Big Brother News Stories
Below are key excerpts of revealing news articles on Big Brother from reliable news media sources. If any link fails to function, a paywall blocks full access, or the article is no longer available, try these digital tools.
On April 30, 1966 ... Anton LaVey signed away his soul forever and became leader of ... the Church of Satan. In the church's first year, LaVey conducted a satanic wedding, a satanic funeral on Treasure Island (in cooperation with the U.S. Navy) and a satanic baptism of his young daughter, Zeena. The church was brazenly and publicly devoted to selfish hedonism. In 1968, LaVey opened up his home to a documentary film crew. Satanic rituals were staged for the cameras, with a nude woman serving as the altar. In 1969, LaVey published "The Satanic Bible": "Hate your enemies with a whole heart, and if a man smite you on one cheek, SMASH him on the other." The canon has gone on to sell nearly a million copies. Michael Aquino began corresponding with Anton LaVey while a psychological operative for the U.S. Army. Aquino returned to the States and was soon made a high-ranking priest. His distinctive appearance – he sported a prominent widow's peak and darkly accented eyebrows – was further enhanced by a small 666 tattooed on his scalp. In 1975, Aquino left with many church members and priests ... to form the Temple of Set, a tightly organized religion that revolved around an Egyptian deity on whom the Hebraic Satan supposedly was based. LaVey's church has been besieged for years by bickering former adherents who insist that he was a fraud and that his institution does not worship the Devil properly. "My estrangement from Anton LaVey caused me intense personal pain," Aquino writes. "For six years I had regarded him as a friend, mentor, and ultimately Devil-father."
Note: An openly avowed Satanist while serving as a Lt. Colonel in the U.S. Army, Michael Aquino coauthored the highly controversial document Mindwar in 1980, which would define the strategy and importance of Psychological Operations, aka PSYOPS, for the U.S. Department of Defense. Aquino was investigated in connection with military child abuse scandals, but never brought to court. He defended his beliefs dressed in Satanic wear on this Geraldo show.
The World Health Organization [is facing] charges that the agency deliberately fomented swine flu hysteria. The Parliamentary Assembly of the Council of Europe (PACE) ... is publicly investigating the WHO's motives in declaring a pandemic. The chairman of its influential health committee, epidemiologist Wolfgang Wodarg, has declared that the "false pandemic" is "one of the greatest medicine scandals of the century." Even within the agency, the director of the WHO Collaborating Center for Epidemiology ... Dr. Ulrich Kiel, has essentially labeled the pandemic a hoax. "We are witnessing a gigantic misallocation of resources [$18 billion so far] in terms of public health," he said. The pandemic declaration [reflects] sheer dishonesty motivated not by medical concerns but political ones. Unquestionably, swine flu has proved to be vastly milder than ordinary seasonal flu. It kills at a third to a tenth the rate, according to [CDC] estimates. Did the WHO have any indicators of this mildness when it declared the pandemic in June? Absolutely. We were then fully 11 weeks into the outbreak and swine flu had only killed 144 people worldwide--the same number who die of seasonal flu worldwide every few hours. (An estimated 250,000 to 500,000 per year by the WHO's own numbers.) The agency was losing credibility over the refusal of avian flu H5N1 to go pandemic and kill as many as 150 million people worldwide, as its "flu czar" had predicted in 2005. Around the world nations heeded the warnings and spent vast sums developing vaccines and making other preparations. So when swine flu conveniently trotted in, the WHO essentially crossed out "avian," inserted "swine."
Note: Forbes removed this article from their website once it gained attention. In this intriguing 11-minute video, epidemiologist Dr. Wodarg questions the validity of the Coronavirus numbers and explains how fear and manipulation have greatly exaggerated the fear around this virus. Explore extensive, eye-opening coverage from reliable sources revealing how the swine and avian flu "pandemics" were designed for corporate profit. For more along these lines, see concise summaries of deeply revealing news articles on the coronavirus from reliable major media sources.
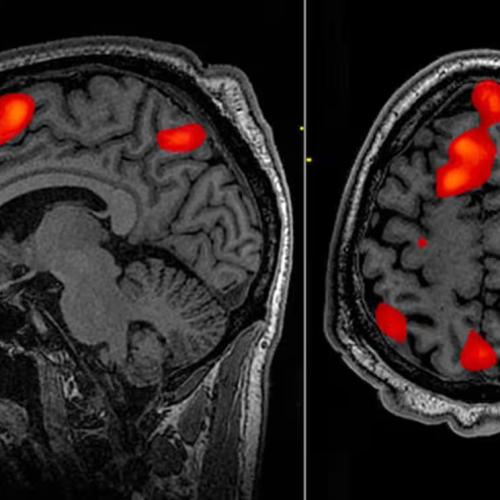
Dr. Jose M. R. Delgado of [Yale University] is one of the leading pioneers in ... E.S.B.: electrical stimulation of the brain. He is also the impassioned prophet of a new “psychocivilized” society whose members would influence and alter their own mental functions to create a “happier, less destructive and better balanced man.” [Delgado said,] “We know that [E.S.B.] can delay a heartbeat, move a finger, bring a word to memory, evoke a sensation.” [His] animals performed like electrical toys. One monkey, Ludy, each time she was stimulated [would] stand up on two feet and circle to the right; climb a pole and then descend again. This “automatism” was repeated [by Ludy] through 20,000 stimulations! The tickling of a few electric volts can send a monkey into a deep sleep, or snap him awake. Similarly, human beings are unable to resist motor responses elicited by E.S.B. Large-scale studies of rats with electrodes in [a] “pleasureful area” found that they preferred E.S.B. above all else—including water, sex and food. Sometimes ravenously hungry rats, ignoring nearby food, would stimulate themselves up to 5,000 times an hour—persisting with manic singleness of purpose for more than a day running, until they keeled over on the floor in a faint! “In humans also ... states of arousal and pleasure have been evoked" ... Delgado added. One patient of ours was a rather reserved 30-year-old woman. E.S.B. at one cerebral point made her suddenly confess her passionate regard for the therapist—whom she'd never seen before." According to one psychoanalyst, “The danger of this being abused is ... tremendous.”
Note: Though quite long, this entire intriguing article is well worth reading. If behavior manipulation was this advanced in 1970, what are they capable of now, and why is it being kept quiet? For more along these lines, see concise summaries of deeply revealing news articles on mind control from reliable major media sources. Then explore the excellent, reliable resources provided in our Mind Control Information Center.
Four years ago ago, officers of the Central Intelligence Agency and National Security Agency participated in a series of unusual experiments run by Stanford Research Institute (SRI) to verify claims that certain people have psychic abilities. The results ... were astonishing. The SRI investigators, physicists Harold E. Puthoff (a former NSA research engineer) and Russell Targ, set out to demonstrate to their CIA sponsor that their subjects, a noted psychic named Ingo Swann and ... Pat Price, could describe distant locations merely by knowing which geographic coordinates to "look at." Puthoff and Targ [call this] "remote viewing." In one case, Swann described and sketched with reasonable accuracy a target island in the South Indian Ocean. In another instance, Pat Price gave an incredibly detailed description of a supposedly secret, underground military installation in Virginia. "Hell, there's no security left," a government security officer exclaimed upon hearing of Price's alleged success at psychic spying. One of Ingo Swann's remote viewing demonstrations at SRI was to pinpoint the location of Soviet submarines around the world. The CIA scientist monitoring the tests ... believed he had a potential class A espionage agent who could roam psychically anywhere in the world – in effect, the perfect spy. For the past 25 years, various branches of the military and intelligence communities have actively investigated this highly controversial field of parapsychology. There is particular concern ... that the Russians are able telepathically to influence the behavior of others, alter their emotions or health, knock them out or even kill. CIA psychologists are swamped with proposals for psychic studies.
Note: This article strangely is not to be found anywhere in the online archives of the Washington Post. It is still available for a fee in the archives of smaller newspapers which published the article. The amazing entire article can be found free at the link above. For lots more along these lines, see a wealth of reliable videos and information on remote viewing. And a great documentary "Third Eye Spies" on remote viewing can be found here. Then explore the excellent, reliable resources provided in our Mind Control Information Center.
The Justice Department is investigating allegations that officers of a special Venezuelan anti-drug unit funded by the CIA smuggled more than 2,000 pounds of cocaine into the United States with the knowledge of CIA officials - despite protests by the Drug Enforcement Administration. That is a huge amount of cocaine. But it was hardly a first. The agency has never been above using individuals or organizations with known links to drug trafficking. Until recently, no DEA country attach overseas was allowed to initiate an investigation into a suspected drug trafficker ... without clearance from the local CIA station chief. CIA ties to international drug trafficking date to the Korean War. Nowhere, however, was the CIA more closely tied to drug traffic than it was in Pakistan during the Afghan War. As its principal conduit for arms and money to the Afghan guerrillas, the agency chose the Pakistan military's Inter-Services Intelligence Bureau. The ISI in turn steered the CIA's support toward [an Islamic fundamentalist who] received almost half of the agency's financial support during the war. But many of his commanders were also major heroin traffickers. Soon the trucks that delivered arms to the guerrillas in Afghanistan were coming back ... full of heroin. The heroin traffic blossomed in the shadows of a CIA-sustained guerrilla war. The conflict and its aftermath have given the world another Golden Triangle: the Golden Crescent, sweeping through Afghanistan, Pakistan and parts of the former Soviet Union. Many of those involved in the drug traffic are men who were once armed, trained and financed by the CIA.
Note: The entire article at the link above is highy revealing. Read more about the CIA's ongoing involvement with Afghan heroin trafficking. The Taliban banned opium production in 2000 reducing the yield by 90%. Yet shortly after the U.S. defeated the Taliban, Afghanistan quickly returned to supplying 75% of the world's heroin. Do you think the U.S. is serious about stopping the drug trade? For more along these lines, see concise summaries of deeply revealing intelligence agency corruption news articles from reliable major media sources.
Amazon has apparently started removing anti-vaccine documentaries from its Amazon Prime Video streaming service. The move came days after a CNN Business report highlighted the anti-vaccine comment available on the site, and hours after Rep. Adam Schiff wrote an open letter to Amazon CEO Jeff Bezos, saying he is concerned "that Amazon is surfacing and recommending" anti-vaccination books and movies. Anti-vaccine movies that were previously available free for Prime subscribers, like "We Don't Vaccinate!," "Shoot 'Em Up: The Truth About Vaccines," and "Vaxxed: From Cover-Up to Catastrophe," are now "currently unavailable." While some anti-vaccine videos are gone from the Prime streaming service, a number of anti-vaccine books were still available for purchase on Amazon.com ... and some were still being offered for free to Kindle Unlimited subscribers. A sponsored post for the book "Vaccines On Trial: Truth and Consequences of Mandatory Shots" also remained live. Amongst the titles taken down are "VAXXED: From Cover-Up to Catastrophe," the notorious anti-vaccine documentary that was banned from the Tribeca Film Festival in 2016, and whose director, Andrew Wakefield, is one of the central figures in the anti-vaccine movements. Schiff had previously written letters to the heads of Facebook and Google, which owns YouTube, about anti-vaccine content on their platforms. Both companies publicly vowed to make changes to how anti-vaccine content is made available.
Note: This New York Times article reports that facebook is also removing key vaccine content. Our freedom to access information on all sides of various debates is gradually being eroded by giants like amazon and facebook. The documentary "Vaxxed" presents solid, verifiable evidence of a major cover-up around vaccine safety. You can find it on this webpage. For more along these lines, see concise summaries of deeply revealing news articles on vaccine risks from reliable major media sources. Then explore the excellent, reliable resources provided in our Health Information Center.
Democratic presidential candidates Sens. Bernie Sanders, Kamala Harris and Elizabeth Warren on Wednesday defended Rep. Ilhan Omar against the backlash to her comments slamming pro-Israel groups and politicians, which have been called anti-Semitic. Sanders, who is Jewish, said criticism of Omar and efforts to get her taken off the House Foreign Affairs Committee ... are aimed at stopping a discussion about American's foreign policy toward Israel. [He] differentiated between promoting anti-Semitism and criticizing Israel as a state. Harris called out all instances of bigotry and expressed concern that the focus on Omar "may put her at risk." Warren [stated], "Branding criticism of Israel as automatically anti-Semitic has a chilling effect on our public discourse and makes it harder to achieve a peaceful solution between Israelis and Palestinians. Threats of violence -- like those made against Rep. Omar -- are never acceptable." Last month, Omar faced criticism for tweets insinuating that the pro-Israel lobbying group American Israel Public Affairs Committee was effectively buying off US politicians. The Minnesota Democrat subsequently apologized after demands from Speaker Nancy Pelosi of California. Omar [also] implied that pro-Israel lawmakers are under a "political influence in this country that says it is OK for people to push for allegiance to a foreign country." House Foreign Affairs Chairman Eliot Engel said Tuesday that he does not want Omar removed from her seat on the committee because of her recent comments, despite previously calling for her to apologize in a fiery statement.
Robert A. Maheu was such a colorful character that its widely believed the television show Mission: Impossible was based on him and his private investigative agency. As an ex-FBI agent, the CIA asked him to handle jobs it wanted to steer clear of, such as lining up prostitutes for a foreign president or hiring the mafia to kill Fidel Castro. For more than 15 years, Maheu [was] on monthly retainer to The Agency, CIA records show. Maheu was the right-hand man to Howard Hughes as Hughes ... helped finance CIA operations. A new book alleges that Maheu may have performed another mission for the CIA: the assassination of Sen. Robert F. Kennedy. Maheu would have had access to the CIAs experiments in hypnosis and mind control. That would have enabled him to frame Sirhan Sirhan as a patsy for the slaying of Kennedy, while other gunmen actually fired the fatal shots, argues author Lisa Pease, who spent 25 years researching her book, A Lie Too Big to Fail." Sirhans lawyers in 2010 accused the CIA of hypnotizing Sirhan and making him an involuntary participant. With Maheus contacts throughout the CIA and organized crime, he is the most credible high-level suspect for the planner of Robert Kennedys assassination, Pease wrote. Chief among that evidence is the autopsy finding that Kennedy was shot point blank in the back of the head, while Sirhan was in front of Kennedy. Witnesses at the scene of the shooting were adamant that Sirhan never got close enough to fire at close range. Not long after the trial, a ballistics expert examined the three bullets recovered from the scene and found that they did not match Sirhans gun.
Note: The entire article at the link above is chock full of excellent information which leaves little doubt that RFK was not assassinated by one man. For more along these lines, see concise summaries of deeply revealing news articles on the Kennedy assassinations from reliable major media sources. Then explore the excellent, reliable resources provided in our Media Information Center, which show how the media has been complicit in covering huge stories like this and many more.
Jeffrey Epstein had a little black book filled with the names and personal phone numbers of some of the world's wealthiest and most influential people, from Bill Clinton and Donald Trump to actors, actresses, scientists and business tycoons. For years, Epstein lured an endless stream of teenage girls to his Palm Beach mansion, offering to pay them for massages. Instead, police say, for years he coerced middle and high school girls into engaging in sex acts with him and others. As evidence emerged that there were victims and witnesses outside of Palm Beach, the FBI began an investigation in 2006 into whether Epstein and others employed by him were involved in underage sex trafficking. But in 2007, despite substantial evidence that corroborated the girls' stories of abuse by Epstein, the U.S. attorney in Miami, Alexander Acosta, signed off on a secret deal for the multimillionaire, one that ensured he would never spend a day in prison. Acosta, now President Donald Trump's secretary of labor, agreed to seal the agreement so that no one – not even Epstein's victims – would know the full extent of his crimes or who was involved. The Miami Herald obtained thousands of FBI and court records, lawsuits, and witness depositions, and went to federal court in New York to access sealed documents in the reporting of "Perversion of Justice." The Herald also tracked down more than 60 women who said they were victims, some of whom had never spoken of the abuse before.
Note: See the timeline on this critical story. Learn about other major cover-ups in high places in deeply revealing news articles on sexual abuse scandals from reliable major media sources. Watch an excellent segment by Australia's "60-Minutes" team "Spies, Lords and Predators" on a pedophile ring in the UK which leads directly to the highest levels of government. A second suppressed documentary, "Conspiracy of Silence," goes even deeper into this topic in the US.
Woody Norris aims the silvery plate ... demonstrating something called HyperSonic Sound (HSS). I pace out a hundred yards. Norris pelts me with the Handel. The sound is inside my head. Imagine, he says, walking by a soda machine (say, one of the five million in Japan that will soon employ HSS) ... then hearing what you alone hear -- the plink of ice cubes and the invocation, ''Wouldn't a Coke taste great right about now?'' An HSS transmission can travel 450 feet - at practically the same volume all along its path. In past months, Norris and his staff have made a further, key improvement to HSS -- instead of sending out a column of sound, they can now project a single sphere of it, self-contained, like a bubble. [And] there are Defense Department applications. Norris [has] been busy honing something called High Intensity Directed Acoustics (HIDA). Although [it] has been routinely referred to as a "nonlethal weapon," ... in reality, HIDA is both warning and weapon. If used from a battleship, it can ward off stray crafts at 500 yards with a pinpointed verbal warning. Should the offending vessel continue ... the stern warnings are replaced by 120-decibel sounds that are as physically disabling as shrapnel. Certain noises, projected at the right pitch, can incapacitate even a stone-deaf terrorist; the bones in your head are brutalized by a tone's full effect whether you're clutching the sides of your skull in agony or not. "HIDA can instantaneously cause loss of equilibrium, vomiting, migraines - really, we can pretty much pick our ailment," he says brightly. Last month, [Norris' company] A.T.C. cut a five-year, multimillion-dollar licensing agreement with General Dynamics, one of the giants of the military-industrial complex.
Note: This entire article is well worth reading if you want to understand just how advanced these dangerous weapons are. And there is little doubt that this weapon can cause death. Remember the article was written in 2003. Sound weapons developed for war are now routinely used against civilian populations. Explore an excellent, well researched article going into more detail on these weapons. For more along these lines, see concise summaries of deeply revealing non-lethal weapons news articles from reliable major media sources.
Dont want to get a vaccine for yourself or your child? Prepare to face the consequences. In the last month, a Detroit mother went to jail because she refused to vaccinate her child. Fifty people lost their jobs at a group of Midwestern hospitals and clinics because they declined a flu shot. And an Oregon university has blocked students from registering for classes unless they have a meningitis shot. All states have some vaccine requirements for public educationno shots, no school. All but three states - Mississippi, West Virginia and California - allow parents to send their child to school without vaccines based on some kind of non-medical exemption. In 2013, more than 90 percent of American children had been vaccinated for chicken pox, hepatitis B, measles, mumps and rubella, according to the Centers for Disease Control and Prevention. However, a significant number of people ... hesitate when a doctor offers them a vaccine. A new study released on Monday found that 27 percent of the parents surveyed could be classified as moderately or highly hesitant around vaccines. That same study found these people may be particularly concerned with the purity of vaccines. Increasingly, parents who choose not to vaccinate are warned of harsh penalties. People who choose not to vaccinate themselves may also face serious consequences. Some states have laws guiding which vaccinations people working at hospitals or other health care facilities must have; more often, requirements may be enshrined in a facility's policy, not in law.
Note: Watch an excellent video of Emmy award winning reporter Sharyl Attkisson exposing how the government fired an vaccine expert who found links to autism. For more along these lines, see concise summaries of deeply revealing vaccine controversy news articles from reliable major media sources.
On July 26, 2016, the Office of the Inspector General (OIG) issued a report “Army General Fund Adjustments Not Adequately Documented or Supported”. The report indicates that for fiscal year 2015 the Army failed to provide adequate support for $6.5 trillion. Given that the entire Army budget in fiscal year 2015 was $120 billion, unsupported adjustments were 54 times the level of spending authorized by Congress. An appendix to the July 2016 report shows $2 trillion in changes to the Army General Fund balance sheet due to unsupported adjustments. On the asset side, there is $794 billion increase in the Army's Fund Balance with the U.S. Treasury. There is also an increase of $929 billion in the Army's Accounts Payable. What is the source of the additional $794 billion in the Army's Fund Balance? The July 2016 report is not the only such report of unsubstantiated adjustments. Mark Skidmore and Catherine Austin Fitts, former Assistant Secretary of Housing and Urban Development, conducted a search of government websites and found similar reports dating back to 1998. While the documents are incomplete, original government sources indicate $21 trillion in unsupported adjustments have been reported for the Department of Defense and the Department of Housing and Urban Development for the years 1998-2015. [And why] after Mark Skidmore began inquiring about OIG-reported unsubstantiated adjustments, [was] the OIG's webpage, which documented, albeit in a highly incomplete manner, these unsupported "accounting adjustments," ... mysteriously taken down?
Note: Explore this webpage for a brief background to this astounding news. See also a detailed analysis of these missing trillions, which amount to $65,000 per man, woman, and child in the US. And don't miss this highly revealing interview with Prof. Mark Skidmore of Michigan State with even more startling news.
The U.S. government [planned] false flag attacks with Soviet aircraft to justify war with the USSR or its allies, newly declassified documents surrounding the assassination of President John F. Kennedy show. In a three-page memo, members of the National Security Council wrote, "There is a possibility that such aircraft could be used in a ... provocation operation in which Soviet aircraft would appear to attack US or friendly installations to provide an excuse for U.S. intervention." The memo shows that the department, along with the CIA, considered buying Soviet aircraft to stage the attacks, even getting estimates from the Air Force on how long it would take and how much it would cost to produce the planes domestically and covertly. The document also outlined the possibility of purchasing such aircraft from non-Soviet Bloc countries that had received planes from the USSR, or from pilots that had defected, instead of building them domestically. The CIA deemed those plans too risky. It is unclear when the memo was written or circulated. The NSC staff mention a meeting on March 22, 1962, when a "Special Group" discussed the attorney general's questions about acquiring Soviet aircraft. The document was last reviewed by the CIA in February 1998, and a stamp shows it was declassified in March 2016. But, strangely, the document's cover letter shows a date of "00/00/00."
Note: ABC News back in 2001 was the only major media to report on Operation Northwoods, which is the code name for a very similar plan, when the first documents on this were declassified. As these earlier documents show, the plan was approved by the top Pentagon chiefs to create a pretext for war with Cuba by sinking an American ship in the Havana harbor or creating a "terror campaign" in cities like Miami and Washington D.C. Why was this stunning news only reported by ABC? For a possible reason, see this excellent summary of testimony by major media whistleblowers.
Regulators have approved the first drug with a sensor that alerts doctors when the medication has been taken. The digital pill combines two existing products: the former blockbuster psychiatric medication Abilify - long used to treat schizophrenia and bipolar disorder - with a sensor tracking system first approved in 2012. Experts say the technology could be a useful tool, but it will also change how doctors relate to their patients as theyre able to see whether they are following instructions. The pill has not yet been shown to actually improve patients medication compliance, a feature insurers are likely to insist on before paying for the pill. Additionally, patients must be willing to allow their doctors and caregivers to access the digital information. The technology carries risks for patient privacy, too, if there are breaches of medical data or unauthorized use as a surveillance tool, said James Giordano, a professor of neurology at Georgetown University Medical Center. Could this type of device be used for real-time surveillance? The answer is of course it could, said Giordano. The new pill, Abilify MyCite, is embedded with a digital sensor that is activated by stomach fluids, sending a signal to a patch worn by the patient and notifying a digital smartphone app that the medication has been taken.
Note: In 2010, it was quietly reported that Novartis AG would be seeking regulatory approval for such "chip-in-a-pill technology". For more along these lines, see concise summaries of deeply revealing news articles on microchip implants and the disappearance of privacy.
On December 7, 1941, Japanese war planes bombed the U.S. naval base at Pearl Harbor, Hawaii. Six decades later, Al Qaeda terrorists flew hijacked airplanes into the World Trade Center and the Pentagon. Neither President Franklin Roosevelt nor President George W. Bush targeted and killed Americans on U.S. soil in the aftermath of those attacks. Doing so wouldn't have made any sense. How strange, then, that Attorney General Eric Holder invoked those very attacks in a letter confirming that President Obama believes there are circumstances in which he could order Americans targeted and killed on U.S. soil. "It is possible ... for the President to authorize the military to use lethal force within the territory of the United States," he wrote. "The President could conceivably have no choice but to authorize the military to use such force if necessary to protect the homeland in the circumstances of a catastrophic attack like the ones suffered on December 7, 1941 and on September 11, 2001." The very scenario to be guarded against is a president using the pretext of a terrorist attack to seize extraordinary powers. Isn't that among the most likely scenarios for the United States turning into an authoritarian security state?
Note: For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the erosion of civil liberties.
Executives with Europe's biggest bank, HSBC, were subjected to a humiliating onslaught from US senators on Tuesday over revelations that staff at its global subsidiaries laundered billions of dollars for drug cartels, terrorists and pariah states. HSBC's subsidiaries transported billions of dollars of cash in armoured vehicles, cleared suspicious travellers' cheques worth billions, and allowed Mexican drug lords buy to planes with money laundered through Cayman Islands accounts. Other subsidiaries moved money from Iran, Syria and other countries on US sanctions lists, and helped a Saudi bank linked to al-Qaida to shift money to the US. The committee had released a damning report on Monday, which detailed a collapse in HSBC's compliance standards. Executives at the bank [were] consistently warned of problems. HSBC's Mexican operations moved $7bn into the bank's US operations, and according to its own staff, much of that money was tied to drug traffickers. Leigh Winchell, assistant director for investigative programs at US immigration & customs enforcement ... said 47,000 people had lost their lives since 2006 as a result of Mexican drug traffickers. The senators highlighted testimony from Leopoldo Barroso, a former HSBC anti money-laundering director, who told company officials in an exit interview that he was concerned about "allegations of 60% to 70% of laundered proceeds in Mexico" going through HSBC's affiliate.
Note: HSBC may have been founded to service the international drug trade. They eventually settled this case for $1.92 billion. The corrupt bankers were not criminally prosecuted. Settlements like this often amount to "cash for secrecy" deals that are ultimately profitable for banks. For more along these lines, see concise summaries of deeply revealing banking corruption news articles from reliable major media sources.
Trump administration lawyers are demanding the private account information of potentially thousands of Facebook users in three separate search warrants served on the social media giant. The warrants specifically target the accounts of three Facebook users who are described ... as "anti-administration activists who have spoken out at organized events, and who are generally very critical of this administration's policies." One of those users, Emmelia Talarico, operated the disruptj20 page where Inauguration Day protests were organized and discussed; the page was visited by an estimated 6,000 users whose identities the government would have access to if Facebook hands over the information. Talarico says if her account information was given to the government, officials would have access to her "personal passwords, security questions and answers, and credit card information," plus "the private lists of invitees and attendees to multiple political events." The American Civil Liberties Union, representing the three Facebook users, filed a motion to quash the warrants Thursday. "What is particularly chilling about these warrants is that anti-administration political activists are going to [be] scrutinized by the very administration they are protesting," said ACLU attorney Scott Michelman. Facebook was initially served the warrants in February 2017 along with a gag order which barred the social media company from alerting the three users that the government was seeking their private information.
Note: United Nations officials recently said that the US government's treatment of activists was increasingly "incompatible with US obligations under international human rights law". For more along these lines, see concise summaries of deeply revealing news articles on government corruption and the disappearance of privacy.
A human sacrifice has been staged in the grounds of the European Organisation for Nuclear Research, the home of the God Particle. A video circulating online shows hooded figures apparently engaging in a ritual, staged under a huge statue of a Hindu deity, at the end of which a woman is stabbed. The footage appears to have been recorded as part of a prank by scientists at Europes top physics lab, which serves as the home of the Large Hadron Collider. The identity and motives of those behind the video hasnt yet been discovered. In the footage itself, multiple people are shown wearing long, flowing black robes and one appears to have hiking boots on underneath. They are depicted walking around, before a woman moves onto the floor and is apparently stabbed. As that happens, the person who is supposedly recording the video appears to react firing out expletives and apparently running away, which causes the camera to move away from the scene before it is cut off. A Cern spokesperson confirmed that the video had been filmed there, but said that it had been made without permission or knowledge. Its far from the first time that scientific work has been associated with the occult or the mystical. Because of the highly-specialised and often terrifying work that goes on at Cern, it has become a haven of speculation.
Note: Was this sacrifice really faked? Watch the one-minute video available here. The opening of the huge Gotthard tunnel with its most bizarre, occult opening ceremony (as reported by BBC), occurred not long before this ritual. Watch a video filled with intriguing speculation on this and more. And to dive even deeper into what's going on with occult sacrifice, read this important article.
As grocery shoppers work to digest Amazons massive acquisition of Whole Foods for $13.7 billion, the digital storefront recently scored a victory that aims to reinforce the companys growing investments in brick-and-mortar retail. Amazon was awarded a patent May 30 that could help it choke off a common issue faced by many physical stores: Customers use of smartphones to compare prices even as they walk around a shop. But Amazon now has the technology to prevent that type of behavior when customers enter any of its physical stores and log onto the WiFi networks there. Titled Physical Store Online Shopping Control, Amazons patent describes a system that can identify a customers Internet traffic and sense when the smartphone user is trying to access a competitors website. When that happens, Amazon may take one of several actions. It may block access to the competitors site, preventing customers from viewing comparable products from rivals. It might redirect the customer to Amazons own site or to other, Amazon-approved sites. It might notify an Amazon salesperson to approach the customer. Or it might send the customers smartphone a text message, coupon or other information designed to lure the person back into Amazons orbit.
Note: For more along these lines, see concise summaries of deeply revealing corporate corruption news articles from reliable major media sources.
Trump delegate and Gawker bankrupter Peter Thiel is no stranger to the idea of increasing his lifespan through science. On Bloomberg TV in 2014, Thiel explained that he was taking human-growth hormone pills as part of his plan to live 120 years. Given Thiels obsession with warding off death, it comes as no surprise that the Silicon Valley billionaire is interested in at least one radical way of doing it: injecting himself with a young persons blood. [In] a year-old interview ... the venture-capitalist [said] that hes interested in parabiosis, which includes the practice of getting transfusions of blood from a younger person, as a means of improving health and potentially reversing aging. I'm looking into parabiosis stuff. This is where they did the young blood into older mice and they found that had a massive rejuvenating effect, he said. Its one of these very odd things where people had done these studies in the 1950s and then it got dropped altogether. I think there are a lot of these things that have been strangely under-explored. A Thiel Capital employee ... previously expressed interest in the technique to Jesse Karmazin, the founder of Ambrosia LLC, a company that has been looking for volunteers over the age of 35 to receive blood transfusions from individuals under the age of 25. Bercovici notes that Silicon Valley is abound with rumors of wealthy tech elites experimenting with parabiosis, and Gawker ... received a tip in June claiming that Thiel spends $40,000 per quarter to get an infusion of blood from an 18-year-old.
Note: One university researcher has found that many in the European royalty until the end of the 18th century practiced selective cannibalism in the belief if would keep them young. Another article goes into greater depth about the practice some elder members of the wealthy elite taking blood infusions from young people to stay young.
Important Note: Explore our full index to revealing excerpts of key major media news stories on several dozen engaging topics. And don't miss amazing excerpts from 20 of the most revealing news articles ever published.