Engineered Pandemic Flu, Hacking US Elections, Syria's Secret Library
August 16, 2016
Dear friends,

Below are key excerpts of revealing news articles on how a US university scientist deliberately engineered a strain of pandemic flu to evade the human immune system, irrefutable evidence that US elections could be manipulated by many kinds of hacking, the revelation that the DEA has unaccountably seized more than $209 million from at least 5,200 people while building successful criminal cases against very few of these people, and more.
Read also wonderfully inspiring articles on the secret library in Syria where people risk life and limb to protect and share books while under siege by pro-Assad forces, the new website Steemit that aims to challenge corporate dominance of social media, curbing food waste by rescuing leftovers and selling these to consumers at a discount, and more. You can also skip to this section now.
Each excerpt is taken verbatim from the major media website listed at the link provided. If any link fails, see this page. The most important sentences are highlighted. And don't miss the "What you can do" section below the summaries. By educating ourselves and spreading the word, we can and will build a brighter future.
With best wishes for a transformed world,
Mark Bailey and Fred Burks for PEERS and WantToKnow.info
Special note: Read a revealing essay by the wife of Dr. Mercola on the over 50 holistic doctors who have died under strange circumstances in the last year. The UK's popular Express published an article on Hollywood star Chuck Norris talking about chemtrails. Learn how history changes over time in this essay on the roots of the Cherokees. Check out this cool article from the New Yorker on the amazing interconnectedness of plant life. Watch an intriguing 10-minute video of a Japanese qigong master who subdues a small herd of buffalo and more.
Quote of the week: "After the game, the King and the Pawn go into the same box." ~~ Italian proverb
Video of the week: Watch a powerfully revealing 22-minute Bill Moyers clip titled "The Secret Government" Though made almost 30 years ago, it is as potent for today's world as back then.
Exclusive: Controversial US scientist creates deadly new flu strain for pandemic research
June 30, 2014, The Independent (One of the UK's leading newspapers)
http://www.independent.co.uk/news/science/exclusive-controversial-us-scientist-creates...
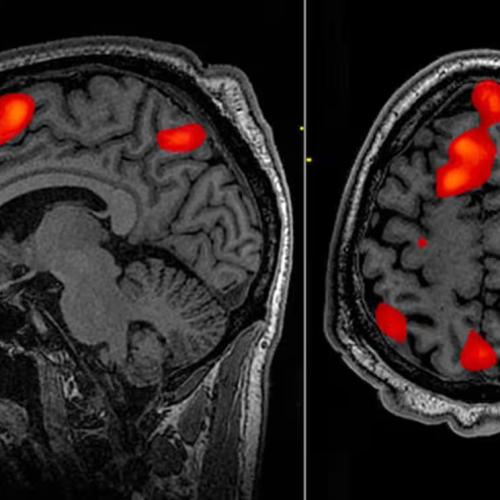
A controversial scientist who carried out provocative research on making influenza viruses more infectious has completed his most dangerous experiment to date by deliberately creating a pandemic strain of flu that can evade the human immune system. Yoshihiro Kawaoka of the University of Wisconsin-Madison has genetically manipulated the 2009 strain of pandemic flu in order for it to “escape” the control of the immune system’s neutralising antibodies, effectively making the human population defenceless against its reemergence. Most of the world today has developed some level of immunity to the 2009 pandemic flu virus. However ... Professor Kawaoka intentionally set out to see if it was possible to convert it to a pre-pandemic state in order to analyse the genetic changes involved. Professor Kawaoka’s work had been cleared by Wisconsin’s Institutional Biosafety Committee, but some members of the committee were not informed about details of the antibody study ... and have voiced concerns about the direction, oversight and safety of his overall research on flu viruses. “I have met Professor Kawaoka in committee and have heard his research presentations and honestly it was not re-assuring,” said Professor Tom Jeffries, a dissenting member of the 17-person biosafety committee. This is the first time that someone has taken a strain of influenza virus, called H1N1, known to have caused a global epidemic, in other words a “pandemic”, and deliberately mutated it many times over.
Is it that Easy to Hack an Election?
August 5, 2016, MSN News/Politico
http://www.msn.com/en-us/money/videos/is-it-that-easy-to-hack-an-election/vp-BBvi23c
Princeton professor Andrew Appel decided to hack into a voting machine. He bought one online. Appel parted with $82 and became the owner of ...the Sequoia AVC Advantage, one of the oldest and vulnerable, electronic voting machines in the United States. He summoned a graduate student named Alex Halderman, who could pick the machine’s lock in seven seconds. Clutching a screwdriver, [Appel then] deftly wedged out the four ROM chips - they weren’t soldered into the circuit board, as sense might dictate - making it simple to replace them with one of his own: A version of modified firmware that could throw off the machine’s results, subtly altering the tally of votes, never to betray a hint to the voter. The attack was concluded in minutes. Elections could be vulnerable at myriad strike points, among them the software that aggregates the precinct vote totals, and the voter registration rolls that are increasingly digitized. But the threat, the cyber experts say, starts with the machines that tally the votes and crucially keep a record of them - or, in some cases, don't. It’s not just the voting machines themselves - it’s the desktop and laptop computers that election officials use. And the computers that aggregate the results together from all of the optical scans. If any of those get hacked, it could could significantly disrupt the election. Hackers this year have [already] targeted voter registration rolls in Illinois and possibly Arizona, another attack highlighted by the Princeton alums.
Note: For the text of the video at the above link and more, see this webpage. For more along these lines, see concise summaries of deeply revealing elections corruption news articles from reliable major media sources. Then explore the excellent, reliable resources provided in our Elections Information Center.
DEA regularly mines Americans' travel records to seize millions in cash
August 11, 2016, USA Today
http://www.usatoday.com/story/news/2016/08/10/dea-travel-record-airport-seizures...
Federal drug agents regularly mine Americans’ travel information to profile people who might be ferrying money for narcotics traffickers - though they almost never use what they learn to make arrests or build criminal cases. Instead, that targeting has helped the Drug Enforcement Administration seize a small fortune in cash. The DEA surveillance is separate from the vast and widely-known anti-terrorism apparatus. DEA units assigned to patrol 15 of the nation’s busiest airports seized more than $209 million in cash from at least 5,200 people over the past decade “They count on this as part of the budget,” said Louis Weiss, a former [DEA group] supervisor. “Basically, you’ve got to feed the monster.” Federal law gives the government broad powers to seize cash and other assets if agents have evidence that they are linked to crime. That process, commonly known as asset forfeiture, has come under fire ... after complaints that police were using the law as a way to raise money rather than to protect the public or prevent crime. Court records show agents and informants flagged travelers for questioning based on whether they were traveling with one-way tickets, had paid in cash, had listed a non-working phone number on the reservation or had checked luggage. Agents said Zane Young fit that profile when they ... seized $36,000 from his bags. Young’s lawyer, Thomas Baker, said in a court filing that the drug agency’s profile was “vague, ambiguous, overbroad, and can be manipulated to include just about anyone.”
Note: Read about how the DEA stole a young man's life savings without ever charging him with a crime. For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the erosion of civil liberties.
FBI Agent Apparently Egged on ‘Draw Muhammad’ Shooter
August 4, 2016, Daily Beast
http://www.thedailybeast.com/articles/2016/08/04/fbi-agent-apparently-egged-on-texas...
Days before an ISIS sympathizer attacked a cartoon contest in Garland, Texas, he received a text from an undercover FBI agent. “Tear up Texas,” the agent messaged Elton Simpson days before he opened fire at the Draw Muhammad event, according to an affidavit filed in federal court Thursday. “U know what happened in Paris,” Simpson responded. “So that goes without saying ... No need to be direct.” That revelation comes amidst a national debate about the use of undercover officers and human sources in terrorism cases. The texts were included in the indictment, released Thursday, of Erick Jamal Hendricks. He was charged with conspiring to provide material support to ISIS. [Hendricks] tried to recruit other Americans to form an ISIS cell on secret compounds and introduced an undercover agent to one of the Draw Muhammad attackers, according to the FBI. But Hendricks did more than make a connection. According to the court papers, he asked the undercover officer about the Draw Muhammad event’s security, size, and police presence, during the event, according to an affidavit filed in court. FBI spokeswoman Carol Cratty hung up on The Daily Beast after being asked about the “tear up Texas” text. But shortly after that exchange, Simpson and his accomplice, Nadir Soofi, drove up to the contest and opened fire. Both men were killed in the altercation, but Hendricks would remain free for another year. Every major U.S. attack was linked to FBI investigation before it happened.
Note: The FBI has been stepping up its use of stings in ISIS cases. Read how an FBI mole posing as a potential lover recently convinced a man to become a terrorist. If terrorism is such a grave threat in the US, why does the FBI have to manufacture "terrorist" plots and then exaggerate its anti-terrorism success?
This Company Has Built a Profile on Every American Adult
August 5, 2016, BloombergBusinessweek
http://www.bloomberg.com/news/articles/2016-08-05/this-company-has-built-a-profile-on...
For more than a decade, professional snoops have been able to search troves of ... addresses, DMV records, photographs of a person’s car - and condense them into comprehensive reports costing as little as $10. Now they can combine that information with the kinds of things marketers know about you, such as which politicians you donate to, what you spend on groceries, and whether it’s weird that you ate in last night, to create a portrait of your life and predict your behavior. IDI, a year-old company in the so-called data-fusion business, is the first to centralize and weaponize all that information for its customers. Chief Executive Officer Derek Dubner says the system isn’t waiting for requests from clients - it’s already built a profile on every American adult, including young people who wouldn’t be swept up in conventional databases, which only index transactions. These personal profiles include all known addresses, phone numbers, and e-mail addresses; every piece of property ever bought or sold, plus related mortgages; past and present vehicles owned; criminal citations, from speeding tickets on up; voter registration; hunting permits; and names and phone numbers of neighbors. The reports also include photos of cars taken by private companies using automated license plate readers - billions of snapshots tagged with GPS coordinates and time stamps to help PIs surveil people or bust alibis. IDI also runs two coupon websites ... that collect purchasing and behavioral data.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corporate corruption and the erosion of privacy.
Whipped, kicked, beaten: Illinois workers describe abuse of hogs
August 4, 2016, Chicago Tribune
http://www.chicagotribune.com/news/watchdog/pork/ct-pig-farms-abuse-met-20160802...
Weeks after taking a job as a breeding technician at Eagle Point Farms, an anguished Sharee Santorineos sat down and wrote a three-page whistleblower complaint. "I seen pigs that are pregnant beat with steel bars," said her letter to the Illinois Bureau of Animal Health and Welfare. Santorineos knows about raising animals. At a friend's rural Illinois farmhouse, she grows pigs and poultry that they eventually will have slaughtered. Like other worker allegations about animal abuse in Illinois' 900-plus hog confinement facilities, Santorineos' account went nowhere. The state has regularly discounted or dismissed such worker complaints, a Tribune investigation has found. In the Illinois hog confinements that send 12 million pigs to market annually, the bureau did not find a single animal welfare infraction or violation during the past five years. A lack of inspectors - the bureau has just six - contributes to the scant enforcement, while weak Illinois and federal livestock protection laws do little to safeguard animals. In on-the-record interviews, Santorineos and more than a dozen other Illinois swine-confinement workers told the Tribune they witnessed fellow employees whip pigs with metal rods and gouge them with pliers and ballpoint pens to hurry the animals from one stall to the next or onto the trucks that took them to slaughter. They described employees abusing pigs for amusement and encouraging colleagues to take out their frustrations on the animals.
Note: For more along these lines, see concise summaries of deeply revealing news articles on corruption in government and in the food system.
Researchers or Corporate Allies? Think Tanks Blur the Line
August 7, 2016, New York Times
http://www.nytimes.com/2016/08/08/us/politics/think-tanks-research-and-corporate...
Think tanks, which position themselves as “universities without students,” have power in government policy debates because they are seen as researchers independent of moneyed interests. But in the chase for funds, think tanks are pushing agendas important to corporate donors, at times blurring the line between researchers and lobbyists. And they are doing so while reaping the benefits of their tax-exempt status, sometimes without disclosing their connections to corporate interests. On issues as varied as military sales to foreign countries, international trade, highway management systems and real estate development, think tanks have frequently become vehicles for corporate influence and branding campaigns. “This is about giant corporations who figured out that by spending, hey, a few tens of millions of dollars, if they can influence outcomes here in Washington, they can make billions of dollars,” said Senator Elizabeth Warren, Democrat of Massachusetts, a frequent critic of undisclosed Wall Street donations to think tanks. Washington has seen a proliferation of think tanks, particularly small institutions with narrow interests tied to specific industries. At the same time, the brand names of the field have experienced explosive growth. [The Brookings Institution]’s annual budget has doubled in the last decade, to $100 million. The American Enterprise Institute is spending at least $80 million on a new headquarters in Washington, not far from where the Center for Strategic and International Studies built a $100 million office tower.
Note: Read more about how big money buys off institutions democracy depends on. For more along these lines, see concise summaries of deeply revealing news articles on corruption in government and in the corporate world.
Police will be required to report officer-involved deaths under new US system
August 8, 2016, The Guardian (One of the UK's leading newspapers)
https://www.theguardian.com/us-news/2016/aug/08/police-officer-related-deaths-department...
Police departments will be required to give the US justice department full details of deadly incidents involving their officers each quarter, under a new government system for counting killings by police that was influenced by the Guardian. Announcing a new program for documenting all “arrest-related deaths”, federal officials said they would actively work to confirm fatal cases seen in media reports and other open sources rather than wait for departments to report them voluntarily. The new system, which aims to replace a discredited count by the FBI, mirrors that of The Counted, an ongoing Guardian effort to document every death caused by law enforcement officers. Writing in the Federal Register, Department of Justice officials said their new program should increase transparency around the use of force by police and improve accountability for the actions of individual officers. The federal government has kept no comprehensive record of killings by police officers, even as a series of controversial deaths set off unrest in cities across the country over the past two years. An annual voluntary count by the FBI of fatal shootings by officers has recorded only about half the true number. The new system is being overseen by the department’s bureau of justice statistics (BJS). It would, like the Guardian’s, document deaths caused by physical force, Taser shocks and some vehicle crashes caused by law enforcement in addition to fatal shootings by officers.
Note: For more along these lines, see concise summaries of deeply revealing police corruption news articles from reliable major media sources.
How the US Spies on Medical Nonprofits and Health Defenses Worldwide
August 10, 2016, The Intercept
https://theintercept.com/2016/08/10/how-the-u-s-spies-on-medical-nonprofits-and-health...
As part of an ongoing effort to “exploit medical intelligence,” the National Security Agency teamed up with the military-focused Defense Intelligence Agency to extract “medical SIGINT” from the intercepted communications of nonprofit groups starting in the early 2000s, a top-secret document shows. Medical intelligence can include information about disease outbreaks; the ability of a foreign regime to respond to chemical, biological, and nuclear attacks; the capabilities of overseas drugs companies; advances in medical technology; medical research, and the medical response capabilities of various governments, according to the document and others like it, provided by NSA whistleblower Edward Snowden. One of the more prominent examples of focused medical spying came in 2010, when the agency crafted a plan to stow tracking devices with medical supplies bound for an ill Osama bin Laden in order to locate the terrorist leader. One article from August 2003 identifies an NSA project to keep an eye on the evolution of biotechnology in various countries. “Can we ... determine the specific features that would distinguish a Bio Warfare Program from a benign civilian pharmaceutical production effort?” the author wrote, identifying a “suspect Iranian [biological warfare] facility” as a target for inspection. Medical intelligence gathering has continued since then, according to the so-called “black budget” proposed for the 2013 fiscal year, published in February 2012.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and terrorism.
Piltdown Man: Scientists finally get to the bottom of notorious scientific forgery
August 11, 2016, Christian Science Monitor
http://www.csmonitor.com/Science/2016/0811/Piltdown-Man-Scientists-finally-get-to-the...
Piltdown Man was heralded as the missing link, connecting humans to their ape ancestors. Discovered in England in 1912, the fossils were exactly what British paleontologists were hoping to find. Newspapers proclaimed: "Missing Link Found - Darwin's Theory Proved." In 1953, scientists concluded that Piltdown Man was an elaborate fraud, compiled of pieces of a human skull and orangutan jaw and teeth. Now ... scientists have definitively narrowed the blame down to just one person: Charles Dawson, an amateur archaeologist and fossil collector. “The shocking thing was how many people accepted it because it fell right into their belief system,” [said] David Begun, a paleoanthropologist professor at the University of Toronto. “Dawson put together this fraudulent fossil to fit the preconceptions of the time." Anthropologists hadn't pinned down where humans first arose, so it was still possible to link them back to Europe. More recent discoveries of human ancestors have immediately raised red flags because they upended people's expectations, including the enigmatic "hobbit" from Indonesia, and strange, small human ancestors in the Rising Star cave in South Africa. But those excavations were carefully documented and the specimens were verified as real. In contrast, the greatest scientific fraud in history fit exactly what scientists were looking for. Because it confirmed the biases of the time, the Piltdown Man closed people's eyes to the new things there were to discover.
Note: Scientists all too often herald discoveries which confirm their theories without carefully checking the facts. The carefully researched book "Forbidden Archeology" raises serious questions about the origins of the human race. For more along these lines, see concise summaries of deeply revealing archeology and history news articles from reliable major media sources.
Melting Ice In Greenland Could Expose Serious Pollutants From Buried Army Base
August 5, 2016, NPR
http://www.npr.org/sections/thetwo-way/2016/08/05/488872411/melting-ice-in-greenland...
Buried below the ice sheet that covers most of Greenland, there's an abandoned U.S. Army base. Camp Century had trucks, tunnels, even a nuclear reactor. It was also a test site for deploying nuclear missiles. The camp was abandoned almost 50 years ago. But serious pollutants were left behind. Now a team of scientists says that as climate warming melts the ice sheet, those pollutants could spread. [Researcher William Colgan] found unclassified records that described what was left behind there - for example, the nuclear reactor was removed, but low-level radioactive cooling water used in it was not. There were very likely PCBs, which are toxic compounds in electrical equipment. There's no record of how much remained. Colgan says the Army figured all of it would be entombed forever. "They thought it would snow in perpetuity," he says, "and the phrase they used was that the waste would be preserved for eternity by perpetually accumulating snow." Except now, the climate has changed. Greenland's ice sheet is melting. Computer models say the camp could be uncovered by the end of this century. Meltwater could easily end up in the buried camp and then carry contamination through under-ice channels to the ocean. Colgan says it's unclear who owns this waste. The Army built the camp under a treaty between the U.S. and Denmark, which had jurisdiction over Greenland. It's a legal dilemma that's likely to start cropping up more often.
Note: For more along these lines, see concise summaries of deeply revealing global warming news articles from reliable major media sources.
‘The Profiteers: Bechtel and the Men Who Built the World’, by Sally Denton
March 24, 2016, Financial Times
http://www.ft.com/cms/s/0/19d38076-f11b-11e5-9f20-c3a047354386.html#axzz4H4LUklvK
Bechtel - a behemoth among closely held companies - has been the world’s builder, benefiting from vast government contracts for engineering and infrastructure work in difficult places while it nurtured relationships with power brokers in Washington. In The Profiteers, journalist Sally Denton seeks to unravel the history of Bechtel. Her story is one of “how a dynastic line of rulers from the same American family conducts its business” and how its system of networking now pervades US capitalism. Anecdotes of Bohemian Grove, the secretive retreat that became an all-male “summer camp” for US corporate, political and military elites to toast marshmallows, skinny-dip in the river north of San Francisco and dress in drag for skits, elucidate the chummy nature of big business. As of 2014, [Bechtel's] reported revenue was $37bn, with projects and employees in 37 countries. The corporation’s embrace of Saudi Arabia as a lucrative client and its decades-long and contorted experience in Iraq also makes sense of some aspects of US foreign policy - as well as its intelligence-gathering operations. The life and times of John McCone, a former Bechtel executive who later served as CIA director in the US administrations of Presidents Kennedy and Johnson, is chronicled deftly here. It is worth noting: McCone was and is critical to Bechtel’s dominance today. He devised the idea of “cost-plus contracts” for the toughest jobs sought by government. Contractors are guaranteed a profit in such deals.
Note: Bechtel was at the center of a major Iraqi reconstruction scandal in 2007. More recently, major defense contractors have been publicly congratulating themselves for steering US policy towards militarism. For more along these lines, see concise summaries of deeply revealing news articles on corruption in government and in the corporate world.
Inspiring Articles
Syria's secret library
July 28, 2016, BBC News
http://www.bbc.com/news/magazine-36893303
Buried beneath a bomb-damaged building [is] a secret library that provides learning, hope and inspiration to many in the besieged Damascus suburb of Darayya. "We saw that it was vital to create a new library so that we could continue our education. We put it in the basement to help stop it being destroyed by shells and bombs like so many other buildings here," says Anas Ahmad, a former civil engineering student who was one of the founders. The siege of Darayya by government and pro-Assad forces began nearly four years ago. Since then Anas and other volunteers, many of them also former students whose studies were brought to a halt by the war, have collected more than 14,000 books on just about every subject imaginable. Over the same period more than 2,000 people ... have been killed. But that has not stopped Anas and his friends scouring the devastated streets for more material to fill the library's shelves. The location of the library is secret because Anas and other users fear it would be targeted by Darayya's attackers if they knew where it was. "The library holds a special place in all our hearts. And every time there's shelling near the library we pray for it," says Omar Abu Anas, a former engineering student. "Books motivate us to keep on going. We read how in the past everyone turned their backs on a particular nation, yet they still made it. So we can be like that too." [Update] Within days of the publication of this story, Omar was killed on the front line during an attack by pro-Assad forces.
Note: Explore a treasure trove of concise summaries of incredibly inspiring news articles which will inspire you to make a difference.
Steemit: Get on the blockchain social media juggernaut and earn cryptocurrency for posting content
July 15, 2016, International Business Times
http://www.ibtimes.co.uk/steemit-get-blockchain-social-media-juggernaut-earn...
"Welcome to the Blockchain! Your voice is worth something," states a webpage of Steemit, the social network built on a blockchain that's now exploding with popularity. Steemit ... supports community building and social interaction through cryptocurrency rewards and a reputation or influence-based system, known as Steem Dollars and Steem Power. Ned Scott, CEO and co-founder of Steemit, told IBTimes: "If you think about the existing models - Facebook, Twitter, Instagram - these are platforms that invite people to come and do all this work so that their shareholders, who are not necessarily contributors make all this money. "Our platform is a cooperative version of a social network which is more intuitive, and a more shared, community-driven approach, and that's why our early user base is growing. We are completely open source." Steemit grew out of a long process set in motion by gifted developer and co-founder, Daniel Larimer. It evolved from the idea of a decentralised exchange ... to a later exploration of blockchain-based mutual aid and micro-insurance, with a forum added for users to interact and compare notes. It does away with traditional cryptocurrency barriers to entry, like having to go and buy coins at an exchange. Scott said everyone is rewarded one way or another. People who post content actually get rewarded [with Steem, a currency whose value] is split between tradability and reputation. Steem is currently the third most valuable cryptocurrency in the world.
Note: Unlike other social media platforms such as Facebook, Steemit is technically impossible to censor and is owned by everyone that uses it. Explore a treasure trove of concise summaries of incredibly inspiring news articles which will inspire you to make a difference.
Selling unwanted food at a discount, a growing trend you may want to bite into
August 4, 2016, CBC (Canada's public broadcasting system)
http://www.cbc.ca/news/business/leftover-food-flashfood-app-1.3704145
It's a dirty little secret in the food industry that plenty of goods wind up in the trash. As the world's population grows, so does the pressure to tackle the problem. This week, Italy passed new measures to curb food waste. It will now be easier for businesses to donate surplus food and easier for customers to request a "doggy bag" in restaurants - currently not a widespread practice in Italy. There's also an emerging business model that can help take a bite out of food waste. It involves rescuing leftovers and peddling them to consumers at a discount. In 2014, consulting firm Value Chain Management calculated that more than $31 billion worth of food is wasted every year in Canada. Josh Domingues in Toronto ... recently quit his six-figure finance job on Bay Street to create an app called Flashfood. It will connect Toronto food vendors selling leftover food at a discount with customers. Domingues felt he had little choice but to switch careers after his sister, who works as a chef, complained about an epic food waste incident. He did his research and discovered that along with restaurants tossing food, grocers sometimes throw out goods days before they hit their "best before" date. "There's no easy way to connect these food companies directly to the [consumer]," says Domingues. His app, he explains, will help bridge that gap. None of the food sold on Flashfood will have actually passed its "best before" date. Domingues wants to make Flashfood available across Canada and eventually expand to other countries.
Note: Explore a treasure trove of concise summaries of incredibly inspiring news articles which will inspire you to make a difference.
What if Schools Taught Kindness?
February 1, 2016, Greater Good
http://greatergood.berkeley.edu/article/item/what_if_schools_taught_kindness
Every school teaches math and reading, but what about mindfulness and kindness? Twice a week for 20 minutes, pre-kindergarten kids were introduced to stories and practices for paying attention, regulating their emotions, and cultivating kindness. The initial results of our research ... suggest that this program can improve kids’ grades, cognitive abilities, and relationship skills. Having classrooms full of mindful, kind kids completely changes the school environment. Imagine entire schools - entire districts - where kindness is emphasized. That would be truly powerful. Teaching kindness is a way to bubble up widespread transformation that doesn’t require big policy changes or extensive administrative involvement. If you had visited one of our classrooms during the 12-week program, you might have seen a poster on the wall called “Kindness Garden.” When kids performed an act of kindness or benefitted from one, they added a sticker to the poster. The idea is that friendship is like a seed - it needs to be nurtured and taken care of in order to grow. Through that exercise, we got students talking about ... how we might grow more friendship in the classroom. Students who went through the curriculum showed more empathy and kindness and a greater ability to calm themselves down when they felt upset, according to teachers’ ratings. They earned higher grades at the end of the year in certain areas (notably for social and emotional development), and they showed improvement in the ability to think flexibly and delay gratification, skills that have been linked to health and success later in life.
Note: Explore a treasure trove of concise summaries of incredibly inspiring news articles which will inspire you to make a difference.
We're $7,200 in the red for the year.
Kindly support this important work. Donate here.
Please note that most of the summarizing of the revealing news articles in the above summary was done by Mark Bailey of WantToKnow.info. Many thanks to Mark for all the time and skill he puts into this. The section below provides several ideas on what you can do to spread the news.
- Contact your media and political representatives to inform them of the important news articles above. Urge them to study and bring publicity to this vital news. Invite them to read these articles and explore the links included.
- Explore an index to the most revealing major media news articles sorted by topic.
- Learn more about how some of the most vital news is censored by corporate major media ownership in this powerful lesson from the free Insight Course.
- Read excerpts of the 20 most revealing major media news articles ever reported.
- Spread this news to your friends and colleagues, and bookmark this article on key news websites using the "Share" icon on this page, so that we can fill the role at which the major media is sadly failing. Together, we can make a difference.
Finding Balance: WantToKnow.info Inspiration Center
WantToKnow.info believes it is important to balance disturbing cover-up information with inspirational writings which call us to be all that we can be and to work together for positive change. For an abundance of uplifting material, please visit our Inspiration Center.
See our exceptional archive of revealing news articles.
www.momentoflove.org - Every person in the world has a heart
www.personalgrowthcourses.net - Dynamic online courses powerfully expand your horizons
www.WantToKnow.info - Reliable, verifiable information on major cover-ups
www.weboflove.org - Strengthening the Web of Love that interconnects us all
Subscribe here to the WantToKnow.info email list (two messages a week)