company launched Thursday in Mexico the sale of microchips that can be implanted under a person's skin and used to confirm everything from health history to identity. The microchips ... went on sale last year in the United States. The microchip, the size of a grain of rice, is implanted in the arm or hip and can contain information on everything from a person's blood type to their name. In a two-hour presentation, Palm Beach, Florida-based Applied Digital Solutions Inc. introduced reporters to the VeriChip and used a syringe-like device and local anesthetic to implant a sample in the right arm of employee Carlos Altamirano. It doesn't hurt at all, he said. The whole process is just painless. Antonio Aceves, the director of the Mexican company charged with distributing the chip here, said that in the first year of sales, the company hoped to implant chips in 10,000 people and ensure that at least 70 percent of all hospitals had the technology to read the devices. One chip costs $150 and has a $50 annual fee. Users can update and manage their chips' information by calling a 24-hour customer service line. The VeriChip can track subjects who are within 5 miles, but officials want to develop a new chip that can use satellite technology to track people who are farther away and may have been kidnapped. While the idea of using the chip to track people has raised privacy concerns in the United States, the idea has been popular with Mexicans. The company hopes to have the new anti-kidnapping chip developed by 2003.
Apple has managed to prevent the hottest iPhone hacking company in the world from doing its thing. In March, Atlanta-based Grayshift promised governments its GrayKey tech could crack the passcodes of the latest iOS models, right up to the iPhone X. From then on, Apple continued to invest in security in earnest, continually putting up barriers for Grayshift to jump over. Grayshift continued to grow, however, securing contracts with Immigration and Customs Enforcement, and the Secret Service. Now, though, Apple has put up what may be an insurmountable wall. Multiple sources familiar with the GrayKey tech tell Forbes the device can no longer break the passcodes of any iPhone running iOS 12 or above. On those devices, GrayKey can only do whats called a partial extraction, sources from the forensic community said. That means police using the tool can only draw out unencrypted files and some metadata, such as file sizes and folder structures. Previously, GrayKey used brute forcing techniques to guess passcodes and had found a way to get around Apples protections preventing such repeat guesses. But no more. Though its clear Apple has locked GrayShift out, no one actually knows just how the iPhone maker has done it. Vladimir Katalov, chief of forensic tech provider Elcomsoft, has repeatedly uncovered weaknesses in Apple technology. But he was stumped too.
Note: For more along these lines, see concise summaries of deeply revealing privacy news articles from reliable major media sources.
A major U.S. telecommunications company discovered manipulated hardware from Super Micro Computer Inc. in its network and removed it in August, fresh evidence of tampering in China of critical technology components bound for the U.S., according to a security expert working for the telecom company. The security expert, Yossi Appleboum, provided ... evidence of the discovery following the publication of an investigative report in Bloomberg Businessweek that detailed how Chinas intelligence services had ordered subcontractors to plant malicious chips in Supermicro server motherboards over a two-year period ending in 2015. [Appleboums company] was hired to scan several large data centers belonging to the telecommunications company. Unusual communications from a Supermicro server and a subsequent physical inspection revealed an implant built into the servers Ethernet connector. The executive said he has seen similar manipulations of different vendors' computer hardware made by contractors in China, not just products from Supermicro. Supermicro is a victim - so is everyone else, he said. There are countless points in the supply chain in China where manipulations can be introduced, and deducing them can in many cases be impossible. The manipulation of the Ethernet connector appeared to be similar to a method also used by the U.S. National Security Agency, details of which were leaked in 2013.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
The Supreme Court ruled that police generally need a search warrant to review cell phone records that include data like a user's location, which will impose a higher bar for law enforcement to access data collected on the millions of people who use smartphones on a daily basis. The plaintiff in the case, Timothy Carpenter, was convicted of multiple robbery and gun offenses in 2010 but challenged the conviction saying that officers investigating the case didn't get a warrant for his cell phone records. The government argued that law enforcement doesn't need a warrant to get cell phone records from the service provider since it's a third party. The Court ruled that the government's search, in this case, did not meet the bar for probable cause for a warrant. Chief Justice John Roberts wrote in the majority decision that the government is obligated to get a warrant before compelling a wireless provider to provide cell phone records in an investigation. "We decline to grant the state unrestricted access to a wireless carrier's database of physical location information," Roberts said.
Note: While this ruling limits police powers, the NSA was authorized in 2016 to freely share communications data it collected without warrants on Americans with 16 intelligence and law enforcement agencies. For more along these lines, see concise summaries of deeply revealing news articles on police corruption and the disappearance of privacy.
Trump administration lawyers are demanding the private account information of potentially thousands of Facebook users in three separate search warrants served on the social media giant. The warrants specifically target the accounts of three Facebook users who are described ... as "anti-administration activists who have spoken out at organized events, and who are generally very critical of this administration's policies." One of those users, Emmelia Talarico, operated the disruptj20 page where Inauguration Day protests were organized and discussed; the page was visited by an estimated 6,000 users whose identities the government would have access to if Facebook hands over the information. Talarico says if her account information was given to the government, officials would have access to her "personal passwords, security questions and answers, and credit card information," plus "the private lists of invitees and attendees to multiple political events." The American Civil Liberties Union, representing the three Facebook users, filed a motion to quash the warrants Thursday. "What is particularly chilling about these warrants is that anti-administration political activists are going to [be] scrutinized by the very administration they are protesting," said ACLU attorney Scott Michelman. Facebook was initially served the warrants in February 2017 along with a gag order which barred the social media company from alerting the three users that the government was seeking their private information.
Note: United Nations officials recently said that the US government's treatment of activists was increasingly "incompatible with US obligations under international human rights law". For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy.
They wanted to kill landmark privacy regulations that would soon ban Internet providers, such as Comcast and AT&T, from storing and selling customers browsing histories without their express consent. While the nation was distracted by the Houses pending vote to repeal Obamacare, Senate Republicans would schedule a vote to wipe out the new privacy protections. On March 23, the measure passed on a straight party-line vote, 50 to 48. President Trump signed the bill in early April without ceremony or public comment. While everyone was focused on the latest headline crisis coming out of the White House, Congress was able to roll back privacy, said former Federal Communications Commission chairman Tom Wheeler, who worked for nearly two years to pass the rules. The process to eliminate them took only a matter of weeks. The Internet privacy rules were adopted ... after an intense battle that pitted large Internet service providers, the advertising industry and tech giants against consumer advocates and civil rights groups. The rules required Internet service providers to get explicit consent before they gather their customers data - their browsing histories, the locations of businesses they physically visit and the mobile applications they use - and sell it to third parties. The requirements were modeled after a law passed decades ago by Congress that prohibited telephone companies from collecting customers calling histories and selling the information to third parties.
Note: For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the disappearance of privacy.
A doll called My Friend Cayla listens a little too well, according to German regulators who say the toy is essentially a stealthy espionage device that shares what it hears and is also vulnerable to takeover by third parties. "Cayla ist verboten in Deutschland," says Jochen Homann, the president of Germany's Federal Network Agency (the Bundessnetzagentur), announcing a ban on the doll in Germany on Friday. His agency oversees electronic privacy as part of its telecommunications mandate. Cayla looks like an everyday doll and gives no notice that it collects and transmits everything it hears - in this case, to [Nuance], a voice-recognition company in the U.S. whose other customers include intelligence agencies. The My Friend Cayla doll remains for sale in the U.S., including via Amazon. Much of what the German agency says echoes the concerns of privacy and consumer advocates in the U.S., who filed a complaint against Cayla during the recent Christmas shopping season. They criticized the scope of what the Internet-connected toy captures, as well as the vulnerabilities it poses for users who link the doll with their smartphones. Consumer groups have also criticized the doll for its habit of praising commercial products, in what's often seen as a stealth marketing campaign that targets children. "For example, Cayla will happily talk about how much she loves different Disney movies," Norway's Consumer Council says. "Meanwhile, the app-provider has a commercial relationship with Disney."
Note: The use of artificial intelligence in a new Barbie doll generated controversy in 2015, while a New York Times article from that same year called "smart objects" a "train wreck in privacy and security". For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
When Bill Binney, former NSA analyst and head of the anti-terror ThinThread metadata program sits in front of you and says he is not afraid of the government, you have to admire him. A wheel-chair-bound U.S. serviceman who rose in the ranks of intelligence to work in top-secret NSA programs, Binney created ThinThread prior to September 11, 2001, and says it mathematically broke down all phone communications anywhere in the world without any infringement on Constitutional rights. The program was self-running. More important, it worked. In "A Good American," the new documentary from executive producer Oliver Stone ... audiences are taken on a tense and frightening ride through Binney and his colleagues' experience developing and deploying ThinThread in tests, only to see its funding pulled just weeks before 9/11 in favor of an expensive and ineffective ... program called Trailblazer. Binney contends that ThinThread would have identified the terrorists who planned and executed the 9/11 terror attacks, thereby preventing them from occurring. When ThinThread's plug was pulled, Binney and his team challenged their NSA bosses, and in the process found themselves at odds with the U.S. government and in a complex web of lies and corruption. Thus, when Binney said he remains unafraid of possible repercussions or retaliation tied to the film's thesis, it's not hard to believe. "What else can they do to me?" he asks. "They've already tried everything to stop me."
Note: Watch a free trailer or rent the whole documentary on this webpage. Read a revealing, detailed New York Times article on Oliver Stone and his profound work to expose corruption and manipulation through film. For more along these lines, see concise summaries of deeply revealing intelligence agency corruption news articles from reliable major media sources. Then explore the excellent, reliable resources provided in our 9/11 Information Center.
Between your laptop, smartphone, smart TV, and perhaps a virtual assistant, how many microphones are in your home? The number of households with a hands-free assistant is growing by millions each year, but their convenience may come at a price. With law enforcement already using smart-device collected data as evidence, digital privacy rights are becoming more important. Amazons ... Echo family of devices are all variations on the theme of a smart speaker that can listen to, understand, and respond to voice commands. Like Siris implementation in recent iOS devices ... the device is always listening, so you dont have to put down what youre doing and find your phone to get an answer. But some worry theres a fine line between always listening, and always recording. Are we truly alone when were with our devices? Amazon maintains a database of your conversations with the Echo. Police in Bentonville, Ark. have already submitted a search warrant for audio recordings, transcribed records, and other text records from the Echo of 2015 murder suspect James Andrew Bates. Amazon refused to turn over data from its servers beyond basic account information, [but] this case should be a wake-up call. The Fourth Amendment establishes the sanctity of the home, which prevents law enforcement from an unjustified search of a house. The third-party doctrine, [however] permits police to access information voluntarily shared with a third party such as your bank or phone company, even without a warrant.
Note: For more along these lines, see concise summaries of deeply revealing privacy news articles from reliable major media sources.
Yahoo has been accused of secretly building a customised software programme to search all of its customers incoming emails for specific information provided by US intelligence officials. The company complied with a classified US government directive, scanning hundreds of millions of Yahoo Mail accounts at the behest of the National Security Agency or FBI. Reuters said that a number of surveillance experts said this represented the first case to surface of a US Internet company agreeing to a spy agencys demand by searching all arriving messages, as opposed to examining stored messages or scanning a small number of accounts in real time. The agency also said it was unable to determine what data the company had handed over, and if the intelligence officials had approached other email providers besides Yahoo. US phone and Internet companies are known to have handed over bulk customer data to intelligence agencies. But some former government officials and private surveillance experts said they had not previously seen either such a broad directive for real-time Web collection or one that required the creation of a new computer program. Ive never seen that, a wiretap in real time on a selector, said Albert Gidari, a lawyer who represented phone and Internet companies on surveillance. A selector refers to a type of search term used to zero in on specific information. He added: It would be really difficult for a provider to do that.
Note: For more along these lines, see concise summaries of deeply revealing news articles about corporate corruption and the disappearance of privacy.
Secret FBI rules allow agents to obtain journalists phone records with approval from two internal officials - far less oversight than under normal judicial procedures. The classified rules ... govern the FBIs use of national security letters, which allow the bureau to obtain information about journalists calls without going to a judge or informing the news organization being targeted. Obtaining a journalists records with a national security letter (or NSL) requires the signoff of the FBIs general counsel and the executive assistant director of the bureaus National Security Branch. The Obama administration has come under criticism for bringing a record number of leak prosecutions and aggressively targeting journalists in the process. In 2013, after it came out that the Justice Department had secretly seized records from phone lines at the Associated Press and surveilled ... reporter James Rosen, then-Attorney General Eric Holder tightened the rules. The FBI could not label reporters as co-conspirators in order to try to identify their sources - as had happened with Rosen - and it became more difficult to get journalists phone records without notifying the news organization first. Yet these changes did not apply to NSLs. Those are governed by a separate set of rules. The FBI issues thousands of NSLs each year, including nearly 13,000 in 2015. Over the years, a series of Inspector General reports found significant problems with their use, yet the FBI is currently pushing to expand the types of information it can demand with an NSL.
Note: The aggressive pursuit of leaks and journalists that report them led BBC to recently ask: "Is the US government at war with whistleblowers?" Read more about the FBI's use of secret National Security Letters. For more along these lines, see concise summaries of deeply revealing news articles on media manipulation and the disappearance of privacy.
Hidden microphones that are part of a clandestine government surveillance program that has been operating around the Bay Area has been exposed. Imagine standing at a bus stop, talking to your friend and having your conversation recorded without you knowing. It happens all the time, and the FBI doesnt even need a warrant to do it. Jeff Harp, a ... security analyst and former FBI special agent said, They put microphones under rocks, they put microphones in trees, they plant microphones in equipment. I mean, theres microphones that are planted in places that people dont think about, because thats the intent! FBI agents hid microphones inside light fixtures and at a bus stop outside the Oakland Courthouse without a warrant to record conversations, between March 2010 and January 2011. Federal authorities are trying to prove real estate investors in San Mateo and Alameda counties are guilty of bid rigging and fraud and used these recordings as evidence. The lawyer for one of the accused real estate investors who will ask the judge to throw out the recordings, told KPIX 5 News that, Speaking in a public place does not mean that the individual has no reasonable expectation of privacy private communication in a public place qualifies as a protected oral communication.'
Note: For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the disappearance of privacy.
Microsoft filed a landmark lawsuit against the U.S. Department of Justice on Thursday. The company accuses the federal government of adopting a widespread, unconstitutional policy of looking through Microsoft customers' data - and forcing the company to keep quiet about it. Over the past 18 months, federal judges have approved 2,600 secret searches of Microsoft customers. In two-thirds of those cases, Microsoft can't even notify their customers that they've been searched - ever - because there's no expiration date on these judicial orders. At issue here is the 1986 Electronic Communications Privacy Act, which creates a double standard when it comes to a person's right to know when police are rummaging through their stuff. "People do not give up their rights when they move their private information from physical storage to the cloud," Microsoft says in its lawsuit. "The government, however, has exploited the transition to cloud computing as a means of expanding its power to conduct secret investigations." In its lawsuit, Microsoft claims that federal agents have been violating the company's First Amendment right to speak to its own customers, as well as their customers' Fourth Amendment right to know when they're being searched. This lawsuit also notes the odd, modern distinction that the government makes between searching your computer and searching your information on a company's computer. Law enforcement agents often remain covert when they dig through information stored on company data backup services.
Note: For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the disappearance of privacy.
The Transportation Security Administrations new rules for screening passengers with its controversial full-body scanners - which were quietly changed just before the busy holiday travel season - represent a significant policy reversal that could affect your next flight. Getting checked by the TSAs advanced-imaging technology used to be entirely optional, allowing those who refused a scan to be subjected to a pat-down. In fact, many observers thought the agency installed the 740 body scanners in 160 airports with an understanding that no one would be forced to use them, ever. But on a Friday in late December, the TSA revised its rules, saying an opt out is no longer an option for certain passengers. The TSA is going back on its word, says Fred Cate, a law professor at Indiana University and prominent TSA-watcher. The scanners were sold to Congress and the public on the promise that they were optional, but for at least some people, that is no longer the case. In previous court filings, the agency offered written assurance that the scanners were optional. Based on the agencys statements, a federal appeals court affirmed the legality of using the full-body scanners as long as fliers were given a choice.
Note: Read more on the controversy surrounding TSA's costly but technically questionable scanners. For more along these lines, see concise summaries of deeply revealing government corruption news articles from reliable major media sources.
Local police around the country are increasingly using high-tech mass surveillance gear that can vacuum up private information on entire neighborhoods. Many cops are ... purposefully hiding their spying from courts to avoid any scrutiny from judges. Two important news reports from the last week have shed light on the disturbing practices. The first investigation, done by USA Todays Brad Heath, found: In one case after another ... police in Baltimore and other cities used the phone tracker, commonly known as a stingray, to locate the perpetrators of routine street crimes and frequently concealed that fact from the suspects, their lawyers and even judges. Stingrays are so controversial that some state legislatures have already passed laws restricting their use which is exactly why police want to keep [their use] secret. The Wall Street Journal also reported last week about newer devices costing as little as a few hundred dollars [that] the police supposedly dont think ... require a court order at all to use against potential suspects. These devices are handheld or can be attached to clothing. Not only are these cops violating the constitutional rights of defendants by spying on them without court orders, but, in some cases, theyre also allegedly dismissing felony cases involving potentially dangerous criminals, so they can prevent judges from ruling on whether their surveillance tactics are legal ... all to continue their blanket surveillance practices with minimal scrutiny.
Note: For more along these lines, see concise summaries of deeply revealing news articles about the erosion of privacy rights.
Moxie Marlinspike has ... created an encryption program that scrambles messages until they reach the intended reader. The software is effective enough to alarm governments. British Prime Minister David Cameron called protected-messaging apps a safe space for terrorists. The following week, President Barack Obama called them a problem. In a research paper released Tuesday, 15 prominent technologists cited three programs relying on Mr. Marlinspikes code as options for shielding communications. His encrypted texting and calling app, Signal, has come up in White House meetings. Former National Security Agency contractor Edward Snowden, who leaked troves of U.S. spying secrets, urged listeners to use anything that Mr. Marlinspike releases. That endorsement was a little bit terrifying, Mr. Marlinspike says. But he says he sees an opening, following Mr. Snowdens revelations, to demystify, and simplify, encryption, so more people use it. Consumer encryption tools ... have been around since the early 1990s, but most are so cumbersome that few people use them, [limiting] the use of encryption to a level law enforcement has mostly learned to live with. Adding easy-to-use encryption that companies cant unscramble to products used by millions changes that calculus. Technology companies, once cozy with Washington, sound increasingly like Mr. Marlinspike. Apple, Facebook, Google and others are resisting efforts to give the government access to encrypted communications.
Note: For more along these lines, see concise summaries of deeply revealing news articles about the corrupt intelligence agencies that are attempting to erode privacy rights in the U.S. and elsewhere.
Edward Snowden is in exile in Moscow. He's still hard at work. Whatever he's working on, the former NSA contractor who exposed controversial US surveillance practices, says it's much tougher than his last gig. "The fact is I was getting paid an extraordinary amount of money for very little work with very little in the way of qualifications. That's changed significantly," Snowden said in an event at Stanford University on Friday, via teleconference from Moscow. Last week, a federal appeals court ruled that the NSA's massive collection of Americans' phone records is illegal a victory for Snowden, who revealed the existence of the surveillance program in the documents he leaked to the press. Snowden said in the teleconference that he worked with reporters so that there could be a system of checks and balances, and noted that he did not publish a single document himself. Still, he couldn't leak his secrets anonymously to the reporters because his colleagues' livelihoods would have been at risk as well if the NSA conducted a witch-hunt, Snowden said. "Whistleblowers are elected by circumstance. Nobody self nominates to be a whistleblower because its so painful," Snowden said, [and] emphasized that he doesn't see himself as a hero or a traitor, but he had just reached the tipping point where he needed to do something.
Note: For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the erosion of privacy rights from reliable major media sources.
The NSA whistleblower, Edward Snowden, has urged lawyers, journalists, doctors, accountants, priests and others with a duty to protect confidentiality to upgrade security in the wake of the spy surveillance revelations. Snowden said professionals were failing in their obligations to their clients, sources, patients and parishioners in what he described as a new and challenging world. "What last year's revelations showed us was irrefutable evidence that unencrypted communications on the internet are no longer safe. Any communications should be encrypted by default," he said. Snowden's plea for the professions to tighten security came during an extensive and revealing interview with the Guardian in Moscow. During the seven hours of interview, Snowden: Said if he ended up in US detention in Guantnamo Bay he could live with it. Does not have any regrets. Said that ... he was independently secure, living on savings, and money from awards and speeches he has delivered online round the world. Made a startling claim that a culture exists within the NSA in which, during surveillance, nude photographs picked up of people in "sexually compromising" situations are routinely passed around. He works online late into the night; a solitary, digital existence not that dissimilar to his earlier life. He said he was using part of that time to work on the new focus for his technical skills, designing encryption tools to help professionals such as journalists protect sources and data. He is negotiating foundation funding for the project, a contribution to addressing the problem of professions wanting to protect client or patient data, and in this case journalistic sources.
Note: Read the transcript of the Guardian's new interview of Edward Snowden. For more on this, see concise summaries of deeply revealing government surveillance news articles from reliable major media sources.
Former National Security Agency contractor Edward Snowden, and one of the reporters who first broke the news of Snowden's documents, Laura Poitras, received a Ridenhour Truth-Teller prize [on April 30] to a standing ovation at the National Press Club. Snowden leaked classified documents that exposed the NSA's massive global surveillance programs. Snowden ... compared his actions with that of Director of National Intelligence James R. Clapper, who denied that the NSA was "wittingly" collecting data on millions of Americans in a Senate Intelligence Committee hearing last spring -- a claim at odds with revelations about domestic phone records collection as a result of documents provided by Snowden. "The oath that I remember is James Clapper raising his hand, swearing to tell the truth and then lying to the American public," Snowden said. "I also swore an oath, but that oath was not to secrecy, but to defend the American Constitution." While Clapper has accused Snowden of perpetrating the most "massive and damaging theft of intelligence" in U.S. history, Snowden argues his actions were serving a larger public interest that superseded the national intelligence need for secrecy. Later in the speech, he described Clapper as having "committed a crime by lying under oath to the American people," and questioned why charges were never brought against the director. By contrast, Snowden said, charges were brought against him soon after he revealed himself as the source of the leaks.
Note: For more on the construction of a total surveillance state, see the deeply revealing reports from reliable major media sources available here.
At least since the aftermath of September 2001, western governments and intelligence agencies have been hard at work expanding the scope of their own power, while eroding privacy, civil liberties and public control of policy. What used to be viewed as paranoid, Orwellian, tin-foil hat fantasies [turn] out post-Snowden, to be not even the whole story. We've been warned for years that these things were going on: wholesale surveillance of entire populations, militarization of the internet, the end of privacy. Secret laws, secret interpretations of secret laws by secret courts and no effective parliamentary oversight whatsoever. By and large the media have paid scant attention to this, even as more and more courageous, principled whistleblowers stepped forward. The unprecedented persecution of truth-tellers, initiated by the Bush administration and severely accelerated by the Obama administration, has been mostly ignored, while record numbers of well-meaning people are charged with serious felonies simply for letting their fellow citizens know what's going on. Numerous ex-NSA officials have come forward in the past decade, disclosing massive fraud, vast illegalities and abuse of power in [that] agency, including Thomas Drake, William Binney and Kirk Wiebe. The response was 100% persecution and 0% accountability by both the NSA and the rest of government. Since the summer of 2013, the public has witnessed a shift in debate over these matters. The reason is that one courageous person: Edward Snowden.
Note: For more on government corruption, see the deeply revealing reports from reliable major media sources available here.
There was a time when the U.S. National Security Agency was so secretive that government officials dared not speak its name in public. NSA, the joke went, stood for "No Such Agency." That same agency this month held an on-the-record conference call with reporters, issued a lengthy press release to rebut a newspaper story, and posted documents on a newly launched open website - icontherecord.tumblr.com (which stands for intelligence community on the record). The steps were taken under pressure as President Barack Obama's administration tries to calm a public storm over disclosures by former NSA contractor Edward Snowden. The NSA's moves out of the shadows were meant to show that it operates lawfully..., but not everyone is convinced that it is a fundamental shift toward more openness at the intelligence agencies. Jameel Jaffer, deputy legal director at the American Civil Liberties Union, said the [disclosures] should not be viewed as a huge shift toward transparency by the administration. "In fact, on the same day the president promised more transparency on surveillance issues, the CIA filed a brief in one of our 'targeted killing' cases arguing that it could not release legal memos about the drone program, could not release civilian casualty numbers, and for that matter could not even acknowledge that the agency had played any role in targeted killings," Jaffer said.
Note: For more on the realities of intelligence operations, see the deeply revealing reports from reliable major media sources available here.
The news that the National Security Agency (NSA) is routinely operating outside of the law and overstepping its legal authority by carrying out surveillance on American citizens is not really much of a surprise. This is what happens when you give the government broad powers and allow government agencies to routinely sidestep the Constitution. Consider that the government's Utah Data Center (UDC), the central hub of the NSA's vast spying infrastructure, will be a clearinghouse and a depository for every imaginable kind of information - whether innocent or not, private or public - including communications, transactions and the like. In fact, anything and everything you've ever said or done, from the trivial to the damning - phone calls, Facebook posts, Twitter tweets, Google searches, emails, bookstore and grocery purchases, bank statements, commuter toll records, etc. - will be tracked, collected, cataloged and analyzed by the UDC's supercomputers and teams of government agents. By sifting through the detritus of your once-private life, the government will come to its own conclusions about who you are, where you fit in, and how best to deal with you should the need arise. Surveillance of all citizens ... is not friendly to freedom. Frankly, we are long past the point where we should be merely alarmed. These are no longer experiments on our freedoms. These are acts of aggression.
Note: Former US Senator Frank Church warned of the dangers of creating a surveillance state in 1975. By 2013, it had become evident that the US did not heed his warning. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
The National Security Agency has broken privacy rules or overstepped its legal authority thousands of times each year since Congress granted the agency broad new powers in 2008, according to an internal audit and other top-secret documents. Most of the infractions involve unauthorized surveillance of Americans or foreign intelligence targets in the United States, both of which are restricted by statute and executive order. They range from significant violations of law to typographical errors that resulted in unintended interception of U.S. e-mails and telephone calls. The documents, provided earlier this summer to The Washington Post by former NSA contractor Edward Snowden, include a level of detail and analysis that is not routinely shared with Congress or the special court that oversees surveillance. In one of the documents, agency personnel are instructed to remove details and substitute more generic language in reports to the Justice Department and the Office of the Director of National Intelligence. In one instance, the NSA decided that it need not report the unintended surveillance of Americans. The NSA audit obtained by The Post, dated May 2012, counted 2,776 incidents in the preceding 12 months of unauthorized collection, storage, access to or distribution of legally protected communications. Many involved failures of due diligence or violations of standard operating procedure. The most serious incidents included a violation of a court order and unauthorized use of data about more than 3,000 Americans and green-card holders.
Note: For more on the realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
Edward Snowden, the whistle-blower shining spotlights on federal surveillance practices, made a rhetorical - and volatile - point during an online question-and-answer session Monday. "If Facebook, Google, Microsoft and Apple refused to provide this cooperation with the intelligence community, what do you think the government would do? Shut them down?" he asked. Snowden's point implies that tech companies should push back on all government requests for data on their users. Prosecuting these much-used companies for noncompliance would only shed light on the extent of the programs they aimed to keep secret in the first place. Whether a tech company dares go that far remains to be seen. But in the past week a number of household names in Silicon Valley have at least started demanding more freedom to disclose what the government wants to know about their users. As the tech companies associated with Snowden's leaked materials scramble to comply with government requests, they're also scrambling to save face with customers. It's still not clear what exact technical mechanism the government used to acquire information about users of Facebook, Google, Microsoft, Yahoo and Apple, among others. But it is clear that some Internet users have come to view these tech giants as proxy spies as a result of their assumed compliance. The companies say they would like nothing better than to clear their names, but they simply aren't allowed to release details about government requests.
Note: For deeply revealing reports from reliable major media sources on government assaults on privacy, click here.
[Daniel] Ellsberg is one of the most outspoken critics of the Obama administrations prosecution of leakers. Under President Obamas tenure, the government has prosecuted six individuals for releasing classified information to media organizations. Ellsberg is particularly fierce in his support of Bradley Manning, a young soldier who released a large amount of classified information to WikiLeaks. Manning was arrested in 2010, and his military court-martial began this week. Ellsberg considers Manning a hero, and he argues that there is little difference between what Manning did in 2010 and what Ellsberg did four decades earlier. [Q.}: In a 1973 interview, you said that a secondary objective of releasing the Pentagon Papers was the hope of changing the tolerance of Executive secrecy that had grown up over the last quarter of a century both in Congress and the courts and in the public at large. How has that tolerance of secrecy changed over the last four decades? DE: Theres been very great tolerance that if the magic words national security, or the new words homeland security are invoked, Congress has given the president virtually a free hand in deciding what information they will know as well as the public. I wouldnt count on the current court with its current makeup making the same ruling with the Pentagon Papers as they did 40 years ago. Im sure that President Obama would have sought a life sentence in my case. Various things that were counted as unconstitutional then have been put in the presidents hands now. Hes become an elected monarch. Nixons slogan, when the president does it, its not illegal, is pretty much endorsed now.
Note: To see key quotes showing the amazing courage and dedication of Snowden, click here. For deeply revealing reports from reliable major media sources on the realities of intelligence agency activity, click here.
The case of Stephen Jin-Woo Kim, the government adviser, and James Rosen, the chief Washington correspondent for Fox News, bears striking similarities to a sweeping leaks investigation disclosed last week in which federal investigators obtained records over two months of more than 20 telephone lines assigned to the Associated Press. At a time when President Obamas administration is under renewed scrutiny for an unprecedented number of leak investigations, the Kim case provides a rare glimpse into the inner workings of one such probe. Court documents in the Kim case reveal how deeply investigators explored the private communications of a working journalist - and raise the question of how often journalists have been investigated as closely as Rosen was in 2010. The case also raises new concerns among critics of government secrecy about the possible stifling effect of these investigations on a critical element of press freedom: the exchange of information between reporters and their sources. The latest events show an expansion of this law enforcement technique, said attorney Abbe Lowell, who is defending Kim on federal charges filed in 2010 that he disclosed national defense information. Individual reporters or small time periods have turned into 20 [telephone] lines and months of records with no obvious attempt to be targeted or narrow. The Obama administration has pursued more such cases than all previous administrations combined.
Note: Read more about the Kim case in this article. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and media manipulation.
Raytheon, a Massachusetts defense contractor, has built tracking software that pulls information from social networks, according to a video obtained by the Guardian newspaper in London. "[Raytheon] has acknowledged the technology was shared with U.S. government and industry as part of a joint research and development effort, in 2010, to help build a national security system capable of analyzing 'trillions of entities' from cyberspace." Using public data from Facebook, Twitter, Gowalla and Foursquare, the software - called RIOT, or Rapid Information Overlay Technology - apparently gathers uploaded information and forms a profile of a person's every move that was registered with one of the websites. The video obtained by the newspaper starts with a demonstration by Raytheon's "principal investigator," Brian Urch, showing how easy it is to track an employee named Nick - a real person - based on all the places he has checked in using his smartphone. "When people take pictures and post them on the Internet using their smartphones, the phone will actually embed the latitude and longitude in the header data - so we're going to take advantage of that," Urch says. "So now we know where Nick's gone ... and now we'll predict where he'll be in the future." Urch goes on to analyze - using graphs and calendars - where Nick likes to spend his personal time and make predictions about his behavior. "If you ever wanted to get a hold of his laptop, you might want to visit the gym at 6 a.m. on Monday," Urch says with alarming casualness.
Note: To read the full Guardian article, click here.
The FISA Amendments Act of 2008 did much more than shield lawbreaking telecoms from all forms of legal accountability. It also legalized vast new, sweeping and almost certainly unconstitutional forms of warrantless government eavesdropping. [The] 2008 law gutted the 30-year-old FISA statute that had [barred] the government from eavesdropping on the communications of Americans without first obtaining a warrant from a court. Worst of all, the 2008 law legalized ... the NSA warrantless eavesdropping program secretly implemented by George Bush after the 9/11 attack. The 2008 FISA law provided that it would expire in four years unless renewed. Yesterday, the Senate debated its renewal. Several Senators - Democrats Jeff Merkley and Ron Wyden of Oregon along with Kentucky GOP Senator Rand Paul - each attempted to attach amendments to the law simply to provide some modest amounts of transparency and oversight to ensure that the government's warrantless eavesdropping powers were constrained and checked from abuse. The Democratic Chair of the Senate Intelligence Committee, Dianne Feinstein ... demanded renewal of the FISA law without any reforms. And then predictably, in virtually identical 37-54 votes, Feinstein and her conservative-Democratic comrades joined with virtually the entire GOP caucus ... to reject each one of the proposed amendments and thus give Obama exactly what he demanded: reform-free renewal of the law.
Note: For analysis of this Senate vote, click here. For deeply revealing reports from reliable major media sources on government assaults on privacy, click here.
With little notice and only occasional complaints, the American military and local authorities have been engaged in an ambitious effort to record biometric identifying information on a remarkable number of people in Afghanistan and Iraq, particularly men of fighting age. Information about more than 1.5 million Afghans has been put in databases operated by American, NATO and local forces. In Iraq, an even larger number of people, and a larger percentage of the population, have been registered. Data have been gathered on roughly 2.2 million Iraqis. A citizen in Afghanistan or Iraq would almost have to spend every minute in a home village and never seek government services to avoid ever crossing paths with a biometric system. What is different from traditional fingerprinting is that the government can scan through millions of digital files in a matter of seconds. While the systems are attractive to American law enforcement agencies, there is serious legal and political opposition to imposing routine collection on American citizens. Various federal, state and local law enforcement agencies have discussed biometric scanning, and many have even spent money on hand-held devices. But the proposed uses are much more limited, with questions being raised about constitutional rights of privacy and protection from warrantless searches.
Note: Many new technologies for domestic population control are developed, deployed, and tested by the US military in war theaters abroad, and then shared with police agencies in the US. For many examples see our "Non-lethal" Weapons article archive available here.
A member of parliament in Iceland who is also a former WikiLeaks volunteer says the US justice department has ordered Twitter to hand over her private messages. Birgitta Jonsdottir, an MP for the Movement in Iceland, said last night on Twitter that the "USA government wants to know about all my tweets and more since november 1st 2009. Do they realize I am a member of parliament in Iceland?" She said she was starting a legal fight to stop the US getting hold of her messages, after being told by Twitter that a subpoena had been issued. She added that the US authorities had requested personal information from Twitter as well as her private messages and that she was now assessing her legal position. "It's not just about my information. It's a warning for anyone who had anything to do with WikiLeaks. It is completely unacceptable for the US justice department to flex its muscles like this. I am lucky, I'm a representative in parliament. But what of other people? It's my duty to do whatever I can to stop this abuse."
Note: For a New York Times article with more on this, click here.
The growing use by the police of new technologies that make surveillance far easier and cheaper to conduct is raising difficult questions about the scope of constitutional privacy rights. The issue is whether the Fourth Amendments protection against unreasonable searches covers a device that records a suspects movements for weeks or months without any need for an officer to trail him. The GPS tracking dispute coincides with a burst of other technological tools that expand police monitoring abilities including ... the widely discussed prospect of linking face-recognition computer programs to the proliferating number of surveillance cameras. Some legal scholars ... have called for a fundamental rethinking of how to apply Fourth Amendment privacy rights in the 21st century. Traditionally, courts have held that the Fourth Amendment does not cover the trailing of a suspect because people have no expectation of privacy for actions exposed to public view. On [August 12], five judges on the San Francisco appeals court dissented from a decision not to re-hear a ruling upholding the warrantless use of GPS trackers. Chief Judge Alex Kozinski characterized the tactic as creepy and un-American and contended that its capabilities handed the government the power to track the movements of every one of us, every day of our lives.
Note: For lots more on threats to civil liberties and privacy, click here and here.
It is just a technical matter, the Obama administration says: We just need to make a slight change in a law to make clear that we have the right to see the names of anyones e-mail correspondents and their Web browsing history without the messy complication of asking a judge for permission. It is far more than a technical change. The administrations request, reported [on July 29] in The Washington Post, is an unnecessary and disappointing step backward toward more intrusive surveillance from a president who promised something very different during the 2008 campaign. To get this information, the F.B.I. simply has to ask for it in the form of a national security letter, which is an administrative request that does not require a judges signature. The F.B.I. used these letters hundreds of thousands of times to demand records of phone calls and other communications, and the Pentagon used them to get records from banks and consumer credit agencies. Internal investigations of both agencies found widespread misuse of the power, and little oversight into how it was wielded. President Obama campaigned for office on an explicit promise to rein in these abuses. But instead of implementing reasonable civil liberties protections, like taking requests for e-mail surveillance before a judge, the administration is proposing changes to the law that would allow huge numbers of new electronic communications to be examined with no judicial oversight.
Note: For key reports on the growing government and corporate threats to privacy, click here.
The FBI illegally collected more than 2,000 U.S. telephone call records between 2002 and 2006 by invoking terrorism emergencies that did not exist or simply persuading phone companies to provide records, according to internal bureau memos and interviews. FBI officials issued approvals after the fact to justify their actions. E-mails obtained by The Washington Post detail how counterterrorism officials inside FBI headquarters did not follow their own procedures that were put in place to protect civil liberties. A Justice Department inspector general's report due out this month is expected to conclude that the FBI frequently violated the law with its emergency requests. FBI officials said they thought that nearly all of the requests involved terrorism investigations. FBI general counsel Valerie Caproni said ... that the FBI technically violated the Electronic Communications Privacy Act when agents invoked nonexistent emergencies to collect records.
Note: The FBI, by admitting that "nearly all" of the phone records they obtained were related to "terrorism investigations," make it clear that some were not. But they used claims of "terrorism emergency" to obtain them. These they then assert were merely "technical" violations. For many disturbing reports from major media sources on the increasing threats to civil liberties under the pretext of the "war on terrorism," click here.
The Department of Homeland Security is finalizing a proposal to collect fingerprints or eye scans from all foreign travelers at U.S. airports as they leave the country, officials said, a costly screening program that airlines have opposed. The plan ... would collect fingerprints at airport security checkpoints, departure gates or terminal kiosks, allowing the government to track when roughly 35 million foreign visitors a year. In a concession to industry, DHS said it probably will drop plans to require airlines to pay for the bulk of the program and is looking to cut costs, which could reach $1 billion to $2 billion over a decade, largely to be paid by taxpayers or foreign travelers. In addition, the program would not operate for now at land borders, where 80 percent of noncitizens enter and leave the country, because fingerprinting travelers there could cost billions more and significantly delay commerce. Congress focused on inbound travelers after the [September 11, 2001 attacks,] appropriating $3 billion since 2003 on the US-VISIT tracking program. The program collects biological identifiers, such as fingerprints and digital photographs, from all arriving foreigners except Canadians and Mexicans with special border-crossing cards. By the time Bush administration officials unveiled a $3.5 billion program in April 2008, however, political impetus for changes had weakened.
Note: For many reports from major media sources of growing government threats to civil liberties, click here.
Shares of VeriChip Corp tripled after the company said it had been granted an exclusive license to two patents, which will help it to develop implantable virus detection systems in humans. The patents, held by VeriChip partner Receptors LLC, relate to biosensors that can detect the H1N1 and other viruses. The technology will combine with VeriChip's implantable radio frequency identification devices to develop virus triage detection systems. The triage system will provide multiple levels of identification -- the first will identify the agent as virus or non-virus, the second level will classify the virus and alert the user to the presence of pandemic threat viruses and the third level will identify the precise pathogen, VeriChip said in a white paper published May 7, 2009. Shares of VeriChip were up 186 percent.
Note: Beware of efforts to scare you into getting microchipped for your own safety. Click here for more on this. For more on pharmaceutical corporation profiteering from swine flu vaccines, click here.
The Obama administration will largely preserve Bush-era procedures allowing the government to search -- without suspicion of wrongdoing -- the contents of a traveler's laptop computer, cellphone or other electronic device. The policy, disclosed ... in a pair of Department of Homeland Security directives, describes more fully than did the Bush administration the procedures by which travelers' laptops, iPods, cameras and other digital devices can be searched and seized when they cross a U.S. border. And it sets time limits for completing searches. Representatives of civil liberties and travelers groups say they see little substantive difference between the Bush-era policy, which prompted controversy, and this one. "It's a disappointing ratification of the suspicionless search policy put in place by the Bush administration," said Catherine Crump, staff attorney for the American Civil Liberties Union. "It doesn't deal with the fundamental problem, which is that under the policy, government officials are free to search people's laptops and cellphones for any reason whatsoever." "Under the policy begun by Bush and now continued by Obama, the government can open your laptop and read your medical records, financial records, e-mails, work product and personal correspondence -- all without any suspicion of illegal activity," said Elizabeth Goitein, who leads the liberty and national security project at the nonprofit Brennan Center for Justice.
Note: For important revelations of government threats to civil liberties, click here.
Internet "black boxes" will be used to collect every email and web visit in the UK under the Government's plans for a giant "big brother" database, The Independent has learnt. Home Office officials have told senior figures from the internet and telecommunications industries that the "black box" technology could automatically retain and store raw data from the web before transferring it to a giant central database controlled by the Government. Plans to create a database holding information about every phone call, email and internet visit made in the UK have provoked a huge public outcry. Richard Thomas, the Information Commissioner, described it as "step too far" and the Government's own terrorism watchdog said that as a "raw idea" it was "awful". News that the Government is already preparing the ground by trying to allay the concerns of the internet industry is bound to raise suspicions about ministers' true intentions. Further details of the database emerged on Monday at a meeting of internet service providers (ISPs) in London where representatives from BT, AOL Europe, O2 and BSkyB were given a PowerPoint presentation of the issues and the technology surrounding the Government's Interception Modernisation Programme (IMP), the name given by the Home Office to the database proposal. "It was clear the 'back box' is the technology the Government will use to hold all the data. But what isn't clear is what the Home Secretary, GCHQ and the security services intend to do with all this information in the future," said a source close to the meeting.
Note: For lots more on threats to privacy from reliable sources, click here.
Hundreds of US citizens overseas have been eavesdropped on as they called friends and family back home, according to two former military intercept operators who worked at the giant National Security Agency (NSA) center in Fort Gordon, Georgia. "These were just really everyday, average, ordinary Americans who happened to be in the Middle East, in our area of intercept and happened to be making these phone calls on satellite phones," said Adrienne Kinne, a 31-year old US Army Reserves Arab linguist assigned to a special military program at the NSA's Back Hall at Fort Gordon from November 2001 to 2003. She said US military officers, American journalists and American aid workers were routinely intercepted and "collected on" as they called their offices or homes in the United States. Another intercept operator, former Navy Arab linguist, David Murfee Faulk, 39, said he and his fellow intercept operators listened into hundreds of Americans picked up using phones in Baghdad's Green Zone from late 2003 to November 2007. Both former intercept operators came forward at first to speak with investigative journalist [James] Bamford for a book on the NSA, The Shadow Factory, to be published next week. "It's extremely rare," said Bamford, who has written two previous books on the NSA, including the landmark Puzzle Palace which first revealed the existence of the super secret spy agency. "Both of them felt that what they were doing was illegal and improper, and immoral, and it shouldn't be done, and that's what forces whistleblowers."
Note: For many reports from major media sources of disturbing threats to privacy, click here.
The Bush administration has overturned a 22-year-old policy and now allows customs agents to seize, read and copy documents from travelers at airports and borders without suspicion of wrongdoing, civil rights lawyers in San Francisco said Tuesday in releasing records obtained in a lawsuit. The records also indicate that the government gives customs agents unlimited authority to question travelers about their religious beliefs and political opinions, said lawyers from the Asian Law Caucus and the Electronic Frontier Foundation. They said they had asked the Department of Homeland Security for details of any policy that would guide or limit such questioning and received no reply. "We're concerned that people of South Asian or Muslim-looking background are being targeted inappropriately" for questioning and searches, said Asian Law Caucus attorney Shirin Sinnar. The Bay Area legal groups filed a Freedom of Information Act suit against the government in February, seeking documents on the policies that govern searches and questioning of international travelers. The organizations said they had received more than 20 complaints in the previous year, mostly from South Asians and Muslims. The travelers said customs agents regularly singled them out when they returned from abroad, looked at their papers and laptop computers, and asked them such questions as whom they had seen on their trips, whether they attended mosques and whether they hated the U.S. government.
Note: For many reports from major media sources of rising threats to civil liberties, click here.
On a cloudless spring day, the NYPD helicopter soars over the city, its sights set on the Statue of Liberty. A dramatic close-up of Lady Liberty's frozen gaze fills one of three flat-screen computer monitors mounted on a console. Hundreds of sightseers below are oblivious to the fact that a helicopter is peering down on them from a mile and a half away. "They don't even know we're here," said crew chief John Diaz, speaking into a headset over the din of the aircraft's engine. The helicopter's unmarked paint job belies what's inside: an arsenal of sophisticated surveillance and tracking equipment powerful enough to read license plates or scan pedestrians' faces from high above the nation's largest metropolis. "It looks like just another helicopter in the sky," said Assistant Police Chief Charles Kammerdener, who oversees the department's aviation unit. Police Commissioner Raymond Kelly has said that no other U.S. law enforcement agency "has anything that comes close" to the surveillance chopper, which was designed by engineers at Bell Helicopter and computer technicians based on NYPD specifications. The $10 million helicopter is just part of the department's efforts to adopt cutting-edge technology for its [surveillance] operations. The NYPD also plans to spend tens of millions of dollars strengthening security in the lower Manhattan business district with a network of closed-circuit television cameras and license-plate readers posted at bridges, tunnels and other entry points. Civil rights advocates are skeptical about the push for more surveillance, arguing it reflects the NYPD's evolution into ad hoc spy agency.
Note: For many important reports on disturbing threats to privacy, click here.
The number of Americans being secretly wiretapped or having their financial and other records reviewed by the government has continued to increase as officials aggressively use powers approved after the Sept. 11 attacks. But the number of terrorism prosecutions ending up in court -- one measure of the effectiveness of such sleuthing -- has continued to decline, in some cases precipitously. The trends, visible in new government data and a private analysis of Justice Department records, are worrisome to civil liberties groups and some legal scholars. They say it is further evidence that the government has compromised the privacy rights of ordinary citizens without much to show for it. The Bush administration has been seeking to expand its ability to gather intelligence without prior court approval. The [Justice] department ... reported a sharp rise in the use of national security letters by the FBI -- from 9,254 in 2005 to 12,583 in 2006, the latest data available. The letters seek customer information from banks, Internet providers and phone companies. They have caused a stir because consumers do not have a right to know that their information is being disclosed and the letters are issued without court oversight. Civil liberties groups say the new data reveal a disturbing consequence of the government's post-Sept. 11 expanded surveillance capabilities. "The number of Americans being investigated dwarfs any legitimate number of actual terrorism prosecutions, and that is extremely troubling," said Lisa Graves, deputy director of the Center for National Security Studies, a Washington-based civil liberties group.
Note: For many reports from major media sources that question the reality of the "terror" threat, click here.
Here's a vision of the not-so-distant future: Microchips with antennas will be embedded in virtually everything you buy, wear, drive and read, allowing retailers and law enforcement to track consumer items -- and, by extension, consumers -- wherever they go, from a distance. A seamless, global network of electronic "sniffers" will scan radio tags in myriad public settings, identifying people and their tastes instantly so that customized ads, "live spam," may be beamed at them. In "Smart Homes," sensors built into walls, floors and appliances will inventory possessions, record eating habits, monitor medicine cabinets -- all the while, silently reporting data to marketers eager for a peek into the occupants' private lives. Science fiction? In truth, much of the radio frequency identification [RFID] technology that enables objects and people to be tagged and tracked wirelessly already exists -- and new and potentially intrusive uses of it are being patented, perfected and deployed. Some of the world's largest corporations are vested in the success of RFID technology, which couples highly miniaturized computers with radio antennas to broadcast information about sales and buyers to company databases. Already, microchips are turning up in some computer printers, car keys and tires, on shampoo bottles and department store clothing tags. They're also in library books and "contactless" payment cards. With tags in so many objects, relaying information to databases that can be linked to credit and bank cards, almost no aspect of life may soon be safe from the prying eyes of corporations and governments, says Mark Rasch, former head of the computer-crime unit of the U.S. Justice Department.
Note: For lots more on microchip implants, click here.
For the last four years, two robot rovers operated from the Jet Propulsion Laboratory in La Canada Flintridge have been moving across the surface of Mars, taking photographs and collecting information. It's an epic event in the history of exploration, one of many for which JPL's 7,000 civilian scientists and engineers are responsible -- when they're not fending off the U.S. government's attempts to conduct an intimidating and probably illegal inquisition into the intimate details of their lives. The problem began -- as so many have -- in the security mania that gripped the Bush administration after 9/11. Presidential Directive No. 12, issued by the Department of Homeland Security, directed federal agencies to adopt a uniform badge that could be used by employees and contractors to gain access to government facilities. NASA Administrator Michael Griffin ... directed Caltech, which has a contract to run JPL for NASA, to make sure all of the lab's employees complied. The government demanded that the scientists, in order to get the badges, fill out questionnaires on their personal lives and waive the privacy of their financial, medical and psychiatric records. The government also wanted permission to gather information about them by interviewing third parties. Twenty-eight of JPL's senior scientists sued in federal court to stop the government and Caltech from forcing them to agree to the background checks as the price of keeping their jobs. They point out that Griffin is one of those who remain skeptical that human actions contribute to global warming, and that some of JPL's near-Earth science has played a critical role in establishing the empirical case to the contrary. They see the background checks as the first step toward establishing a system of intimidation that might be used to silence inconvenient science.
Note: For many disturbing reports on threats to our civil liberties, click here.
Transcript: [Suzanne] MALVEAUX: A Texas mystery solved -- at least partially. We now know Houston police are going to start using unmanned drone aircraft. But the question remains, well, for what? Stephen Dean of CNN affiliate KPRC has got an exclusive look. STEPHEN DEAN, KPRC CORRESPONDENT (voice-over): HPD [Houston Police Dept.], the federal Department of Homeland Security and other invited guests all watching to see how this drone could be used for police work in and around Houston. We tracked that drone from News Chopper 2. And that drone was able to use a high-powered camera to track us. Those cameras can actually look into people's homes or even follow them in moving cars -- which raises all sorts of new questions. HPD quickly hustled together a news conference when it realized our cameras were there for the entire secret test. Executive Assistant Chief Martha Mantabo admits that could mean covert police action. But she says it's too early to tell what else HPD will do with the aircraft. We asked, are these drones headed for ticketing speeders from the sky? MONTALVO: I'm not ruling anything out. DEAN: Back at the secret test site, police helicopter pilots claimed the entire air space was restricted and even threatened our local 2 Investigates pilot with action from the FAA if we didn't leave. But we checked with FAA several times and there never was a flight restriction. That leaves some to wonder whether the police are now ready to use terrorism fears since 911 to push the envelope further into our private lives.
Note: To watch the video of secret police work in action, click here.
According to a former AT&T employee, the government has warrantless access to a great deal of Internet traffic should they care to take a peek. As information is traded between users it flows also into a locked, secret room on the sixth floor of AT&T's San Francisco offices and other rooms around the country -- where the U.S. government can sift through and find the information it wants, former AT&T employee Mark Klein alleged Wednesday at a press conference on Capitol Hill. "An exact copy of all Internet traffic that flowed through critical AT&T cables -- e-mails, documents, pictures, Web browsing, voice-over-Internet phone conversations, everything -- was being diverted to equipment inside the secret room," he said. Klein ... said that as an AT&T technician overseeing Internet operations in San Francisco, he helped maintain optical splitters that diverted data en route to and from AT&T customers. One day he found that the splitters were hard-wired into a secret room on the sixth floor. Documents he obtained [from] AT&T showed that highly sophisticated data mining equipment was kept there. Conversations he had with other technicians and the AT&T documents led Klein to believe there are 15 to 20 such sites nationwide, including in Seattle, Los Angeles, San Jose, San Diego and Atlanta, he said. Brian Reid, a former Stanford electrical engineering professor who appeared with Klein, said the NSA would logically collect phone and Internet data simultaneously because of the way fiber optic cables are intertwined. He said ... the system described by Klein suggests a "wholesale, dragnet surveillance." Of the major telecom companies, only Qwest is known to have rejected government requests for access to data. Former Qwest CEO Joseph Nacchio, appealing an insider trading conviction last month, said the government was seeking access to data even before Sept. 11.
The Halle Orchestra, one of Great Britain's oldest symphony orchestras, has not toured the United States in more than a decade, so spirits were high when the group secured dates at Lincoln Center and in Upstate New York for performances last winter. But when the orchestra learned that to get their entry visas, all 85 musicians -- every last cellist, oboist and piccolo player -- would have to travel from their Manchester headquarters to the U.S. Embassy in London for personal interviews, electronic fingerprinting and facial-recognition scans, it scrapped the trip. Budgeting for airfare and travel costs to New York was one thing, but simply getting everyone to the embassy at the same time, along with hotel bills and fees for the visas themselves, would have cost an additional $80,000, said marketing director Andy Ryans. "It was very simply money that we didn't have," Ryans explained. "We were desperate to go to the States, but our hands were absolutely tied." Theirs aren't the only ones. To perform in this country, foreign artists of all stripes -- punk rockers, ballet dancers, folk musicians, acrobats -- are funneled through a one-size-fits-all "nonimmigrant" visa process whose costs and complications have become prohibitive, according to booking agents, managers and presenters, such as the Kennedy Center, who program and market the performers. Visiting businesspeople face similar security hurdles put in place since Sept. 11, 2001. But artists' visa petitions also require substantial documentation to satisfy the "sustained international recognition" requirement for the type of visa (called a "P-1") issued to many performing artists. Arts organizations say they have become reluctant to book foreign performers because of the risk of bureaucratic snags. Soon after Sept. 11, the State Department rolled out its Biometric Visa Program, requiring all applicants to undergo fingerprinting and have photographs taken at the nearest U.S. consulate each time they apply.
A former Qwest Communications International executive, appealing a conviction for insider trading, has alleged that the government withdrew opportunities for contracts worth hundreds of millions of dollars after Qwest refused to participate in an unidentified National Security Agency program that the company thought might be illegal. Former chief executive Joseph P. Nacchio, convicted in April of 19 counts of insider trading, said the NSA approached Qwest more than six months before the Sept. 11, 2001, attacks ... about participating in a warrantless surveillance program to gather information about Americans' phone records. In the court filings disclosed this week, Nacchio suggests that Qwest's refusal to take part in that program led the government to cancel a separate, lucrative contract with the NSA in retribution. He is using the allegation to try to show why his stock sale should not have been considered improper. He has claimed in court papers that he had been optimistic that Qwest would overcome weak sales because of the expected top-secret contract with the government. Nacchio's account, which places the NSA proposal at a meeting on Feb. 27, 2001, suggests that the Bush administration was seeking to enlist telecommunications firms in programs without court oversight before the terrorist attacks on New York and the Pentagon. The Sept. 11 attacks have been cited by the government as the main impetus for its warrantless surveillance efforts. In May 2006, USA Today reported that the NSA had been secretly collecting the phone-call records of tens of millions of Americans, using data provided by major telecom firms. Qwest, it reported, declined to participate because of fears that the program lacked legal standing.
Note: The Bush Administration has claimed that the NSA surveillance of the American public was a necessary response to the attacks of 9/11. But this story reveals that the surveillance began before 9/11, shortly after Bush took office. The obvious question is, why? For many other reliable, verifiable reports that suggest the official explanation of the events of 9/11 is false, click here.
The Bush administration ... plans to turn again to a legal tool, the state secrets privilege, to try to stop a suit against a Belgian banking cooperative [known as Swift] that secretly supplied millions of private financial records to the United States government. The state secrets privilege, allowing the government to shut down litigation on national security grounds, was once rarely used. The Bush administration has turned to it more than 30 times, seeking to end public discussion of cases like the claims of an F.B.I. whistle-blower and the abduction of a German terrorism suspect. Most notably, the administration has sought to use the privilege to kill numerous suits against telecommunications carriers over the National Security Agencys eavesdropping program. Swift is considered the nerve center of the global banking industry, routing trillions of dollars each day among banks, brokerage houses and other financial institutions. Its partnership with Washington ... gave Central Intelligence Agency and Treasury Department officials access to millions of records on international banking transactions. Months after the Sept. 11, 2001, attacks, Swift began turning over large chunks of its database in response to a series of unusually broad subpoenas from the Treasury Department. Two American banking customers ... sued Swift on invasion-of-privacy grounds. [Steven E. Schwarz, the lawyer for the plaintiffs, said the Swift program] is an Orwellian example of government overreaching and unfettered access to private financial information that is not consistent with the values upon which our country was founded. Weve seen a real erosion of the state secrets privilege in the last year. I think it is from overuse. Weve seen it used in record numbers, in situations where it was inappropriate, and the courts are starting to recognize that.
The Bush administration plans to leave oversight of its expanded foreign eavesdropping program to the same government officials who supervise the surveillance activities and to the intelligence personnel who carry them out, senior government officials said yesterday. The law, which permits intercepting Americans' calls and e-mails without a warrant if the communications involve overseas transmission, gives Director of National Intelligence Mike McConnell and Attorney General Alberto R. Gonzales responsibility for creating the broad procedures determining whose telephone calls and e-mails are collected. It also gives McConnell and Gonzales the role of assessing compliance with those procedures. The law ... does not contain provisions for outside oversight -- unlike an earlier House measure that called for audits every 60 days by the Justice Department's inspector general. The controversial changes to the 1978 Foreign Intelligence Surveillance Act were approved by both chambers of the Democratic-controlled Congress despite privacy concerns raised by Democratic leaders and civil liberties advocacy groups. Central to the new program is the collection of foreign intelligence from "communication service providers," which the officials declined to identify, citing secrecy concerns. Under the new law, the attorney general is required to draw up the governing procedures for surveillance activity, for approval by the Foreign Intelligence Surveillance Court. Once the procedures are established, the attorney general and director of national intelligence will formally certify that the collection of data is authorized. But the certification will be placed under seal "unless the certification is necessary to determine the legality of the acquisition," according to the law signed by Bush.
Counterterrorism agents at the Federal Bureau of Investigation have conducted numerous surveillance and intelligence-gathering operations that involved, at least indirectly, groups active in causes as diverse as the environment, animal cruelty and poverty relief. One F.B.I. document...talks of the Catholic Workers group's "semi-communistic ideology." The documents...came as part of a series of Freedom of Information Act lawsuits brought by the American Civil Liberties Union. The latest batch of documents...totals more than 2,300 pages and centers on references in internal files to a handful of groups, including PETA, the environmental group Greenpeace and the Catholic Workers group, which promotes antipoverty efforts and social causes. Many of the investigative documents turned over by the bureau are heavily edited. The documents indicate that in some cases, the F.B.I. has used employees, interns and other confidential informants within groups like PETA and Greenpeace to develop leads on potential criminal activity and has downloaded material from the groups' Web sites, in addition to monitoring their protests.
Coming to you soon from the Pentagon: the diary to end all diaries a multimedia, digital record of everywhere you go and everything you see, hear, read, say and touch. Known as LifeLog, the project has been put out for contractor bids by the Defense Advanced Research Projects Agency, or DARPA, the agency that helped build the Internet and that is now developing the next generation of [surveillance] tools. The agency ... [considers] LifeLog ... a tool to capture "one person's experience in and interactions with the world" through a camera, microphone and sensors worn by the user. Everything from heartbeats to travel to Internet chatting would be recorded. The goal is to create breakthrough software that helps analyze behavior, habits and routines, according to Pentagon documents reviewed by The Associated Press. The products of the unclassified project would be available to both the private sector and other government agencies a concern to privacy advocates. John Pike of Global Security.org, a defense analysis group, is dubious the project has military application. "I have a much easier time understanding how Big Brother would want this than how (Defense Secretary Donald) Rumsfeld would use it," Pike said. "They have not identified a military application."
Note: For more on this at Wired, click here.
Computer users across Europe should encrypt all their e-mails, to avoid being spied on by a UK-US eavesdropping network, say Euro-MPs. The tentacles of the Echelon network stretch so far that the UK's involvement could constitute a breach of human rights, they say. The Euro-MPs have been studying Echelon for almost a year, after allegations that it has been used by the US to commit industrial espionage against European firms. They conclude that Echelon - whose existence is not officially acknowledged - is reading millions of e-mails and faxes sent every day by ordinary people. The US has denied the system even exists, and the UK refuses to give details, except to say that communications interception is a vital tool in the fight against "dangers to society". The Echelon operation is based at Fort Meade in Maryland, America, and at the UK's spy centre, GCHQ in Cheltenham.
Note: For another revealing BBC News report on Echelon, click here.
Last March, Tony Schmidt discovered something unsettling about the machine that helps him breathe at night. Without his knowledge, it was spying on him. From his bedside, the device was tracking when he was using it and sending the information not just to his doctor, but to the maker of the machine, to the medical supply company that provided it and to his health insurer. Schmidt, an information technology specialist ... was shocked. "I had no idea they were sending my information across the wire." Like millions of people, he relies on a continuous positive airway pressure, or CPAP, machine that streams warm air into his nose while he sleeps. Without it, Schmidt would wake up hundreds of times a night. As many CPAP users discover, the life-altering device comes with caveats: Health insurance companies are often tracking whether patients use them. If they aren't, the insurers might not cover the machines or the supplies that go with them. And, faced with the popularity of CPAPs ... and their need for replacement filters, face masks and hoses, health insurers have deployed a host of tactics that can make the therapy more expensive or even price it out of reach. A host of devices now gather data about patients, including insertable heart monitors and blood glucose meters. Privacy laws have lagged behind this new technology, and patients may be surprised to learn how little control they have over how the data is used or with whom it is shared.
Note: For more along these lines, see concise summaries of deeply revealing news articles on health and the disappearance of privacy.
Mexican journalists, lawyers and activists were targeted by spyware produced by Israels NSO Group that is sold exclusively to governments. [A] report by Citizen Lab at the University of Toronto said the targets included people, such as prominent journalists Carmen Aristegui and Carlos Loret de Mola, who were investigating alleged government corruption and purported human rights abuses by security forces. The people targeted received messages with links that, if clicked on, opened up their devices to being exploited and spied upon. NSOs Pegasus spyware allows hackers access to phone calls, messages, cameras and personal data. Other targets included members of the Centro Miguel Agustin Pro Juarez, a prominent human rights group that has investigated cases such as the disappearance of 43 students whom police allegedly detained and turned over to drug gang killers; the anti-graft group Mexicans Against Corruption and Impunity; and the Mexican Institute for Competitiveness, a civil society group working on economic policy and combatting corruption. Aristegui, who exposed a case of possible conflict of interest involving a luxury home acquired from a government contractor ... was aggressively targeted. She received more than two-dozen messages with NSO links claiming to be from the U.S. Embassy in Mexico, Amber Alerts, colleagues, people in her personal life, her bank, phone company and notifications of kidnappings, the report said.
Note: If the above link is not working, this Associated Press article is also available here. For more along these lines, see concise summaries of deeply revealing news articles on corruption in government and the erosion of civil liberties.
A decade-old internet scourge called ransomware went mainstream on Friday when cybercriminals seized control of computers around the world, from the delivery giant FedEx in the United States to Britains public health system, universities in China and even Russias powerful Interior Ministry. Ransomware is nothing new. For years, there have been stories of individuals or companies horrified that they have been locked out of their computers and that the only way back in is to pay a ransom to someone, somewhere who has managed to take control. But computer criminals are discovering that ransomware is the most effective way to make money in the shortest amount of time. Fridays attacks were a powerful escalation of earlier, much smaller episodes. Hackers exploited a vulnerability in Microsoft servers that was first discovered by the National Security Agency and then leaked online. It allowed the ransomware to spread [to] more than 70,000 organizations. There is even now a concept of ransomware as a service - a play on the Silicon Valley jargon software as a service, which describes the delivery of software over the internet. Now anyone can visit a web page, generate a ransomware file with the click of a mouse, encrypt someones systems and demand a ransom to restore access to the files. If the victim pays, the ransomware provider takes a cut of the payment. Ransomware criminals also have customer service lines that victims can call to get help paying a ransom.
Note: In 2014, it was reported that the NSA was developing tools to make it relatively easy to hack millions of computers at once. Two years later, a large collection of NSA hacking tools was leaked. Now, these tools are being used by criminals against people all over the world. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
Drone aircraft spy on and attack terrorists with no pilot in harm's way. Small teams of special operations troops quietly train and advise foreign forces. Viruses sent from computers to foreign networks strike silently, with no American fingerprint. It's war in the shadows, with the U.S. public largely in the dark. The high-tech warfare allows Obama to target what the administration sees as the greatest threats to U.S. security, without the cost and liabilities of sending a swarm of ground troops to capture territory; some of them almost certainly would come home maimed or dead. But it also raises questions about accountability and the implications for international norms regarding the use of force outside of traditional armed conflict. "Congressional oversight of these operations appears to be cursory and insufficient," said Steven Aftergood, an expert on government secrecy issues for the Federation of American Scientists, a private group. "It is Congress' responsibility to declare war under the Constitution, but instead it appears to have adopted a largely passive role while the executive takes the initiative in war fighting," Aftergood said in an interview. That's partly because lawmakers relinquished their authority by passing a law just after the Sept. 11 [attacks]. In this shroud of secrecy, leaks to the news media of classified details about certain covert operations have led to charges that the White House orchestrated the revelations to bolster Obama's national security credentials and thereby improve his re-election chances.
Note: For deeper analysis of the threats posed to American citizens by military and police drones in the skies, click here. For information on a federal recent law compelling the Federal Aviation Administration to allow drones to fly in US skies, click here. For more information on the use of drones by police in the US, click here. For lots more from reliable sources on surveillance in the US, click here.
The government will be able to monitor the calls, emails, texts and website visits of everyone in the UK under new legislation set to be announced soon. Internet firms will be required to give intelligence agency GCHQ access to communications on demand, in real time. The Home Office says the move is key to tackling crime and terrorism, but civil liberties groups have criticised it. Tory MP David Davis called it "an unnecessary extension of the ability of the state to snoop on ordinary people". A new law ... would not allow GCHQ to access the content of emails, calls or messages without a warrant. But it would enable intelligence officers to identify who an individual or group is in contact with, how often and for how long. They would also be able to see which websites someone had visited. Conservative MP and former shadow home secretary David Davis said it would make it easier for the government "to eavesdrop on vast numbers of people". "What this is talking about doing is not focusing on terrorists or criminals, it's absolutely everybody's emails, phone calls, web access..." He said that until now anyone wishing to monitor communications had been required to gain permission from a magistrate. Nick Pickles, director of the Big Brother Watch campaign group, called the move "an unprecedented step that will see Britain adopt the same kind of surveillance seen in China and Iran". The previous Labour government attempted to introduce a central, government-run database of everyone's phone calls and emails, but eventually dropped the bid after widespread anger.
Note: For more on this from BBC, click here. Though this is interesting news, many know that the government has had easy access to all people's emails, phone calls, and more for many years through systems like echelon and more. For an abundance of major media articles showing how many of the power elite want to create a big-brother society, click here.
Companies have long used criminal background checks, credit reports and even searches on Google and LinkedIn to probe the previous lives of prospective employees. Now, some companies are requiring job candidates to also pass a social media background check. A year-old start-up, Social Intelligence, scrapes the Internet for everything prospective employees may have said or done online in the past seven years. Then it assembles a dossier with examples of professional honors and charitable work, along with negative information that meets specific criteria: online evidence of racist remarks; references to drugs; sexually explicit photos, text messages or videos; flagrant displays of weapons or bombs and clearly identifiable violent activity. The service ... alarms privacy advocates who say that it invites employers to look at information that may not be relevant to job performance. And what relevant unflattering information has led to job offers being withdrawn or not made? Marc S. Rotenberg, president of the Electronic Privacy Information Center, ... said that employers were entitled to gather information to make a determination about job-related expertise, but he expressed concern that employers should not be judging what people in their private lives do away from the workplace.
Note: For key reports from major media sources on government threats to privacy and civil liberties, click here and here.
Skipping class, though frowned upon, is practically a rite of passage for young teens, but thanks to an elaborate system involving GPS being used by some school districts, it is practically being eliminated completely. The Orange County Register reports that the Anaheim Union High School District in California is currently participating in a pilot program which involves using a combination of Global Positioning System technology, automated telephone reminders, and one-on-one coaching to cut down on truancy. It's similar to programs being used in Baltimore and San Antonio. Basically any students in the seventh- or eighth-grade who have four or more unexcused absences over the course of a school year can be put into the Anaheim program. They will be assigned a GPS tracking device about the size of a cell phone, and they'll need to use it regularly, the newspaper said. It's worth noting that while this anti-truancy program is very elaborate and almost invasive, it is [promoted as] optional. Students and their parents are offered the chance to voluntarily participate in the "monitoring as a way to avoid continuation school or prosecution with a potential stay in juvenile hall." On top of that, parents would also be avoiding the $2,000 fine that can come from turning a blind eye to truancy if a school district chooses to pursue the issue.
Note: For other revealing media articles on microchips being used to invade privacy, click here. To better understand a program of elements within the power elite to microchip the entire population, click here.
Consumer Watchdog, an advocacy group largely focused in recent years on Google's privacy practices, has called [for] a congressional investigation into the Internet giant's "cozy" relationship with U.S. President Barack Obama's administration. In a letter sent [on January 24], Consumer Watchdog asked Representative Darrell Issa, the new chairman of the House Oversight and Government Reform Committee, to investigate the relationship between Google and several government agencies. "We believe Google has inappropriately benefited from close ties to the administration," the letter said. "It should not get special treatment and access because of a special relationship with the administration." Consumer Watchdog's latest complaints about the relationship of Google and the Obama administration are outlined in a 32-page report [which] questions Google's relationship with the U.S. National Security Agency and calls for the company to be more open about what consumer information it shares with the spy agency.
It's time to reflect on the immense powers Americans have ceded to the government and [the] potential for abuse by federal, state and local authorities. The global Internet and telecommunications infrastructure provides massive information on almost ... every person on the planet. One power truly stands out --- the all-encompassing reach and technological capabilities of the US National Security Agency. If you want to be secure, don't use a phone, a computer, credit card or any other technologically linked system because it guarantees that Big Brother will find you. Big Brother is not just the government. Most consumer "spying" comes from subpoenas and requests from non-terrorist-related federal, state, local agency requests and non-governmental private litigation and discovery. Simply put, a subpoena issued by a court in support of private litigation and discovery may have the same impact on an individual as the full force of the NSA. What information is typically requested from a company by say a plaintiff's lawyer during some discovery phase? Well, it's everything. In fact, it's generally a fishing expedition for every log file, every uploaded video, photo, chat session and anything else they can get their hands on.
Note: For lots more from major media sources on the continuing development of a global society under Big Brother's constant gaze, click here.
A San Francisco federal judge rejected on Friday the Obama administration's attempt to derail a challenge to former President George W. Bush's electronic surveillance program by withholding a critical wiretap document. President Obama's Justice Department had appeared to defy a previous order by Chief U.S. District Judge Vaughn Walker to allow lawyers for an Islamic organization to see the classified document, which reportedly showed that the group had been wiretapped. The document, which the government accidentally sent to the Al-Haramain Islamic Foundation, could establish its right to sue over the legality of the program. Justice Department lawyers told Walker in February that he had no power to enforce his order, and indicated they would remove the document from his files if he planned to disclose it to Al-Haramain's lawyers. But after a federal appeals court denied the department's request to intervene, Walker told the government Friday to cooperate. "The United States should now comply with the court's orders," the judge said. He told lawyers for the administration and Al-Haramain to work out a protective order by May 8 that would maintain the document's secrecy after it had been shown to the Islamic group's lawyers. If the two sides can't agree, Walker said, he will issue his own protective order "under which this case may resume forward progress." The case is one of two before Walker challenging the constitutionality of the program that Bush secretly authorized in 2001 to intercept phone calls and e-mails between Americans and suspected foreign terrorists without seeking a court warrant, as required by a 1978 law.
Note: For more reports on government secrecy from reliable sources, click here.
Imagine someone watching your every move, hearing everything you say and knowing where you are at every moment. If you have a cell phone, it could happen to you. After four months of harassing phone calls, Courtney Kuykendall was afraid to answer her cell phone. The Tacoma, Washington, teenager was receiving graphic, violent threats at all hours. And when she and her family changed their cell phone numbers and got new phones, the calls continued. Using deep scratchy voices, anonymous stalkers literally took control of the Kuykendall's cell phones, repeatedly threatened Courtney with murder and rape, and began following the family's every move. "They're listening to us and recording us," Courtney's mother, Heather Kuykendall, told NBC's Today Show. "We know that because they will record us and play it back as a voicemail." How is something like this possible? Just take a look on the internet. That's where you'll find the latest spy technology for cell phones. Spyware marketers claim you can tap into someone's calls, read their text messages and track their movements "anywhere, anytime." Security experts say it's no internet hoax."It's real, and it is pretty creepy," said Rick Mislan, a former military intelligence officer who now teaches cyber forensics at Purdue University's Department of Computer and Information Technology. Mislan has examined thousands of cell phones inside Purdue's Cyber Forensics Lab, and he says spy software can now make even the most high-tech cell phone vulnerable. "I think a lot of people think their cell phone calls are very secure but our privacy isn't always what we think it is."
Note: For lots more on increasing corporate and governmental threats to privacy, click here.
Civil liberties groups started a legal challenge ... to the new federal law designed to dismiss their wiretapping suits against telecommunications companies, saying the statute violates phone customers' constitutional rights and tramples on judicial authority. The law ... granted retroactive protection to AT&T, Verizon and other companies against lawsuits accusing them of illegally sharing their telephone and e-mail networks and millions of customer records with the National Security Agency. Almost 40 such suits from around the nation are pending before Chief U.S. District Judge Vaughn Walker in San Francisco. The law requires him to dismiss the cases if the Justice Department tells him the companies had cooperated in a surveillance program authorized by President Bush. Details of the department's filing and the judge's dismissal order are to be kept secret. The American Civil Liberties Union and the Electronic Frontier Foundation attacked the secrecy requirements and argued that Congress and President Bush lack authority to order courts to whitewash constitutional violations. "If Congress can give the executive the power to exclude the judiciary from considering the constitutional claims of millions of Americans ... then the judiciary will no longer be functioning as a coequal branch of government," Cindy Cohn, the foundation's legal director, said in court papers. She said the law's secrecy makes the proceedings one-sided. "Due process requires more than the chance to shadow-box with the government," Cohn wrote.
Note: For many reports from reliable, verifiable sources on threats to civil liberties, click here.
By exploring the current, post-9/11 operations of the NSA [National Security Agency, James] Bamford ... goes where congressional oversight committees and investigative journalists still struggle to go. [When] the Bush administration declared its ... global war on terror, Congress agreed to most of the White House's demands. According to Bamford, the NSA's expanded powers and resources enabled it to collect communications both inside and outside the United States. He quotes a former NSA employee as a witness to the agency's spying on the conversations of Americans who have no connection to terrorism. After suing the NSA for documents, [Bamford] obtained considerable evidence that telecommunication companies (with the notable exception of Qwest) knowingly violated U.S. law by cooperating with the NSA to tap fiber optic lines. In impressive detail, The Shadow Factory: The Ultra-Secret NSA from 9/11 to the Eavesdropping on America tells how private contractors, including some little-known entities with foreign owners, have done the sensitive work of storing and processing the voices and written data of Americans and non-Americans alike. In the book, he offers new revelations about the National Security Agency's counterterrorism tactics, including its controversial domestic surveillance programs. Bamford warns of worse to come: 'There is now the capacity to make tyranny total in America. Only law ensures that we never fall into that abyss -- the abyss from which there is no return.'"
Note: Bamford is the author of two other books on the NSA: Body of Secrets and The Puzzle Palace.
America is ruled by an intelligence-industrial complex whose allegiance is not to the taxpaying public but to a cabal of private-sector contractors. That is the central thesis of Spies for Hire: The Secret World of Intelligence Outsourcing by Tim Shorrock, ... an investigative journalist. His book [provides a] disturbing overview of the intelligence community, also known as the I.C. Mr. Shorrock says our government is outsourcing 70 percent of its intelligence budget, or more than $42 billion a year, to a secret army of corporate vendors. Because of accelerated privatization efforts after 9/11, these companies are participating in covert operations and intelligence-gathering activities that were considered inherently governmental functions reserved for agencies like the Central Intelligence Agency, he says. Some of the books most intriguing assertions concern the permeating influence of the consulting firm Booz Allen Hamilton. In 2006, Mr. Shorrock reports, Booz Allen amassed $3.7 billion in revenue, much of which came from classified government contracts exempt from public oversight. Among its more than 18,000 employees are R. James Woolsey, the former C.I.A. director, and Joan Dempsey, a former longtime United States intelligence official who declared in a 2004 speech, I like to refer to Booz Allen as the shadow I.C. The revolving door between Booz Allen and the I.C. is personified by Mike McConnell, who joined the firm after serving as head of the National Security Agency under President Bill Clinton, only to return as director of national intelligence under President Bush.
Note: For revealing reports on government corruption from reliable sources, click here.
For 30 years, Lew Ellingson loved being a telephone man. His job splicing phone cables was one that he says gave him a true sense of accomplishment, first for Northwestern Bell, then US West and finally Qwest Communications International. But by the time Mr. Ellingson retired from Qwest last year at 52, he had grown angry. An insider trading scandal had damaged the companys reputation, and the life savings of former colleagues had evaporated in the face of Qwests stock troubles. It was a good place, he said wistfully. And then something like this happened. Now, Mr. Ellingson is the public face of a proposed ballot measure in Colorado that seeks to create what supporters hope will be the nations toughest corporate fraud law. Buttressed by local advocacy groups and criticized by a Colorado business organization, the measure would make business executives criminally responsible if their companies run afoul of the law. It would also permit any Colorado resident to sue the executives under such circumstances. Proceeds from successful suits would go to the state. If passed by voters in November, the proposal would leave top business officers [with] unprecedented individual accountability, said Mr. Ellingson. If nothing else, these folks in charge of the corporations and companies will think twice about cutting corners to make themselves look more profitable than they really are, he said. The plight of Mr. Ellingsons former employer, Qwest, based in Denver, was a motivation for the proposal. Last April, a jury in Denver convicted Qwests former chief executive, Joseph P. Nacchio, of 19 of 42 counts of insider trading. Mr. Nacchio was sentenced to six years in prison and ordered to pay a fine of $19 million and forfeit $52 million in money he earned from stock sales in 2001.
Note: As reported in the Washington Post, Joseph P. Nacchio, the former Qwest CEO, has claimed that he was singled out for prosecution because he refused to cooperate with the National Security Agency's electronic surveillance of American citizens, which began before 9/11.
For three years, the Bush administration has drawn fire from civil liberties groups over its use of national security letters, a kind of administrative subpoena that compels private businesses such as telecommunications companies to turn over information to the government. After the 2001 USA Patriot Act loosened the guidelines, the FBI issued tens of thousands of such requests, something critics say amounts to warrantless spying on Americans who have not been charged with crimes. Now, newly released documents shed light on the use of the letters by the CIA. The spy agency has employed them to obtain financial information about U.S. residents and does so under extraordinary secrecy, according to the American Civil Liberties Union, which obtained copies of CIA letters under the Freedom of Information Act. The CIA's requests for financial records come with "gag orders" on the recipients, said ACLU lawyer Melissa Goodman. In many cases, she said, the recipient is not allowed to keep a copy of the letter or even take notes about the information turned over to the CIA. The ACLU posted copies of some of the letters on its Web site. In most cases, nearly all the text had been redacted by CIA censors.
Note: For many powerful reports on the growing threats to civil liberties, click here.
Executives at the two biggest phone companies contributed more than $42,000 in political donations to Senator John D. Rockefeller IV this year while seeking his support for legal immunity for businesses participating in National Security Agency eavesdropping. The surge in contributions came from a Whos Who of executives at the companies, AT&T and Verizon, starting with the chief executives and including at least 50 executives and lawyers at the two utilities, according to campaign finance reports. The money came primarily from a fund-raiser that Verizon held for Mr. Rockefeller in March in New York and another that AT&T sponsored for him in May in San Antonio. Mr. Rockefeller, chairman of the Senate Intelligence Committee, [has emerged] as the most important supporter of immunity in [the Senate]. Mr. Rockefellers office said ... that the sharp increases in contributions from the telecommunications executives had no influence on his support for the immunity provision. Any suggestion that Senator Rockefeller would make policy decisions based on campaign contributions is patently false, Wendy Morigi, a spokeswoman for him, said. AT&T and Verizon have been lobbying hard to insulate themselves from suits over their reported roles in the security agency program by gaining legal immunity from Congress. The effort included meetings with Mr. Rockefeller and other members of the intelligence panels. Mr. Rockefeller received little in the way of contributions from AT&T or Verizon executives before this year, reporting $4,050 from 2002 through 2006. From last March to June, he collected a total of $42,850 from executives at the two companies. The increase was first reported by the online journal Wired, using data compiled by the Web site OpenSecrets.org. [Telecommunications] industry executives have given significant contributions to a number of other Washington politicians, including two presidential contenders, Senators Hillary Rodham Clinton and John McCain.
Vanessa Alarcon saw them while working at an antiwar rally in Lafayette Square last month. "I heard someone say, 'Oh my god, look at those,' " the college senior from New York recalled. "I look up and I'm like, 'What the hell is that?' They looked kind of like dragonflies or little helicopters. But I mean, those are not insects." Out in the crowd, Bernard Crane saw them, too. "I'd never seen anything like it in my life," the Washington lawyer said. "They were large for dragonflies. I thought, 'Is that mechanical, or is that alive?' " Some suspect the insectlike drones are high-tech surveillance tools, perhaps deployed by the Department of Homeland Security. No agency admits to having deployed insect-size spy drones. But a number of U.S. government and private entities acknowledge they are trying. So what was seen by Crane, Alarcon and a handful of others at the D.C. march -- and as far back as 2004, during the Republican National Convention in New York, when one observant ... peace-march participant described on the Web "a jet-black dragonfly hovering about 10 feet off the ground, precisely in the middle of 7th Avenue . . . watching us?" Three people at the D.C. event independently described a row of spheres, the size of small berries, attached along the tails of the big dragonflies -- an accoutrement that [Jerry Louton, an entomologist at the National Museum of Natural History,] could not explain. And all reported seeing at least three maneuvering in unison. "Dragonflies never fly in a pack," he said. Mara Verheyden-Hilliard of the Partnership for Civil Justice said her group is investigating witness reports and has filed Freedom of Information Act requests with several federal agencies. If such devices are being used to spy on political activists, she said, "it would be a significant violation of people's civil rights."
Note: To read further reliable reports of threats to our civil liberties, click here.
Li Runsen, the powerful technology director of Chinas ministry of public security, is best known for leading Project Golden Shield, Chinas intensive effort to strengthen police control over the Internet. But last month Mr. Li took an additional title: director for China Security and Surveillance Technology, a fast-growing company that installs and sometimes operates surveillance systems for Chinese police agencies, jails and banks, among other customers. The company has just been approved for a listing on the New York Stock Exchange. The companys listing and Mr. Lis membership on its board are just the latest signs of ever-closer ties among Wall Street, surveillance companies and the Chinese governments security apparatus. Wall Street analysts now follow the growth of companies that install surveillance systems providing Chinese police stations with 24-hour video feeds from nearby Internet cafes. Hedge fund money from the United States has paid for the development of not just better video cameras, but face-recognition software and even newer behavior-recognition software designed to spot the beginnings of a street protest and notify police. Executives of Chinese surveillance companies say they are helping their government reduce street crime, preserve social stability and prevent terrorism. They note that London has a more sophisticated surveillance system, although the Chinese system will soon be far more extensive. Wall Street executives also defend the industry as necessary to keep the peace at a time of rapid change in China. They point out that New York has begun experimenting with surveillance cameras in Lower Manhattan and other areas of the city.
Traditionally, powerful spy satellites have been used to search for strategic threats overseas. But now the Department of Homeland Security has developed a new office to use the satellites to [monitor the US itself]. [DHS] officials ... faced extensive criticism [in Congress] about the privacy and civil liberty concerns of the new office, called the National Applications Office. [House Homeland Security] Committee members expressed concern about abuse of the satellite imagery, charging that Homeland Security had not informed the oversight committee about the program. "What's most disturbing is learning about it from The Wall Street Journal," said Committee Chairman Rep. Bennie Thompson, D-Miss. The lawmakers also expressed concern about using military capabilities for U.S. law enforcement and Homeland Security operations, potentially a violation of the Posse Comitatus Act, which bars the military from serving as a law enforcement body within the United States. Committee members said that in addition to not being informed about the National Applications Office program, they had not yet been provided with documents defining the limits and legal guidance about the program. [They] sent a letter to Homeland Security saying, "We are so concerned that ... we are calling for a moratorium on the program. Today's testimony made clear that there is effectively no legal framework governing the domestic use of satellite imagery for the various purposes envisioned by the department."
The ability to blend vast databases containing personal information -- and the sophistication of tracking devices that can announce your presence along with myriad vital statistics when you cross a bridge or enter a room -- have brought Americans to a crossroads. Do we shrug and concede that privacy is lost -- "get over it," as one titan of tech declared so bluntly? Or do we look for ways to draw the line, to identify means and places where employers and governments should not dare to tread? One such place: Our bodies. Life has begun to imitate art -- as in the futuristic film "Minority Report" -- with the refinement of toothpick-thick microchips that can be implanted in your arm and packed with loads of personally identifiable information that can be beamed to the world. These radio-frequency identification (RFID) devices -- or "talking bar codes" -- amount to miniature antennas that transmit the types of information that might otherwise be held on a swipe card. Even if you've shrugged through the debates about warrantless wiretapping and said "what the heck" at the prospect that everything from your spending habits to your Web site travels are being compiled and crunched for commercial purposes, you might think twice about letting your employer insert a microchip under your skin as a condition of getting a job. As of today, it is both a technical and a legal possibility. Just last year, a ... provider of video-surveillance equipment inserted ... microchips into the arms of two employees. Those two workers volunteered, but it's not hard to imagine the lightbulbs going off in Corporate America. Is Joe really making a sales call or is he taking in a baseball game at AT&T Park? How many smoke breaks is Mary taking? Amazingly, there is no California law against "chipping" workers as a condition of employment.
Note: For many reliable reports from the major media on the potential dangers of microchips, click here.
The Bush administration rushed to defend new espionage legislation Monday amid growing concern that the changes could lead to increased spying by U.S. intelligence agencies on American citizens. But officials declined to provide details about how the new capabilities might be used by the National Security Agency and other spy services. And in many cases, they could point only to internal monitoring mechanisms to prevent abuse of the new rules that appear to give the government greater authority to tap into the traffic flowing across U.S. telecommunications networks. Officials rejected assertions that the new capabilities would enable the government to cast electronic "drift nets" that might ensnare U.S. citizens [and] that the new legislation would amount to the expansion of a controversial and critics contend unconstitutional warrantless wiretapping program that President Bush authorized after the 9/11 attacks. Intelligence experts said there were an array of provisions in the new legislation that appeared to make it possible for the government to engage in intelligence-collection activities that the Bush administration officials were discounting. "They are trying to shift the terms of the debate to their intentions and away from the meaning of the new law," said Steven Aftergood, an intelligence policy analyst at the Federation of American Scientists. "The new law gives them authority to do far more than simply surveil foreign communications abroad," he said. "It expands the surveillance program beyond terrorism to encompass foreign intelligence. It permits the monitoring of communications of a U.S. person as long as he or she is not the primary target. And it effectively removes judicial supervision of the surveillance process."
The FBI is taking cues from the CIA to recruit thousands of covert informants in the United States as part of a sprawling effort to boost its intelligence capabilities. According to a recent unclassified report to Congress, the FBI expects its informants to provide secrets about possible terrorists and foreign spies, although some may also be expected to aid with criminal investigations, in the tradition of law enforcement confidential informants. The FBI said the push was driven by a 2004 directive from President Bush ordering the bureau to improve its counterterrorism efforts by boosting its human intelligence capabilities. The aggressive push for more secret informants appears to be part of a new effort to grow its intelligence and counterterrorism efforts. Other recent proposals include expanding its collection and analysis of data on U.S. persons, retaining years' worth of Americans' phone records and even increasing so-called "black bag" secret entry operations. To handle the increase in so-called human sources, the FBI also plans to overhaul its database system, so it can manage records and verify the accuracy of information from "more than 15,000" informants, according to the document. The bureau has arranged to use elements of CIA training to teach FBI agents about "Source Targeting and Development," the report states. The courses will train FBI special agents on the "comprehensive tradecraft" needed to identify, recruit and manage these "confidential human sources."
The arguments against a federal shield law might be frightening if they were not so ludicrous. There are two ways to reassure yourself that legislation to allow journalists to protect the identity of confidential sources will not be exploited by terrorists, thugs, identity thieves, sleazy sleuths and anarchists who expose trade secrets. One is to look at the experience of 49 state laws that grant varying levels of protection for journalists using anonymous sources. The other is to read the bill. "The Free Flow of Information Act of 2007,'' sponsored by Reps. Mike Pence, R-Ind., and Rick Boucher, D-Va., does not provide an absolute right for journalists to protect their sources. Under their HR2102, a journalist could be forced by the courts to reveal his or her source if the disclosure involved: -- A threat to national security. -- A threat of imminent death or significant [bodily] harm to a person. -- A trade secret of significant value. -- Personal financial or health information. [The] Justice Department, which has wielded subpoenas and threats of jail time against journalists in pursuing government leaks, has never liked the idea of a shield law. So it was hardly a surprise when it recently testified against HR2102. What was eye-poppingly outrageous was a Justice official's straight-faced attempt to suggest that criminals or terrorists would invoke the bill's protection for journalists to thwart prosecutors. "Totally absurd," House Judiciary Chairman John Conyers, D-Mich., said of the terrorism argument. However, the dangers that overzealous prosecutors pose to a free and independent press that Pence calls "essential to an informed" electorate are very real and growing. As Pence put it, "there may never be another Deep Throat" if whistle-blowers become worried that journalists cannot keep a promise of confidentiality.
There is increasing military interest in the development of techniques that can survey and possibly manipulate the mental processes of potential enemies, or enhance the potential of one's own troops. There is nothing new about such an interest. In the US, it stretches back at least half a century. Impressed by claims that the Soviet Union was developing psychological warfare, the CIA and the Defence Advanced Projects Agency (Darpa) began their own programmes. Early experiments included the clandestine feeding of LSD to their own operatives and attempts at 'brain-washing'. By the 1960s, Darpa, along with the US Navy, was funding almost all US research into 'artificial intelligence', in order to develop methods and technologies for the 'automated battlefield' and the 'intelligent soldier'. Contracts were let and patents taken out on techniques aimed at recording signals from the brains of enemy personnel at a distance, in order to 'read their minds'. These efforts have burgeoned in the aftermath of the so-called 'war on terror'. The step beyond reading thoughts is to attempt to control them directly. A new technique - transcranial magnetic stimulation (TMS) - has begun to generate interest. This focuses an intense magnetic field on specific brain regions, and has been shown to affect thoughts, perceptions and behaviour.
Note: These technologies are far more developed than this article suggests. For reliable, verifiable information on these little-known "non-lethal" weapons: http://www.WantToKnow.info/mindcontrol10pg#nonlethal
The Department of Homeland Security is gathering intelligence from paid undercover informants inside the migrant caravan that is now reaching the California-Mexico border as well as monitoring the text messages of migrants, according to two DHS officials. The 4,000 migrants, mainly from Honduras, have used WhatsApp text message groups as a way to organize and communicate along their journey to the California border, and DHS personnel have joined those groups to gather that information. The intelligence gathering techniques are combined with reports from DHS personnel working in Mexico. Paying informants, placing officers in the region or monitoring the communications of non-U.S. citizens is not illegal, said John Cohen, former acting undersecretary of intelligence for DHS, but it does raise some concerns about the allocation of resources. "Those resources have to come from some place. They are not being devoted to thwarting terrorist threats, mass shootings, mailed fentanyl coming into the country or cyberattacks," said Cohen. Cohen said the caravan presents a logistical and humanitarian issue, but because the vast majority of its members want to present themselves legally to claim asylum, it is not wise to devote a significant amount of intelligence resources to it. "I find it hard to believe that the highest risk facing this nation comes from this caravan," Cohen said.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
Officials seized Trump protesters cell phones, cracked their passwords, and are now attempting to use the contents to convict them of conspiracy to riot at the presidential inauguration. Prosecutors have indicted over 200 people on felony riot charges for protests in Washington, D.C. on January 20. Some defendants face up to 75 years in prison. Evidence against the defendants has been scant from the moment of their arrest. As demonstrators, journalists, and observers marched through the city, D.C. police officers channelled hundreds of people into a narrow, blockaded corner, where they carried out mass arrests. Some of those people ... are now suing for wrongful arrest. Police also seized more than 100 cell phones. All of the ... phones were locked. But a July 21 court document shows that investigators were successful in opening the locked phones. Prosecutors moved to use a wealth of information from the phones as evidence, including the phones call detail records, SMS or MMS messages, contact logs/email logs, chats or other messaging applications, website search history and website history, and images or videos. One of the more than 200 defendants has pleaded guilty to riot charges after being named extensively in a superseding indictment. But the case against most defendants is less clear; in the superseding indictment, prosecutors accuse hundreds defendants of conspiracy to riot, based on overt acts as banal as chanting anti-capitalist slogans or wearing dark clothing.
Note: In May, United Nations officials said that the US treatment of activists was increasingly "incompatible with US obligations under international human rights law". For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the erosion of civil liberties.
The days leading up to last Fridays release of director Oliver Stones Snowden looked like one long movie trailer. The American Civil Liberties Union ... announced a campaign to win a presidential pardon for Edward Snowden, the former National Security Agency contract employee who leaked hundreds of thousands of its highly classified documents. The next day, the House Intelligence Committee released a bipartisan letter to the president that advised him against any pardon. The week before, Stone had invited me to a private screening of his movie, [along with] a small group of former government employees who were whistleblowers before Snowden and paid a high price for it. The reason they had been persecuted is that U.S. law makes no distinction between revealing illegal government activity to the press about eavesdropping on Americans or engaging in torture, and betraying the country by passing secrets for money or ideology to foreign governments. The Espionage Act was enacted nearly a century ago following World War One, and has already been amended several times. One key issue confronting the next president ... is whether the law needs to be amended again this time to separate the whistleblowers from the spies. Today ... the battle lines have been drawn between those in government both the executive branch and Congress who view the theft of government secrets as espionage, regardless of the motive, and those in civil-liberties groups and the media who see motive as a critical distinction.
Note: The above was written by James Bamford, whistleblower and author of "The Shadow Factory: The Ultra-Secret NSA From 9/11 to the Eavesdropping on America." For more along these lines, see concise summaries of deeply revealing intelligence agency corruption news articles from reliable major media sources.
Canada's electronic spy agency broke privacy laws by sharing information about Canadians with foreign partners, a federal watchdog said Thursday. Commissioner Jean-Pierre Plouffe said in his annual report that the Communications Security Establishment passed along information known as metadata to counterparts in the United States, Britain, Australia and New Zealand. Metadata is information associated with a communication, such as a telephone number or email address, but not the message itself. The communications agency intercepts and analyzes foreign communications for intelligence information of interest to the federal government. The agency is legally authorized to collect and analyze metadata churning through cyberspace. Plouffe, who keeps an eye on the highly secretive agency, said he found that it lacks clarity regarding the sharing of certain types of metadata. Defense Minister Harjit Sajjan said the sharing won't resume until he is satisfied that the proper protections are in place. Plouffe's report noted that certain metadata was not being properly minimized, or rendered unidentifiable, prior to being shared. The CSE's failure to strip out certain Canadian identity information violated the National Defense Act and therefore the federal Privacy Act as well. Privacy advocates have stressed that metadata is far from innocuous since it can reveal a great deal about a person's online behavior and interactions.
Note: Many countries do not allow their intelligence agencies to spy on their own citizens without going through a legal process. The easy way around this that has been used for decades is to simply getting the information from a friendly country. So if the CIA wants information on you in the US, they can't spy directly, but they can ask the UK to do so and pass the information to them and thus get around the laws. For more along these lines, see concise summaries of deeply revealing intelligence agency corruption news articles from reliable major media sources.
The widespread surveillance of Spanish citizens by the US National Security Agency, which caused outrage when it was reported this week, was the product of a collaboration with Spain's intelligence services, according to one Spanish newspaper. Spanish agents not only knew about the work of the NSA but also facilitated it, El Mundo reports. An NSA document entitled "Sharing computer network operations cryptologic information with foreign partners" reportedly shows how the US relies on the collaboration of many countries to give it access to intelligence information, including electronic metadata. According to the document seen by El Mundo, the US classifies cooperation with various countries on four different levels. In the first group "Comprehensive Cooperation" are the UK, Australia, Canada and New Zealand. The second group "Focused Cooperation" of which Spain is a member, includes 19 countries, all of them European, apart from Japan and South Korea. The third group "Limited cooperation" consists of countries such as France, Israel, India and Pakistan; while the fourth "Exceptional Cooperation" is made up of countries that the US considers to be hostile to its interests. The NSA documents [suggest] the Spanish intelligence services were working hand in hand with the NSA, as were other foreign agencies. But if there was any doubt as to who held the upper hand, the NSA documents make clear that any collaboration was always to serve the needs of protecting American interests.
Note: For more on the realities of intelligence agency activities, see the deeply revealing reports from reliable major media sources available here.
The faces of more than 120 million people are in searchable photo databases that state officials assembled to prevent drivers-license fraud but that increasingly are used by police to identify suspects, accomplices and even innocent bystanders in a wide range of criminal investigations. The facial databases have grown rapidly in recent years and generally operate with few legal safeguards beyond the requirement that searches are conducted for law enforcement purposes. The most widely used systems were honed on the battlefields of Afghanistan and Iraq as soldiers sought to identify insurgents. The increasingly widespread deployment of the technology in the United States has helped police [identify people who] leave behind images on surveillance videos or social-media sites that can be compared against official photo databases. But law enforcement use of such facial searches is blurring the traditional boundaries between criminal and non-criminal databases, putting images of people never arrested in what amount to perpetual digital lineups. Though not yet as reliable as fingerprints, these technologies can help determine identity through individual variations in irises, skin textures, vein patterns, palm prints and a persons gait while walking. Facial-recognition systems ... can be deployed remotely, without subjects knowing that their faces have been captured.
Note: For deeply revealing reports from reliable major media sources on government assaults on privacy, click here.
Somewhere, a US government official is reading through a list of those who sent or received an email from Jacob Appelbaum, a 28-year-old computer science researcher at the University of Washington who volunteered for WikiLeaks. Among those listed will be my name, a journalist who interviewed Appelbaum for a book about the digital revolution. Appelbaum is a spokesman for Tor, a free internet anonymising software that helps people defend themselves against internet surveillance. He's spent five years teaching activists around the world how to install and use the service to avoid being monitored by repressive governments. Now, Appelbaum finds himself a target of his own government as a result of his friendship with Julian Assange and the fact WikiLeaks used the Tor software. Appelbaum has not been charged with any wrongdoing; nor has the government shown probable cause that he is guilty of any criminal offence. That matters not a jot, because, as the law stands, government officials don't need a search warrant to access our digital data. Searching someone's home requires a warrant that can only be obtained by proving probable cause, but digital searches require no such burden of proof. Most people are not aware of the ease with which governments free, open and so-called democratic can access and peruse our private communications.
Note: For key reports on government threats to privacy from major media sources, click here.
Former Minnesota Gov. Jesse Ventura is suing the Department of Homeland Security and the Transportation Security Administration, saying full-body scans and pat-downs at airport checkpoints are violating his rights. Ventura filed his lawsuit [on January 24] in federal court in Minnesota. He says the new security measures violate his right to be free from unreasonable searches and seizures. He's asking a federal court to order officials to stop subjecting him to these searches. Ventura was governor of Minnesota from 1999 through 2002. He now hosts the television program "Conspiracy Theory." The lawsuit says Ventura had a hip replacement in 2008, and his titanium implant sets off metal detectors.
Note: Jesse Ventura is one of the heros of our time. Do a video search on his name to watch episodes of his amazingly revealing "Conspiracy Theory" programs.
Everyone who buys a mobile telephone will be forced to register their identity on a national database under government plans to extend massively the powers of state surveillance. Phone buyers would have to present a passport or other official form of identification at the point of purchase. Privacy campaigners fear it marks the latest government move to create a surveillance society. A compulsory national register for the owners of all 72m mobile phones in Britain would be part of a much bigger database. Whitehall officials have raised the idea of a register containing the names and addresses of everyone who buys a phone in recent talks with Vodafone and other telephone companies, insiders say. The move is targeted at monitoring the owners of Britains estimated 40m prepaid mobile phones. They can be purchased with cash by customers who do not wish to give their names, addresses or credit card details. The pay-as-you-go phones are popular with criminals ... because their anonymity shields their activities from the authorities. But they are also used by thousands of law-abiding citizens who wish to communicate in private. The move aims to close a loophole in plans being drawn up by GCHQ, the governments eavesdropping centre in Cheltenham, to create a huge database to monitor and store the internet browsing habits, e-mail and telephone records of everyone in Britain.
Note: For many disturbing reports on increasing threats to privacy, click here.
A privacy group filed a class-action lawsuit on Thursday against the National Security Agency, President Bush and other officials, seeking to halt what it describes as illegal surveillance of Americans telephone and Internet traffic. The lawsuit parallels a legal action brought against the AT&T Corporation in 2006 by the same nonprofit group, the Electronic Frontier Foundation, charging that the company gave the N.S.A. access to its communications lines and customer records without proper warrants. Congress derailed that lawsuit this year by passing legislation granting immunity to telecommunications companies that had provided assistance to the agency, though the foundation has said it intends to challenge the constitutionality of the new law. A lawyer with the foundation, Kevin S. Bankston, said the new suit opened a second front against a massively illegal fishing expedition through AT&Ts domestic networks and databases of customer records. When Mr. Bush started the program in late 2001, the N.S.A. began eavesdropping inside the United States without court warrants for the first time since 1978, when Congress created the Foreign Intelligence Surveillance Court to oversee such intelligence collection. The suits plaintiffs are five AT&T customers, but it is filed on behalf of all customers. Like the 2006 suit, it is based in part on information from Mark Klein, a former AT&T technician who says he saw what he believed to be equipment installed by the N.S.A. at a company communications hub in San Francisco allowing the agency to filter a huge volume of Internet traffic.
Note: For many disturbing reports from major media sources of threats to privacy, click here.
The Big Apple is turning into Big Brother, civil liberties groups have warned in response to a new plan from New York city's police chiefs to photograph every vehicle entering Manhattan and hold the details on a massive database. As well as placing cameras at all tunnels and bridges into Manhattan, the 36-page plan, called Operation Sentinel, calls for a security ring to be erected at Ground Zero and for a 50-mile buffer zone around the city within which mobile units would search for nuclear or "dirty" bombs. [The] 3,000 cameras that could be mounted as a result of the plans of the New York police ... have provoked outrage in the United States. Donna Lieberman, director of the New York Civil Liberties Union, said the idea of tracking the movements of millions of people was "an assault on the country's historical respect for the right to privacy and the freedom to be left alone". The NYCLU is pressing the New York police to release further details of its intentions under freedom of information laws. The toughest element of the scheme relates to preparations to secure Ground Zero once the six-hectare site is rebuilt and open to the public again. Those measures include moveable roadblocks, security cameras across lower Manhattan and an underground bomb-screening centre through which all delivery vehicles would have to pass. The plan to video the number plates of every vehicle would be applied to all points of entry into Manhattan, including the main Brooklyn-Battery, Holland, Lincoln and Midtown tunnels and Brooklyn, Manhattan and other bridges.
Note: For lots more on threats to privacy from major media sources, click here.
The Bush administration said yesterday that it plans to start using the nation's most advanced spy technology for domestic purposes soon, rebuffing challenges by House Democrats over the idea's legal authority. Homeland Security Secretary Michael Chertoff said his department will activate his department's new domestic satellite surveillance office in stages, starting as soon as possible. Sophisticated overhead sensor data will be used for law enforcement once privacy and civil rights concerns are resolved, he said. His statements marked a fresh determination to operate the department's new National Applications Office. But Congress delayed launch of the new office last October. Critics cited its potential to expand the role of military assets in domestic law enforcement, to turn new or as-yet-undeveloped technologies against Americans without adequate public debate, and to divert the existing civilian and scientific focus of some satellite work to security uses. Democrats say Chertoff has not spelled out what federal laws govern the NAO, whose funding and size are classified. Congress barred Homeland Security from funding the office until its investigators could review the office's operating procedures and safeguards. The department submitted answers on Thursday, but some lawmakers promptly said the response was inadequate. [Rep. Bennie G. Thompson (D-Miss.), chairman of the House Homeland Security Committee] said, "We still don't know whether the NAO will pass constitutional muster since no legal framework has been provided."
Note: For many more revealing stories on threats to civil liberties, click here.
Today, more than 23,000 representatives of private industry are working quietly with the FBI and the Department of Homeland Security. The members of this rapidly growing group, called InfraGard, receive secret warnings of terrorist threats before the public does -- and, at least on one occasion, before elected officials. In return, they provide information to the government, which alarms the ACLU. But there may be more to it than that. One business executive, who showed me his InfraGard card, told me they have permission to "shoot to kill" in the event of martial law. In November 2001, InfraGard had around 1,700 members. As of late January, InfraGard had 23,682 members, according to its website, www.infragard.net, which adds that "350 of our nation's Fortune 500 have a representative in InfraGard." FBI Director Robert Mueller addressed an InfraGard convention on August 9, 2005. He urged InfraGard members to contact the FBI if they "note suspicious activity or an unusual event." And he said they could sic the FBI on "disgruntled employees who will use knowledge gained on the job against their employers."
Note: We don't normally use Common Dreams as a news source, but as this news is so important and the major media failed to report it, we decided to include this article here. For a revealing report by the ACLU on this key topic, click here. For important reports from major media sources on threats to civil liberties, click here.
U.S. intelligence officials are [now claiming] that popular Internet services that enable computer users to adopt cartoon-like personas in three-dimensional online spaces also are creating security vulnerabilities by opening novel ways ... to move money, organize and conduct corporate espionage. Over the last few years, "virtual worlds" such as Second Life and other role-playing games have become home to millions of computer-generated personas known as avatars. By directing their avatars, people can take on alternate personalities, socialize, explore and earn and spend money across uncharted online landscapes. Nascent economies have sprung to life in these 3-D worlds, complete with currency, banks and shopping malls. Corporations and government agencies have opened animated virtual offices, and a growing number of organizations hold meetings where avatars gather and converse in newly minted conference centers. Intelligence officials ... say they're convinced that the qualities that many computer users find so attractive about virtual worlds -- including anonymity, global access and the expanded ability to make financial transfers outside normal channels -- have turned them into seedbeds for transnational threats. The government's growing concern seems likely to make virtual worlds the next battlefield in the struggle over the proper limits on the government's quest to [expand] data collection and analysis and the surveillance of commercial computer systems. Virtual worlds could also become an actual battlefield. The intelligence community has begun contemplating how to use Second Life and other such communities as platforms for cyber weapons.
An internal Pentagon review this year found systemic problems ... in the militarys efforts to obtain records from American banks and consumer credit agencies in terrorism and espionage investigations, according to Pentagon documents. The newly disclosed documents, totaling more than 1,000 pages, provide additional confirmation of the militarys expanding use of what are known as national security letters under powers claimed under the Patriot Act. The documents show that the military has issued at least 270 of the letters since 2005, and about 500 in all since 2001. The documents were obtained through the Freedom of Information Act by two private advocacy groups, the American Civil Liberties Union and the Electronic Frontier Foundation. The New York Times first disclosed the militarys use of the letters in January, and senior members of Congress and civil liberties groups criticized the practice on grounds that it seemed to conflict with traditional Pentagon rules against domestic law enforcement operations. The documents raise a number of apparent discrepancies between the Defense Departments internal practices and what officials have said publicly and to Congress about their use of the letters. The documents suggest, for instance, that military officials used the F.B.I. to collect records for what started as purely military investigations. And the documents also leave open the possibility that records could be gathered on nonmilitary personnel in the course of the investigations. Civil liberties advocates said recent controversy over the Department of Defenses collection of information on antiwar protesters made them suspicious of the assertion that the letters had been used exclusively to focus on military personnel. We are very skeptical that the D.O.D. is voluntarily limiting its own surveillance power, said Melissa Goodman, a staff attorney for the A.C.L.U..
The nations biggest telecommunications companies, working closely with the White House, have mounted a secretive lobbying campaign to get Congress to quickly approve a measure wiping out all private lawsuits against them for assisting the U.S. intelligence communitys warrantless surveillance programs. The campaign which involves some of Washington's most prominent lobbying and law firms has taken on new urgency in recent weeks because of fears that a U.S. appellate court in San Francisco is poised to rule that the lawsuits should be allowed to proceed. If that happens, the telecom companies say, they may be forced to terminate their cooperation with the U.S. intelligence community or risk potentially crippling damage awards for allegedly turning over personal information about their customers to the government without a judicial warrant. But critics say the language proposed by the White House drafted in close cooperation with the industry officials is so extraordinarily broad that it would provide retroactive immunity for all past telecom actions related to the surveillance program. Its practical effect, they argue, would be to shut down any independent judicial or state inquires into how the companies have assisted the government in eavesdropping on the telephone calls and e-mails of U.S. residents in the aftermath of the September 11 terror attacks. Its clear the goal is to kill our case," said Cindy Cohn, legal director of the Electronic Frontier Foundation, [which] filed the main lawsuit against the telecoms after The New York Times first disclosed, in December 2005, that President Bush had approved a secret program to monitor the phone conversations of U.S. residents without first seeking judicial warrants. I find it a little shocking that Congress would participate in the covering up of what has been going on," added Cohn.
At least 20,000 police surveillance cameras are being installed along streets here [in Shenzhen] in southern China and will soon be guided by sophisticated computer software from an American-financed company to recognize automatically the faces of police suspects and detect unusual activity. Starting this month in a port neighborhood and then spreading across Shenzhen, a city of 12.4 million people, residency cards fitted with powerful computer chips programmed by the same company will be issued to most citizens. Data on the chip will include not just the citizens name and address but also work history, educational background, religion, ethnicity, police record, medical insurance status and landlords phone number. Even personal reproductive history will be included, for enforcement of Chinas controversial one child policy. Plans are being studied to add credit histories, subway travel payments and small purchases charged to the card. Security experts describe Chinas plans as the worlds largest effort to meld cutting-edge computer technology with police work to track the activities of a population. But they say the technology can be used to violate civil rights. We have a very good relationship with U.S. companies like I.B.M., Cisco, H.P., Dell, said Robin Huang, the chief operating officer of China Public Security. All of these U.S. companies work with us to build our system together. The role of American companies in helping Chinese security forces has periodically been controversial in the United States. Executives from Yahoo, Google, Microsoft and Cisco Systems testified in February 2006 at a Congressional hearing called to review whether they had deliberately designed their systems to help the Chinese state muzzle dissidents on the Internet; they denied having done so.
An internal FBI audit has found that the bureau potentially violated the law or agency rules more than 1,000 times while collecting data about domestic phone calls, e-mails and financial transactions in recent years, far more than was documented in a Justice Department report in March that ignited bipartisan congressional criticism. The new audit covers just 10 percent of the bureau's national security investigations since 2002. The vast majority of the new violations were instances in which telephone companies and Internet providers gave agents phone and e-mail records the agents did not request and were not authorized to collect. The agents retained the information anyway in their files. Two dozen of the newly-discovered violations involved agents' requests for information that U.S. law did not allow them to have. The results confirmed what ... critics feared, namely that many agents did not ... follow the required legal procedures and paperwork requirements when collecting personal information with one of the most sensitive and powerful intelligence-gathering tools of the post-Sept. 11 era -- the National Security Letter, or NSL. Such letters are uniformly secret and amount to nonnegotiable demands for personal information -- demands that are not reviewed in advance by a judge. After the 2001 terrorist attacks, Congress substantially eased the rules for issuing NSLs, [leading] to an explosive growth in the use of the letters. More than 19,000 such letters were issued in 2005 seeking 47,000 pieces of information, mostly from telecommunications companies.
The federal government sued the New Jersey attorney general and other state officials Wednesday to stop them from seeking information about telephone companies' cooperation with the National Security Agency. The unusual filing...is the latest effort by federal authorities to halt legal proceedings aimed at revealing whether and how often AT&T, Verizon and other phone companies have provided customer records to the NSA without a court order. New Jersey Attorney General Zulima Farber, a Democrat, and other officials sent subpoenas to five carriers on May 17, asking for documents that would explain whether they supplied customer records to the NSA, the lawsuit said. The subpoenas followed by a few days a USA Today report that the phone companies had complied with the secretive agency's request for the phone records of millions of ordinary Americans after the Sept. 11 attacks. The Justice Department said more than 20 lawsuits have been filed around the country alleging that the phone companies illegally assisted the NSA. The government says sensitive national security information would be revealed if judges allow those cases to proceed. In this matter, the federal government said the New Jersey officials are treading on federal turf and that the companies, if forced to comply with the subpoenas, would be confirming or denying the existence of the program. President Bush and other top federal officials have refused to do that.
The Defense Department began working yesterday with a private marketing firm to create a database of high school students ages 16 to 18 and all college students to help the military identify potential recruits. The program is provoking a furor among privacy advocates. The new database will include personal information including birth dates, Social Security numbers, e-mail addresses, grade-point averages, ethnicity and what subjects the students are studying. "The purpose of the system is to provide a single central facility within the Department of Defense to compile, process and distribute files of individuals who meet age and minimum school requirements for military service." Some information on high school students already is given to military recruiters in a separate program under provisions of the 2002 No Child Left Behind Act. Recruiters have been using the information to contact students at home, angering some parents and school districts around the country.
The U.S. government can monitor journalists under a foreign intelligence law that allows invasive spying and operates outside the traditional court system, according to newly released documents. Targeting members of the press under the law, known as the Foreign Intelligence Surveillance Act, requires approval from the Justice Departments highest-ranking officials. Prior to the release of these documents, little was known about the use of FISA court orders against journalists. Previous attention had been focused on the use of National Security Letters against members of the press; the letters are administrative orders with which the FBI can obtain certain ... records without a judges oversight. FISA court orders can authorize much more invasive searches and collection, including the content of communications, and do so through hearings conducted in secret and outside the sort of ... judicial process that allows journalists and other targets of regular criminal warrants to eventually challenge their validity. The rules apply to media entities or journalists who are thought to be agents of a foreign government, or ... possess foreign intelligence information. Theres a lack of clarity on the circumstances when the government might consider a journalist an agent of a foreign power, said [Knight Institute staff attorney Ramya] Krishnan. Think about WikiLeaks; the government has said they are an intelligence operation.
Note: In its latest instruction manual for federal prosecutors, the US Justice Department removed a subsection titled Need for Free Press and Public Trial. For more along these lines, see concise summaries of deeply revealing news articles on judicial system corruption and the erosion of civil liberties.
Edward Snowden has no regrets five years on from leaking the biggest cache of top-secret documents in history. He is wanted by the US. He is in exile in Russia. But he is satisfied with the way his revelations of mass surveillance have rocked governments, intelligence agencies and major internet companies. What has happened in the five years since? The most important change, he said, was public awareness. The government and corporate sector preyed on our ignorance. But now we know. People are aware now. People are still powerless to stop it but we are trying. The revelations made the fight more even. He said he had no regrets. His own life is uncertain, perhaps now more than ever, he said. His sanctuary in Russia depends on the whims of the Putin government, and the US and UK intelligence agencies have not forgiven him. For them, the issue is as raw as ever. One of the disclosures to have most impact was around the extent of collaboration between the intelligence agencies and internet companies. In 2013, the US companies were outsmarting the EU in negotiations over data protection. Snowden landed like a bomb in the middle of the negotiations and the data protection law that took effect last month is a consequence. But he will not be marking the anniversary with a victory lap. There is still much to be done. The fightback is just beginning, said Snowden. The governments and the corporates have been in this game a long time and we are just getting started.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
Two Stanford University researchers have reported startling accuracy in predicting sexual orientation using computer technology. Dr. Michal Kosinski and Yilun Wang, whose research will be published by the Journal of Personality and Social Psychology, say that AI can distinguish between the face of a heterosexual man and a homosexual man in 81 percent of cases. For women, the predictive accuracy is 71 percent. The average human is less adept at identifying between straight and gay people purely based on an image: We are only able to guess correctly in 61 percent of cases for men and 54 percent for women. When scientists presented the algorithm with five facial images of a single person, the accuracy increased to 91 percent for men and 83 percent for women. Kosinski and Wang used deep neural networks to sample 35,326 facial images of men and women taken from a dating website. The findings advance discussion about the biological factors that may determine ones sexual orientation. However, Kosinski tells The Economist, the research is not intended to be used to profile or out homosexual men and women. Rather, it is designed to demonstrate - or even warn - that technological advances can be used for such means and could pose a threat to our privacy, given that digital information is so easily accessible. The researchers argue the digitalization of our lives and rapid progress in AI continues to erode the privacy of sexual orientation and other intimate traits.
Note: Emerging artificial intelligence technologies are currently being developed for use in warfare. According to a United Nations report, misuse of these technologies may threaten human rights. For more along these lines, see concise summaries of deeply revealing privacy news articles from reliable major media sources.
Google processes more than three billion search queries a day. It has altered our notions of privacy, tracking what we buy, what we search for online - and even our physical location at every moment of the day. It is a monopoly. So it matters how this company works - who it hires, who it fires and why. Last week, Google fired a software engineer for writing a memo that questioned the companys gender diversity policies and made statements about womens biological suitability for technical jobs. Portions of the memo violate our code of conduct and cross the line by advancing harmful gender stereotypes, Googles chief executive, Sundar Pichai, wrote. Its impossible to believe that Google or other large tech companies a few years ago would have reacted like this to such a memo. In 2011 when CNN filed a Freedom of Information Act request for the workplace diversity data on big tech companies, Google [asked] for its data to be excluded. Google began to disclose statistics [in 2014] showing that only 17 percent of its technical work force was female. Today Google is under growing scrutiny, and the cognitive dissonance between the outward-facing Dont be evil stance and the internal misogynistic brogrammer rhetoric was too extreme. Google had to fire the offending engineer, James Damore, but anyone who spends time on the message boards frequented by Valley engineers will know that the bro culture that gave us Gamergate - an online movement that targeted women in the video game industry - [remains] prevalent.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the erosion of privacy.
Some of the most powerful espionage tools created by the National Security Agencys elite group of hackers have been revealed in recent days. A cache of hacking tools with code names such as Epicbanana, Buzzdirection and Egregiousblunder appeared mysteriously online over the weekend, setting the security world abuzz with speculation over whether the material was legitimate. The file appeared to be real, according to former NSA personnel who worked in the agencys hacking division, known as Tailored Access Operations (TAO). The exploits are not run-of-the-mill tools to target everyday individuals. They are expensive software used to take over firewalls, such as Cisco and Fortinet, that are used in the largest and most critical commercial, educational and government agencies around the world, said [former TAO operator] Blake Darche. Some former agency employees suspect that the leak was the result of a mistake by an NSA operator, rather than a successful hack by a foreign government of the agencys infrastructure. It is not unprecedented for a TAO operator to accidentally upload a large file of tools ... one of the former employees said. Whats unprecedented is to not realize you made a mistake, he said. You would recognize, Oops, I uploaded that set and delete it. Critics of the NSA have suspected that the agency, when it discovers a software vulnerability, frequently does not disclose it, thereby putting at risk the cybersecurity of anyone using that product.
Note: Former US Senator Frank Church warned of the dangers of creating a surveillance state in 1975. By 2013, it had become evident that the US did not heed his warning. For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
A treason investigation into two journalists who reported that the German state planned to increase online surveillance has been suspended by the countrys prosecutor general following protests by leading voices across politics and media. Harald Range, Germanys prosecutor general, said on Friday he was halting the investigation for the good of press and media freedom. It was the first time in more than half a century that journalists in Germany had faced charges of treason. His announcement followed a deluge of criticism and accusations that Germanys prosecutor had misplaced priorities, having failed to investigate with any conviction the NSA spying scandal revealed by whistleblower Edward Snowden, and targeting instead the two investigative journalists, Markus Beckedahl and Andre Meister. The two reporters made reference to what is believed to be a genuine intelligence report that had been classified as confidential, which proposed establishing a new intelligence department to monitor the internet, in particular social media networks. Beckedahl hit out at the prosecutors investigation against him on Friday on the state broadcaster Deutschlandfunk, calling it absurd and suggesting it was meant as a general warning to scare sources from speaking to journalists. Much of the German media called the decision an attack on the freedom of the press.
Note: The NSA recently got caught spying on German reporters, possibly as a favor to the German government. For more along these lines, see concise summaries of deeply revealing news articles about corruption in the intelligence community and the manipulation of public perception.
NPRs David Folkenflik has a revealing new look at ... one of the most important journalistic stories of the last decade: The New York Times 2004 decision ... to suppress for 15 months (through Bushs re-election) its reporters discovery that the NSA was illegally eavesdropping on Americans without warrants. This episode was one significant reason Edward Snowden purposely excluded the Times from his massive trove of documents. In an interview with Folkenflik, the papers new executive editor, Dean Baquet, describes the papers exclusion from the Snowden story as really painful. But ... Baquet has his own checkered history in suppressing plainly newsworthy stories at the governments request, including a particularly inexcusable 2007 decision, when he was the managing editor of The Los Angeles Times, to kill a story based on AT&T whistleblower Mark Kleins revelations that the NSA had built secret rooms at AT&T to siphon massive amounts of domestic telephone traffic. In his NPR interview, Baquet insists that he has had a serious change of heart on such questions as a result of the last year of NSA revelations: "[Baquet] says the experience has proved that news executives are often unduly deferential to seemingly authoritative warnings unaccompanied by hard evidence." Dean Baquets epiphany about the U.S. government and the American media ... is long overdue, but better late than never. Let us hope that it signals an actual change in behavior.
Note: For more on this, see concise summaries of deeply revealing media corruption news articles from reliable major media sources.
To have a genuinely constructive debate, data must be compiled, evidence must be amassed and verifiable truths must be presented. This truism is particularly significant when it comes to debates about security and liberty. Without facts, we get the counterproductive discourse we are being treated to right now - the one hijacked by National Security Administration defenders throwing temper tantrums, tossing out fear-mongering platitudes and trying to prevent any scrutiny of the agency. Tune into a national news program and you inevitably will hear pundits who have spent the last decade mindlessly cheering on wars and warrantless wiretapping now echoing the talking points emanating from surveillance-state apparatchiks like Reps. Mike Rogers, R-Mich., and Dutch Ruppersberger, D-Md. This week, these two lawmakers, who head the House Intelligence Committee, summarized all the bluster in a press release that should be enshrined for posterity. In an attempt to defend the NSA, the bipartisan duo breathlessly claimed that whistle-blower Edward Snowden ended up "endangering each and every American" by exposing the government's mass surveillance (i.e., metadata) programs. They indicted Snowden's patriotism and said his disclosures of the NSA's unlawful and unconstitutional programs "aligned him with our enemy." But the facts now leaking out of the government's national security apparatus are doing the opposite. They are debunking - rather than confirming - the NSA defenders' platitudes.
Note: For more on government surveillance, see the deeply revealing reports from reliable major media sources available here.
The federal government is making progress on developing a surveillance system that would pair computers with video cameras to scan crowds and automatically identify people by their faces, according to newly disclosed documents and interviews with researchers working on the project. The Department of Homeland Security tested a crowd-scanning project called the Biometric Optical Surveillance System or BOSS last fall after two years of government-financed development. Although the system is not ready for use, researchers say they are making significant advances. That alarms privacy advocates, who say that now is the time for the government to establish oversight rules and limits on how it will someday be used. In a sign of how the use of such technologies can be developed for one use but then expanded to another, the BOSS research began as an effort to help the military detect potential suicide bombers. But in 2010, the effort was transferred to the Department of Homeland Security to be developed for use instead by the police in the United States. The effort to build the BOSS system involved a two-year, $5.2 million federal contract given to Electronic Warfare Associates, a Washington-area military contractor with a branch office in Kentucky. Significant progress is already being made in automated face recognition using photographs taken under ideal conditions, like passport pictures and mug shots. The Federal Bureau of Investigation is spending $1 billion to roll out a Next Generation Identification system that will provide a national mug shot database to help local police departments verify identities.
Note: For more on government and corporate threats to privacy, see the deeply revealing reports from reliable major media sources available here.
This Reuters article ... purports to summarize an interview I gave to the daily newspaper La Nacion of Argentina. Like everything in the matter of these NSA leaks, this interview is being wildly distorted to attract attention away from the revelations themselves. I made three points in this La Nacion interview, all of which are true: 1) The oft-repeated claim that Snowden's intent is to harm the US is completely negated by the reality that he has all sorts of documents that could quickly and seriously harm the US if disclosed, yet he has published none of those. When he gave us the documents he provided, he repeatedly insisted that we exercise rigorous journalistic judgment in deciding which documents should be published in the public interest and which ones should be concealed on the ground that the harm of publication outweighs the public value. 2) The US government has acted with wild irrationality. The current criticism of Snowden is that he's in Russia. But the reason he's in Russia isn't that he chose to be there. It's because the US blocked him from leaving: first by revoking his passport (with no due process or trial), then by pressuring its allies to deny airspace rights to any plane they thought might be carrying him to asylum (even one carrying the democratically elected president of a sovereign state), then by bullying small countries out of letting him land for re-fueling. 3) I said that [forcing his plane down] would be completely counter-productive given that ... such an attack could easily result in far more disclosures than allowing us as journalists to vet and responsibly report them, as we've [been] doing.
Note: The above article was written by brave journalist Glenn Greenwald, who broke the Snowden story. For more on the NSA surveillance scandal, see the deeply revealing reports from reliable major media sources available here.
On [July 10] the Washington Post published an article by its long-time reporter Walter Pincus. The article concocted a frenzied and inane conspiracy theory: that it was WikiLeaks and Julian Assange, working in secret with myself [Glenn Greenwald] and Laura Poitras, who masterminded the Snowden leaks ahead of time and directed Snowden's behavior. To peddle this tale, Pincus, in lieu of any evidence, spouted all sorts of accusatory innuendo masquerading as questions ... and invoked classic guilt-by association techniques. See the email I sent Pincus for the conclusive evidence of those factual falsehoods and the other distortions peddled by the Post. Apparently, the Washington Post has decided to weigh in on the ongoing debate over "what is journalism?" with this answer: you fill up articles on topics ... with nothing but idle speculation, rank innuendo, and evidence-free accusations, all under the guise of "just asking questions". You then strongly imply that other journalists who have actually broken a big story are involved in a rampant criminal conspiracy. What was far worse was that Pincus' wild conspiracy theorizing was accomplished only by asserting blatant, easily demonstrated falsehoods. The Post allowed the falsehoods to stand uncorrected all day. More than 8 hours after I first publicized his errors - Pincus emailed me back ... and vowed that a correction would be published. 36 hours after the Post published these falsehoods, 24 hours after I publicized them, and 15 hours after the author of this article acknowledged one of those errors and vowed a correction, the Post article still sits on the internet: uncorrected.
Note: For more on mass media corruption, see the deeply revealing reports from reliable major media sources available here.
Google asked the secretive Foreign Intelligence Surveillance Court on [June 18] to ease long-standing gag orders over data requests the court makes, arguing that the company has a constitutional right to speak about information it is forced to give the government. The legal filing, which invokes the First Amendments guarantee of free speech, is the latest move by the California-based tech giant to protect its reputation in the aftermath of news reports about broad National Security Agency surveillance of Internet traffic. Revelations about the program, called PRISM, have opened fissures between U.S. officials and the involved companies, which have scrambled to reassure their users without violating strict rules against disclosing information that the government has classified as top secret. A high-profile legal showdown might help Googles efforts to portray itself as aggressively resisting government surveillance, and a victory could bolster the companys campaign to portray government surveillance requests as targeted narrowly and affecting only a small number of users. [The] unusual legal move came after days of intense talks between federal officials and several of the technology companies, including Google, over what details can be released. It also comes as the firms increasingly show signs of wanting to outdo each other in demonstrating their commitment to protecting user privacy. Facebook, Microsoft and Yahoo in recent days have won federal government permission to include requests from the court as part of the overall number of data requests they receive from federal, state and local officials.
Note: For deeply revealing reports from reliable major media sources on government assaults on privacy, click here.
Airport body scanners that produce graphic images of travelers' bodies will be removed from checkpoints by June, the Transportation Security Administration says, ending what critics called "virtual strip searches." Passengers will continue to pass through machines that display a generic outline of the human body, raising fewer privacy concerns. The TSA move came after Rapiscan, the manufacturer of the 174 so-called "backscatter" machines, acknowledged it could not meet a congressional-ordered deadline to install privacy software on the machines. "It is big news," said Marc Rotenberg, executive director of the Electronic Privacy Information Center. "It removes the concern that people are being viewed naked by the TSA screener." Currently, the TSA uses the 174 backscatter machines in 30 airports, and has another 76 units in storage. It uses millimeter wave machines in 170 airports. The decision to remove the backscatter machine will make moot, at least temporarily, travelers' concerns about the health effects of the machines. Backscatter machines use X-rays, while millimeter wave machines use radio waves. The TSA has long maintained both machines are safe, but recently signed an agreement with the National Academy of Sciences to study the scanners. The study will continue even though the machines are being pulled, the TSA said, because they could be reintroduced in the future.
Note: Each of those machines cost $175,000. Someone sure made a lot of money on these machines which had a very short lifespan.
University of Reading researcher Mark Gasson has become the first human known to be infected by a computer virus. The virus, infecting a chip implanted in Gasson's hand, passed into a laboratory computer. From there, the infection could have spread into other computer chips found in building access cards. All this was intentional, in an experiment to see how simple radio-frequency identification (RFID) chips like those used for tracking animals can host and spread technological diseases. The research from the British university shows that as implantable bionic devices such as pacemakers get more sophisticated in the years ahead, their security and the safety of the patients whose lives depend on them will become increasingly important, said Gasson. "We should start to think of these devices as miniature computers," Gasson said. And just like everyday computers, they can get sick. "I dont think for us that (infectious technological agents) would be a particularly new concept, but implants in our bodies will make it a lot more real," Gasson told TechNewsDaily. "A denial-of-service attack on a pacemaker, if such a thing were possible, would of course be very detrimental."
Note: For lots more from reliable sources on the dangers of microchip implant technologies, click here.
After a Somali-American teenager from Minneapolis committed a suicide bombing in Africa in October 2008, the Federal Bureau of Investigation began investigating whether a Somali Islamist group had recruited him on United States soil. Instead of collecting information only on people about whom they had a tip or links to the teenager, agents fanned out to scrutinize Somali communities. The operation unfolded as the Bush administration was relaxing some domestic intelligence-gathering rules. The F.B.I.s interpretation of those rules was recently made public when it released, in response to a Freedom of Information lawsuit, its Domestic Investigations and Operations Guide. The disclosure of the manual has opened the widest window yet onto how agents have been given greater power in the post-Sept. 11 era. But the manuals details have alarmed privacy advocates. It raises fundamental questions about whether a domestic intelligence agency can protect civil liberties if they feel they have a right to collect broad personal information about people they dont even suspect of wrongdoing, said Mike German, a former F.B.I. agent who now works for the American Civil Liberties Union. The manual authorizes agents to open an assessment to proactively seek information about whether people or organizations are involved in national security threats. Assessments permit agents to use potentially intrusive techniques, like sending confidential informants to infiltrate organizations and following and photographing targets in public. When selecting targets, agents are permitted to consider political speech or religion as one criterion.
Note: To read the FBI's recently-released and redacted new "Domestic Investigations and Operation Guide", described by the New York Times as giving "F.B.I. agents the most power in national security matters that they have had since the post-Watergate era," click here.
Electronic surveillance and collection of personal data are "pervasive" in British society and threaten to undermine democracy, peers [in the House of Lords] have warned. CCTV cameras and the DNA database were two examples of threats to privacy, the Lords constitution committee said. It called for compensation for people subject to illegal surveillance. Civil liberties campaigners have warned about the risks of a "surveillance society" in which the state acquires ever-greater powers to track people's movements and retain personal data. In its report, the Lords constitution committee said growth in surveillance by both the state and the private sector risked threatening people's right to privacy, which it said was "an essential pre-requisite to the exercise of individual freedom". People were often unaware of the scale of personal information held and exchanged by public bodies, it said. "There can be no justification for this gradual but incessant creep towards every detail about us being recorded and pored over by the state," committee chairman and Tory peer Lord Goodlad said. "The huge rise in surveillance and data collection by the state and other organisations risks undermining the long-standing tradition of privacy and individual freedom which are vital for democracy," Lord Goodlad added. Human rights campaigners Liberty welcomed the report.
Note: For key reports from major media sources on growing threats to privacy from governments and corporations, click here.
This is the year when automated face-recognition finally goes mainstream, and it's about time we considered its social and political implications. Researchers are developing sharply accurate scanners that monitor faces in 3D and software that analyses skin texture to turn tiny wrinkles, blemishes and spots into a numerical formula. The strongest face-recognition algorithms are now considered more accurate than most humans - and already the Home Office and the Association of Chief Police Officers have held discussions about the possibility of linking such systems with automatic car-numberplate recognition and public-transport databases. Join everything together via the internet, and voil - the nation's population, down to the individual Times reader, can be conveniently and automatically monitored in real time. So let's understand this: governments and police are planning to implement increasingly accurate surveillance technologies that are unnoticeable, cheap, pervasive, ubiquitous, and searchable in real time. And private businesses, from bars to workplaces, will also operate such systems, whose data trail may well be sold on or leaked to third parties - let's say, insurance companies that have an interest in knowing about your unhealthy lifestyle, or your ex-spouse who wants evidence that you can afford higher maintenance payments.
Note: For disturbing reports on threats to privacy from major media sources, click here.
The Department of Homeland Security will proceed with the first phase of a controversial satellite-surveillance program, even though an independent review found the department hasn't yet ensured the program will comply with privacy laws. Congress provided partial funding for the program in a little-debated $634 billion spending measure that will fund the government until early March. For the past year, the Bush administration had been fighting Democratic lawmakers over the spy program, known as the National Applications Office. The program is designed to provide federal, state and local officials with extensive access to spy-satellite imagery. Since the department proposed the program a year ago, several Democratic lawmakers have said that turning the spy lens on America could violate Americans' privacy and civil liberties unless adequate safeguards were required. A new [but classified] 60-page Government Accountability Office report said the department "lacks assurance that NAO operations will comply with applicable laws and privacy and civil liberties standards." The report cites gaps in privacy safeguards. The department, it found, lacks controls to prevent improper use of domestic-intelligence data by other agencies and provided insufficient assurance that requests for classified information will be fully reviewed to ensure it can be legally provided. But the bill Congress approved, which President George W. Bush signed into law Tuesday, allows the department to launch a limited version.
Note: For many reports from major media sources of disturbing threats to privacy, click here.
There is apparently no limit to the Bush administrations desire to invade Americans privacy in the name of national security. According to members of Congress, Attorney General Michael Mukasey is preparing to give the F.B.I. broad new authority to investigate Americans without any clear basis for suspicion that they are committing a crime. Opening the door to sweeping investigations of this kind would be an invitation to the government to spy on people based on their race, religion or political activities. Mr. Mukasey has not revealed the new guidelines. But according to senators whose staff have been given limited briefings, the rules may also authorize the F.B.I. to use an array of problematic investigative techniques. Among these are pretext interviews, in which agents do not honestly represent themselves while questioning a subjects neighbors and work colleagues. The F.B.I. has a long history of abusing its authority to spy on domestic groups, including civil rights and anti-war activists, and there is a real danger that the new rules would revive those dark days. Clearly, the Bush administration cannot be trusted to get the balance between law enforcement and civil liberties right. It has repeatedly engaged in improper and illegal domestic spying notably in the National Security Agencys warrantless eavesdropping program. The F.B.I. and the White House no doubt want to push the changes through before a new president is elected. There is no reason to rush to adopt rules that have such important civil liberties implications.
Attorney General Michael Mukasey confirmed plans ... to loosen post-Watergate restrictions on the FBI's national security and criminal investigations. Mukasey said he expected criticism of the new rules because "they expressly authorize the FBI to engage in intelligence collection inside the United States." The Justice Department ... is expected to publicly release the final version within several more weeks. Even then, portions are expected to remain classified for national security reasons. Nonetheless, Mukasey provided enough detail Wednesday to alarm civil libertarians. Michael German, a former veteran FBI agent who is now policy counsel for the American Civil Liberties Union, said if Mukasey moves ahead with the new rules as he describes them, he'll be weakening restrictions originally put in place after the Watergate scandal to rein in the FBI's domestic Counter Intelligence Program, or COINTELPRO. "I'm concerned with the way the attorney general frames the problem," German said. "He talks about 'arbitrary or irrelevant differences' between criminal and national security investigations but these were corrections originally designed to prevent the type of overreach the FBI engaged in for years." German said recent events demonstrated that Mukasey needed to strengthen the FBI's guidelines, not "water them down. ... What the attorney general is doing is expanding the bureau's intelligence collection without addressing the mismanagement within the FBI. If you have an agency collecting more with less oversight, it's only going to get worse."
Note: For many disturbing reports on increasing threats to civil liberties from reliable sources, click here.
Federal agents may take a traveler's laptop computer or other electronic device to an off-site location for an unspecified period of time without any suspicion of wrongdoing, as part of border search policies the Department of Homeland Security recently disclosed. Also, officials may share copies of the laptop's contents with other agencies and private entities for language translation, data decryption or other reasons, according to the policies, dated July 16 and issued by two DHS agencies, U.S. Customs and Border Protection and U.S. Immigration and Customs Enforcement. "The policies . . . are truly alarming," said Sen. Russell Feingold (D-Wis.), who is probing the government's border search practices. He said he intends to introduce legislation soon that would require reasonable suspicion for border searches, as well as prohibit profiling on race, religion or national origin. DHS officials said the newly disclosed policies ... apply to anyone entering the country, including U.S. citizens. Civil liberties and business travel groups have pressed the government to disclose its procedures as an increasing number of international travelers have reported that their laptops, cellphones and other digital devices had been taken -- for months, in at least one case -- and their contents examined. The policies cover "any device capable of storing information in digital or analog form," including hard drives, flash drives, cellphones, iPods, pagers, beepers, and video and audio tapes. They also cover "all papers and other written documentation," including books, pamphlets and "written materials commonly referred to as 'pocket trash' or 'pocket litter.' "
Note: For many reports from reliable, verifiable sources on threats to privacy, click here.
In a development that consumer groups say raises privacy issues, a growing number of hospitals are mining patients' personal financial information to figure out how likely they are to pay their bills. Some hospitals are peering into patients' credit reports, which contain information on people's lines of credit, debts and payment histories. Other hospitals are contracting with outside services that predict a patient's income and whether he or she is likely to walk away from a medical bill. Hospitals often use these services when patients are uninsured or have big out-of-pocket costs despite having health insurance. Consumer advocates say the practice creates the potential for hospitals to misuse the information by denying or cutting back on patients' care if they can't pay. What's more, hospitals could scour a patient's financial records for credit lines and encourage the patient to tap them, despite high interest rates or other costs. "It has the potential to put people at risk financially," says Mark Rukavina, executive director of the Access Project, a research and advocacy group that focuses on medical debt. The Health Insurance Portability and Accountability Act, or Hipaa, a federal law that has patient-privacy provisions, doesn't bar hospitals from providing patient payment histories to consumer reporting agencies. It's unclear how much latitude hospitals have to legally check a patient's financial information. Under the Fair Credit Reporting Act, hospitals are allowed to obtain patients' credit reports if they get their permission, says Rebecca Kuehn, an assistant director in the Federal Trade Commission's division of privacy and identity protection.
Note: For many other revelations of privacy abuses from reliable, verifiable sources, click here.
Microsoft is developing Big Brother-style software capable of remotely monitoring a workers productivity, physical wellbeing and competence. The Times has seen a patent application filed by the company for a computer system that links workers to their computers via wireless sensors that measure their metabolism. The system would allow managers to monitor employees performance by measuring their heart rate, body temperature, movement, facial expression and blood pressure. Unions said they fear that employees could be dismissed on the basis of a computers assessment of their physiological state. This is believed to be the first time a company has proposed developing such software for mainstream workplaces. Microsoft submitted a patent application in the US for a unique monitoring system that could link workers to their computers. Wireless sensors could read heart rate, galvanic skin response, EMG, brain signals, respiration rate, body temperature, movement facial movements, facial expressions and blood pressure, the application states. The system could also automatically detect frustration or stress in the user. Physical changes to an employee would be matched to an individual psychological profile based on a workers weight, age and health. If the system picked up an increase in heart rate or facial expressions suggestive of stress or frustration, it would tell management. Civil liberties groups and privacy lawyers strongly criticised the potential of the system for taking the idea of monitoring people at work to a new level.
Note: For revealing reports from major media sources on the increasing surveillance of all aspects of society by secret government and corporate programs, click here.
When previous Republican administrations were accused of illegality in the FBI and CIA spying abuses of the 1970s or the Iran-Contra affair of the 1980s, Democrats in Congress launched investigations or pushed for legislative reforms. But last week, faced with admissions by several telecommunication companies that they assisted the Bush administration in warrantless spying on Americans, leaders of the Senate intelligence committee took a much different tack -- proposing legislation that would grant those companies retroactive immunity from prosecution or lawsuits. The proposal marks the second time in recent years that Congress has moved toward providing legal immunity for past actions that may have been illegal. The Military Commissions Act, passed by a GOP-led Congress in September 2006, provided retroactive immunity for CIA interrogators who could have been accused of war crimes for mistreating detainees. Legal experts say the granting of such retroactive immunity by Congress is unusual, particularly in a case involving private companies. "It's particularly unusual in the case of the telecoms because you don't really know what you're immunizing," said Louis Fisher, a specialist in constitutional law with the Law Library of the Library of Congress. Civil liberties groups and many academics argue that Congress is allowing the government to cover up possible wrongdoing and is inappropriately interfering in disputes that the courts should decide. The American Civil Liberties Union [said] in a news release Friday that "the administration is trying to cover its tracks."
Broad new surveillance powers approved by Congress this month could allow the Bush administration to conduct spy operations that go well beyond wiretapping to include without court approval certain types of physical searches on American soil and the collection of Americans business records. This may give the administration even more authority than people thought, said David Kris, a former senior Justice Department lawyer in the Bush and Clinton administrations. Several legal experts said that by redefining the meaning of electronic surveillance, the new law narrows the types of communications covered in the Foreign Intelligence Surveillance Act, known as FISA, by indirectly giving the government the power to use intelligence collection methods far beyond wiretapping that previously required court approval if conducted inside the United States. These new powers include the collection of business records, physical searches and so-called trap and trace operations, analyzing specific calling patterns. For instance, the legislation would allow the government, under certain circumstances, to demand the business records of an American in Chicago without a warrant if it asserts that the search concerns its surveillance of a person who is in Paris, experts said. Some civil rights advocates said they suspected that the administration made the language of the bill intentionally vague to allow it even broader discretion over wiretapping decisions. The end result ... is that the legislation may grant the government the right to collect a range of information on American citizens inside the United States without warrants, as long as the administration asserts that the spying concerns the monitoring of a person believed to be overseas.
The Defense Intelligence Agency is preparing to pay private contractors up to $1 billion to conduct core intelligence tasks of analysis and collection over the next five years, an amount that would set a record in the outsourcing of such functions by the Pentagon's top spying agency. The proposed contracts ... reflect a continuing expansion of the Defense Department's intelligence-related work and fit a well-established pattern of Bush administration transfers of government work to private contractors. Since 2000, the value of federal contracts signed by all agencies each year has more than doubled to reach $412 billion, with the largest growth at the Defense Department. Outsourcing particularly accelerated among intelligence agencies after the [Sept. 11] 2001 terrorist attacks. The DIA's action comes a few months after CIA Director Michael V. Hayden, acting under pressure from Congress, announced a program to cut the agency's hiring of outside contractors by at least 10 percent. The DIA is the country's major manager and producer of foreign military intelligence, with more than 11,000 military and civilian employees worldwide and a budget of nearly $1 billion. It has its own analysts from the various services as well as collectors of human intelligence in the Defense HUMINT Service. DIA also manages the Defense attaches stationed in embassies all over the world. Unlike the CIA, the DIA outsources the major analytical products known as all-source intelligence reports, a senior intelligence official said.
The Bush administration has approved a plan to expand domestic access to some of the most powerful tools of 21st-century spycraft, giving law enforcement officials and others the ability to view data obtained from satellite and aircraft sensors that can see through cloud cover and even penetrate buildings and underground bunkers. A program approved by the Office of the Director of National Intelligence and the Department of Homeland Security will allow broader domestic use of secret overhead imagery beginning as early as this fall, with the expectation that state and local law enforcement officials will eventually be able to tap into technology once largely restricted to foreign surveillance. But the program ... quickly provoked opposition from civil liberties advocates, who said the government is crossing a well-established line against the use of military assets in domestic law enforcement. The administration's decision would provide domestic authorities with unprecedented access to high-resolution, real-time satellite photos. They could also have access to much more. Civil liberties groups quickly condemned the move, which Kate Martin, director of the Center for National Security Studies, ... likened to "Big Brother in the sky. They want to turn these enormous spy capabilities ... onto Americans. They are laying the bricks one at a time for a police state." Steven Aftergood, director of the Project on Government Secrecy for the Federation of American Scientists, said that ... oversight for the program was woefully inadequate. Enhanced access "shouldn't be adopted at all costs because it comes with risk to privacy and to the integrity of our political institutions," he said.
The Department of Homeland Security is funneling millions of dollars to local governments nationwide for purchasing high-tech video camera networks, accelerating the rise of a "surveillance society" in which the sense of freedom that stems from being anonymous in public will be lost, privacy rights advocates warn. The department ... has doled out millions on surveillance cameras, transforming city streets and parks into places under constant observation. A Globe [investigation] shows that a large number of new surveillance systems, costing at least tens and probably hundreds of millions of dollars, are being simultaneously installed around the country as part of homeland security grants. Federal money is helping New York, Baltimore, and Chicago build massive surveillance systems that may also link thousands of privately owned security cameras. Boston has installed about 500 cameras in the MBTA system, funded in part with homeland security funds. Marc Rotenberg, director of the Electronic Privacy Information Center, said [the] Homeland Security Department is the primary driver in spreading surveillance cameras, making their adoption more attractive by offering federal money to city and state leaders. The proliferation of cameras could mean that Americans will feel less free because legal public behavior -- attending a political rally, entering a doctor's office, or even joking with friends in a park -- will leave a permanent record, retrievable by authorities at any time.
It was appalling to watch over the last few days as Congress now led by Democrats caved in to yet another unnecessary and dangerous expansion of President Bushs powers, this time to spy on Americans in violation of basic constitutional rights. Many of the 16 Democrats in the Senate and 41 in the House who voted for the bill said that they had acted in the name of national security, but the only security at play was their job security. What [do] the Democrats ... plan to do with their majority in Congress if they are too scared of Republican campaign ads to use it to protect the Constitution and restrain an out-of-control president[?] The White House and its allies on Capitol Hill railroaded Congress into voting a vast expansion of the presidents powers. They gave the director of national intelligence and the attorney general authority to intercept without warrant, court supervision or accountability any telephone call or e-mail message that moves in, out of or through the United States as long as there is a reasonable belief that one party is not in the United States. While serving little purpose, the new law has real dangers. It would allow the government to intercept, without a warrant, every communication into or out of any country, including the United States. The Democratic majority has made strides on other issues like childrens health insurance against White House opposition. As important as these measures are, they do not excuse the Democrats from remedying the damage Mr. Bush has done to civil liberties and the Bill of Rights. That is their most important duty.
A federal intelligence court judge earlier this year secretly declared a key element of the Bush administration's wiretapping efforts illegal, according to a lawmaker and government sources, providing a previously unstated rationale for fevered efforts by congressional lawmakers this week to expand the president's spying powers. House Minority Leader John A. Boehner (R-Ohio) disclosed elements of the court's decision in remarks ... to Fox News as he was promoting the administration-backed wiretapping legislation. The judge, whose name could not be learned, concluded early this year that the government had overstepped its authority in attempting to broadly surveil communications between two locations overseas that are passed through routing stations in the United States. The decision was both a political and practical blow to the administration, which had long held that all of the National Security Agency's enhanced surveillance efforts since 2001 were legal. The administration for years had declined to subject those efforts to the jurisdiction of the Foreign Intelligence Surveillance Court, and after it finally did so in January the court ruled that the administration's legal judgment was at least partly wrong. The practical effect has been to block the NSA's efforts to collect information from a large volume of foreign calls and e-mails that passes through U.S. communications nodes clustered around New York and California. Both Democrats and Republicans have signaled they are eager to fix that problem through amendments to the Foreign Intelligence Surveillance Act (FISA). An unstated facet of the program is that anyone the foreigner is calling inside the United States, as long as that person is not the primary target, would also be wiretapped.
The Bush administration is pressing Congress this week for the authority to intercept, without a court order, any international phone call or e-mail between a surveillance target outside the United States and any person in the United States. It would also give the attorney general sole authority to order the interception of communications for up to one year as long as he certifies that the surveillance is directed at a person outside the United States. Civil liberties and privacy groups have denounced the administration's proposal, which they say would effectively allow the National Security Agency to revive a warrantless surveillance program conducted in secret from 2001 until late 2005. They say it would also give the government authority to force carriers to turn over any international communications into and out of the United States without a court order. An unstated facet of the program is that anyone the foreigner is calling inside the United States, as long as that person is not the primary target, would also be wiretapped. Caroline Fredrickson, director of the ACLU's Washington legislative office [said], "What the administration is really going after is the Americans. Even if the primary target is overseas, they want to be able to wiretap Americans without a warrant." The proposal would also allow the NSA to ... have access to the entire stream of communications without the phone company sorting, said Kate Martin, director of the Center for National Security Studies. "It's a 'trust us' system," she said. "Give us access and trust us."
The Federal Bureau of Investigation is developing a computer-profiling system that would enable investigators to target possible terror suspects. The System to Assess Risk, or STAR, assigns risk scores to possible suspects based on a variety of information, similar to the way a credit bureau assigns a rating based on a consumer's spending behavior and debt. The program focuses on foreign suspects but also includes data about some U.S. residents. Some lawmakers said ... that the report raises new questions about the government's power to use personal information and intelligence without accountability. "The Bush administration has expanded the use of this technology, often in secret, to collect and sift through Americans' most sensitive personal information," said Sen. Patrick J. Leahy (D-Vt.), chairman of the Senate Judiciary Committee. The use of data mining in the war on terror has sparked criticism. An airplane-passenger screening program called CAPPS II was revamped and renamed because of civil liberty concerns. An effort to collect Americans' personal and financial data called Total Information Awareness was killed. Law enforcement and national security officials have continued working on other programs to use computers to sift through information for signs of threats. The Department of Homeland Security, for example, flags travelers entering and leaving the United States who may be potential suspects through a risk-assessment program called the Automated Targeting System.
A federal appeals court removed a serious legal challenge to the Bush administration's warrantless wiretapping program yesterday, overruling the only judge who held that a controversial surveillance effort by the National Security Agency was unconstitutional. Two members of a three-judge panel ... ordered the dismissal of a major lawsuit that challenged the wiretapping, which President Bush authorized secretly to eavesdrop on communications ... shortly after the Sept. 11, 2001, attacks. The court did not rule on the spying program's legality. Instead, it declared that the American Civil Liberties Union and the others who brought the case -- including academics, lawyers and journalists -- did not have the standing to sue because they could not demonstrate that they had been direct targets of the clandestine surveillance. The decision vacates a ruling in the case made last August by a U.S. District Court judge in Detroit, who ruled that the administration's program to monitor private communications violated the Bill of Rights and a 1970s federal law. Steven R. Shapiro, the ACLU's legal director, said: "As a result of today's decision, the Bush administration has been left free to violate the Foreign Intelligence Surveillance Act, which Congress adopted almost 30 years ago to prevent the executive branch from engaging in precisely this kind of unchecked surveillance."
Pediatrician Rupin Thakkar's first inkling that the pharmaceutical industry was peering over his shoulder ... came in a letter from a drug representative about the generic drops Thakkar prescribes to treat infectious pinkeye. In the letter, the salesperson wrote that Thakkar was causing his patients to miss more days of school than they would if he put them on Vigamox, a more expensive brand-name medicine made by Alcon Laboratories. "My initial thought was 'How does she know what I'm prescribing?' " Thakkar said. "It feels intrusive ... I just feel strongly that medical encounters need to be private." He is not alone. Many doctors object to drugmakers' common practice of contracting with data-mining companies to track exactly which medicines physicians prescribe and in what quantities -- information marketers and salespeople use to fine-tune their efforts. The concerns are not merely about privacy. Proponents say using such detailed data for drug marketing serves mainly to influence physicians to prescribe more expensive medicines, not necessarily to provide the best treatment. "We don't like the practice, and we want it to stop," said Jean Silver-Isenstadt, executive director of the National Physicians Alliance. (Thakkar is on the group's board of directors.) "We think it's a contaminant to the doctor-patient relationship, and it's driving up costs." The American Medical Association makes millions of dollars each year by helping data-mining companies link prescribing data to individual physicians. It does so by licensing access to the AMA Physician Masterfile, a database containing names, birth dates, educational background, specialties and addresses for more than 800,000 doctors.
Note: For more reliable, verifiable information about major corruption in the drug industry, click here.
Congressional Republicans and Democrats demanded answers from the Bush administration Thursday about a government spy agency secretly collecting records of ordinary Americans' phone calls to build a database of every call made within the country. This database affects as many as 200 million Americans. AT&T Corp., Verizon Communications Inc., and BellSouth Corp. telephone companies began turning over records of tens of millions of their customers' phone calls to the NSA program shortly after the Sept. 11, 2001, terrorist attacks. 'We have reached a privacy crisis,' said Rep. Edward J. Markey, D-MA, the ranking Democrat on the House Telecommunications and Internet Subcommittee. 'The N.S.A. stands for Now Spying on Americans.' Republican Sen. Lindsey Graham, R-S.C., told Fox News Channel: "The idea of collecting millions or thousands of phone numbers, how does that fit into following the enemy?" The Justice Department has abruptly ended an inquiry into the warrantless eavesdropping program because the NSA refused to grant its lawyers the necessary security clearance. The Justice Department's Office of Professional Responsibility [said] they were closing their inquiry because without clearance their lawyers cannot examine Justice lawyers' role in the program.
Note: Who gave the NSA power to stop the Justice Department from performing an inquiry?
The National Security Agency used law enforcement agencies, including the Baltimore Police Department, to track members of a city anti-war group as they prepared for protests outside the sprawling Fort Meade facility, internal NSA documents show. The target of the clandestine surveillance was the Baltimore Pledge of Resistance, a group...whose members include many veteran city peace activists with a history of nonviolent civil disobedience. Since the Sept. 11 terrorist attacks, members of the group say, their protests have come under increasing scrutiny by federal and local law enforcement officials working on behalf of the NSA. An internal NSA e-mail, posted on two Internet sites this week, shows how operatives with the "Baltimore Intel Unit" provided a minute-by-minute account of Pledge of Resistances' preparations for a July 3, 2004. "****UPDATE: 11:55 HRS. S/A V------- ADVISED THE PROTESTORS LEFT 4600 YORK ROAD EN ROUTE TO THE NSA CAMPUS ... S/A V----- REPORTED FIVE OR SIX PEOPLE IN A BLUE VAN WITH BLACK BALLOONS, ANTI-WAR SIGNS AND A POSSIBLE HELIUM TANK." Some legal analysts and administration critics say the agency's actions violate the 1978 Foreign Intelligence Surveillance Act.
Abandoned pets are a growing part of the military culture. Dogs and cats are dropped off in remote corners of the post at a rate of more than 20 a week. But the US Armed Forces are fighting back. Adopting a Big Brother approach, the military is implanting microchips in cats and dogs that live on government land as much for animal control as for owner control. Says Fort Polk, La., Garrison Command Sgt. Maj. Ricky L. Jones of the soldier who abandons a pet, "with the chip you can't hide." Fort Polk has used the chip to track down soldiers who have abandoned their pets and forced them to pay an adoption fee. "It's a way to control our stray animal population and protect our working force, too," says Capt. Steven Baty, a veterinarian at Fort Carson, Colo., where microchipping has been mandatory since 1998. The tiny chips, the size of a grain of rice, are injected under the skin on an animal's neck and contain a bar code that can be scanned and read by humane societies and veterinary clinics nationwide. The procedure costs about $15, takes two to three seconds, and is no more painful than a typical vaccination. Microchip enforcement varies by base. At Fort Polk, La., animal controllers are part of a weekly housing patrol, joining inspectors who check to make sure lawns are cut and that soldiers aren't violating housing regulations. The animal controller carries a portable scanner and runs the wand over dogs and cats, looking for numbers to light up the small screen. If the pets don't have a microchip, soldiers are warned, and if they don't comply, their animals are taken away.
Note: The Monitor removed this article from their website. To see a copy of it on the Internet archive, click here.
Since the 9/11 terrorist attacks, the Bush administration has repeatedly demonstrated that it does not feel bound by the law or the Constitution. It cannot even be trusted to properly use the enhanced powers it was legally granted after the attacks. Yet, once again, President Bush has been trying to stampede Congress into a completely unnecessary expansion of his power to spy on Americans. The fight is over the 1978 Foreign Intelligence Surveillance Act, which requires the government to obtain a warrant before eavesdropping on electronic communications that involve someone in the United States. Mr. Bush decided after 9/11 that he was no longer going to obey that law. He authorized the National Security Agency to intercept international telephone calls and e-mail messages of Americans and other residents of this country without a court order. He told the public nothing and Congress next to nothing about what he was doing, until The Times disclosed the spying in December 2005. Ever since, the White House has tried to pressure Congress into legalizing Mr. Bushs rogue operation. The administration and its ... supporters in Congress argue that American intelligence is blinded by FISA and have seized on neatly timed warnings of heightened terrorist activity to scare everyone. It is vital for Americans, especially lawmakers, to resist that argument. It is pure propaganda. [The question at issue is] whether we are a nation ruled by law, or the whims of men in power.
AT&T Inc. said on Wednesday it was revising its privacy policy, explaining to customers that it owns their phone records and can hand them over to law enforcers if necessary. The changes...come at a time when AT&T and other phone companies face lawsuits claiming they aided a U.S. government domestic spying program by giving the National Security Agency call records of millions of customers without their permission. The new policy, unlike the old one, spells out the fact that AT&T...customer information constitutes "business records that are owned by AT&T. As such, AT&T may disclose such records to protect its legitimate business interests, safeguard others, or respond to legal process." The earlier policy had simply said that...the company could share customer information to "respond to subpoenas, court orders or other legal process, to the extent required and/or permitted by law." Under the new policy...the company also said that it would track viewing information for customers of a television service it is developing in order to help it make recommendations to customers based on their viewing habits. It also said that before customers use its services they must agree to the policy, an element that was not in its previous guidelines.
One of the fastest-growing online businesses is the business of spying on Internet users by using sophisticated software to track movements through the Web, so that the information can be sold to advertisers. Julia Angwin recently led a team of reporters from The Wall Street Journal in analyzing the tracking software. They discovered that nearly all of the most commonly visited websites gather information in real time about the behavior of online users. The Journal series identified more than 100 tracking companies, data brokers and advertising networks collecting data which are then sold on a stock market-like exchange to online advertisers. Angwin explains how consumer surveillance works, how users can disable the tracking software and how advertisers are continually evolving to keep up with the data they receive. She notes that many Internet users are unaware that their information is being tracked and then traded. "Most people that we have heard from since writing these stories did not know what was going on," Angwin explains. "So when you go to a website, you're not thinking about the fact that they might have relationships with all different types of monitoring firms, and those firms are installing things that are invisible to you on your computer."
Note: Julia Angwin is senior technology editor of The Wall Street Journal, and author of the book, Stealing MySpace: The Battle to Control the Most Popular Website in America. For lots more on growing threats to privacy, click here.
The U.S. government has been increasing its use of the state secrets privilege to avoid disclosure of classified information in civil lawsuits. Some legal scholars and members of Congress contend that the Bush administration has employed it excessively as it intervened in cases that could expose information about sensitive programs. These include the rendition of detainees to foreign countries for interrogation and cases related to the National Security Agency's use of warrantless wiretaps. The privilege allows the government to argue that lawsuits -- and the information potentially revealed by them -- could damage national security. It gives judges the power to prevent information from reaching public view or to dismiss cases even if they appear to have merit. Sen. Edward M. Kennedy (D-Mass.) ... cited statistics that show the Bush administration has used the state secrets privilege substantially more, on a percentage basis, than previous administrations to block or dismiss lawsuits. Kevin Bankston, a lawyer with the Electronic Frontier Foundation ... said "The administration is attempting to use the privilege as a back-door immunity to obtain dismissal of any case that attempts to put the NSA wiretapping issue in front of a judge. It is no secret such a program existed."
Note: For many disturbing reports on government secrecy from reliable sources, click here.
The questions from the civilian spokesman at Fort Lewis started sounding suspicious to Sarah Olson. He had called to ask the Oakland freelance journalist about the accuracy of quotes in her story about Lt. Ehren Watada, which had appeared on the liberal Web site Truthout.org. As the telephone conversation progressed, Olson realized that the military was using her to fortify its case against Watada, whom it was prosecuting as the first commissioned officer to refuse deployment to Iraq. While Watada faces a court-martial next month for conduct unbecoming an officer, the U.S. military pursues Olson. Last month, military prosecutors subpoenaed the 31-year-old writer and radio journalist, asking her to appear at his court-martial, scheduled to begin next month, to verify what Watada said. If Olson doesn't testify, she faces six months in jail or a $500 fine and a felony charge for a story she was paid $300 to write. Olson doesn't want to be part of a legal action that she believes limits someone's free speech. She came to journalism six years ago ... hoping to create more places for dissenting or seldom-heard voices, not fewer. "Journalists should not be asked to participate in the prosecution of political speech," Olson said. [She] isn't being asked to reveal unpublished work. "What I don't understand is why they (prosecutors) can't get this information digitally," said Fidell, president of the National Institute of Military Justice. Olson doesn't have a problem with journalists testifying in court. She doesn't want journalists to be coerced to testify in cases that could limit free speech.
Note: Truthout.org is one of the main sources of our information. Interesting that one of their reporters should be targeted in this way. For stories by 20 award-winning journalists on how the media is controlled, click here.
Deep in a remote, fog-layered hollow near Sugar Grove, W.Va., hidden by fortress-like mountains, sits the country's largest eavesdropping bug. The station's large parabolic dishes secretly and silently sweep in millions of private telephone calls and e-mail messages an hour. Run by the ultrasecret National Security Agency, the listening post intercepts all international communications entering the eastern United States. Another N.S.A. listening post, in Yakima,Wash., eavesdrops on the western half of the country. According to John E. McLaughlin, who as the deputy director of the Central Intelligence Agency in the fall of 2001 was among the first briefed on the program, this eavesdropping was the most secret operation in the entire intelligence network, complete with its own code word - which itself is secret. Jokingly referred to as "No Such Agency," the N.S.A. was created in absolute secrecy in 1952 by President Harry S. Truman. But the agency is still struggling to adjust to the war on terror. At home, it increases pressure on the agency to bypass civil liberties and skirt formal legal channels of criminal investigation. Originally created to spy on foreign adversaries, the N.S.A. was never supposed to be turned inward.
Note: Don't miss the amazing article on Operation Northwoods by the author of this article, former ABC producer James Bamford. It details the 1962 plans of the Pentagon chiefs to foment terrorism in the US as a pretext for war with Cuba. See http://www.WantToknow.info/010501operationnorthwoods
Facing a wave of litigation challenging its eavesdropping at home and its handling of terror suspects abroad, the Bush administration is increasingly turning to a legal tactic that swiftly torpedoes most lawsuits: the state secrets privilege. Officials have used the privilege...to ask the courts to throw out three legal challenges to the National Security Agency's domestic surveillance program. The privilege claim, in which the government says any discussion of a lawsuit's accusations would endanger national security, has short-circuited judicial scrutiny and public debate. While the privilege...was once used to shield sensitive documents or witnesses from disclosure, it is now often used to try to snuff out lawsuits at their inception. "If the very people you're suing are the ones who get to use the state secrets privilege, it's a stacked deck," said Representative Christopher Shays, Republican of Connecticut. Robert M. Chesney, a law professor at Wake Forest University...said the administration's legal strategy "raises profound legal and policy questions." Under Mr. Bush, the secrets privilege has been used to block a lawsuit by a translator at the Federal Bureau of Investigation, Sibel Edmonds, who was fired after accusing colleagues of security breaches. Two lawsuits challenging the government's practice of rendition, in which terror suspects are seized and delivered to detention centers overseas, were dismissed after the government raised the secrets privilege.
Note: Sibel Edmonds is one of several whistleblowers with powerfully incriminating information on 9/11 who have been silenced with tactics like those mentioned above. To learn more about this critical case which has been blocked, see http://www.WantToKnow.info/050131sibeledmonds
A four-page memo circulating in Congress that reveals alleged United States government surveillance abuses is being described by lawmakers as shocking. The lawmakers said they could not yet discuss the contents of the memo they reviewed on Thursday after it was released to members by the House Intelligence Committee. But they say the memo should be immediately made public. It is so alarming the American people have to see this, Ohio Rep. Jim Jordan said. It's troubling, North Carolina Rep. Mark Meadows said. Part of me wishes that I didn't read it because I dont want to believe that those kinds of things could be happening in this country that I call home and love so much. The House Intelligence Committee on Thursday approved a motion by New York Rep. Pete King to release the memo on abuses of FISA, or the Foreign Intelligence Surveillance Act, to all House members. The memo details the Intelligence Committees oversight work for the FBI and Justice, including the controversy over unmasking and FISA surveillance. The process for releasing it to the public involves a committee vote. If approved, it could be released as long as there are no objections from the White House within five days. On Thursday, the Senate voted 65-34 to reauthorize a FISA provision that allows U.S. spy agencies to conduct surveillance on foreign targets abroad for six years.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy.
Leaked documents and public records reveal a troubling fusion of private security, public law enforcement, and corporate money in the fight over the Dakota Access Pipeline. By the time law enforcement officers began evicting residents of the ... resistance camp near the Standing Rock Sioux reservation on February 22, the brutal North Dakota winter had already driven away most of the pipeline opponents. It would have been a natural time for the private security company in charge of monitoring the pipeline to head home. But internal communications between TigerSwan and its client, pipeline parent company Energy Transfer Partners, show that the security firm instead reached for ways to stay in business. Indeed, TigerSwan appeared to be looking for new causes, too. The ... firms sweeping surveillance of anti-Dakota Access protesters had already spanned five months and expanded into Iowa, South Dakota, and Illinois. TigerSwan became particularly interested in Chicago. [Leaked] documents dated between February 19 and February 21 describe TigerSwans efforts to monitor an anti-Trump protest organized by the local chapter of the Answer Coalition, an anti-war, anti-racism group. Answer Coalitions ... John Beacham, who organized the protest TigerSwan described, said that [the NoDAPL movement] was not the events primary focus. Theyre trying to make connections where they arent. Its almost like theyre trying to cast conspiracy theories across the entire progressive movement, he told The Intercept.
Note: The above article is part of an in-depth series, and includes many original source documents. Standing Rock activists were also targeted for investigation by the FBIs joint terrorism taskforce. For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the disappearance of privacy.
A federal appeals court on Tuesday revived a high-profile challenge to the National Security Agencys warrantless surveillance of internet communications. The ruling ... increases the chances that the Supreme Court may someday scrutinize whether the N.S.A.s so-called upstream system for internet surveillance complies with Fourth Amendment privacy rights. The ruling reversed a Federal District Court judges decision to throw out the case. The district judge had ruled that the plaintiffs - including the Wikimedia Foundation - lacked standing to sue because they could not prove that their messages had been intercepted. Because of how the internet works, surveillance of communications crossing network switches is different from traditional circuit-based phone wiretapping. While the government can target a specific phone call without touching anyone elses communications, it cannot simply intercept a surveillance targets email. Instead ... to find such emails it is necessary first to systematically copy data packets crossing a network switch and sift them in search of components from any messages involving a target. Documents provided by [Edward] Snowden and declassified by the government have shown that this system works through equipment installed at the facilities of companies, like AT&T, that [connect] the American internet to the rest of the world. Privacy advocates contend that the initial copying and searching of all those data packets ... violates Fourth Amendment protections against government search and seizure.
Note: For more along these lines, see concise summaries of deeply revealing news articles about intelligence agency corruption and the disappearance of privacy.
Edward Snowden, the whistleblower whose NSA revelations sparked a debate on mass surveillance, has waded into the arguments over the FBIs attempt to force Apple to help it unlock the iPhone 5C of one of the San Bernardino shooters. The FBI says that only Apple can deactivate certain passcode protections on the iPhone, which will allow law enforcement to guess the passcode by using brute-force. Talking via video link from Moscow to the Common Cause Blueprint for a Great Democracy conference, Snowden said: The FBI says Apple has the exclusive technical means to unlock the phone. Respectfully, thats bullshit. Snowden then went on to tweet his support for an American Civil Liberties Union report saying that the FBIs claims in the case are fraudulent. Apple co-founder Steve Wozniak also spoke out against the FBI on the Conan OBrien show on Monday, saying: I side with Apple on this one. [The FBI] picked the lamest case you ever could. Wozniak added: Verizon turned over all the phone records and SMS messages. So they want to take this other phone that the two didnt destroy, which was a work phone. Its so lame and worthless to expect theres something on it and to get Apple to expose it. Apples clash with the FBI comes to a head in California this month when the two will meet in federal court to debate whether the smartphone manufacturer should be required to weaken security settings on the iPhone of the shooter.
Note: According to The New York Times, the FBI has been misleading the public about the San Bernadino attacks for months. For more along these lines, see concise summaries of deeply revealing news articles about government corruption and the disappearance of privacy.
Newly-released documents show that FBI spied on the Burning Man festival in 2010. It remains unclear if FBI agents actually attended the event. Burning Man [takes place] in an isolated Nevada desert, where up to 70,000 people gather annually for music, art, drugs and large fires. The revelations of federal surveillance come from heavily-redacted internal FBI memos handed to ... reporter Inkoo Kang, who filed a request under the federal Freedom of Information Act for any FBI documents "mentioning the phrase 'Burning Man." In late August, a private security firm contacted the FBI's Las Vegas division for help conducting a "threat assessment" ahead of the event, to which the FBI replied that they had no worrying intelligence about Burning Man. Days later, the Las Vegas division messaged the FBI's Special Events Management Unit requesting guidance on planning an approach to the festival. A subsequent paragraph, sandwiched between two entirely-redacted paragraphs, said, "scheduled overtime for special agents assigned to work special events will be approved under certain very limited and relatively rare circumstances," raising question over whether or not FBI special agents were deployed at Burning Man. A final memo listed two "accomplishments" from the operation; one was redacted, the other was "local agency liaison established/utilized." The FBI concluded that the greatest threat present at Burning Man was "use of illegal drugs by the participants."
Note: The CIA once used art as a weapon in its propaganda campaigns. Is the investigation of a large art festival merely another erosion of privacy, or is the FBI up to something comparably strange?
Facial recognition software, which American military and intelligence agencies used for years in Iraq and Afghanistan to identify potential terrorists, is being eagerly adopted by dozens of police departments around the country. It is being used with few guidelines and with little oversight or public disclosure. Facial recognition ... is among an array of technologies, including StingRay tracking devices and surveillance aircraft with specialized cameras, that were used in overseas wars but have found their way into local law enforcement. The F.B.I. is pushing ahead with its $1 billion Next Generation Identification program, in which the agency will gather data like fingerprints, iris scans and photographs, as well as information collected through facial recognition software. The F.B.I. system will eventually be made accessible to more than 18,000 local, state, federal and international law enforcement agencies. But people who are not criminal suspects are included in the database, and the error rate for the software is as high as 20 percent meaning the authorities could misidentify millions of people. Among the cities that use facial recognition technology are New York and Chicago, which has linked it to 25,000 surveillance cameras. In many ways, though, San Diego County is at the forefront. Here, beat cops, detectives and even school police officers have been using hand-held devices to create a vast database of tens of thousands of photos of people usually without the persons consent.
Note: For more along these lines, read about the increasing militarization of police in the U.S. after 9/11, or see concise summaries of deeply revealing news articles about the erosion of privacy rights.
Whistleblower Edward Snowden received several standing ovations in the Swedish parliament after being given the Right Livelihood award for his revelations of the scale of state surveillance. Snowden, who is in exile in Russia, addressed the parliament by video from Moscow. In a symbolic gesture, his family and supporters said no one picked up the award on his behalf in the hope that one day he might be free to travel to Sweden to receive it in person. Snowden is wanted by the US on charges under the Espionage Act. His chances of a deal with the US justice department that would allow him to return home are slim and he may end up spending the rest of his days in Russia. His supporters hope that a west European country such as Sweden might grant him asylum. The awards jury, in its citation, said Snowden was being honoured for his courage and skill in revealing the unprecedented extent of state surveillance violating basic democratic processes and constitutional rights. The chamber was filled with members of parliament from almost all the parties. The Guardian editor, Alan Rusbridger, was also among the recipients. The jury citation said his award was in celebration of building a global media organisation dedicated to responsible journalism in the public interest, undaunted by the challenge of exposing corporate and government malpractices.
Note: For more along these lines, read how Wikipedia founder Jimmy Wales considers Edward Snowden a hero. For more on the Snowden case, see the deeply revealing reports from reliable major media sources available here.
To many Americans, online eavesdropping by the U.S. National Security Agency is an outrage, a threat to privacy and freedom. To some, it's a business opportunity. A small but growing number of companies have introduced Internet and communications services designed to shield users from the government's eyes. A few even advertise their products as "NSA-proof." Many of the companies have been offering encrypted online services for years, scrambling their customers' data and communications in ways that require the right computer-generated "key" to decode. They are at least as concerned with thwarting private hackers and corporate spies as they are with blocking federal agents. But some entrepreneurs in the field found motivation in the NSA, after learning that the agency has been collecting troves of Internet and phone data on ordinary citizens for years. "Privacy and democracy go hand in hand - that's why this is so important," said Jason Stockman, one of the creators of ProtonMail, which began offering an encrypted e-mail service in May. "Our goal is to protect people against mass surveillance." But most companies will quickly admit that if the NSA - or some foreign intelligence service - really wants your data, they can't guarantee protection. Since the NSA conducts its business in secret, its full capabilities remain a matter of speculation. Most companies that invoke the NSA in their marketing focus on encryption.
Note: For more on this, see concise summaries of deeply revealing government surveillance news articles from reliable major media sources.
An Indiana University faculty member has sued two U.S. customs agents for detaining her after the government eavesdropped on emails she exchanged with a Greek friend. The American Civil Liberties Union of Indiana filed a federal lawsuit [on February 19] alleging the customs agents violated Christine Von Der Haars constitutional protection against unreasonable searches and seizures. This case raises troubling issues about the power of the government to detain and question citizens, said Ken Falk, the ACLU of Indiana legal director who represents Von Der Haar. The lawsuit alleges Von Der Haar, a senior lecturer in the sociology department at Indiana University in Bloomington, was confined in a guarded room at Indianapolis International Airport for more than 20 minutes on June 8, 2012, while she was questioned about her relationship with her friend. The lawsuit alleges the questioning was based on surreptitious monitoring of communications between Von Der Haar and her friend, Dimitris Papatheodoropoulus. The two communicated frequently through emails. Some of these emails were flirtatious and romantic in nature, the lawsuit said. Von Der Haar felt she had no choice but to answer questions from the agents, whom she believed to be armed, and did not believe she could leave until they released her, the lawsuit said. The detention of Dr. Von Der Haar was without cause or justification, the complaint said, and caused her anxiety, concern, distress and other damages. The lawsuit names the two customs agents as defendants and seeks damages.
Note: For more on government abuses of civil liberties, see the deeply revealing reports from reliable major media sources available here.
Jimmy Wales, the founder of Wikipedia, has called on Barack Obama to rein in the National Security Agency as he described the whistleblower Edward Snowden as "a hero" whom history will judge "very favourably". Wales called for a "major re-evaluation" of the NSA, adding that the public "would have never approved this sweeping surveillance program" had it been put to a vote. The revelations, Wales said, had been "incredibly damaging and embarrassing to the US. It makes it very difficult for someone like me to go out, as I do, [to] speak to people in authoritarian countries, and say: 'You shouldnt be spying on activists, you shouldnt be censoring the internet', when we [in the US] are complicit in these acts of extraordinary intrusion into peoples personal lives. [Snowden] has exposed what I believe to be criminal wrongdoing, lying to Congress, and certainly [an] affront to the Fourth Amendment. I think that history will judge him very favourably. There is a growing sense of concern in Congress about this, a growing sense in Congress that public is angry about this, that they have been misled and I think we are going to see legislation to change this."
Note: For more on the realities of intelligence agency activities, see the deeply revealing reports from reliable major media sources available here.
The Guardian has agreed with the New York Times to give the U.S. newspaper access to some classified documents leaked by former National Security Agency contractor Edward Snowden, both papers said on [August 23]. In a brief story posted on its website, the Guardian said it "struck a partnership" with the Times after the British government threatened the Guardian with legal action unless it either surrendered or destroyed files it received from Snowden about Government Communications Headquarters - Britain's equivalent of NSA. The Times' executive editor, Jill Abramson, confirmed the collaboration. A source familiar with the matter said the partnership deal had been struck several weeks ago and that Abramson was personally involved in negotiating it. The Guardian said in its story that its partnership with the Times would enable it to "continue exposing mass surveillance by putting the Snowden documents on GCHQ beyond government reach." The Times and the Guardian previously collaborated on stories related to alleged phone hacking by British tabloid newspapers and on coverage of secret U.S. military and diplomatic documents made available by U.S. Army soldier Bradley Manning to the WikiLeaks website.
Note: For more on the NSA spying scandal, see the deeply revealing reports from reliable major media sources available here.
A divided Supreme Court ruled [on June 3] that police may take DNA samples when booking those arrested for serious crimes, narrowly upholding a Maryland law and opening the door to more widespread collection of DNA by law enforcement. The court ruled 5 to 4 that government has a legitimate interest in collecting DNA from arrestees ... to establish the identity of the person in custody. Conservative Justice Antonin Scalia ... amplified his displeasure by reading a summary of his dissent from the bench. The court has cast aside a bedrock rule of our Fourth Amendment law: that the government may not search its citizens for evidence of crime unless there is a reasonable cause to believe that such evidence will be found, Scalia said from the bench. He added, Make no mistake about it: As an entirely predictable consequence of todays decision, your DNA can be taken and entered into a national DNA database if you are ever arrested, rightly or wrongly, and for whatever reason. Steven R. Shapiro, legal director of the American Civil Liberties Union said the decision creates a gaping new exception to the Fourth Amendment and violates a long-established understanding that police cannot search for evidence of a crime ... without individualized suspicion.
Note: For deeply revealing reports from reliable major media sources on government assaults on privacy, click here.
Is your car spying on you? If it's a recent model, has a fancy infotainment system or is equipped with toll-booth transponders or other units you brought into the car that can monitor your driving, your driving habits or destination could be open to the scrutiny of others. If your car is electric, it's almost surely capable of ratting you out. You may have given your permission, or you may be the last to know. All too often, "people don't know it's happening," says Dorothy Glancy, a law professor at Santa Clara University in California who specializes in transportation and privacy. "People should be able to decide whether they want it collected or not." Try as you may to protect your privacy while driving, it's only going to get harder. The government is about to mandate installation of black-box accident recorders, a dumbed-down version of those found on airliners that remember all the critical details leading up to a crash, from your car's speed to whether you were wearing a seat belt. The devices are already built into 96% of new cars. Privacy becomes an issue when data end up in the hands of outsiders whom motorists don't suspect have access to it, or when the data are repurposed for reasons beyond those for which they were originally intended. Though the information is being collected with the best of intentions safer cars or to provide drivers with more services and conveniences there is always the danger it can end up in lawsuits, or in the hands of the government or with marketers looking to drum up business from passing motorists.
Note: For more on the OnStar system in most GM cars now and how it allows spying on you, read the CNN article titled "OnStar's 'brazen' data tracking comes under fire" at this link.
Dozens of police departments nationwide are gearing up to use a tech company's already controversial iris- and facial-scanning device that slides over an iPhone and helps identify a person or track criminal suspects. Its use has set off alarms with some who are concerned about possible civil liberties and privacy issues. The smartphone-based scanner, named Mobile Offender Recognition and Information System, or MORIS, is made by BI2 Technologies in Plymouth, Massachusetts. An iris scan, which detects unique patterns in a person's eyes, can reduce to seconds the time it takes to identify a suspect in custody. When attached to an iPhone, MORIS can photograph a person's face and run the image through software that hunts for a match in a BI2-managed database of U.S. criminal records. Constitutional rights advocates are concerned, in part because the device can accurately scan an individual's face from up to four feet away, potentially without a person's being aware of it. Experts also say that before police administer an iris scan, they should have probable cause a crime has been committed. "What we don't want is for them to become a general surveillance tool, where the police start using them routinely on the general public, collecting biometric information on innocent people," said Jay Stanley, senior policy analyst with the national ACLU in Washington, D.C.
Note: For key reports from major media sources on government threats to privacy and civil liberties, click here and here.
Scotland Yard has admitted giving MPs inaccurate information by denying "covert officers" were deployed at London's G20 protests in April 2009. In a statement, the Metropolitan Police said it had established that covert officers had been deployed to the protests. The letter came after ... the unmasking of undercover policeman Mark Kennedy, who attended many demonstrations during seven years living as a spy among green activists. Giving evidence at the select committee in 2009, Commander Bob Broadhurst told MPs then: "The only officers we deploy for intelligence purposes at public order are forward intelligence team officers who are wearing full police uniforms with a yellow jacket with blue shoulders. There were no plain clothes officers deployed at all." The Met statement released on Wednesday said: "Having made thorough checks on the back of recent media reporting we have now established that covert officers were deployed during the G20 protests. Therefore the information that was given by Commander Bob Broadhurst to the Home Affairs Select Committee saying that 'We had no plain-clothes officers deployed within the crowd' was not accurate."
Note: For lots more on the police provocateur Mark Kennedy, click here.
A growing pilot and passenger revolt over full-body scans and what many consider intrusive pat-downs couldn't have come at a worse time for the nation's air travel system. Thanksgiving, the busiest travel time of the year, is less than two weeks away. Grassroots groups are urging travelers to either not fly or to protest by opting out of the full-body scanners and undergo time-consuming pat-downs instead. Some pilots, passengers and flight attendants have chosen to opt out of the revealing scans. One online group, National Opt Out Day calls for a day of protest against the scanners on Wednesday, November 24, the busiest travel day of the year. Another group argues the TSA should remove the scanners from all airports. The Electronic Privacy Information Center (EPIC)... is taking legal action. Pilots' unions for US Airways and American Airlines are urging their members to avoid full-body scanning at airport security checkpoints, citing health risks and concerns about intrusiveness and security officer behavior. "Pilots should NOT submit to AIT (Advanced Imaging Technology) screening," wrote Capt. Mike Cleary, president of the U.S. Airline Pilots Association. "Frequent exposure to TSA-operated scanner devices may subject pilots to significant health risks," Cleary wrote. The website We Won't Fly urgers travelers to "Act now. Travel with Dignity."
Note: For a powerful, one-minute video showing just how invasive these searches are, click here.
The world of modern eavesdropping, or signals intelligence ... for many years ... operated in the shadows. The Puzzle Palace, the 1983 best seller by James Bamford that remains the benchmark study of the N.S.A., first pulled back the curtain to provide a glint of unwanted sunlight on the place. As each operation has come to light, an anxious public has wanted to know whether this powerful new surveillance model was undermining traditional notions of privacy and civil liberties. Just whom is the government watching? And who is watching the watchers? It has been left to outsiders journalists, authors, civil rights advocates and privacy groups to keep tabs on the watchers and to bring public scrutiny to once-secret programs. For the spymasters, this spotlight was decidedly unwelcome. Mike McConnell, a director of intelligence in the Bush administration, ... is one of the recurring characters in The Watchers: The Rise of Americas Surveillance State by Shane Harris. Mr. Harris, with some success, does what Mr. McConnell and others in the intelligence world have found so objectionable: he watches the watchers. At its best The Watchers provides an insightful glimpse into how Washington works and how ideas are marketed and sold in the back rooms of power, whether the product being peddled is widgets or a radical model for intelligence gathering.
Note: For more insights into the activities of Big Brother, click here.
As demonstrations have evolved with the help of text messages and online social networks, so too has the response of law enforcement. On Thursday, F.B.I. agents descended on a house in Jackson Heights, Queens [NY], and spent 16 hours searching it. The most likely reason for the raid: a man who lived there had helped coordinate communications among protesters at the Group of 20 summit in Pittsburgh. The man, Elliot Madison, 41, a social worker who has described himself as an anarchist, had been arrested in Pittsburgh on Sept. 24 and charged with hindering apprehension or prosecution, criminal use of a communication facility and possession of instruments of crime. The Pennsylvania State Police said he was found in a hotel room with computers and police scanners while using the social-networking site Twitter to spread information about police movements. He has denied wrongdoing. American protesters first made widespread use of mass text messages in New York, during the 2004 Republican National Convention. Messages, sent as events unfolded, allowed demonstrators and others to react quickly to word of arrests, police mobilizations and roving rallies. Mass texting has since become a valued tool among protesters, particularly at large-scale demonstrations. Mr. Madison [may be] the first to be charged criminally while sending information electronically to protesters about the police. He and a friend were part of a communications network among people protesting the G-20, Mr. Madisons lawyer, Martin Stolar, said on Saturday. Theres absolutely nothing that hes done that should subject him to any criminal liability.
Note: For many reports from reliable sources on increasing government erosion of civil liberties, click here.
The European security research programme (ESRP) has a 1.4bn EU budget and its twin objectives are to enhance European security and foster the growth of a globally competitive security industry in Europe. Unfortunately, in its haste to cash-in on the homeland security boom, the EU has effectively outsourced the design of its security research agenda to some of the corporations that have the most to gain from its implementation. It has created bodies outside the formal structure of the EU, beyond parliamentary scrutiny and democratic control. The result is a public research programme designed by lobbyists, for lobbyists, with corporations invited to shape the objectives and annual priorities, and then apply for the money on offer. ESRP was the brainchild of the "group of personalities", an EU advisory body convened in 2003 that included some of Europe's largest defence and IT contractors alongside the likes of NATO, the EU military committee and the Rand Corporation. The group's primary concern was the scale of the US government's investment in homeland security R&D, which meant that the US was "taking a lead" in the development of security "technologies and equipment which could meet a number of Europe's needs", putting US multinationals in "a very strong competitive position".
Note: The author of this article, Ben Hayes, has written a detailed report, NeoConOpticon: the EU Security-Industrial Complex published by Statewatch and the Transnational Institute.
Interpol is planning to expand its role into the mass screening of passengers moving around the world by creating a face recognition database. Every year more than 800 million international travellers fail to undergo "the most basic scrutiny" to check whether their identity documents have been stolen, the global policing cooperation body has warned. Senior figures want a system that lets immigration officials capture digital images of passengers and immediately cross-check them against a database of pictures of [alleged] terror suspects, international criminals and fugitives. The UK's first automated face recognition gates -- matching passengers to their digital image in the latest generation of passports -- began operating at Manchester airport in August. Mark Branchflower, head of Interpol's fingerprint unit, will this week unveil proposals in London for the creation of biometric identification systems that could be linked to such immigration checks. The civil liberties group No2ID, which campaigns against identity cards, expressed alarm at the plans. "This is a move away from seeking specific persons to GCHQ-style bulk interception of information," warned spokesman Michael Parker. "This is the next step. Law enforcement agencies want the most efficient systems but there has to be a balance between security and privacy."
Note: For many disturbing reports on increasing threats to privacy, click here.
US Attorney General Michael Mukasey has signed new guidelines for FBI operations he said are designed to better protect the country from terrorist attacks, but that raise concern of some lawmakers and civil rights groups. The new, revised regulations -- the original version met strong criticism from congressional committees last month -- comprise 50 pages dealing with five areas of FBI investigation, including criminal, national security and foreign intelligence. Despite Mukasey's assurances that the new regulations "reflect consultation with Congress as well as privacy and civil liberties groups," not all concerns over their effect on privacy rights were dispelled. [The] Senate Judiciary Committee chairman, Democrat Patrick Leahy, said the new guidelines expand the FBI's powers of surveillance. "It appears that with these guidelines, the attorney general is once again giving the FBI broad new powers to conduct surveillance and use other intrusive investigative techniques on Americans without requiring any indication of wrongdoing or any approval even from FBI supervisors," Leahy said in a statement. "The American people deserve a ... Justice Department that does not sacrifice or endanger their rights and privacy," he added. The American Civil Liberties Union, who had called for an investigation into the first version of the FBI regulations, said the new rules "reduce standards for beginning 'assessments.'" "More troubling still," it added, "the guidelines allow a person's race or ethnic background to be used as a factor in opening an investigation, a move that the ACLU believes may institute a racial profiling as a matter of policy."
Note: For many reports on increasing government surveillance and threats to privacy, click here.
A Bush administration lawyer resisted a San Francisco federal judge's attempts Wednesday to get him to say whether Congress can limit the president's wiretap authority in terrorism and espionage cases, calling the question simplistic. "You can't possibly make that judgment on the public record" without knowing the still-secret details of the electronic surveillance program that President Bush approved in 2001, Justice Department attorney Anthony Coppolino said at a crucial hearing in a wiretapping lawsuit. Chief U.S. District Judge Vaughn Walker didn't rule immediately on the government's request to dismiss the suit by an Islamic charity in Oregon, which says a document that federal authorities accidentally released showed it was wiretapped. But Walker, in an extensive exchange with Coppolino, said Congress had spoken clearly in a 1978 law that required the government to obtain a warrant from a secret court before it could conduct electronic surveillance of suspected foreign terrorists or spies. "The president is obliged to follow what Congress has mandated," Walker said. The case may determine whether any U.S. court can judge the legality of Bush's covert order to the National Security Agency to intercept phone calls and e-mails between Americans and suspected foreign terrorists without seeking judicial approval. After Bush acknowledged the existence of the program, Congress temporarily extended it in August and now is debating whether to protect telecommunications companies from lawsuits for their past cooperation. Most lawsuits challenging the program have been dismissed because the plaintiffs were unable to show that they had been wiretapped.
Note: For many disturbing reports of increasing threats to civil liberties, click here.
The military is using the FBI to skirt legal restrictions on domestic surveillance to obtain private records of Americans' Internet service providers, financial institutions and telephone companies, the ACLU said Tuesday. The American Civil Liberties Union based its conclusion on a review of more than 1,000 documents turned over by the Defense Department after it sued the agency last year for documents related to national security letters. The letters are investigative tools used to compel businesses to turn over customer information without a judge's order or grand jury subpoena. ACLU lawyer Melissa Goodman said the documents the civil rights group studied "make us incredibly concerned that the FBI and DoD might be collaborating to evade limits" placed on the Defense Department's use of the letters. Goodman, a staff attorney with the ACLU National Security Project, said the military is allowed to demand financial and credit records in certain instances but does not have the authority to get e-mail and phone records or lists of Web sites that people have visited. That is the kind of information that the FBI can get by using a national security letter, she said. "That's why we're particularly concerned. The DoD may be accessing the kinds of records they are not allowed to get," she said. Goodman also noted that legal limits are placed on the Defense Department "because the military doing domestic investigations tends to make us leery.
Note: For further disturbing reports on threats to civil liberties, click here.
When the nation's intelligence agencies wanted a computer network to better share information ... they turned to a big name in the technology industry to supply some of the equipment: Google Inc. The Mountain View company sold the agencies servers for searching documents. Many of the contracts are for search appliances - servers for storing and searching internal documents. Agencies can use the devices to create their own mini-Googles on intranets made up entirely of government data. Additionally, Google has had success licensing a souped-up version of its aerial mapping service, Google Earth. Spy agencies are using Google equipment as the backbone of Intellipedia, a network aimed at helping agents share intelligence. [The system] is maintained by the director of national intelligence and is accessible only to the CIA, FBI, National Security Agency and an alphabet soup of other intelligence agencies and offices. Google supplies the computer servers that support the network, as well as the search software that allows users to sift through messages and data. Because of the complexities of doing business with the government, Google uses resellers to process orders on its behalf. Google takes care of the sales, marketing and management of the accounts. Google is one of many technology vendors vying for government contracts. On occasion, Google is the target of conspiracy theories from bloggers who say it is working with spy agencies more closely than simply selling search equipment.
The sad saga of [Eliot] Spitzer should concern every American. The web of snooping in which federal investigators and regulators are now able to ensnare any person who engages in any form of financial transaction has become so complex and pervasive that almost no person anywhere in the world can escape its clutches. The seeds of this modern-day Orwellian financial web were sown in the late 1960s and early 1970s when such expansive federal laws as the Bank Secrecy Act were enacted. Designed as tools to ferret out organized crime figures, major drug traffickers and international money launderers, this family of far-reaching regulatory-cum-criminal laws initially was used largely as intended. Many of the Suspicious Activity Reports (or SARs) required by the Bank Secrecy Act of 1970, for example, were largely ignored by investigators and prosecutors, who viewed them as burdensome and difficult to catalog and utilize. Two events have conspired to change all that. First, the advent of digital technology has elevated dramatically the ability of the government to gather, analyze, manipulate, retrieve and disseminate the SAR data. The second factor ... was, of course, the events of 9/11 and the ensuing USA Patriot Act. These two things institutionalized fear as the driving force in virtually all federal policies, including those relating to financial reporting. [A section of] the Patriot Act has been interpreted by banking examiners to require banks to profile their customers and the full range of their transactions, regardless of amount. These know your customer regulations are among the most insidious of this entire class of invasive federal laws and regulations.
Note: This informative article is by former US Congressman Bob Barr, who has become a crusader against the excesses of the PATRIOT Act.
When Congress passed the Patriot Act in the aftermath of the 9/11 attacks, law-enforcement agencies hailed it as a powerful tool to help track down the confederates of Osama bin Laden. No one expected it would end up helping to snag the likes of Eliot Spitzer. In the fine print were provisions that gave the Treasury Department authority to demand more information from banks about their customers' financial transactions. But Treasury went further. It issued stringent new regulations that required banks themselves to look for unusual transactions (such as odd patterns of cash withdrawals or wire transfers) and submit SARsSuspicious Activity Reportsto the government. Facing potentially stiff penalties if they didn't comply, banks and other financial institutions installed sophisticated software to detect anomalies among millions of daily transactions. They began ranking the risk levels of their customers ... based on complex formulas that included ... whether an account holder was a "politically exposed person" [PEP]. At first focused on potentially crooked foreign officials, the PEP lists expanded to include many U.S. politicians and public officials who were conceivably vulnerable to corruption. Federal prosecutors around the country routinely scour the SARs for potential leads. One of those leads led to Spitzer. Last summer New York's North Fork Bank, where Spitzer had an account, filed a SAR about unusual money transfers he had made. The governor called attention to himself by asking the bank to transfer money in someone else's name. The SAR was not itself evidence that Spitzer had committed a crime. But it made the Feds curious enough to follow the money.
Note: This story provides useful information about how the PATRIOT Act has been applied since its passage. The reasons for the investigation of Eliot Spitzer, leading to his resignation, may not have been so simple, however, given his many powerful enemies in government and on Wall Street.
Montana Governor Brian Schweitzer is urging a third of the nation's governors to join him in opposing the implementation of a national identification card, saying they can force Congress to change it. Schweitzer, who last year said "no, nope, no way, hell no" to the federal plan calling for national driver's licenses under the REAL ID Act, sent a letter yesterday to 17 other governors asking them to oppose a Department of Homeland Security effort to penalize states that have not adopted the mandate. Homeland Security has said recently that travelers from states that have not adopted the license will have to use a passport or certain types of federal border-crossing cards if they want to avoid a vigorous secondary screening at airport security.
Residents of at least 17 states are suddenly stuck in the middle of a fight between the Bush administration and state governments over post-September 11 security rules for driver's licenses -- a dispute that, by May, could leave millions of people unable to use their licenses to board planes or enter federal buildings. Homeland Security Secretary Michael Chertoff, who unveiled final details of the REAL ID Act's rules on Friday, said that if states want their licenses to remain valid for air travel after May 2008, those states must seek a waiver indicating they want more time to comply with the legislation. Chertoff said that in instances where a particular state doesn't seek a waiver, its residents will have to use a passport or a newly created federal passport card if they want to avoid a vigorous secondary screening at airport security. Chertoff spoke as he discussed the details of the administration's plan to improve security for driver's licenses in all 50 states -- an effort delayed due to opposition from states worried about the cost and civil libertarians upset about what they believe are invasions of privacy. Under the rules announced Friday, Americans born after Dec. 1, 1964, will have to get more secure driver's licenses in the next six years. The American Civil Liberties Union has fiercely objected to the effort, particularly the sharing of personal data among government agencies. In its written objection to the law, the ACLU claims REAL ID amounts to the "first-ever national identity card system," which "would irreparably damage the fabric of American life."
Federal officials are routinely asking courts to order cellphone companies to furnish real-time tracking data so they can pinpoint the whereabouts of drug traffickers, fugitives and other criminal suspects, according to judges and industry lawyers. In some cases, judges have granted the requests without requiring the government to demonstrate that there is probable cause to believe that a crime is taking place or that the inquiry will yield evidence of a crime. Privacy advocates fear such a practice may expose average Americans to a new level of government scrutiny of their daily lives. The requests and orders are sealed at the government's request, so it is difficult to know how often the orders are issued or denied. "Most people don't realize it, but they're carrying a tracking device in their pocket," said Kevin Bankston of the privacy advocacy group Electronic Frontier Foundation. "Cellphones can reveal very precise information about your location, and yet legal protections are very much up in the air." In a stinging opinion this month, a federal judge in Texas denied a request by a Drug Enforcement Administration agent for data that would identify a drug trafficker's phone location by using the carrier's E911 tracking capability. E911 tracking systems read signals sent to satellites from a phone's Global Positioning System (GPS) chip or triangulated radio signals sent from phones to cell towers. "Law enforcement routinely now requests carriers to continuously 'ping' wireless devices of suspects to locate them when a call is not being made . . . so law enforcement can triangulate the precise location of a device and [seek] the location of all associates communicating with a target," wrote Christopher Guttman-McCabe, vice president of regulatory affairs for CTIA -- the Wireless Association.
Note: For many major media reports on serious new threats to civil liberties, click here.
A proposed new FBI program would skirt federal laws by paying private companies to hold millions of phone and Internet records which the bureau is barred from keeping itself, experts say. The $5 million project would apparently pay private firms to store at least two years' worth of telephone and Internet activity by millions of Americans, few of whom would ever be considered a suspect in any terrorism, intelligence or criminal matter. The FBI is barred by law from collecting and storing such data if it has no connection to a specific investigation or intelligence matter. In recent years the bureau has tried to encourage telecommunications firms to voluntarily store such information, but corporations have balked at the cost of keeping records they don't need."The government isn't allowed to warehouse the information, and the companies don't want to, so this creates a business incentive for the companies to warehouse it, so the government can access it later," said Mike German, a policy expert on national security and privacy issues for the American Civil Liberties Union (ACLU)."It's a public-private partnership that puts civil liberties to the test." In March, an FBI official identified the companies as Verizon, MCI and AT&T.Even the bureau's own top lawyer said she found the [FBI's] behavior "disturbing," noting that when requesting access to phone company records, it repeatedly referenced "emergency" situations that did not exist, falsely claimed grand juries had subpoenaed information and failed to keep records on much of its own activity.
In a public health emergency, suspected victims would no longer have to give permission before experimental tests could be run to determine why they're sick, under a federal rule published Wednesday. Privacy experts called the exception unnecessary, ripe for abuse and an override of state informed-consent laws. Health care workers will be free to run experimental tests on blood and other samples taken from people who have fallen sick as a result of a bioterrorist attack, bird flu outbreak, detonation of a dirty bomb or any other life-threatening public health emergency, according to the rule issued by the Food and Drug Administration. The rule took effect Wednesday but remains subject to public comment until Aug. 7. The FDA said it published the rule without first seeking comments because it would hinder the response to an outbreak of bird flu or other public health emergency.
They were loyal conservatives and Bush appointees. They fought a quiet battle to rein in the president's power in the war on terror. And they paid a price for it. James Comey...resigned as deputy attorney general in the summer of 2005. Comey's farewell speech...contained...an unusual passage. Comey thanked "people who came to my office, or my home, or called my cell phone late at night, to quietly tell me when I was about to make a mistake; they were the people committed to getting it right....Some of them did pay a price for their commitment to right, but they wouldn't have it any other way." These Justice Department lawyers, backed by their intrepid boss Comey, had stood up to the hard-liners, centered in the office of the vice president, who wanted to give the president virtually unlimited powers in the war on terror. Demanding that the White House stop using what they saw as farfetched rationales for riding rough-shod over the law and the Constitution, [they] fought to bring government spying and interrogation methods within the law. These government attorneys did not always succeed, but their efforts went a long way toward vindicating the principle of a nation of laws and not men. They did not see the struggle in terms of black and white but in shades of gray -- as painfully close calls with unavoidable pitfalls. They worried deeply about whether their principles might put Americans at home and abroad at risk. Their story...is a quietly dramatic profile in courage.
Note: If you want to understand the complexities involved behind the scenes at the top levels of US politics, I most highly recommend reading this entire article. It is five webpages in length.
In the guise of fighting terrorism and maintaining public order, Tony Blair's Government has quietly and systematically taken power from Parliament and the British people. The author charts a nine-year assault on civil liberties that reveals the danger of trading freedom for security. A new law...says that no one may demonstrate within a kilometre...of Parliament Square if they have not first acquired written permission. This effectively places the entire centre of British government...off-limits to the protesters. Blair...turns out to have an authoritarian streak. What is remarkable...is the harm his government has done to the unwritten British constitution in those nine years, without anyone really noticing, without the press objecting or the public mounting mass protests. Last year...I started to notice trends in Blair's legislation...to put in place all the necessary laws for total surveillance of society. The right not to be tried twice for the same offence...no longer exists. The presumption of innocence is compromised. The ID card [and] centralised database...will log and store details of every important action in a person's life. "You and I will carry them because we are upright citizens. But a terrorist ...will be carrying yours." Once a person is arrested he or she may be fingerprinted and photographed by the police and have a DNA sample removed with an oral swab - by force if necessary...before that person has been found guilty of any crime, whether it be dropping litter or shooting someone.
The U.S. military called no witnesses, withheld evidence from detainees and usually reached a decision within a day as it determined that hundreds of men detained at Guantanamo Bay were enemy combatants, according to a new report. The analysis of transcripts and records...found that hearings that determined whether a prisoner should remain in custody gave the accused little opportunity to contest allegations against him. These were not hearings. These were shams, said Mark Denbeaux, an attorney and Seton Hall University law professor who along with his son, Joshua, is the author of the report. The military held Combatant Status Review Tribunals for 558 detainees...between July 2004 and January 2005 and found all but 38 were enemy combatants. Handcuffed detainees appeared before a panel of three officers with no defense attorney, only a military personal representative. Representatives said nothing in the hearings 14 percent of the time and made no substantive comments in 30 percent. In 74 percent of the cases, the government denied requests to call witnesses who were detained at the prison. The report is based on transcripts...released earlier this year in response to a Freedom of Information Act lawsuit... The Military Commissions Act, which President Bush signed on Oct. 17, strips all non-U.S. citizens held under suspicion of being an enemy combatant of their right to challenge their detention in civilian courts with petitions of habeas corpus.
Investigators have revealed that targets of high-tech spying in Mexico included an international group of experts backed by the Organization of American States who had criticized the governments investigation into the disappearance of 43 students. Previous investigations by the internet watchdog group Citizen Lab found that the spyware had been directed at journalists, activists and opposition politicians in Mexico. But targeting foreign experts operating under the aegis of an international body marks an escalation of the scandal. The experts had diplomatic status, making the spying attempt even graver. The spyware, known as Pegasus, is made by the Israel-based NSO Group, which says it sells only to government agencies for use against criminals and terrorists. It turns a cellphone into an eavesdropper, giving snoopers the ability to remotely activate its microphone and camera and access its data. The spyware is uploaded when users click on a link in email messages. Citizen Lab said the spyware attempts against the international experts occurred in March 2016 as the group was preparing its final, critical report on the government investigation into the disappearances. The 43 students were detained by local police in the city of Iguala on 26 September 2014, and were turned over to a crime gang. Only one students remains have been identified. The experts criticized the governments conclusions, saying ... that government investigators had not looked into other evidence.
Note: Read the report by Citizen Lab at the University of Toronto for the details of these suspicious spyware attacks. For more along these lines, see concise summaries of deeply revealing news articles on corruption in government and the erosion of civil liberties.
Dozens of companies, non-profits and trade organizations including Apple, Google, and Facebook sent a letter [on July 18] pushing the Obama administration and Congress for more disclosures on the government's national security-related requests for user data. Together with LinkedIn, Yahoo!, Microsoft, Twitter and many others, the companies asked for more transparency of secret data gathering in the letter. Tech companies have been scrambling to assert their independence after documents leaked last month by former U.S. security contractor Edward Snowden suggested they had given the government direct access to their computers as part of the NSA's secret surveillance program called Prism. The classified nature of the data gathering has barred the participating companies from disclosing even their involvement, let alone the content of the requests. Some companies, including Facebook and Apple, in June struck an agreement with the government to release some information about the number of surveillance requests they receive. But they were limited to disclosing aggregate government requests for data without showing the split between surveillance and criminal requests, and only for a six-month period.
Note: For more on government and corporate privacy invasions, see the deeply revealing reports from reliable major media sources available here.
The U.S. government will have unmanned surveillance aircraft monitoring the whole southwest border with Mexico from September 1, as it ramps up border security in this election year. Homeland Security Secretary Janet Napolitano said U.S. Customs and Border Protection would begin flying a Predator B drone out of Corpus Christi, Texas, on [that date], extending the reach of the agency's unmanned surveillance aircraft across the length of the nearly 2,000 mile border with Mexico. "With the deployment of the Predator in Texas, we will now be able to cover the southwest border from the El Centro sector in California all the way to the Gulf of Mexico in Texas, providing critical aerial surveillance assistance to personnel on the ground," Napolitano said during a conference call. Earlier this month, President Barack Obama signed a $600 million bill that would fund some 1,500 new Border Patrol agents, customs inspectors and other law enforcement officials along the border, as well as paying for two more unmanned drones. The Predator B drones are made by defense contractor General Atomics. They carry equipment including sophisticated day and night vision cameras that operators use to detect drug and human smugglers, and can stay aloft for up to 30 hours at a time.
Note: How long will it be before aerial surveillance drones, now positioned over the southern border of the US, are deployed in other parts of the country?
A broad coalition of technology companies, including AT&T, Google and Microsoft, and advocacy groups from across the political spectrum said Tuesday that it would push Congress to strengthen online privacy laws to protect private digital information from government access. The group, calling itself the Digital Due Process coalition, said it wanted to ensure that as millions of people moved private documents from their filing cabinets and personal computers to the Web, those documents remain protected from easy access by law enforcement and other government authorities. The coalition, which includes the American Civil Liberties Union, the Electronic Frontier Foundation and the Center for Democracy and Technology, wants law enforcement agencies to use a search warrant approved by a judge or a magistrate rather than rely on a simple subpoena from a prosecutor to obtain a citizens online data. The group also said that it wanted to safeguard location-based information collected by cellphone companies and applications providers. forcement agencies and the Obama administration.
Note: For many key articles from reliable sources on privacy issues in the new age of surveillance, click here.
Despite President Barack Obama's vow to open government more than ever, the Justice Department is defending Bush administration decisions to keep secret many documents about domestic wiretapping, data collection on travelers and U.S. citizens, and interrogation of suspected terrorists. "The signs in the last few days are not ... encouraging," said Jameel Jaffer, an attorney for the American Civil Liberties Union, which filed several lawsuits seeking the Bush administration's legal rationales for warrantless domestic wiretapping and for its treatment of terrorism detainees. The documents sought in these lawsuits "are in many cases the documents that the public most needs to see," Jaffer said. "It makes no sense to say that these documents are somehow exempt from President Obama's directives." Groups that advocate open government, civil liberties and privacy were overjoyed that Obama on his first day in office reversed the FOIA policy imposed by Bush's first attorney general, John Ashcroft. Obama pledged "an unprecedented level of openness in government" and ordered new FOIA guidelines written with a "presumption in favor of disclosure." But Justice's actions in courts since then have cast doubt on how far the new administration will go. "This is not change," said ACLU executive director Anthony Romero. "President Obama's Justice Department has disappointingly reneged" on his promise to end "abuse of state secrets."
Note: For lots more on state secrecy from reliable, verifiable sources, click here.
U.S. spy agencies' sensitive data should soon be linked by Google-like search systems. Director of National Intelligence Mike McConnell has launched a sweeping technology program to knit together the thousands of databases across all 16 spy agencies. After years of bureaucratic snafus, intelligence analysts will be able to search through secret intelligence files the same way they can search public data on the Internet. Linking up the 16 agencies is the challenge at the heart of the job of director of national intelligence, created after 9/11. The new information program also is designed to include Facebook-like social-networking programs and classified news feeds. It includes enhanced security measures to ensure that only appropriately cleared people can access the network. The price tag is expected to be in the billions of dollars. The impact for analysts, Mr. McConnell says, "will be staggering." Not only will analysts have vastly more data to examine, potentially inaccurate intelligence will stand out more clearly, he said. Today, an analyst's query might scan only 5% of the total intelligence data in the U.S. government, said a senior intelligence official. Even when analysts find documents, they sometimes can't read them without protracted negotiations to gain access. Under the new system, an analyst would likely search about 95% of the data, the official said.
Note: For key reports from reliable sources on the hidden realities of the War on Terror, click here.
If you're reading this story on our Web site, I don't know what you did online before you reached this page. But your Internet provider might if it engages in something called deep packet inspection. That phrase may sound like what the Transportation Security Administration does to uncooperative airline passengers, but on the Internet it means a thorough and automatic inspection of online traffic -- not just where you've been but also what you've seen. Peering inside the digital packets of data zipping across the Internet -- in real time, for tens of thousands of users at once -- was commercially impractical until recently. But the ceaseless march of processing power has made it feasible. Unsurprisingly, companies have been trying to turn this potential into profit. By tracking users' Web habits this closely, they can gain a much more detailed picture of their interests -- and then display precisely targeted, premium-priced ads. The House Committee on Energy and Commerce recently asked dozens of providers to explain whether they had done any such testing. Most companies said they had yet to try the technology and had no plans to do so. (Although AT&T allowed that "if done properly," deep packet inspection "could prove quite valuable to consumers.") Taking these companies at their word, what's there to worry about? Systems such as deep packet inspection unnerve a lot of Internet users for sound reasons. One is, of course, the immensely greater surveillance they allow. Another concern is the difficulty of circumventing this constant tracking. The machinery of deep packet inspection hides out of reach in your provider's servers.
Several Internet and broadband companies have acknowledged using targeted-advertising technology without explicitly informing customers, according to letters released yesterday by the House Energy and Commerce Committee. The revelations came in response to a bipartisan inquiry of how more than 30 Internet companies might have gathered data to target customers. Some privacy advocates and lawmakers said the disclosures help build a case for an overarching online-privacy law. "Increasingly, there are no limits technologically as to what a company can do in terms of collecting information . . . and then selling it as a commodity to other providers," said committee member Edward J. Markey (D-Mass.). "Our responsibility is to make sure that we create a law that, regardless of the technology, includes a set of legal guarantees that consumers have with respect to their information." Markey said he and his colleagues plan to introduce legislation next year, a sort of online-privacy Bill of Rights, that would require that consumers must opt in to the tracking of their online behavior and the collection and sharing of their personal data. Ari Schwartz, vice president of the Center for Democracy and Technology, said lawmakers are beginning to understand the convergence across platforms. "People are starting to see: 'Oh, we have these different industries that are collecting the same types of information to profile individuals and the devices they use on the network," he said. "Internet. Cellphones. Cable. Any way you tap into the network, concerns are raised."
Note: For lots more on increasing threats to privacy from reliable sources, click here.
[Las Vegas], famous for being America's playground, has also become its security lab. Like nowhere else in the United States, Las Vegas has embraced the twin trends of data mining and high-tech surveillance, with arguably more cameras per square foot than any airport or sports arena in the country. Even the city's cabs and monorail have cameras. Some privacy advocates view the city as a harbinger of things to come. In secret rooms in casinos across Las Vegas, surveillance specialists are busy analyzing information about players and employees. Relying on thousands of cameras in nearly every cranny of the casinos, they evaluate ... behavior. They ping names against databases that share information with other casinos, sometimes using facial-recognition software to validate a match. And in the marketing suites, casino staffers track players' every wager, every win or loss, the better to target high-rollers for special treatment and low- and middle-rollers for promotions. "You could almost look at Vegas as the incubator of a whole host of surveillance technologies," said James X. Dempsey, policy director for the Center for Democracy and Technology. Those technologies, he said, have spread to other commercial venues: malls, stadiums, amusement parks. After Sept. 11, 2001, several airports tested facial-recognition software, with little success. But the government is continuing to invest in biometric technologies. "We often hear of the surveillance technology du jour, but what we're seeing now in America is a collection of surveillance technologies that work together," said Barry Steinhardt, the American Civil Liberties Union's technology and liberty project director. "It isn't just video surveillance or face recognition or license plate readers or RFID chips. It's that all these technologies are converging to create a surveillance society."
Note: For revealing major media reports of privacy risks and invasions, click here.
Frustrated by press leaks about its most sensitive electronic surveillance work, the secretive National Security Agency convened an unprecedented series of off-the-record "seminars" in recent years to teach reporters about the damage caused by such leaks and to discourage reporting that could interfere with the agency's mission to spy on America's enemies. The half-day classes featured high-ranking NSA officials highlighting objectionable passages in published stories and offering "an innocuous rewrite" that officials said maintained the "overall thrust" of the articles but omitted details that could disclose the agency's techniques, according to course outlines obtained by The New York Sun. Dubbed "SIGINT 101," using the NSA's shorthand for signals intelligence, the seminar was presented "a handful of times" between approximately 2002 and 2004. The syllabi make clear that the sessions, which took place at NSA headquarters in Fort Meade, Md., were conceived of ... as part of a campaign to limit the damage caused by leaks of sensitive intelligence. During one sensitive discussion, journalists were to be told they could not take any notes. The exact substitutions of language that the NSA proposed were deleted from the syllabi released to the Sun under the Freedom of Information Act. In 2005, following the publication of a New York Times story on a secret program for warrantless wiretapping ... Director of Central Intelligence Porter Goss crusaded against leaks at the CIA and later told a Senate committee that he hoped reporters would be called before grand juries to identify their sources. Attorney General Gonzales also discussed the "possibility" of prosecuting journalists who wrote stories based on leaked intelligence. The syllabi, which are marked as drafts, list presenters including the director of the NSA at the time, General Michael Hayden, [now director of the CIA].
The Bush administration's chief intelligence official said yesterday that President Bush authorized a series of secret surveillance activities under a single executive order in late 2001. The disclosure makes clear that a controversial National Security Agency program was part of a much broader operation than the president previously described. The disclosure by Mike McConnell [is] the first time that the administration has publicly acknowledged that Bush's order included undisclosed activities beyond the warrantless surveillance of e-mails and phone calls that Bush confirmed in December 2005. McConnell [disclosed] that the executive order following the Sept. 11, 2001 attacks included "a number of . . . intelligence activities" and that a name routinely used by the administration -- the Terrorist Surveillance Program -- applied only to "one particular aspect of these activities, and nothing more. This is the only aspect of the NSA activities that can be discussed publicly, because it is the only aspect of those various activities whose existence has been officially acknowledged." News reports ... have detailed a range of activities linked to the program, including the use of data mining to identify surveillance targets and the participation of telecommunication companies in turning over millions of phone records. Kate Martin ... of the Center for National Security Studies, said the new disclosures show that ... administration officials have "repeatedly misled the Congress and the American public" about the extent of NSA surveillance efforts. "They have repeatedly tried to give the false impression that the surveillance was narrow and justified," Martin said. "Why did it take accusations of perjury before the DNI disclosed that there is indeed other, presumably broader and more questionable, surveillance?"
Highly sensitive information about the religious beliefs, political opinions and even the sex life of Britons travelling to the United States is to be made available to US authorities when the European Commission agrees to a new system of checking passengers. The EC is in the final stages of agreeing a new Passenger Name Record system with the US which will allow American officials to access detailed biographical information about passengers entering international airports. Civil liberty groups warn it will have serious consequences for European passengers. In a strongly worded document drawn up in response to the plan that will affect the 4 million-plus Britons who travel to the US every year, the EU parliament said it 'notes with concern that sensitive data (ie personal data revealing racial or ethnic origin, political opinions, religious or philosophical beliefs, trade union membership, and data concerning the health or sex life of individuals) will be made available to the DHS.' The US will be able to hold the records of European passengers for 15 years compared with the current three year limit. The EU parliament said it was concerned the data would lead to 'a significant risk of massive profiling and data mining, which is incompatible with basic European principles and is a practice still under discussion in the US congress.' Peter Hustinx, the European Data Protection Supervisor, has written to the EC expressing his 'grave concern' at the plan, which he describes as 'without legal precedent' and one that puts 'European data protection rights at risk'. Hustinx warns: 'Data on EU citizens will be readily accessible to a broad range of US agencies and there is no limitation to what US authorities are allowed to do with the data.'
Walter Soehnge is a retired Texas schoolteacher. What got him so upset might seem trivial to some people who have learned to accept small infringements on their freedom as just part of the way things are in this age of terror-fed paranoia. The balance on their JCPenney Platinum MasterCard had gotten to an unhealthy level. So they sent in a large payment, a check for $6,522. And an alarm went off. A red flag went up. The Soehnges' behavior was found questionable. After sending in the check, they checked online to see if their account had been duly credited. They learned that the check had arrived, but the amount available for credit on their account hadn't changed. They were told, as they moved up the managerial ladder at the call center, that the amount they had sent in was much larger than their normal monthly payment. And if the increase hits a certain percentage higher than that normal payment, Homeland Security has to be notified. And the money doesn't move until the threat alert is lifted. Walter called television stations, the American Civil Liberties Union and me. And he went on the Internet to see what he could learn. He learned about changes in something called the Bank Privacy Act. "The more I'm on, the scarier it gets," he said. "It's scary how easily someone in Homeland Security can get permission to spy."
JOURNALISTS. Our attorney general is coming for us. On Sunday, Alberto Gonzales told ABC's "This Week" that he would consider prosecuting reporters who get their hands on classified information and break news about President Bush's terrorist surveillance program. "There are some statutes on the book which, if you read the language carefully, would seem to indicate that that is a possibility. We have an obligation to enforce those laws." Asked...if The New York Times should be prosecuted for its initial story on government surveillance without warrants, Gonzales said, "We are engaged now in an investigation about what would be the appropriate course of action." This is the same administration that...has already set the presidential record in claiming the authority to circumvent the law in more than 750 cases. Gonzales...issued the infamous "torture memo" that advised President Bush to throw the Geneva Convention into the trash can for detainees in the war on terror. Gonzales...helped the administration block and drag its feet on the release of presidential papers from Ronald Reagan and George H.W. Bush. Gonzales helped to withhold or delay highly classified documents from the president's own 9/11 Commission and from...the energy task force of Vice President Dick Cheney. The actions of Gonzales show how little the Bush administration promotes the rights of the press. With every pronouncement, freedom is disappearing, in incremental steps.
The IRS is quietly moving to loosen the once-inviolable privacy of federal income-tax returns. If it succeeds, accountants and other tax-return preparers will be able to sell information from individual returns - or even entire returns - to marketers and data brokers. The change is raising alarm among consumer and privacy-rights advocates. It was included in a set of proposed rules that the Treasury Department and the IRS published...where the official notice labeled them "not a significant regulatory action." The proposed rules...would require a tax preparer to obtain written consent before selling tax information. Critics call the changes a dangerous breach in personal and financial privacy. They say the requirement for signed consent would prove meaningless for many taxpayers, especially those hurriedly reviewing stacks of documents before a filing deadline.The IRS first announced the proposal in a news release the day before the official notice was published, headlined: "IRS Issues Proposed Regulations to Safeguard Taxpayer Information."
Back in December, 60 Minutes broadcast a now-notorious segment of pure access journalism in which they gullibly disseminated one false NSA claim after the next. The program claimed that Snowden is believed to still have access to 1.5 million classified documents he has not leaked. Ever since then, that Snowden stole 1.7 or 1.8 million documents from the NSA has been repeated over and over again by US media outlets as verified fact. The Washington Posts Walter Pincus, citing an anonymous official source, purported to tell readers that among the roughly 1.7 million documents he walked away with the vast majority of which have not been made public are highly sensitive, specific intelligence reports. Reuters frequently includes in its reports the unchallenged assertion that Snowden was believed to have taken 1.7 million computerized documents. In fact, that number is and always has been a pure fabrication, as even Keith Alexander admits. The claimed number has changed more times than one can count: always magically morphing into randomly chosen higher and scarier numbers. The reality, in the words of the General, is that the US Government really [doesn't know] what he actually took with him and they dont have an accurate way of counting. All they know is how many documents he accessed in his entire career at NSA, which is a radically different question from how many documents he took. But that hasnt stopped American media outlets from repeatedly affirming the inflammatory evidence-free claim that Snowden took 1.7 million documents.
Note: For more on the realities of intelligence agency operations, see the deeply revealing reports from reliable major media sources available here.
Washington looks set to wave through new cybersecurity legislation next week that opponents fear will wipe out decades of privacy protections at a stroke. The Cyber Intelligence Sharing and Protection Act (Cispa) will be discussed in the House of Representatives next week and already has the support of 100 House members. It will be the first such bill to go to a vote since the collapse of the Stop Online Piracy Act (Sopa) in January after global protests and a concerted campaign by internet giants such as Google, Wikipedia and Twitter. The author of the new bill, Mike Rogers, the Republican chair of the House intelligence committee, has said it is aimed at tracking the nefarious activities of hackers, terrorists and foreign states, especially China. But its critics charge the bill will affect ordinary citizens and overturn the privacy protections they now enjoy. Opponents fear the way it is currently drafted will open up ordinary citizens to unprecedented scrutiny. The bill uses the wording: "Notwithstanding any other provision of law," a phrase that if it became law would trump all existing legislation, according to critics. In one section, the bill defines "efforts to degrade, disrupt or destroy" a network as an area that would trigger a Cispa investigation. Opponents argue something as simple as downloading a large file a movie for example could potentially be defined as an effort to "degrade" a network. The bill also exempts companies from any liability for handing over private information.
Note: For lots more on government and corporate threats to civil liberties, click here.
President Obama has signed off on new security protocols for people flying to the United States, establishing a system that uses intelligence information and assessment of threats to identify passengers who could have links to terrorism. The system, which will be put in place this month, applies only to travelers flying into the United States. Officials said intelligence information from a variety of United States agencies would be made available to foreign airlines, whose employees and security officials would have wide latitude to stop passengers, or not. Currently, the only information typically checked before a passenger boards an airplane is the name, date of birth and nationality information found in a passport, which is compared against the terror watch lists. But the Homeland Security Department separately already collects much more information on the travel patterns of passengers headed to the United States, including other stops made on the way to an American airport, how the passenger paid for the ticket as well as other details contained in the reservation, like what hotel a passenger might be staying in, or if he or she is traveling alone.
Note: For many disturbing reports from major media sources on increasing governmental threats to civil liberties, click here.
The federal government has been using its system of border checkpoints to greatly expand a database on travelers entering the country by collecting information on all U.S. citizens crossing by land, compiling data that will be stored for 15 years and may be used in criminal and intelligence investigations. The Border Crossing Information system, disclosed last month by the Department of Homeland Security in a Federal Register notice, ... reflects the growing number of government systems containing personal information on Americans that can be shared for a broad range of law enforcement and intelligence purposes, some of which are exempt from some Privacy Act protections. While international air passenger data has long been captured this way, Customs and Border Protection agents only this year began to log the arrivals of all U.S. citizens across land borders, through which about three-quarters of border entries occur. The volume of people entering the country by land prevented compiling such a database until recently. But the advent of machine-readable identification documents, which the government mandates eventually for everyone crossing the border, has made gathering the information more feasible. Critics say the moves exemplify efforts by the Bush administration in its final months to cement an unprecedented expansion of data gathering for national security and intelligence purposes. The data could be used beyond determining whether a person may enter the United States. For instance, information may be shared with foreign agencies when relevant to their hiring or contracting decisions.
The Justice Department has proposed a new domestic spying measure that would make it easier for state and local police to collect intelligence about Americans, share the sensitive data with federal agencies and retain it for at least 10 years. Law enforcement agencies would be allowed to target groups as well as individuals, and to launch a criminal intelligence investigation based on the suspicion that a target is engaged in terrorism or providing material support to terrorists. They also could share results with a constellation of federal law enforcement and intelligence agencies, and others in many cases. Michael German, policy counsel for the American Civil Liberties Union, said the proposed rule may [permit] police to collect intelligence even when no underlying crime is suspected. German, an FBI agent for 16 years, said easing established limits on intelligence-gathering would lead to abuses against peaceful political dissenters. He pointed to reports in the past six years that undercover New York police officers infiltrated protest groups before the 2004 Republican National Convention; that California state agents eavesdropped on peace, animal rights and labor activists; and that Denver police spied on Amnesty International and others before being discovered. "If police officers no longer see themselves as engaged in protecting their communities from criminals and instead as domestic intelligence agents working on behalf of the CIA, they will be encouraged to collect more information," German said. "It turns police officers into spies on behalf of the federal government."
Note: For many disturbing reports on increasing threats to civil liberties from reliable sources, click here.
Health and life insurance companies have access to a powerful new tool for evaluating whether to cover individual consumers: a health "credit report" drawn from databases containing prescription drug records on more than 200 million Americans. Collecting and analyzing personal health information in commercial databases is a fledgling industry, but one poised to take off as the nation enters the age of electronic medical records. Some insurers have already begun testing systems that tap into not only prescription drug information, but also data about patients held by clinical and pathological laboratories. Privacy and consumer advocates fear [the trend] it is taking place largely outside the scrutiny of federal health regulators and lawmakers. The practice also illustrates how electronic data gathered for one purpose can be used and marketed for another -- often without consumers' knowledge, privacy advocates say. And they argue that although consumers sign consent forms, they effectively have to authorize the data release if they want insurance. "As health care moves into the digital age, there are more and more companies holding vast amounts of patients' health information," said Joy Pritts, research professor at Georgetown University's Health Policy Institute. "Most people don't even know these [companies] exist. Unfortunately the federal health privacy rule does not cover many of them." Tim Sparapani, senior legislative counsel at the American Civil Liberties Union, said, "We've got to stop these practices before the marketplace is fully developed and patients lose all control over their medical information."
Note: For lots more on increasing threats to privacy from reliable sources, click here.
Intelligence centers run by states across the country have access to personal information about millions of Americans, including unlisted cellphone numbers, insurance claims, driver's license photographs and credit reports, according to a document obtained by The Washington Post. One center also has access to top-secret data systems at the CIA, the document shows, though it's not clear what information those systems contain. Dozens of the organizations known as fusion centers were created after the Sept. 11, 2001, terrorist attacks. The centers use law enforcement analysts and sophisticated computer systems to compile, or fuse, disparate tips and clues and pass along the refined information to other agencies. Though officials have publicly discussed the fusion centers' importance to national security, they have generally declined to elaborate on the centers' activities. But a document that lists resources used by the fusion centers shows how a dozen of the organizations in the northeastern United States rely far more on access to commercial and government databases than had previously been disclosed. The list of information resources was part of a survey conducted last year, officials familiar with the effort said. It shows that, like most police agencies, the fusion centers have subscriptions to private information-broker services that keep records about Americans' locations, financial holdings, associates, relatives, firearms licenses and the like. "Fusion centers have grown, really, off the radar screen of public accountability," said Jim Dempsey, vice president for public policy at the Center for Democracy and Technology, a nonpartisan watchdog group in the District. "Congress and the state legislatures need to get a handle over what is going on at all these fusion centers."
Note: For further disturbing reports on threats to privacy, click here.
Several thousand law enforcement agencies are creating the foundation of a domestic intelligence system through computer networks that analyze vast amounts of police information. As federal authorities struggled to meet information-sharing mandates after the Sept. 11, 2001 terrorist attacks, police agencies from Alaska and California to the Washington region poured millions of ... records into shared digital repositories called data warehouses, giving investigators and analysts new power to discern links among people, patterns of behavior and other hidden clues. Those network efforts will begin expanding further this month, as some local and state agencies connect to a fledgling Justice Department system called the National Data Exchange, or N-DEx. The expanding police systems illustrate the prominent roles that private companies play in homeland security and counterterrorism efforts. They also underscore how the use of new data -- and data surveillance -- is evolving faster than the public's understanding or the laws intended to check government power and protect civil liberties. Three decades ago, Congress imposed limits on domestic intelligence activity after revelations that the FBI, Army, local police and others had misused their authority for years to build troves of personal dossiers and monitor political activists and other law-abiding Americans. Since those reforms, police and federal authorities have observed a wall between law enforcement information-gathering, relating to crimes and prosecutions, and more open-ended intelligence that relates to national security and [politics]. That wall is fast eroding following the passage of laws expanding surveillance authorities, the push for information-sharing networks, and the expectation that local and state police will play larger roles.
Note: For many revealing reports from reliable sources of serious threats to civil liberties, click here.
A little-remarked feature of pending legislation on domestic surveillance has provoked alarm among university and public librarians who say it could allow federal intelligence-gathering on library patrons without sufficient court oversight. Draft House and Senate bills would allow the government to compel any "communications service provider" to provide access to e-mails and other electronic information within the United States. The Justice Department has previously said that "providers" may include libraries, causing three major university and library groups to worry that the government's ability to monitor people targeted for surveillance without a warrant would chill students' and faculty members' online research activities. "It is fundamental that when a user enters the library, physically or electronically," said Jim Neal, the head librarian at Columbia University, "their use of the collections, print or electronic, their communications on library servers and computers, is not going to be subjected to surveillance unless the courts have authorized it." The librarians said their concern about such monitoring is rooted in recent history. In the summer of 2005, FBI agents handed an administrative subpoena called a national security letter (NSL) to a Connecticut librarian, and demanded subscriber, billing and other information on patrons who used a specific computer at a branch library. NSLs can be approved by certain FBI agents without court approval. The agents ordered the librarian to keep the demand secret. But he refused to produce the records, and his employer filed suit, challenging the gag order. A federal judge in September 2005 declared the gag order unconstitutional. The Association of Research Libraries, ... the American Library Association ... and the Association of American Universities ... each say they seek to amend the draft bills to make clear that the term "communications provider" does not include libraries.
Note: For more eye-opening reports from major media sources on the erosion of civil liberties, click here.
Two new questions arise, courtesy of the latest advancement in cellphone technology: Do you want your friends, family, or colleagues to know where you are at any given time? And do you want to know where they are? Obvious benefits come to mind. Parents can take advantage of the Global Positioning System chips embedded in many cellphones to track the whereabouts of their phone-toting children. And for teenagers and 20-somethings, who are fond of sharing their comings and goings on the Internet, youth-oriented services like Loopt and Buddy Beacon are a natural next step. But ... if G.P.S. [makes] it harder to get lost, new cellphone services are now making it harder to hide. There are massive changes going on in society, particularly among young people who feel comfortable sharing information in a digital society, said Kevin Bankston, a staff lawyer at the Electronic Frontier Foundation. We seem to be getting into a period where people are closely watching each other, he said. There are privacy risks we havent begun to grapple with. What if a boss asks an employee to use the service? Almost 55 percent of all mobile phones sold today in the United States have the technology that makes such friend- and family-tracking services possible. Consumers can turn off their service, making them invisible to people in their social-mapping network. Still, the G.P.S. service embedded in the phone means that your whereabouts are not a complete mystery. There is a Big Brother component, said Charles S. Golvin, a wireless analyst. The thinking goes that if my friends can find me, the telephone company knows my location all the time, too.
Note: For revealing major media reports of privacy risks and invasions, click here.
The U.S. government is collecting electronic records on the travel habits of millions of Americans who fly, drive or take cruises abroad, retaining data on the persons with whom they travel or plan to stay, the personal items they carry during their journeys, and even the books that travelers have carried, according to documents obtained by a group of civil liberties advocates and statements by government officials. The personal travel records are meant to be stored for as long as 15 years, [by] the Department of Homeland Security's ... Automated Targeting System. But new details about the information being retained suggest that the government is monitoring the personal habits of travelers more closely than it has previously acknowledged. The details were learned when a group of activists requested copies of official records on their own travel. Those records included a description of a book on marijuana that one of them carried and small flashlights bearing the symbol of a marijuana leaf. Civil liberties advocates have alleged that the type of information preserved by the department raises alarms about the government's ability to intrude into the lives of ordinary people. The millions of travelers whose records are kept by the government are generally unaware of what their records say, and the government has not created an effective mechanism for reviewing the data and correcting any errors, activists said. The activists alleged that the data collection effort, as carried out now, violates the Privacy Act, which bars the gathering of data related to Americans' exercise of their First Amendment rights, such as their choice of reading material or persons with whom to associate. They also expressed concern that such personal data could one day be used to impede their right to travel.
One in three people are expected not to cooperate with identity card checks, Home Office papers from 2004 suggest. The working assumptions were revealed in the documents published by the Department for Work and Pensions under the Freedom of Information laws. They show that the assumption was that the cards, due to be introduced on a voluntary basis from 2008, would become compulsory to own - though not carry - in 2014. Lib Dem MP Mark Oaten had asked for the information to be made public when he was the party's home affairs spokesman in 2004. The department had resisted his request, which came under the Freedom of Information Act. But the department was ordered to release the data by the Information Commissioner - a decision which was subsequently backed by the Information Tribunal.
Note: Why do you think the government was so keen on keeping this information secret? For more, click here.
The Pentagon has its own domestic spying program. Even its leaders say the outfit may have gone too far. Late on a June afternoon in 2004, a motley group of about 10 peace activists showed up outside the Houston headquarters of Halliburton, the giant military contractor once headed by Vice President Dick Cheney. The demonstrators wore papier-mache masks and handed out free peanut-butter-and-jelly sandwiches to Halliburton employees as they left work. The idea, according to organizer Scott Parkin, was to call attention to allegations that the company was overcharging on a food contract for troops in Iraq. To U.S. Army analysts at the top-secret Counterintelligence Field Activity (CIFA), the peanut-butter protest was regarded as a potential threat to national security. A Defense document shows that Army analysts wrote a report on the Halliburton protest and stored it in CIFA's database. There are now questions about whether CIFA exceeded its authority and conducted unauthorized spying on innocent people and organizations. The deputy Defense secretary now acknowledges that...reports may have contained information on U.S. citizens and groups that never should have been retained. The number of reports with names of U.S. persons could be in the thousands, says a senior Pentagon official.
The Government is creating a system of "mass public surveillance" capable of tracking every adult in Britain without their consent, MPs say. They warn that people who have never committed a crime can be "electronically monitored" without their knowledge. Biometric facial scans, which will be compulsory with ID cards, are to be put on a national database which can then be matched with images from CCTV. The database of faces will enable police and security services to track individuals regardless of whether they have broken the law. CCTV surveillance footage from streets, shops and even shopping centres could be cross-referenced with photographs of every adult in the UK once the ID cards Bill becomes law. Biometric facial scans, iris scans and fingerprints of all adults in the UK will be stored on a national database. Civil liberties groups say the plans are a "dangerous" threat to people's privacy. Mark Oaten, the Liberal Democrat home affairs spokesman, said the plans were being brought in by the Government without informing the public.
Looking for signs of "stress, fear and deception" among the hundreds of passengers shuffling past him at Orlando International Airport one day last month, security screener Edgar Medina immediately focused on four casually dressed men trying to catch a flight to Minneapolis. One of the men, in particular, was giving obvious signs of trying to hide something, Medina said. After obtaining the passengers' ID cards and boarding passes, the Transportation Security Administration officer quickly determined the men were illegal immigrants traveling with fake Florida driver's licenses. They were detained. The otherwise mundane arrests Aug. 13 illustrated an increasingly popular tactic in the government's effort to fight terrorism: detecting lawbreakers or potential terrorists by their behavior. The TSA has embraced the strategy, training 600 of its screeners ... in detection techniques. The TSA's teams are the most publicly acknowledged effort by the government or the private sector to come up with strategies and technology to detect lawbreakers or terrorists before they commit a crime. Other technologies under development or being deployed include machines that detect stress in voices and software that scans video images to match the faces of passengers with those of known terrorists. The government is testing other technology that can see through clothing with ... electromagnetic waves. TSA's growing reliance on detecting behavior and the close study of passengers' expressions concerns civil liberties groups and members of Congress. "The problem is behavioral characteristics will be found where you look for them," said John Reinstein, legal director of the American Civil Liberties Union of Massachusetts.
Across the country, police are using GPS devices to snare [criminal suspects], often without a warrant or court order. Privacy advocates said tracking suspects electronically constitutes illegal search and seizure, violating Fourth Amendment rights of protection against unreasonable searches and seizures, and is another step toward George Orwell's Big Brother society. With the ... ever-declining cost of the technology, many analysts believe that police will increasingly rely on GPS ... and that the public will hear little about it. "I've seen them in cases from New York City to small towns -- whoever can afford to get the equipment and plant it on a car," said John Wesley Hall, president of the National Association of Criminal Defense Lawyers. "And of course, it's easy to do. You can sneak up on a car and plant it at any time." Details on how police use GPS usually become public when the use of the device is challenged in court. Leibig said GPS should be held to a different standard because it provides greater detail. "While it may be true that police can conduct surveillance of people on a public street without violating their rights, tracking a person everywhere they go and keeping a computer record of it for days and days without that person knowing is a completely different type of intrusion," he said. Barry Steinhardt, director of the American Civil Liberties Union's technology and liberty program, considers GPS monitoring, along with license plate readers, toll transponders and video cameras with face-recognition technology, part of the same trend toward "an always-on, surveillance society."
Note: For lots more on threats to privacy from major media sources, click here.
President Bush, again defying Congress, says he has the power to edit the Homeland Security Department's reports about whether it obeys privacy rules while handling background checks, ID cards and watchlists. In the law Bush signed Wednesday, Congress stated no one but the privacy officer could alter, delay or prohibit the mandatory annual report on Homeland Security department activities that affect privacy, including complaints. But Bush, in a signing statement attached to the agency's 2007 spending bill, said he will interpret that section "in a manner consistent with the President's constitutional authority to supervise the unitary executive branch." The American Bar Association and members of Congress have said Bush uses signing statements excessively as a way to expand his power. Bush's signing statement Wednesday challenges several other provisions in the Homeland Security spending bill. Bush, for example, said he'd disregard a requirement that the director of the Federal Emergency Management Agency must have at least five years experience and "demonstrated ability in and knowledge of emergency management and homeland security."
Attorney General Alberto R. Gonzales told the Senate Judiciary Committee on Tuesday that President Bush had personally decided to block the Justice Department ethics unit from examining the role played by government lawyers in approving the National Security Agency's domestic eavesdropping program. Mr. Gonzales made the assertion in response to questioning from Senator Arlen Specter, Republican of Pennsylvania and chairman of the committee. Mr. Specter said the Office of Professional Responsibility at the Justice Department had to call off an investigation into the conduct of department lawyers who evaluated the surveillance program because the unit was denied clearance to review classified documents. Representative Zoe Lofgren...said Tuesday that she was shocked that Mr. Bush had blocked the clearances of lawyers from that office. "The president's latest action shows that he is willing to be personally involved in the cover-up of suspected illegal activity," Ms. Lofgren said.
The attorney general's startling revelation that President Bush personally blocked a Justice Department investigation into the administration's controversial secret domestic spying programs hasn't gotten the attention it deserves. Bush's move -- denying the requisite security clearances to attorneys from the department's ethics office -- is unprecedented in that office's history. It also comes in stark contrast to the enthusiastic way in which security clearances were dished out to...those charged with finding out who leaked information about the program to the press. Time and time again, Bush and his aides have selectively leaked or declassified secret intelligence findings that served their political agenda -- while aggressively asserting the need to keep secret the information that would tend to discredit them. Some legal experts and members of Congress who have questioned the legality of the NSA program said Bush's move to quash the Justice probe represents a politically motivated interference in Justice Department affairs. The government has in effect curtailed an investigation of itself and hardly anyone has noticed. It has not caused much interest in Congress, or on the nation's editorial pages, or the even in the blogosphere, which takes pride in causing a stir about things that should but nobody else has yet taken notice."
Note: As noted in our key summary Building a Brighter Future, "Secrecy leads to control through preventing the exposure of hidden agendas, and through breeding distrust, suspicion, and paranoia in the world."
We bet that former Health and Human Services Secretary Tommy Thompson wishes he had gone to work for Breyers or Hershey's. To set a good example, he's preparing to consume his new company's product--VeriChip Corp's flesh-embedded medical radio chip. "It doesn't cause any pain," he assures us, explaining that a rice-size chip will be inserted into his arm. The chip stores coding that makes the user's health records available worldwide. Hospitals wave a radio wand over the arm to get the info. "People are dying all the time," he says, "because they can't access their medical information overseas."
Only a tiny fraction of Americans 7 percent, according to a recent survey by The Ponemon Institute change any behaviors in an effort to preserve their privacy. Few people turn down a discount at toll booths to avoid using the EZ-Pass system that can track automobile movements. And few turn down supermarket loyalty cards. Privacy will remain in the headlines in the months to come, as states implement the federal governments Real ID Act, which will effectively create a national identification program by requiring new high-tech standards for drivers licenses and ID cards. The right to be left alone is a decidedly conservative -- even Libertarian -- principle. People are now well aware there are video cameras and Internet cookies everywhere, [yet] there is abundant evidence that people live their lives ignorant of the monitoring. People write e-mails and type instant messages they never expect anyone to see. Just ask Mark Foley or even Bill Gates, whose e-mails were a cornerstone of the Justice Departments antitrust case against Microsoft. It is also impossible to deny that Americans are now being watched more than at any time in history. But there is another point in the discussion about which there is little disagreement: The debate over how much privacy we are willing to give up never occurred.
The Bush administration told a judge in Detroit that the president's warrantless domestic spying is legal and constitutional, but refused to say why. The judge should just take his word for it, the lawyer said, because merely talking about it would endanger America. Today, Senator Arlen Specter wants his Judiciary Committee to take an even more outlandish leap of faith for an administration that has shown it does not deserve it. Mr. Specter wants the committee to approve a bill he drafted that tinkers dangerously with the rules on wiretapping, even though the president has said the law doesn't apply to him anyway, and even though Mr. Specter and most of the panel are just as much in the dark as that judge in Detroit. The bill could well diminish the power of the Foreign Intelligence Surveillance Act, known as FISA, which was passed in 1978 to prevent just the sort of abuse that Mr. Bush's program represents. This is not a time to offer the administration a chance to steamroll Congress into endorsing its decision to ignore the 1978 intelligence act and shred constitutional principles on warrants and on the separation of powers. This is a time for Congress to finally hold Mr. Bush accountable for his extralegal behavior and stop it.
Important Note: Explore our full index to revealing excerpts of key major media news articles on several dozen engaging topics. And don't miss amazing excerpts from 20 of the most revealing news articles ever published.