Intelligence Agency Corruption News Articles
Below are key excerpts of revealing news articles on intelligence agency corruption from reliable news media sources. If any link fails to function, a paywall blocks full access, or the article is no longer available, try these digital tools.
For further exploration, delve into our comprehensive Military-Intelligence Corruption Information Center.
Whistle-blower AT&T technician Mark Klein says his effort to reveal alleged government surveillance of domestic Internet traffic was blocked not only by U.S. intelligence officials but also by the top editors of the Los Angeles Times. Klein describes how he stumbled across "secret NSA rooms" being installed at an AT&T switching center in San Francisco and later heard of similar rooms in at least six other cities. Eventually, Klein says he decided to take his documents to the Los Angeles Times, to blow the whistle on what he calls "an illegal and Orwellian project." But after working for two months with LA Times reporter Joe Menn, Klein says he was told the story had been killed at the request of then-Director of National Intelligence John Negroponte and then-director of the NSA Gen. Michael Hayden. Klein says he then took his AT&T documents to The New York Times, which published its exclusive account last April [later removed from NY Times website]. In the court case against AT&T, Negroponte formally invoked the "state secrets privilege," claiming the lawsuit and the information from Klein and others could "cause exceptionally grave damage to the national security of the United States." The Los Angeles Times' decision was made by the paper's editor at the time, Dean Baquet, now the Washington bureau chief of The New York Times. As the new Washington bureau chief of The New York Times, Baquet now oversees the reporters who have broken most of the major stories involving the government surveillance program, often over objections from the government.
Note: This webpage was removed from the ABC website, but is still available through archive.org on thise webpage. So after the NY Times has the guts to report this important story, the man who was responsible for the censorship at the LA Times is transferred to the very position in the NY Times where he can now block future stories there. For why this case of blatant media censorship isn't making headlines, click here.
In December 1974, the New York Times reported that the CIA had conducted illegal domestic activities, including experiments on U.S. citizens during the 1960s. That report prompted investigations by both Congress (in the form of the Church Committee) and a presidential commission (known as the Rockefeller Commission) into the domestic activities of the CIA, the FBI, and intelligence-related agencies of the military. Congressional hearings and the Rockefeller Commission report revealed to the public for the first time that the CIA and the DOD had conducted experiments on both cognizant and unwitting human subjects as part of an extensive program to influence and control human behavior through the use of psychoactive drugs (such as LSD and mescaline) and other chemical, biological, and psychological means. They also revealed that at least one subject had died after administration of LSD. Frank Olson, an Army scientist, was given LSD without his knowledge or consent in 1953 as part of a CIA experiment and apparently committed suicide a week later. Subsequent reports would show that another person ... died as a result of a secret Army experiment involving mescaline. The CIA program, known principally by the codename MKULTRA, began in 1950 and was motivated largely in response to alleged Soviet, Chinese, and North Korean uses of mind-control techniques on U.S. prisoners of war in Korea. Most of the MKULTRA records were deliberately destroyed in 1973 by order of then-Director of Central Intelligence Richard Helms.
Note: This highly revealing article on a U.S. government website shows that the CIA was actively involved in mind control projects. Explore also an excellent summary based on thousands of pages of declassified CIA documents showing the secret creation of unknowing assassins or "Manchurian Candidates."
New video and photographic evidence ... puts three senior CIA operatives at the scene of Robert Kennedy's assassination. It reveals that the operatives and four unidentified associates were at the Ambassador Hotel, Los Angeles in the moments before and after the shooting on 5 June, 1968. The CIA had no domestic jurisdiction and some of the officers were based in South-East Asia at the time, with no reason to be in Los Angeles. Kennedy had just won the California Democratic primary on an anti-War ticket and was set to challenge Nixon for the White House. A 24-year-old Palestinian, Sirhan Sirhan, was arrested as the lone assassin. However, even under hypnosis, he has never been able to remember the shooting and defence psychiatrists concluded he was in a trance at the time. Witnesses placed Sirhan's gun several feet in front of Kennedy but the autopsy showed the fatal shot came from one inch behind. Dr Herbert Spiegel, a world authority on hypnosis at Columbia University, believes Sirhan may have been hypnotically programmed to act as a decoy for the real assassin. Three of these men have been positively identified as senior officers who worked together in 1963 at JMWAVE, the CIA's Miami base. David Morales was Chief of Operations and once told friends: "I was in Dallas when we got the son of a bitch and I was in Los Angeles when we got the little bastard." George Joannides was Chief of Psychological Warfare Operations. Now, we see him at the Ambassador Hotel the night a second Kennedy is assassinated.
Note: There is ample evidence that Sirhan Sirhan was a programmed Manchurian Candidate. Declassified CIA documents show that U.S. intelligence services were creating programmed assassins back as early as the 1950s. For reliable, verifiable information on this key topic, click here.
Michael Scheuer, a 22-year veteran of the CIA, wrote "Imperial Hubris: Why the West is Losing the War on Terror." Between January 1996 and June 1999 I was in charge of running operations against Al Qaeda from Washington. When it comes to this small slice of the large U.S. national security pie, I speak with firsthand experience (and for several score of CIA officers) when I state categorically that during this time senior White House officials repeatedly refused to act on sound intelligence that provided multiple chances to eliminate Osama bin Laden either by capture or by U.S. military attack. I witnessed and documented, along with dozens of other CIA officers, instances where life-risking intelligence-gathering work of the agency's men and women in the field was wasted. I was never charged with deciding whether to act against Bin Laden. That decision properly belongs solely to senior White House officials. However, as a now-private American citizen, it is my right to question their judgment; I am entitled to know why the protection of Americans most selfishly, my own children and grandchildren was not the top priority of the senior officials who refused to act on the opportunities to attack Bin Laden provided by the clandestine service. Each of these officials have publicly argued that the intelligence was not "good enough" to act, but they almost always neglect to say that they were repeatedly advised that the intelligence was not going to get better and that Bin Laden was going to kill thousands of Americans if he was not stopped.
Note: If the above link fails, click here. For many other serious questions around the 9/11 attacks, click here.
In what the government describes as a bizarre coincidence, one U.S. intelligence agency was planning an exercise last Sept. 11 in which an errant aircraft would crash into one of its buildings. But the cause wasn't terrorism it was to be a simulated accident. Officials at the Chantilly, Va.-based National Reconnaissance Office had scheduled an exercise that morning in which a small corporate jet would crash into one of the four towers at the agency's headquarters building. The agency is about four miles from the runways of Washington Dulles International Airport. "It was just an incredible coincidence that this happened to involve an aircraft crashing into our facility," [NRO spokesman Art] Haubold said. "As soon as the real world events began, we canceled the exercise." Adding to the coincidence, American Airlines Flight 77 the Boeing 767 that was hijacked and crashed into the Pentagon took off from Dulles at 8:10 a.m. on Sept. 11, 50 minutes before the exercise was to begin. It struck the Pentagon around 9:40 a.m., killing 64 aboard the plane and 125 on the ground. The National Reconnaissance Office operates many of the nation's spy satellites. It draws its personnel from the military and the CIA. In a promotion for speaker John Fulton, a CIA officer assigned as chief of NRO's strategic gaming division, the announcement says, "On the morning of September 11th 2001, Mr. Fulton and his team ... were running a pre-planned simulation to explore the emergency response issues that would be created if a plane were to strike a building."
Note: For many more disturbing coincindences and outright cover-ups around 9/11, click here. And for yet another amazing "coincidence" surrounding the London bombings, click here.
[An] FBI counter-terrorism agent [is] accusing the agency of prohibiting him from conducting his probe into terror financing activities because he complained about obstruction by bureau superiors. Chicago-based FBI Special Agent Robert Wright ... said the recent trajectory of his FBI career has taken a downward spiral since he complained about two incidents that inhibited his ability to continue terror funding and money laundering probes of members of ... Hamas and Hezbollah. The FBI has been under fire since it was revealed that FBI field alerts to Washington of Middle Eastern men training at U.S. flight schools during the summer of 2001 were buried in paperwork, and agents in Minneapolis who circumvented normal channels to contact the CIA about suspected "20th hijacker" Zacarias Moussaoui were reprimanded. Agents who have complained about bureaucratic barriers in the past have been punished, and Wright said that he is one of them. Wright has been demoted to "paper pusher" and "chief dishwasher" at the Chicago field office since he complained about the wrenches thrown into his probe. Wright is under threat of retribution should he talk to members of Congress about what he knows. Wright said throughout his six-year posting in counter-terrorism, he was involved in probes of Hamas and Hezbollah. His most successful 'get' netted $1.4 million in terrorist money in 1998, money that he said today was linked to Saudi businessman and financier Yassin Kadi, who was identified late last year as a close associate of Usama Bin Laden.
Note: For lots more on what happened with Robert Wright, click here. For many still-unanswered questions from highly respected government officials and professors about the behavior of the highest levels of the FBI and other US government agencies before, during and after the 9/11 attacks, click here and here.
GREG PALAST: The CIA and Saudi Arabia, the Bushes and the Bin Ladens. Did their connections cause America to turn a blind eye to terrorism? UNNAMED MAN: There is a hidden agenda at the very highest levels of our government. PETER ELSNER: How can it be that the former President of the US and the current President of the US have business dealings with characters that need to be investigated? PALAST: In the eight weeks since the attacks, over 1,000 suspects and potential witnesses have been detained. Yet, just days after the hijackers took off from Boston aiming for the Twin Towers, a special charter flight out of the same airport whisked 11 members of Osama Bin Laden's family off to Saudi Arabia. That did not concern the White House. Their official line is that the Bin Ladens are above suspicion - apart from Osama, the black sheep, who they say hijacked the family name. That's fortunate for the Bush family and the Saudi royal household, whose links with the Bin Ladens could otherwise prove embarrassing. But Newsnight has obtained evidence that the FBI was on the trail of other members of the Bin Laden family for links to terrorist organisations before and after September 11th. This document is marked "Secret". Case ID - 199-Eye WF 213 589. 199 is FBI code for case type. 9 would be murder. 65 would be espionage. 199 means national security. WF indicates Washington field office special agents were investigating ABL. ABL is Abdullah Bin Laden.
Note: For a Washington Post article showing that former President George H.W. Bush was meeting with a brother of Osama bin Laden the day before 9/11, click here. For lots more on the unanswered questions about the official account of 9/11, click here and here.
Security chiefs on both sides of the Atlantic repeatedly turned down the chance to acquire a vast intelligence database on Osama bin Laden and more than 200 leading members of his al-Qaeda terrorist network in the years leading up to the 11 September attacks. They were offered thick files, with photographs and detailed biographies of many of his principal cadres, and vital information about al-Qaeda's financial interests in many parts of the globe. On two separate occasions, they were given an opportunity to extradite or interview key bin Laden operatives who had been arrested in Africa because they appeared to be planning terrorist atrocities. None of the offers, made regularly from the start of 1995, was taken up. One senior CIA source admitted last night: 'This represents the worst single intelligence failure in this whole terrible business.' Bin Laden and his cadres came to Sudan in 1992 because at that time it was one of the few Islamic countries where they did not need visas. He used his time there to build a lucrative web of legitimate businesses, and to seed a far-flung financial network - much of which was monitored by the Sudanese. They also kept his followers under close surveillance. One US source who has seen the files on bin Laden's men in Khartoum said some were 'an inch and a half thick'. They included photographs, and information on their families, backgrounds and contacts.
Note: For many questions raised about the official account of the 9/11 attacks by highly credible professors and officials, click here and here.
Their names were flashed around the world as suicide hijackers who carried out the attacks on America. But yesterday four innocent men told how their identities had been stolen by Osama bin Laden's teams to cover their tracks. The men - all from Saudi Arabia - spoke of their shock at being mistakenly named by the FBI as suicide terrorists. None of the four was in the United States on September 11 and all are alive in their home country. The FBI released the list of 19 suicide terrorists three days after the attacks. The Saudi Airlines pilot, Saeed Al-Ghamdi, 25, and Abdulaziz Al-Omari, an engineer from Riyadh, are furious that the hijackers' "personal details" - including name, place, date of birth and occupation - matched their own. The other two men accused of being terrorists are Salem Al-Hamzi and Ahmed Al-Nami. Mr Al-Hamzi is 26 and had just returned to work at a petrochemical complex in the industrial eastern city of Yanbou ... when the hijackers struck. Mr Al-Nami, 33, from Riyadh, an administrative supervisor with Saudi Arabian Airlines, said that he was in Riyadh when the terrorists struck. The FBI admitted that there was some doubt about the identities of some of the suspects. A spokesman said: "The identification process has been complicated by the fact that many Arabic family names are similar. It is also possible that the hijackers used false identities." The spokesman declined to say whether the FBI would apologise but added: "If we have made mistakes then obviously that would be regrettable."
Note: The deceptions in the official story of 9/11 are nowhere more clearly shown than in this important story. The FBI never revised its list of alleged hijackers, and these four are all later listed in the official 9/11 Commission report as the hijackers. Click here and scroll down a little over half way to see their photos in the official report. For more on this, click here. For an abundance of reliable information suggesting a major 9/11 cover-up, click here. For other revealing news articles on 9/11, click here.
[In 1977's] Senate hearings about CIA abuses ... one of the witnesses described a government drug-testing programme known as MKULTRA, which had used innocent Americans selected as human guinea pigs. This CIA-sponsored 'research' directly violated the Nuremberg Code [which] stipulates that patients must give 'informed consent' before any experimentation may begin. [The] architect of MKULTRA, Sidney Gottlieb [testified] about the policy of spiking the drinks of unsuspecting Americans [with LSD]. Ultimately, Gottlieb would admit that MKULTRA tested an array of techniques and substances on dozens of unsuspecting people, and there may well have been hundreds. Gottlieb ... personally spiked the drinks of scientists working with him. An Army scientist, Frank Olson, was given a massive dose and ... ended up jumping through the 10th-floor window of a Manhattan hotel. Gottlieb asked a government narcotics agent named George White to begin testing hallucinogens on unsuspecting citizens. White, a hard-drinking, fast-living man ... began dosing unwitting guinea pigs in autumn 1952. He would later, with Gottlieb's approval, set up safe houses in New York and San Francisco where he played host to prostitutes, drug dealers and their customers and handed the unsuspecting guests drinks laced with LSD. In a 1953 memo to a researcher, Gottlieb gave an indication of the kinds of mind control issues he was interested in -- for both offensive and defensive purposes: 'Disturbance of memory; discrediting by aberrant behaviour; alteration of sex patterns; eliciting of information.' Gottlieb and his boss, Richard Helms -- in an unprecedented and controversial move -- ordered all MKULTRA records destroyed in 1973. A few financial records survived.
Note: Though the CIA denies that mind control techniques were successful, an abundance of evidence suggests otherwise. For a powerful two-page summary of this evidence, click here. For major media articles, key documentaries, and other verifiable information on the secret mind control programs, see our Mind Control Information Center available here.
It had been an entirely routine night watch for the Imperial Iranian Air Force's command post in the Tehran area [when] in quick succession, four calls arrived ... reporting a series of strange airborne objects. A senior officer ... immediately scrambled an IIAF F-4 to investigate. The F-4 pilot reported that the brilliant object was easily visible 70 miles away. When approximately 25 NM [nautical miles] distant, the interceptor lost all instrumentation and UHF/Intercom communications. Upon breaking off the intercept and turning towards his home base, all systems returned to normal, as if the strange object no longer regarded the aircraft as a threat. A second F-4 was scrambled ten minutes after the first. Upon reaching the 25 NM point, the object began rapidly moving away to maintain a constant separation distance. Visually, it resembled flashing strobe lights arranged in a rectangular pattern and alternating blue, green, red, and orange. Their sequence was so fast that all colors could be seen at once. As the F-4 continued pursuit south of Tehran, a second brightly-lit object (about one-half to one-third the size of the moon) detached from the original UFO and headed straight for the F-4 at a high rate of speed. The pilot attempted to fire an AIM-9 missile at the new object but was prevented by a sudden power loss in his weapons control panel. UHF and internal communications were simultaneously lost. The pilot promptly initiated a turn and negative G dive to escape. Continuing the turn, the pilot observed the second object turn inside of him and then away, subsequently returning to the primary UFO for a perfect rendezvous.
Note: This official report by U.S. Air Force Captain Henry Shields, taken from the NSA website at the link above, raises many questions. A copy of this document is available at this link. A 1976 report to the US Joint Chiefs of Staff on this remarkable incident is also available here. For astounding statements by other top government and military officials acknowledging a major cover-up of UFOs, click here.
Both subjects were placed in a very deep trance state and while in this state, the following instructions were given: [Deleted] was instructed that upon awakening, she would proceed to [deleted] room where she would wait at the desk for a telephone call. Upon receiving the call, a person known as "Jim" would engage her in normal conversation. During the course of the conversation, this individual would mention a code word. When she heard this code word, she would pass into a SI trance state, but would not close her eyes and remain perfectly normal and continue the telephone conversation. She was told that ... upon conclusion of the telephone conversation, she would carry out instructions: [Deleted] was shown an electric timing device. She was informed that this device was an incendiary bomb, and was then instructed how to attach and set the device. After [deleted] learned how to set and attach the device, she was told ... to take the timing device which was in a briefcase, and proceed to the ladies room. In the ladies room, she would be met by a girl whom she had never seen who would identify herself by the code word "New York." [Deleted] was then to show this individual how to attach and set the timing device and further instructions would be given ... that the timing device was to be carried in the briefcase to [deleted] room, placed in the nearest empty electric-light plug and concealed in the bottom, left-hand drawer of [deleted] desk, with the device set for 82 seconds and turned on. The experiment was carried out perfectly without any difficulty.
Note: This text is quoted from pages 1 and 2 of declassified CIA document MORI ID 190527. To verify the statement in the text, make a FOIA (Freedom of Information Act) request as described here, or directly view a scanned copy of page 1 here and page 2 here. For a two-page summary of highly revealing government mind control programs, click here. To access thousands of pages of declassified CIA mind control documents online, click here. For lots more reliable information on this crucial topic, click here.
An investigator for the Air Forces stated that three so-called flying saucers had been recovered in New Mexico. They were described as being circular in shape with raised centers, approximately 50 feet in diameter. Each one was occupied by three bodies of human shape but only three feet tall, dressed in metallic cloth of a very fine texture. Each body was bandaged in a manner similar to the blackout suits used by speed fliers and test pilots. The saucers were found in New Mexico due to the fact that the Government has a very high powered radar set-up in that area and it is believed the radar interferes with the controlling mechanism of the saucers.
Note: Download this amazing document and view it on our website at this link. For an ABC news article discussing this, click here. Another FBI document shows FBI chief J. Edgar Hoover wanted "full access to discs recovered" at Roswell. For numerous highly revealing major media reports presenting strong evidence on UFOs, click here. For other reliable and inspiring information on this topic, visit our UFO Information Center.
In 2010, the Washington Post reported that "every day, collection systems at the [NSA] intercept and store 1.7 billion emails, phone calls and other type of communications." In 2011, NSA expanded a program to provide real-time location information of every American with a cell phone, acquiring more than a billion cell phone records each day from AT&T. Later, newspapers around the world began publishing confidential documents leaked by [Edward] Snowden. Americans learned that the NSA can tap almost any cell phone in the world, exploit computer games like Angry Birds to poach personal data, access anyone's email and web browsing history [and] remotely penetrate almost all computers. The NSA used Facebook and Google apps to send malware to targeted individuals. NSA filched almost 200,000,000 records a month from private computer cloud accounts. Obama perpetuated perverse Bush-era legal doctrines to totally shield federal surveillance from judicial scrutiny. Obama's Justice Department secretly decreed that all phone records of all Americans were "relevant" to terrorism investigations and that the NSA could therefore justifiably seize everyone's personal data. Snowden revealed how the NSA had covertly carried out "the most significant change in the history of American espionage from the targeted surveillance of individuals to the mass surveillance of entire populations."
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
It is shocking: The Bush administration is suppressing a CIA report on 9/11 until after the election, and this one names names. "It is infuriating that a report which shows that high-level people were not doing their jobs in a satisfactory manner before 9/11 is being suppressed," an intelligence official who has read the report told me. [The] release of the report, which represents an exhaustive 17-month investigation by an 11-member team within the agency, has been "stalled." First by acting CIA Director John McLaughlin and now by Porter J. Goss, the former Republican House member (and chairman of the Intelligence Committee) who recently was appointed CIA chief. The official stressed that the report was more blunt and more specific than the earlier bipartisan reports produced by the Bush-appointed Sept. 11 commission and Congress. "The report found very senior-level officials responsible." By law, the only legitimate reason the CIA director has for holding back such a report is national security. None of this should surprise us given the Bush administration's great determination since 9/11 to resist any serious investigation. The president fought against the creation of the Sept. 11 commission, for example, agreeing only after enormous political pressure was applied by a grass-roots movement led by the families of those slain. And then Bush refused to testify to the commission under oath. Instead he deigned only to chat with the commission members, with Vice President Dick Cheney present, in a White House meeting in which commission members were not allowed to take notes.
Note: If the above link fails, click here. For other reliable information on the 9/11 cover-up, click here.
The future of wearable technology, beyond now-standard accessories like smartwatches and fitness tracking rings, is ePANTS, according to the intelligence community. The federal government has shelled out at least $22 million in an effort to develop “smart” clothing that spies on the wearer and its surroundings. Similar to previous moonshot projects funded by military and intelligence agencies, the inspiration may have come from science fiction and superpowers, but the basic applications are on brand for the government: surveillance and data collection. Billed as the “largest single investment to develop Active Smart Textiles,” the SMART ePANTS — Smart Electrically Powered and Networked Textile Systems — program aims to develop clothing capable of recording audio, video, and geolocation data, the Office of the Director of National Intelligence announced in an August 22 press release. Garments slated for production include shirts, pants, socks, and underwear, all of which are intended to be washable. There is already evidence that private industry outside of the national security community are interested in smart clothing. Meta, Facebook’s parent company, is looking to hire a researcher “with broad knowledge in smart textiles and garment construction, integration of electronics into soft and flexible systems, and who can work with a team of researchers working in haptics, sensing, tracking, and materials science.”
Note: Smart objects have been called a "train wreck in privacy and security." For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and the disappearance of privacy from reliable major media sources.
Anthropologist Orisanmi Burton has blown the lid off a dark chapter in CIA history. Classified Agency files, recently obtained through Freedom of Information laws, expose shocking ties between the infamous MKULTRA program and nightmarish experiments on prisoners of color within the United States. Burton's findings expose MKULTRA's sinister mission to develop psychological warfare and behavioral manipulation tactics specifically aimed at people of color under the guise of "counterinsurgency." [In] 1968, the American Psychiatric Association's Diagnostic and Statistical Manual of Mental Disorders underwent an alarming update, adding "hostility" and "aggression" as prominent symptoms of schizophrenia. The implications were profound: civil rights activists daring to resist were at risk of being diagnosed and institutionalized. Prisoners refusing to bend to oppressive jail regimes could be conveniently labeled as "criminally insane." In August 2022, MintPress News revealed how Black Americans were disproportionately targeted by the CIA's monstrous mind control machinations. Many MKULTRA trials appeared to have been expressly conducted to gauge potentially varying reactions to psychedelic drugs in Black and White participants. The CIA had a specific – or greater – interest in the effect of certain substances on people of color, rather than the general civilian population. The CIA did indeed seek to determine optimal drugs for targeting Black Americans, if not other ethnic groups.
Note: The MKULTRA program was also used to create mind-controlled assassins. Government and business interests have a long history of experimenting on human beings. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and mind control from reliable major media sources.
Journalist Stephen Kinzer has spent several years investigating the CIA's mind control program, which was known as MKUltra. LSD was just one of the mind-altering drugs that were used in the program to see if and how they could be weaponized to control human behavior. Many of the unwitting subjects of these experiments were subjected to what amounts to psychological torture. The CIA basically set up phony philanthropic foundations which then funded university and college research, and it's through those research experiments that people like Ginsberg and Kesey and Robert Hunter got introduced to LSD. And the university researchers had no idea that their research was actually being funded by the CIA. Stanford University was running a program in which they asked for volunteers to come in and try this new substance. Allen Ginsberg was one of the volunteers; so was Robert Hunter. A similar set of experiments was going on at the Menlo Park Veterans Administration Hospital. That's where Ken Kesey took LSD for the first time. He was so excited about it he took a job in the hospital and began stealing the LSD to give it to his friends. That became the basis for "One Flew Over The Cuckoo's Nest." So all of these original strands that came together in the '60s to produce this great countercultural revolt based around LSD can be traced back through these bogus foundations to the CIA and, ultimately, the director of MKUltra, Sidney Gottlieb.
Note: Read more about the MKUltra program. For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption and mind control from reliable major media sources.
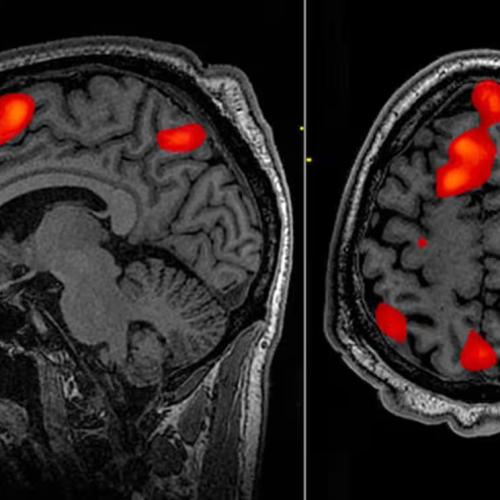
Billionaire Elon Musk’s brain-computer interface (BCI) company Neuralink made headlines earlier this year for inserting its first brain implant into a human being. Such implants ... are described as “fully implantable, cosmetically invisible, and designed to let you control a computer or mobile device anywhere you go." They can help people regain abilities lost due to aging, ailments, accidents or injuries, thus improving quality of life. Yet, great ethical concerns arise with such advancements, and the tech is already being used for questionable purposes. Some Chinese employers have started using “emotional surveillance technology” to monitor workers’ brainwaves. Governments and militaries are already ... describing the human body and brain as war’s next domain. On this new “battlefield,” an era of neuroweapons ... has begun. The Pentagon’s research arm DARPA directly or indirectly funds about half of invasive neural interface technology companies in the US. DARPA has initiated at least 40 neurotechnology-related programs over the past 24 years. As a 2024 RAND report speculates, if BCI technologies are hacked or compromised, “a malicious adversary could potentially inject fear, confusion, or anger into [a BCI] commander’s brain and cause them to make decisions that result in serious harm.” Academic Nicholas Evans speculates, further, that neuroimplants could “control an individual’s mental functions,” perhaps to manipulate memories, emotions, or even to torture the wearer. In a [military research paper] on neurowarfare: "Microbiologists have recently discovered mind-controlling parasites that can manipulate the behavior of their hosts according to their needs by switching genes on or off. Since human behavior is at least partially influenced by their genetics, nonlethal behavior modifying genetic bioweapons that spread through a highly contagious virus could thus be, in principle, possible.
Note: The CIA once used brain surgery to make six remote controlled dogs. For more, see important information on microchip implants and CIA mind control programs from reliable major media sources.
For more than half a century, governments all over the world trusted a single company to keep the communications of their spies, soldiers and diplomats secret. The company, Crypto AG ... made millions of dollars selling equipment to more than 120 countries well into the 21st century. Its clients included Iran, military juntas in Latin America, nuclear rivals India and Pakistan, and even the Vatican. But what none of its customers ever knew was that Crypto AG was secretly owned by the CIA in a highly classified partnership with West German intelligence. These spy agencies rigged the companys devices so they could easily break the codes that countries used to send encrypted messages. The decades-long arrangement, among the most closely guarded secrets of the Cold War, is laid bare in a classified, comprehensive CIA history of the operation obtained by The Washington Post and ZDF, a German public broadcaster, in a joint reporting project. The company always made at least two versions of its products secure models that would be sold to friendly governments, and rigged systems for the rest of the world. Throughout the 1980s, the list of Cryptos leading clients read like a catalogue of global trouble spots. In 1981, Saudi Arabia was Cryptos biggest customer, followed by Iran, Italy, Indonesia, Iraq, Libya, Jordan and South Korea. To protect its market position, Crypto and its secret owners engaged in subtle smear campaigns against rival companies ... and plied government officials with bribes.
Note: For more along these lines, see concise summaries of deeply revealing news articles on intelligence agency corruption from reliable major media sources.
Important Note: Explore our full index to revealing excerpts of key major media news articles on several dozen engaging topics. And don't miss amazing excerpts from 20 of the most revealing news articles ever published.